Why Reconnaissance Defines Attack Success?
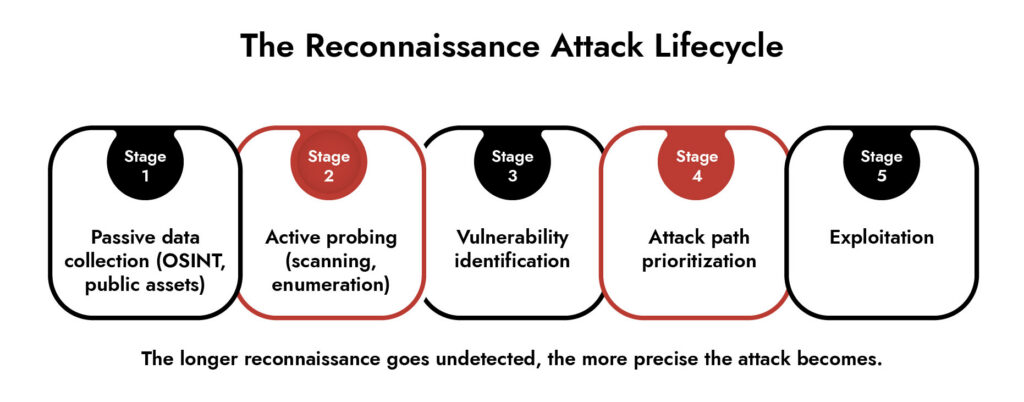
Reconnaissance is where attacks are quietly won or lost. Before any exploit fires, adversaries map your environment, identify weak signals, and prioritize targets. Modern breaches rarely start with brute force. They start with patient observation, often weeks before detection. Organizations that treat reconnaissance in cybersecurity as background noise miss the earliest and most actionable signals of compromise.
Introduction
In spite of the fact that most security strategies tend to concentrate on the time of the attack itself, it is not a good idea.
It is necessary to think about what happens in terms of how breaches take place if one wants to comprehend them. In fact, one must concentrate on the phase which is called reconnaissance, during which hackers gather all the needed information before taking any steps.
Nowadays, the process of reconnaissance cannot be described as an accidental attempt anymore; instead, it is well-planned and automated. Hackers know everything.
What is Reconnaissance in Cybersecurity?
At its core, reconnaissance comes down to intelligence gathering. Attackers collect data about targets to identify vulnerabilities, entry points, and high-value assets.
In reconnaissance cyber security operations, this phase typically includes:
- Mapping network architecture
- Identifying exposed services
- Profiling employees and credentials
- Detecting third-party dependencies
This isn’t a noisy activity. It blends into normal traffic patterns.
According to NIST SP 800-61 Rev. 2 (Computer Security Incident Handling Guide), reconnaissance often precedes exploitation and should be treated as an early-stage incident indicator.
Why Reconnaissance Matters More Than You Think
Understanding what is reconnaissance shifts how you think about risk.
Reconnaissance is not just preparation. It is active engagement with your environment. Every probe reveals:
- What’s exposed
- What’s outdated
- What’s misconfigured
Attackers use this data to reduce uncertainty. That’s why modern reconnaissance attacks feel precise. They are.
From a defensive standpoint, this phase offers something rare: early visibility without damage. If you detect reconnaissance activity, you can disrupt an attack before it escalates.
Types of Reconnaissance in Cybersecurity
To understand what is reconnaissance, you need to distinguish between its two primary forms.
1. Passive Reconnaissance-Passive reconnaissance collects information without direct interaction with your systems.
Examples include:
- Scraping public websites
- Mining social media profiles
- Reviewing job postings for tech stack insights
- Analyzing leaked credentials from data breaches
Here’s the critical point: perimeter reconnaissance does not involve direct system probing in passive methods. That makes it almost invisible from a detection standpoint.
2. Active Reconnaissance-Active reconnaissance involves direct interaction with your infrastructure.
Common techniques:
- Port scanning
- DNS queries
- Service enumeration
- Network fingerprinting
This is where reconnaissance network activity becomes detectable. But detection still requires context. A single scan is noise. Repeated patterns across endpoints? That’s intent.
Common Reconnaissance Attack Techniques
Attackers don’t rely on a single method. They combine multiple reconnaissance technologies to build a complete picture.
Network Scanning – Attackers map your reconnaissance network using tools like Nmap. They identify:
- Open ports
- Running services
- Firewall configurations
DNS Enumeration – DNS remains one of the richest reconnaissance security sources.
Attackers extract:
- Subdomains
- Mail servers
- Internal naming conventions
OSINT (Open Source Intelligence) – Cyber reconnaissance heavily depends on publicly available data.
This includes:
- LinkedIn employee roles
- GitHub repositories
- Company filings
- Vendor disclosures
Social Engineering Reconnaissance – Before phishing, attackers research:
- Organizational hierarchy
- Communication styles
- Recent company events
The goal is credibility.
Credential Harvesting – Attackers use breach databases and dark web sources to test reused passwords across systems.
API and Application Mapping – Modern reconnaissance in cybersecurity increasingly targets APIs.
Attackers:
- Reverse engineer endpoints
- Analyze response structures
- Identify authentication flaws
How Reconnaissance Attacks Evade Detection
Understanding what is reconnaissance also means understanding why it’s hard to catch.
Attackers avoid detection by:
- Slowing down scans to mimic normal traffic
- Distributing requests across multiple IPs
- Using legitimate tools and services
- Blending into cloud and SaaS activity
According to a 2025 industry report, over 60% of reconnaissance attacks bypass traditional signature-based detection systems.
This is not a tooling problem. It’s a visibility problem.
Indicators of Reconnaissance Activity
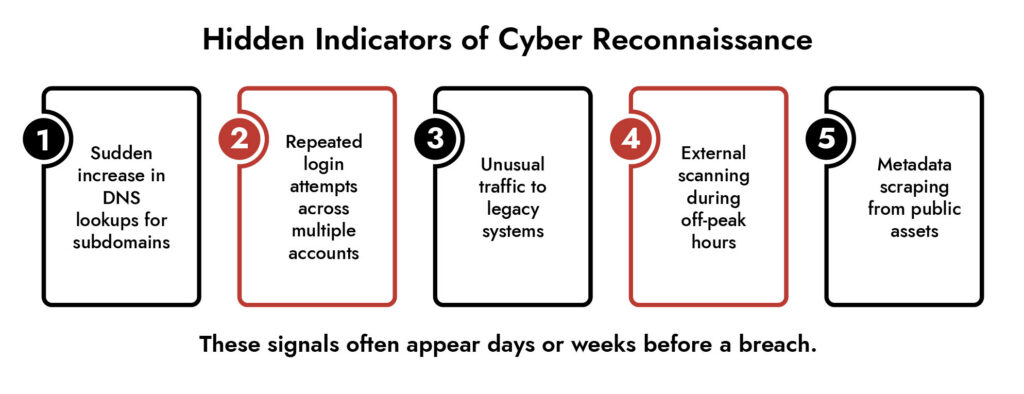
You won’t see a single alert that says “reconnaissance attack detected.”
Instead, you need to connect patterns:
- Repeated connection attempts across ports.
- Unusual DNS query spikes.
- Access attempts from unfamiliar geographies.
- Enumeration-like API requests.
- Low-volume but persistent scanning behavior.
The challenge is correlation. Isolated events mean little. Combined signals tell the story.
How to Defend Against Reconnaissance in Cybersecurity
If you understand what is reconnaissance, your defense strategy changes. You stop reacting and start anticipating.
1. Reduce Your Attack Surface-
- Remove unused services
- Harden exposed endpoints
- Audit public-facing assets regularly
2. Monitor for Behavioral Patterns- Signature detection won’t help here. You need:
- Network traffic analysis
- Behavioral analytics
- Anomaly detection
3. Implement Deception Techniques- Decoys can expose reconnaissance early:
- Fake credentials
- Honeypots
- Dummy endpoints
4. Strengthen Identity Controls- Reconnaissance often targets identities first. Focus on:
- MFA enforcement
- Credential hygiene
- Access monitoring
5. Integrate Threat Intelligence- Use intelligence feeds to identify:
- Known scanning IPs
- Emerging reconnaissance tools
- Attack patterns across industries
Achieve NIS2 Compliance with Confidence
- Meet NIS2 requirements across IT and OT environments
- Detect and respond to threats in real time
- Streamline compliance reporting and audit readiness
- Reduce risk with continuous monitoring and analytics

Where NetWitness Fits In
Reconnaissance doesn’t generate obvious alerts. It creates weak signals across your environment. That’s where deep visibility matters.
NetWitness enables:
- Full packet capture for forensic-level network visibility
- Detection of low-and-slow reconnaissance patterns
- Correlation across network, endpoint, and logs
- Behavioral analytics to identify anomalous probing activity
Instead of relying on isolated alerts, it builds a narrative. That’s critical when dealing with reconnaissance attacks that unfold over time.
For organizations managing hybrid and OT environments, this level of visibility becomes essential. Attackers don’t distinguish between IT and OT. Your detection strategy shouldn’t either.
Conclusion
Understanding what reconnaissance changes is how you approach cybersecurity. This phase is not optional for attackers. It is foundational. And that makes it one of the most reliable opportunities for early detection.
The organizations that get ahead don’t wait for exploitation. They identify intent early, disrupt it, and force attackers to move on. If your detection strategy starts at intrusion, you’re already late.
Frequently Asked Questions
1. What is reconnaissance in cyber security?
In cyber security, reconnaissance is defined as the act performed by attackers in which information is collected regarding the target system or network prior to an actual cyber-attack.
2. What are the best tools for detecting reconnaissance attacks?
Detection of reconnaissance attacks requires usage of several tools, namely tools that analyze network traffic, behavioral analysis software, and full packet capture tools.
3. How can I protect my network from reconnaissance attacks?
Start by reducing your attack surface, monitoring for unusual patterns, enforcing strong identity controls, and using deception techniques. Continuous visibility into network behavior is critical.
4. What cybersecurity services specialize in reconnaissance attacks?
Security operations platforms that combine threat detection, network analysis, and incident response capabilities are best suited. Managed detection and response (MDR) services also help identify reconnaissance activity early.
5. What are top software solutions for identifying reconnaissance attacks on corporate networks?
Look for solutions that provide deep network visibility, behavioral analytics, and correlation across multiple data sources. Platforms like NetWitness are designed to detect subtle reconnaissance patterns over time.
6. What is a reconnaissance attack in computer security?
A reconnaissance attack is the initial phase of a cyberattack where adversaries collect intelligence about a target system to identify vulnerabilities and plan exploitation strategies.




