Key Features of the Best OT Cyber Security Solutions
When it comes to choosing the best solution in terms of OT Cyber Security, there are five major components that you need to consider. These include full asset view; protocol-aware tools for monitoring; ongoing detection of threats in real-time; network segmentation; as well as prioritization of risks according to their impact. If you miss any part of your OT Security strategy, you will create gaps. These gaps can make it hard to respond quickly to an attack. This can lead to downtime.
Introduction
Because industrial environments weren’t made with gracefully failing in mind, production stops when there is an OT system failure. Production ceases when there is an OT system failure, safety is compromised when there is an OT system failure, and production losses begin occurring just minutes following an OT system failure. The importance of having the best cybersecurity for operational technology networks has shifted from a necessary compliance-based decision to a decision rooted in survival.
However, the majority of organizations evaluate OT cybersecurity solutions using the same criteria for assessing IT cybersecurity solutions, which is a big mistake when the costs of downtime are significant, legacy systems are the norm, and visibility is at best patchy.
This means that to achieve the optimal cybersecurity for OT networks, you should evaluate your operational technology cybersecurity measures based on visibility, detection, and uptime, rather than assessing the control level at what expense, along with any disruptions to the process. Let’s explore what really matters.
Why the Best Cybersecurity for Operational Technology Networks Requires a Different Approach
OT environments operate on deterministic processes. They rely on predictable communication patterns, proprietary protocols, and systems that weren’t built with security in mind.
Unlike IT networks:
- You cannot patch frequently
- You cannot install heavy agents
- You cannot afford downtime
This is why cybersecurity for industrial environments demands specialized OT security tools.
Key differences shaping OT cybersecurity solutions:
- Legacy infrastructure with minimal native security
- Flat network architectures that increase attack spread
- Safety-critical operations where disruption can cause physical harm
Core Capabilities of the Best Cybersecurity for Operational Technology Networks
You’re not buying tools. You’re buying resilience. The best cybersecurity for operational technology networks consistently delivers on five non-negotiables.
1. Deep OT Visibility Across All Assets
You can’t secure what you don’t see. OT visibility is the foundation.
Look for:
- Passive asset discovery (no disruption)
- Identification of PLCs, RTUs, HMIs
- Real-time mapping of OT networks
Strong OT network security solutions provide:
- Asset inventory with context
- Communication baselines
- Risk scoring tied to operational impact
2. Protocol-Aware Monitoring for OT Networks
Industrial protocols like Modbus, DNP3, and OPC are not designed for security.
The best cybersecurity for operational technology networks includes:
- Native decoding of OT protocols
- Behavior-based anomaly detection
- Deep packet inspection tailored for OT environments
This enables effective network monitoring for OT environments without interfering with operations.
3. Real-Time Threat Detection Without Disruption
Detection speed defines impact. OT threat detection solutions must operate in real time while remaining invisible to operations.
Capabilities to expect:
- Behavioral analytics for anomaly detection
- Detection of lateral movement inside OT networks
- Integration with threat intelligence feeds
4. Network Segmentation and Access Control
Flat OT networks remain one of the biggest risks. Effective OT security solutions must support:
- Micro-segmentation
- Zone-based architecture
- Secure remote access
This aligns with frameworks like NIST SP 800-82, which prioritizes segmentation as a core control.
5. OT Risk Management Tools That Align with Operations
Risk in OT isn’t theoretical. It’s operational. The best cybersecurity for operational technology networks connects:
- Vulnerabilities → operational impact
- Threats → safety consequences
- Incidents → downtime risk
Strong OT risk management tools should:
- Prioritize risks based on production impact
- Map threats to MITRE ATT&CK for ICS
- Provide actionable remediation without disrupting workflows
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
How the Best Cybersecurity for Operational Technology Networks Fits Together
Think of this as a working model, not a diagram. If one layer is weak, the entire OT security posture starts to crack.
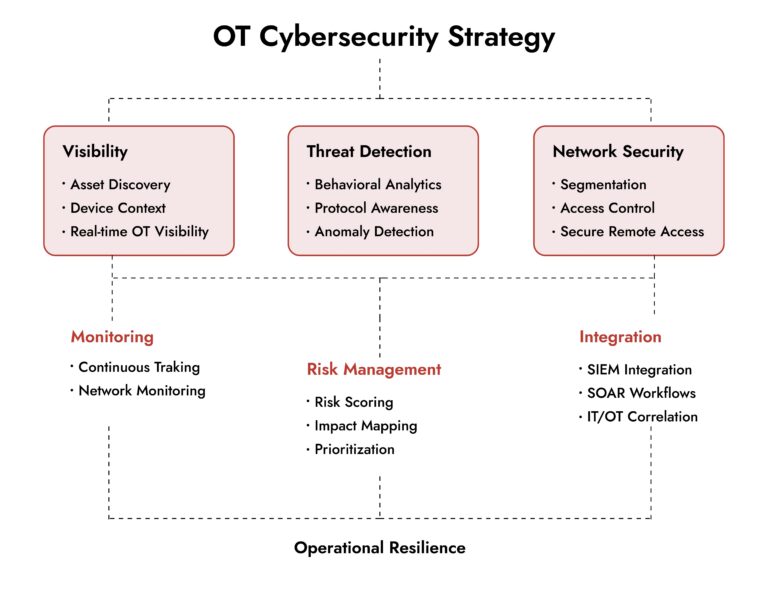
If your current approach to the best cybersecurity for operational technology networks doesn’t connect these layers, you’re not securing OT, you’re managing isolated tools.
Missing visibility → You don’t know what to protect Weak detection → You’ll find threats too late No integration → Your response will always lag
Evaluating OT Cybersecurity Solutions: What Separates Leaders from Tools
Not all OT cybersecurity solutions are built equally. Some focus on monitoring. Others claim visibility but lack depth.
Here’s how to evaluate effectively:
Signal vs Noise
- Can the system reduce false positives?
- Does it understand industrial behavior patterns?
Deployment Model
- Passive deployment preferred
- No operational downtime during rollout
Integration Capabilities
- Works with SIEM, SOAR, and NDR
- Supports unified visibility across IT and OT
Scalability
- Can handle large, distributed OT networks
- Supports multi-site industrial environments
The best cybersecurity for operational technology networks scales without complexity.
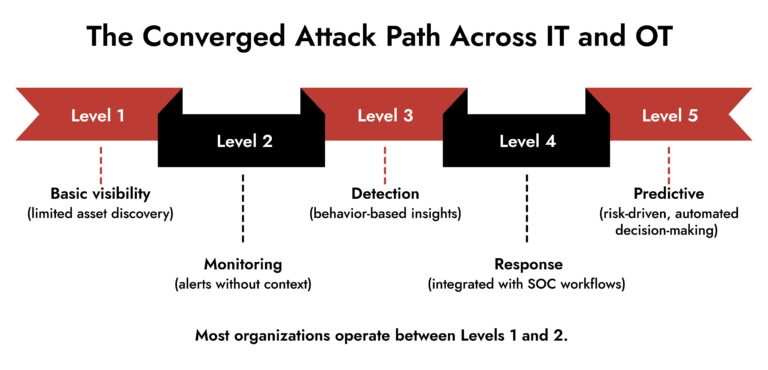
Where NetWitness Fits into OT Cybersecurity Strategy
Industrial security requires more than isolated OT tools. It demands integration across detection, investigation, and response.
Solutions like those from NetWitness focus on:
- Deep network visibility across IT and OT environments
- Advanced threat detection using behavioral analytics
- Packet-level inspection for forensic investigation
- Unified platform for detection, investigation, and response
What this enables:
- Faster identification of threats across OT networks
- Correlation between IT and OT attack vectors
- Stronger incident response workflows
This approach aligns with the growing need for convergence between IT security and OT cybersecurity solutions.
Common Mistakes When Choosing OT Security Tools
Even mature organizations get this wrong.
Watch for these pitfalls:
- Treating OT like IT
- Prioritizing compliance over operational risk
- Ignoring legacy systems
- Overloading teams with alerts
- Deploying intrusive tools that disrupt operations
The best cybersecurity for operational technology networks avoids these traps by design.
Conclusion
Industrial cybersecurity has moved beyond theoretical risk. It now directly affects uptime, safety, and revenue. The best cybersecurity for operational technology networks doesn’t rely on traditional controls. It builds visibility, understands industrial behavior, and detects threats before they disrupt operations.
Organizations that invest in the right OT cybersecurity solutions don’t just reduce risk. They gain operational confidence. If your current approach still treats OT as an extension of IT, it’s time to rethink the strategy.
Frequently Asked Questions
1. What key features should you look for in OT cybersecurity solutions?
The leading OT cybersecurity solutions provide extensive OT visibility, protocol-aware monitoring, immediate threat detection, segmentation features, and OT risk management instruments.
2. What is the importance of real-time monitoring in OT security?
Real-time monitoring in OT security is essential as it helps in detecting threats and anomalies immediately. In OT, any delay in recognizing threats and irregularities may result in outages.
3. What industries benefit most from OT cybersecurity solutions?
The industries that benefit most from OT cybersecurity solutions are manufacturing, energy, oil and gas, utilities, and transportation.
4. Why is scalability important in OT cybersecurity solutions?
OT environments involve various sites. Scalability is important in OT network security solutions because it does not increase complexity.
5. Why is asset visibility important in OT environments?
Asset visibility is important in OT environments because it gives an overall understanding of all devices in an OT network.
6. How do OT security tools differ from traditional IT security tools?
OT security tools differ from traditional IT security tools in that they use passive monitoring and protocol awareness. Traditional IT security tools use active controls.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.