What are social engineering attacks and how can enterprises prevent them in 2026?
Social engineering attacks manipulate people into revealing sensitive information or taking harmful actions. In 2026, these attacks use AI, deep fake video, and voice cloning to become more convincing and faster than ever.
To prevent them, enterprises should:
- Use phishing-resistant MFA like FIDO2 security keys
- Implement callback verification for sensitive requests
- Introduce approval delays for financial transactions
- Deploy AI-based behavioral threat detection
- Train employees on real-world attack scenarios like vishing and deepfakes
The key shift is this: don’t rely on spotting attacks. Build processes that verify every critical action.
Introduction
If you’ve been tracking enterprise security trends, you already know that the threat landscape has shifted dramatically. Social engineering attacks aren’t new they’ve been the hacker’s weapon of choice for decades. What is new is how frighteningly effective they’ve become.
A finance executive in Hong Kong transfers $25 million after a video call with people he trusts. All of them were deepfakes. In a separate case, attackers cloned a CEO’s voice and convinced a subordinate to wire $18.5 million. These aren’t hypotheticals. They happened.
Here’s the uncomfortable reality: AI hasn’t invented a new type of threat. It’s taken an old one exploiting human trust and made it faster, more convincing, and nearly impossible to spot with the naked eye. If your enterprise isn’t rethinking its approach to social engineering in security, this is the year you need to.
What Is Social Engineering? The Security Definition You Need
Before getting into 2026-specific threats, let’s be precise about what we’re talking about.
The social engineering security definition, at its core, is this: manipulating people into doing something they otherwise wouldn’t handing over credentials, authorizing payments, clicking a link, or opening a door. It bypasses technical controls entirely by targeting the human layer of your security stack.
Social engineering in security isn’t about exploiting software vulnerabilities. It exploits trust, urgency, authority, and fear. And unlike a code exploit, there’s no patch for human psychology.
That’s what makes social engineering cybersecurity such a uniquely difficult problem. You can update your firewall. You can’t update your workforce overnight.
The 2026 Social Engineering Landscape: What’s Actually Changed
AI Has Become the Attacker’s Force Multiplier
According to ISACA’s 2026 Tech Trends report, AI-driven social engineering has overtaken ransomware to become the single biggest cybersecurity concern 63% of surveyed IT professionals flagged it as their top threat. Only 13% of organizations say they feel “very prepared” to handle it.
The numbers explain why. Attackers can now generate highly convincing phishing emails in roughly 5 minutes, compared to 16 hours manually a 192x increase in speed, with no drop in quality. AI-generated phishing achieves a 54% click-through rate. Traditional phishing? About 12%.
That gap is devastating.
The Speed of an Attack Has Collapsed
Mandiant’s M-Trends 2026 report found something alarming: the median time between initial access and handoff to ransomware operators has dropped from over 8 hours in 2022 to just 22 seconds in 2025. By the time your SOC reads the alert, the breach may already be monetized. This isn’t a technology problem you can throw more monitoring at you need to stop the initial access from happening.
Types of Social Engineering Attacks Dominating 2026
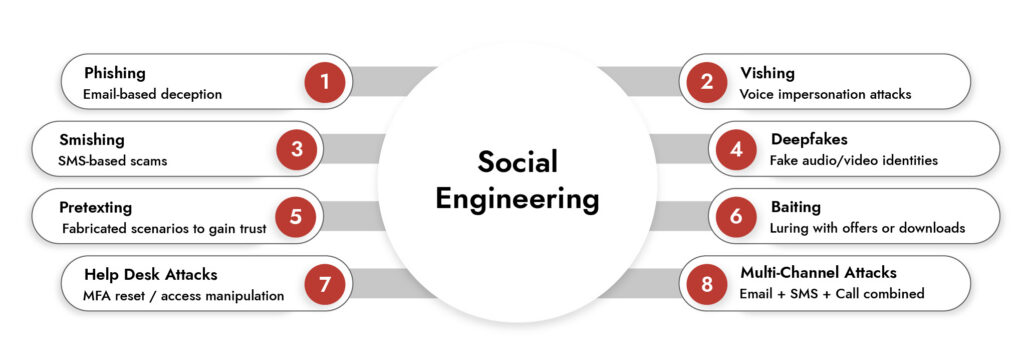
Understanding the types of social engineering attacks in play right now is the starting point for any realistic defense strategy. Here’s what’s actually hitting enterprises this year.
1. Voice Phishing (Vishing) Now the Primary Vector
Vishing has overtaken email as the dominant social engineering attack vector. It accounts for 11% of incidents overall and 23% of cloud compromises. There’s been a 442% increase in vishing since the second half of 2024.
The reason? AI voice cloning. An attacker can clone an executive’s voice from publicly available audio and call your IT help desk, HR team, or finance department sounding exactly like someone they trust. In one documented case, attackers gained domain admin access in under 40 minutes using only social pretexts no malware, no hacking, just a phone call.
2. ClickFix and Browser-Based Attacks
This one saw a 517% surge in 2025. The attack is surprisingly simple and brutally effective: a malicious website presents a fake error message and walks the user through “fixing” it by running a PowerShell command. The user does it themselves, thinking they’re solving a problem. The attacker gets in.
ClickFix bypasses traditional email security entirely there’s no suspicious attachment, no phishing link to flag. It shows up in search results, on compromised websites, and through malvertising.
3. Deepfake Video and Audio
There are now over 8 million deepfake files circulating online up from 500,000 in 2023. The technology has become accessible enough that sophisticated deepfake video calls are no longer a nation-state capability. The $25.6 million Hong Kong fraud was executed via a deepfake video conference call involving multiple fake participants, all convincingly rendered.
Your executives’ public speaking clips, LinkedIn videos, and interview recordings are training data. Attackers have already collected them.
4. Multi-Channel Orchestration
Modern social engineering attacks don’t come through a single channel. They run coordinated sequences a suspicious email, followed by a convincing SMS, followed by a phone call “confirming” the request. Each touchpoint reinforces the others. By the time the target acts, they’ve had the same “legitimate” story confirmed across three different channels. That’s not a phishing email. That’s a campaign.
5. IT Help Desk Targeting
Help desks are prime targets because they’re designed to be helpful and they hold the keys. An attacker who convincingly impersonates an employee can request an MFA reset, account recovery, or password change. Once they have that, the entire enterprise may be exposed. The social pretexts don’t even need to be elaborate. Urgency and authority alone are often enough.
Methods for Understanding and Reducing Social Engineering Attacks
This is where most security guides go generic. Let’s be specific about what actually works in 2026.
Rethink Identity Verification from the Ground Up
Traditional knowledge-based verification “what’s your employee ID?” or “what’s your mother’s maiden name?” is dead. An attacker who has spent 20 minutes on LinkedIn knows those answers. Worse, AI can synthesize background details from dozens of sources automatically.
What works instead:
Hardware FIDO2 security keys for MFA are phishing-resistant and immune to AI voice cloning bypass attempts. Out-of-band verification is essential for sensitive requests: if someone calls asking for a password reset, call them back on their registered number don’t use the number they gave you on the call. For high-value actions, require video verification while training staff on deepfake artifacts unnatural blinking patterns, audio-visual sync delays, lighting inconsistencies. And introduce time-delayed approvals for financial transactions and access changes. Urgency is the attacker’s weapon. Remove it from your processes.
Stop ClickFix Before It Hits the Terminal
Browser-based attacks require browser-level defenses. Deploy browser isolation or enterprise browsers with command-line execution controls enabled. Block PowerShell and terminal execution for standard users via application control policies. Train every employee explicitly on “copy-paste” social engineering the concept that no legitimate website ever needs you to paste a command into your terminal.
This training needs to be specific and concrete. Telling people to “be careful on the internet” doesn’t work. Showing them exactly what a ClickFix prompt looks like and why it should never be followed does.
Fight AI with AI
Manual security reviews can’t keep up with AI-generated attacks at scale. Your defense architecture needs to match the threat. Behavioral analytics and identity threat detection can spot anomalous authentication patterns before they lead to breaches. Deepfake detection tools can be integrated into video conferencing and voice authentication workflows. AI-powered email security analyzes conversation patterns and behavioral context, not just content keywords. Cross-channel correlation platforms can detect multi-stage attacks that span email, Slack, SMS, and voice something no human analyst watching a single channel can catch.
Fix the Workflows That Attackers Exploit
Social engineering attacks are fundamentally process attacks. Attackers aren’t beating your technology they’re finding the gap between your policy and your people.
For IT help desks: require manager approval for MFA resets. Implement callback verification to registered numbers. Require a service ticket with a case number for any account changes. Flag any “urgent” request for additional scrutiny urgency is a red flag, not a reason to move faster.
For financial processes: mandate verified callback procedures for any payment changes. Add 24-48 hour holds on new beneficiary additions. Require dual authorization for high-value transfers. Never accept banking changes via email or voice alone, period.
For executive impersonation: establish “safe word” verification codes for out-of-hours or urgent requests. Create escalation protocols for requests that arrive through unusual channels. Use secure, authenticated communication platforms for sensitive discussions not email or personal messaging apps.
Uncover the Top Threats Shaping Industrial Network Security
- Emerging threats targeting industrial control systems (ICS)
- Ransomware and supply chain risks in OT environments
- Hidden attack paths across converged IT/OT networks
- Real-world trends impacting critical infrastructure security

Modernize Security Awareness Training
Annual compliance-based security training doesn’t prepare employees for 2026-grade attacks. It teaches people to spot bad grammar in phishing emails. Attackers have moved on.
Effective training in 2026 looks different. Simulate AI-generated phishing using actual current attack patterns. Run vishing simulations with AI-cloned voices with appropriate ethics oversight so employees know what voice impersonation actually sounds like. Train on deepfake recognition and what verification steps to take when something feels off. Most importantly, shift the framing from “spot the attack” to “follow the process.” Assume the content will look perfect. Assume the voice will sound right. The defense is the verification step, not the detection.
Just-in-time training triggered by risky behavior is more effective than annual reminders. When an employee almost clicks a simulated phishing link, that’s the moment to teach them — not six months ago during an onboarding session.
Assume Breach Build for Detection
Prevention will fail. Plan for it. After any social engineering attempt even an apparently unsuccessful one monitor for lateral movement indicators. Watch for OAuth token abuse and session cookie harvesting. Alert on unusual cloud access patterns and privilege escalations. Track break-glass account usage and credential vault access.
Implement 24/7 SOC coverage with specific playbooks for voice-based incidents. Most SOC teams have solid playbooks for malware. Far fewer have thought through what to do when the breach started with a phone call.
Extend Defense to Your Supply Chain
Many of the most damaging social engineering attacks in recent years haven’t targeted enterprises directly they’ve targeted vendors and third parties with access to enterprise systems. Audit your third-party identity verification processes. Monitor for unusual OAuth consent grants to SaaS applications. Require security attestations from vendors that specifically cover social engineering defenses. Implement vendor access reviews and session monitoring.
Your security is only as strong as the weakest link in your supply chain, and attackers know which link that usually is.
The Bottom Line
AI hasn’t changed the fundamentals of social engineering it still exploits the same human trust and process gaps it always has. What’s changed is scale, speed, and believability. The $25 million deepfake video conference fraud and the $18.5 million voice cloning scam demonstrate clearly that technical controls alone are insufficient.
Your enterprise protection strategy needs to do four things:
First, assume every digital interaction is suspect verify through independent channels. Second, slow down high-risk processes urgency is the attacker’s most powerful tool and removing it from your workflows removes their leverage. Third, invest in AI-powered defenses that detect behavioral anomalies, not just content. Fourth, build a verification culture where “trust but verify” is standard operating procedure, not a sign of distrust.
The organizations that come through 2026 intact will be the ones that treat social engineering as a business process problem, not just a security technology problem. The threat lives in the gap between your policies and your people. Close that gap.
Frequently Asked Questions
1. What are social engineering attacks?
Social engineering attacks manipulate people into sharing information or taking harmful actions. The social engineering security definition focuses on exploiting human behavior, not systems, making them a major risk in social engineering cybersecurity.
2. How do social engineering attacks work?
They work by building trust, creating urgency, and triggering action. In social engineering in security, attackers often impersonate trusted identities using email, calls, or AI-driven deepfakes, especially in social engineering attacks 2026.
3. What are the risks of social engineering for enterprises?
Enterprises face data breaches, financial loss, and unauthorized access. With social engineering attacks 2026, faster and more convincing attacks increase the chances of large-scale impact.
4. How can enterprises prevent social engineering attacks?
Key methods for understanding and reducing social engineering attacks include strong MFA, callback verification, approval delays, AI-based detection, and continuous employee training.
5. What are common types of social engineering attacks?
Common types of social engineering attacks include phishing, vishing, smishing, pretexting, baiting, deepfake scams, and multi-channel attacks.
Why Trust Has Become the New Attack Surface
- Expanding digital attack surface across cloud and OT
- Unmonitored identities and excessive privileges
- Disconnected security tools lacking context
- Blind spots in east-west network traffic





