What Is Automated Incident Management in Cybersecurity?
Automated incident management is the use of technology, orchestration, and predefined workflows to detect, triage, investigate, respond to, and document security incidents without heavy manual intervention. It combines automated incident response tools, SOAR platforms, and AI-driven analytics to accelerate cyber incident response, reduce alert fatigue, and improve compliance incident management across the entire incident lifecycle.
Introduction
Cyberattacks don’t wait for shift changes. They move fast, hide well, and exploit every second of delay. That’s why automated incident management has become a core part of modern security operations. It replaces manual, reactive workflows with structured, technology-driven processes that detect, triage, investigate, and contain threats at machine speed.
If your SOC is still juggling alerts across disconnected tools, here’s what this really means: automation is no longer optional. It’s foundational to scalable, resilient cyber defense. Let’s break it down.
What Is Automated Incident Management?
Automated incident management is the use of technology to streamline and orchestrate the full lifecycle of a security incident — from detection and triage to containment, remediation, and reporting.
In traditional cyber security incident management, analysts manually:
- Review alerts
- Validate threats
- Gather logs
- Correlate data
- Escalate tickets
- Execute response actions
With incident management automation, those steps are predefined, standardized, and triggered automatically based on rules, risk scoring, or AI-driven detection.
Instead of reacting one alert at a time, organizations implement cybersecurity incident management automation that:
- Correlates multi-source telemetry
- Eliminates false positives
- Enriches alerts with threat intelligence
- Executes containment workflows
- Documents actions for compliance
The result are faster resolution, lower analyst fatigue, and consistent incident handling.
The Problem Automation Solves
Modern environments generate millions of security events daily. SOC teams face:
- Alert overload
- Fragmented visibility
- Manual ticketing processes
- Slow containment
- Compliance documentation gaps
Without automation, even the strongest cyber incident response team struggles to keep up. Here’s the hard truth: attackers automate their operations. Defenders must do the same.
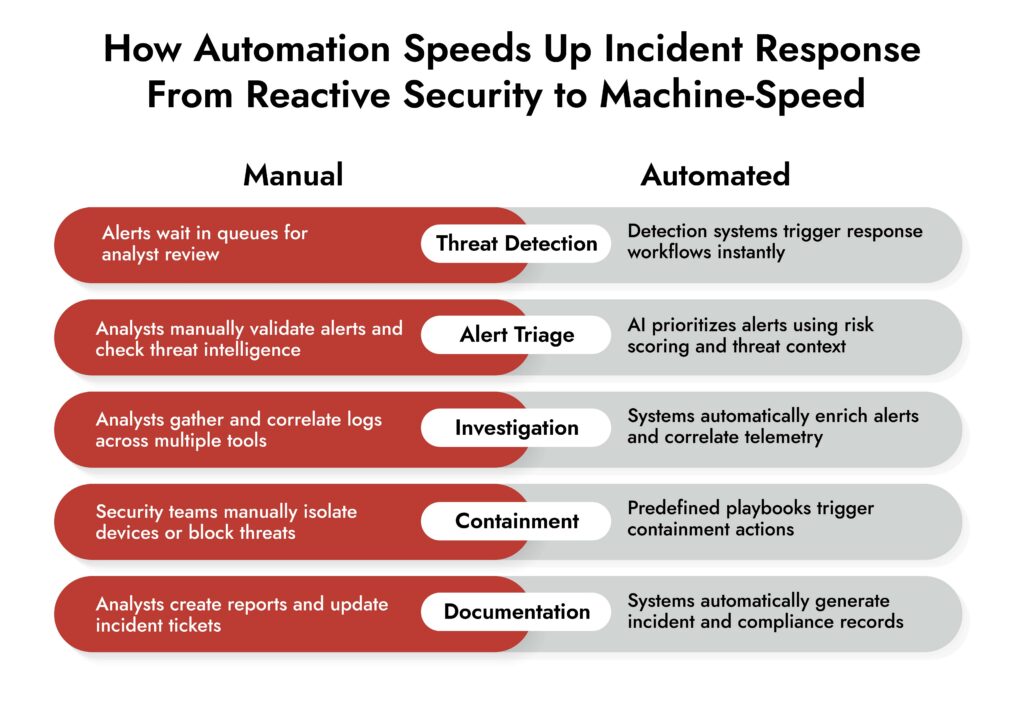
The Difference Between Manual and Automated Incident Management
| Manual Process | Automated Incident Management |
| Analyst-driven triage | Risk-based auto-triage |
| Static playbooks | Dynamic automated workflows |
| Tool-by-tool investigation | Unified, correlated visibility |
| Manual documentation | Auto-generated compliance logs |
| Slower containment | Immediate response triggers |
Automation does not eliminate human oversight. It elevates it. Analysts focus on strategic investigation while repetitive tasks are handled automatically.
Core Components of Automated Incident Management
Effective automated incident management typically includes:
1. Automated Detection – Integrated SIEM, XDR, and analytics engines identify suspicious activity in real time.
2. Intelligent Triage – Alerts are prioritized based on risk scoring, asset value, behavior patterns, and threat intelligence.
3. Orchestrated Response – Using automated incident response tools, systems can:
- Isolate endpoints
- Disable compromised accounts
- Block malicious IPs
- Trigger MFA resets
4. Case Management – Built-in cyber incident management workflows track investigation steps, approvals, and escalations.
5. Compliance Reporting – Automation ensures every action is logged for compliance incident management, supporting frameworks like ISO 27001, NIST, and GDPR.
How Automated Incident Response Fits In
People often confuse automated incident response with automated incident management.
They are related but not identical.
- Automated incident management governs the full lifecycle of incidents.
- Automated incident response focuses specifically on containment and remediation actions.
Think of it this way:
- Management is the strategy and workflow.
- Response is the tactical execution.
Both are critical for strong cyber incident response maturity.
What Role Does SOAR Play?
SOAR platforms are the backbone of many automation initiatives. Security Orchestration, Automation, and Response systems integrate tools across your environment and execute playbooks automatically.
SOAR enables:
- Cross-tool automation
- Alert enrichment
- Multi-step containment workflows
- Automated ticketing
- Escalation triggers
Without SOAR capabilities, incident management automation remains fragmented.
The 5 Steps of Incident Management (Automated Version)
The traditional five steps remain the same. Automation enhances each one.
1. Preparation
- Predefined playbooks
- Asset classification
- Integrated telemetry sources
2. Identification
- Real-time threat detection
- Behavioral analytics
- Automated alert prioritization
3. Containment
- Immediate endpoint isolation
- Network segmentation triggers
- Credential lockdown
4. Eradication
- Malware removal automation
- Patch deployment workflows
- Threat hunting triggers
5. Recovery
- Automated system restoration validation
- Continuous monitoring escalation
Automation accelerates every stage without sacrificing control.
What Tasks Can Be Automated?
A mature cyber security incident management program automates:
- Alert enrichment
- IOC lookups
- Log aggregation
- Ticket creation
- Endpoint quarantine
- User account suspension
- Password resets
- Threat intelligence correlation
- Compliance report generation
- Notification workflows
What this really means is your analysts stop copying data between dashboards and start focusing on threat analysis.
Factors to Consider While Investing in an Incident Response Retainer
Evaluate incident response readiness and expert coverage before incidents occur.
Understand cost vs. risk reduction to optimize security budgets.
Align retainer services with detection, investigation, and response needs.
Balance internal capabilities with external expertise for faster recovery.
Why Automated Incident Management Is Critical for SOC Teams
SOC teams are under pressure to:
- Reduce mean time to detect
- Reduce mean time to respond
- Improve threat visibility
- Maintain compliance
- Prevent burnout
Automated workflows dramatically reduce mean time to respond by removing manual bottlenecks. It also improves consistency. Every alert is handled according to predefined standards, not individual interpretation. For organizations relying on a cyber incident response retainer, automation ensures that external responders have immediate, structured visibility into active cases.
Benefits of Cybersecurity Incident Management Automation
Faster Containment – Automated response actions execute within seconds.
Reduced False Positives – AI-driven triage eliminates low-risk alerts before analysts engage.
Improved Compliance – Automated documentation simplifies audit readiness.
Scalable Operations – SOC teams handle higher alert volumes without proportional headcount increases.
Better Visibility – Correlated telemetry improves root cause analysis.
Automated Incident Management and Compliance
Regulations increasingly require formalized compliance incident management processes.
Automation helps organizations:
- Maintain detailed audit trails
- Enforce standardized response playbooks
- Meet breach notification timelines
- Demonstrate incident handling effectiveness
For heavily regulated sectors like finance and healthcare, this is not optional.
How to Automate Incident Management
Here’s a practical roadmap:
- Centralize telemetry through SIEM or XDR
- Standardize incident classification models
- Build automated playbooks for common scenarios
- Integrate SOAR for orchestration
- Define escalation thresholds
- Continuously refine workflows based on metrics
Start with high-volume, repetitive alerts. That’s where automation delivers immediate ROI.
Challenges to Consider
Automation must be implemented carefully. Common pitfalls include:
- Over-automating without validation
- Poorly defined playbooks
- Lack of cross-team alignment
- Incomplete telemetry integration
Automation amplifies both strengths and weaknesses. Strong governance is essential.
The Future of Cyber Incident Management
AI-driven detection, behavioral analytics, and machine learning are making cybersecurity incident management automation more predictive than reactive. Instead of waiting for compromise indicators, systems will increasingly identify pre-attack behaviors and initiate protective actions.
The next evolution? Autonomous SOC environments with minimal manual intervention.
Conclusion
Automated incident management transforms how organizations defend against modern threats. It brings speed, consistency, and scale to cyber incident response operations. It reduces analyst fatigue. It strengthens compliance posture. And it ensures your cyber incident response team focuses on complex threats instead of repetitive workflows.
Here’s the bottom line: automation does not replace people. It empowers them to operate at the speed of attackers. If your security operations still rely heavily on manual processes, the risk is not just inefficiency. It’s exposure.
Frequently Asked Questions
1. How to automate incident management?
Start by centralizing detection tools, implementing SOAR capabilities, defining standardized playbooks, and automating repetitive tasks like alert enrichment and containment workflows.
2. What are the 5 steps of incident management?
Preparation, Identification, Containment, Eradication, and Recovery. Automation enhances each stage by reducing manual effort and accelerating response.
3. Why is automated incident management important for SOC teams?
It reduces alert fatigue, improves response times, enforces consistent workflows, and enables SOC teams to scale without increasing headcount proportionally.
4. What is the difference between automated incident management and automated incident response?
Automated incident management covers the full lifecycle of an incident. Automated incident response focuses specifically on containment and remediation actions.
5. What role does SOAR play in automated incident management?
SOAR platforms orchestrate tools, automate workflows, enrich alerts, and execute predefined response playbooks across systems.
6. What types of tasks can be automated in incident management?
Alert triage, log correlation, threat intelligence enrichment, ticket creation, endpoint isolation, account suspension, compliance reporting, and notification workflows.
Avoid Delays and Strengthen Response with NetWitness Guidance