What is OT Network Security in Converged IT/OT Networks?
OT network security involves protecting every type of industrial site that uses technology to run equipment, such as those connected to an IT platform. Because there is now a unified, integrated environment, the OT network has new vulnerabilities. These new risks include more external access points to the OT environment. They also create a larger attack surface for the OT environment. In addition, there is little visibility into how many industrial communications occur. To properly protect the OT networks, you will need to establish a continual monitoring process, implement strong OT network segmentation techniques, and build a comprehensive OT-specific cybersecurity strategy.
Introduction
The OT network security was never meant to be connected like this.
For decades, operational systems have been in isolation. Predictable, deterministic, and mostly untouched by external threats. Then came convergence. IT systems are connected with industrial control systems to improve efficiency, analytics, and remote operations.
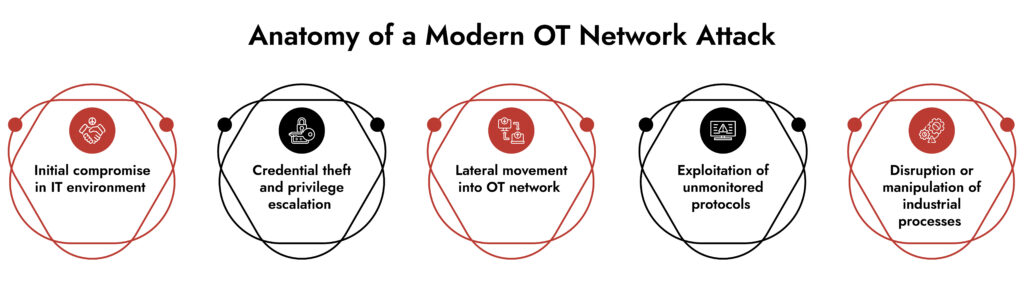
Here’s the trade-off: every connection expanded the OT network attack surface.
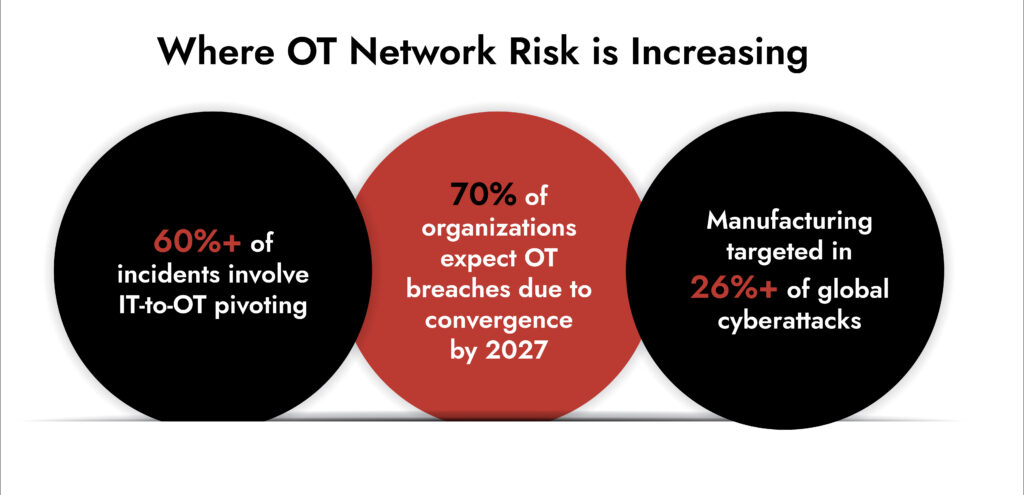
The attackers don’t require any physical presence anymore. They can shift focus from the IT environment to the OT network. They take advantage of gaps that current tools cannot detect. Recent NIST and CISA reports (2024-2025) indicate that nearly 60% of attacks follow this pattern. These assaults on vital infrastructure employ lateral movement from IT to OT.
Essentially, this means that if your OT network is still based on outdated assumptions, you are protecting an old architecture from current threats.
Why OT Network Convergence Changes the Security Equation
Convergence doesn’t just connect to systems. It changes how risk behaves inside the OT network security.
Traditional OT environments prioritize uptime and safety. Security came later. IT environments, on the other hand, evolved with layered defenses and continuous monitoring. When these worlds merge, mismatched priorities create exploitable gaps.
Key shifts impacting the OT network security:
- Expanded attack paths: IT compromises now extend into industrial systems
- Increased exposure: Remote access, cloud integrations, and IoT devices widen entry points
- Protocol complexity: Legacy industrial protocols lack authentication and encryption
- Operational constraints: You cannot patch or reboot critical systems freely
Core OT Network Security Challenges in Converged Environments
1. OT Network Visibility Challenges are Still the Biggest Risk
You cannot secure what you cannot see. Most OT network environments still lack deep, real-time visibility into industrial traffic.
Common issues:
- Blind spots in east-west traffic within the OT network
- Lack of protocol-aware monitoring
- Limited asset inventory accuracy
- Incomplete mapping of IT-OT interdependencies
Without visibility, OT threat detection becomes reactive at best.
2. OT Attack Surface is Expanding Faster Than Controls
Every connected sensor, PLC, and gateway increases the OT network attack surface.
Modern drivers:
- Industrial IoT deployments
- Cloud-based analytics platforms
- Remote vendor access
- Converged identity systems
Manufacturing stayed the most targeted sector for cyberattacks for the third year. Many incidents started from exposed OT network components.
3. IT Security Tools Don’t Translate to OT Cybersecurity
Deploying IT tools inside an OT network security often creates more risk than protection.
Why?
- OT systems cannot tolerate aggressive scanning
- Signature-based detection misses industrial anomalies
- Endpoint agents are incompatible with legacy devices
This mismatch leaves organizations with fragmented OT cybersecurity strategies that fail during real incidents.
4. OT Network Segmentation is Often Incomplete or Misconfigured
Segmentation is the backbone of industrial network security, yet many environments implement it superficially.
Common failures:
- Flat network architectures
- Weak firewall rules between IT and OT network zones
- No micro-segmentation within critical processes
- Over-permissive remote access pathways
Without strong OT network segmentation, attackers move laterally without resistance.
What Effective OT Network Security Looks Like Now
Strong OT network security requires alignment between visibility, detection, and response across IT and OT environments.
1. Unified Visibility Across the OT Network
You need protocol-aware monitoring that understands industrial traffic behavior, not just IP flows.
This includes:
- Deep packet inspection for ICS protocols
- Passive asset discovery
- Behavioral baselining of the OT network
2. Context-Driven OT Threat Detection
Detection must go beyond signatures. It must understand intent inside the OT network.
Effective OT threat detection includes:
- Anomaly detection based on process behavior
- Correlation between IT and OT events
- Integration with OT threat intelligence sources
3. Enforced OT Network Segmentation
Segmentation should isolate critical systems and restrict lateral movement.
Best practices:
- Zone-based architecture aligned with ISA/IEC 62443
- Strict access control between IT and OT network
- Microsegmentation for high-value assets
4. Continuous OT Risk Management
Static controls fail in dynamic environments. OT risk management must evolve continuously.
This means:
- Ongoing asset inventory updates
- Risk scoring based on exposure and criticality
- Real-time monitoring of configuration changes
Bridging the Gap: Aligning IT and OT Security Operations
The real challenge isn’t just securing the OT network. It’s aligning two fundamentally different operational models.
Key priorities:
- Shared visibility between IT and OT teams
- Unified incident response workflows
- Centralized analytics across environments
- Clear ownership of operational technology cyber security
Organizations that succeed treat convergence as a design problem, not just a tooling issue.
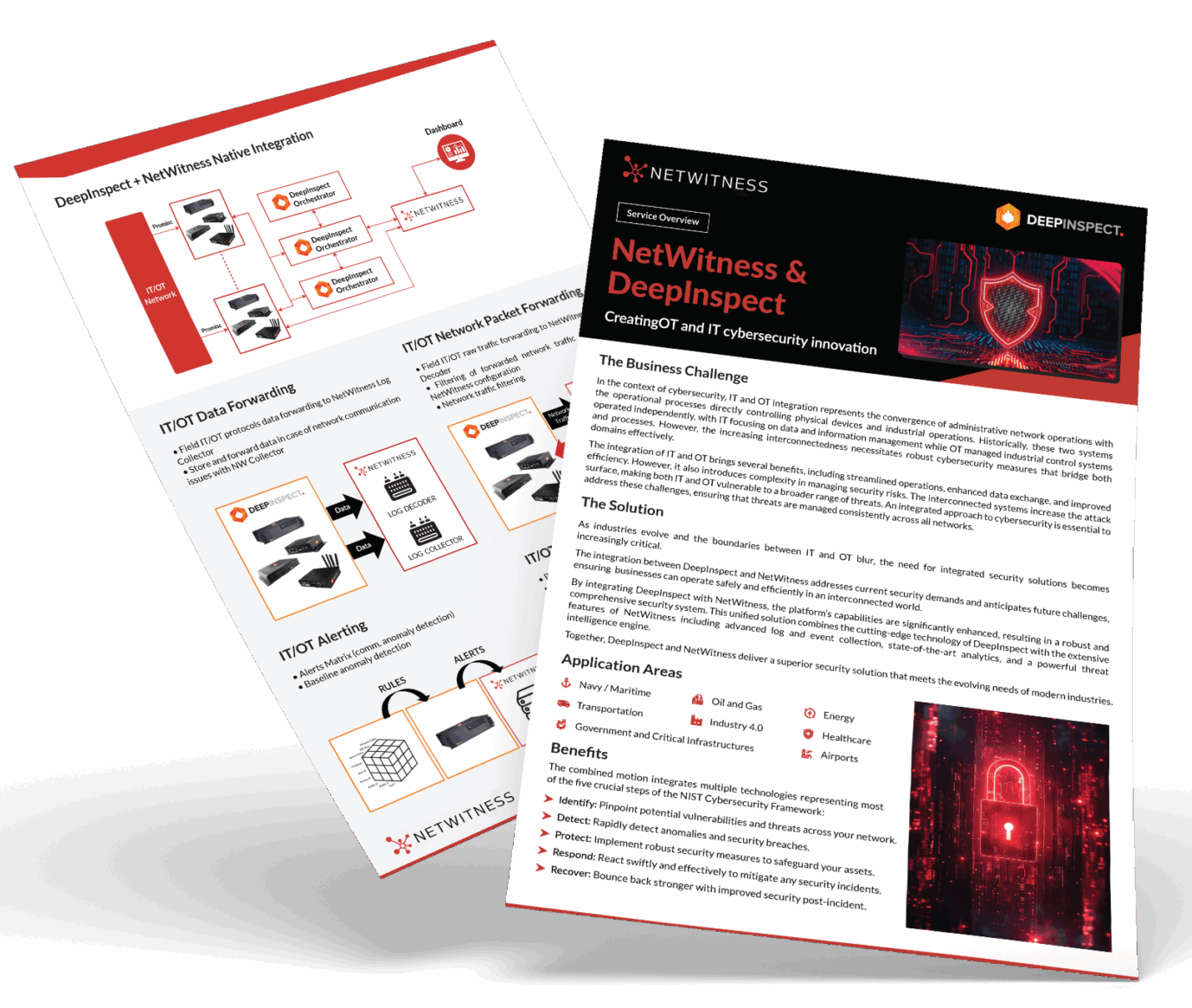
Where NetWitness Fits into OT Network Security
Securing a modern OT network requires more than isolated monitoring tools. It demands deep visibility, cross-domain correlation, and investigative depth.
NetWitness supports OT cybersecurity by enabling:
- Full-packet visibility across IT and OT environments
- Advanced threat detection tailored to industrial protocols
- Unified investigation workflows across converged networks
- Integration with threat intelligence for context-driven decisions
This approach strengthens industrial network security without disrupting operations. It gives teams the ability to detect, investigate, and respond to threats inside the OT network with precision.
Conclusion
The OT network security is no longer isolated. It is exposed, interconnected, and actively targeted. Security strategies must reflect that reality.
Organizations that rely on legacy assumptions will struggle to detect and contain modern threats. Those that invest in visibility, segmentation, and integrated detection will gain control over their OT network risk.
This is not about adding more tools. It’s about building a security model that understands how the OT network actually operates today. If your current approach still treats OT as a separate problem, it’s time to rethink that assumption.
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
Frequently Asked Questions
1. What are the best practices for OT network segmentation?
For proper OT network segmentation, one needs to consider using zones as an architecture, have tight access controls, and perform micro–segmentation of critical assets. Using the ISA/IEC 62443 standards may help minimize lateral movement and increase OT network security.
2. What are the leading platforms for OT network visibility and monitoring?
One should seek a platform capable of conducting deep packet inspection, passive asset discovery, and behavioral analysis for the OT network. Unification of the IT and OT networks in terms of visibility will lead to better OT threat detection.
3. How can organizations integrate OT networks with IT infrastructure securely?
Integration demands suitable control points, strong identity management, and consistent monitoring. Collaboration between IT and OT cybersecurity teams will guarantee uniform application of the policy across the OT network.
4. Can you recommend tools for effective OT segmentation?
The most important features include network zoning, industrial firewalling, and microsegmentation. One should not forget about reducing exposure within the OT network.
5. How does IoT network segmentation improve security?
IoT network segmentation reduces extra device-to-device communication. This also reduces possible attack paths. For an OT network, this reduces the overall OT attack surface.