What is Advanced Threat Detection?
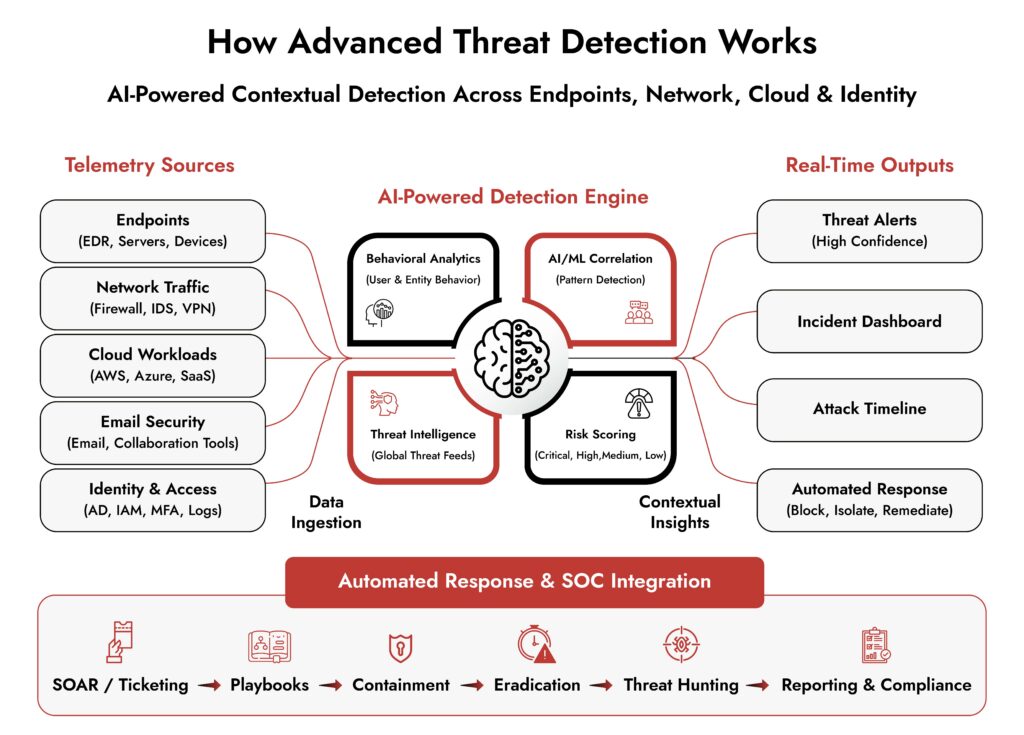
Advanced threat detection starts where signature-based tools stop working. Instead of matching known patterns, these systems analyze patterns in network traffic, user behavior, and system activity to spot unusual behavior. They correlate data from endpoints, networks, cloud environments, and identity systems, and help SOCs to identify suspicious activity earlier and investigate potential attacks before they cause serious damage.
Attackers today are evolving faster than the security tools that safeguard enterprises against them. They use your own administrative tools against you. They don’t stand out, but blend in. They lurk around for weeks, slowly causing damage.
Traditional tools like firewalls, antivirus, and signature-based detections are rudimentary and fail very early on. That’s the context you need to understand before diving into advanced threat detection. It’s a fundamentally different philosophy about how detection should work.
What is Traditional Detection and Where It Breaks Down
When traditional security tools were designed and built, they worked around a core assumption that threats have an identifiable pattern. If anything matches the pattern, it should be blocked.
It worked at a time when attackers relied more on readily available toolkits than creativity. Their technical expertise was often limited to deploying commodity malware rather than engineering sophisticated campaigns.
But today, cyber-attack techniques have evolved far more than traditional tools.
- Signature-based detection fails as attackers employ polymorphic malware that changes its own signature. Zero-day exploits and living-off-the-land techniques easily pass through traditional tools. The attackers also use valid credentials and identities that are not flagged by them.
- Perimeter-focused security assumes that sensitive data lives within a specific boundary, but in today’s multi-platform infrastructure, the perimeters have faded.
Even with grave shortcomings, traditional tools still find a place in the security stack. They catch opportunistic, low-sophisticated attacks. But for advanced persistent threats they are not enough.
What is Advanced Threat Detection?
Advanced threat detection is designed to defend against sophisticated attacks. It puts together multiple security capabilities such as full detailed visibility across logs, network, and endpoints, AI, behavioral analysis, and threat intelligence into a unified system. It aims to detect and stop the attacks before they start.
Advanced threat detection is built around a different question. Instead of “does this match something bad we’ve seen before,” it asks “does this behavior make sense for this environment, this user, this time of day?”
A different kind of reasoning about what is happening in your environment, and not matching signatures faster, is what makes modern enterprise threat detection unique.
What is the Main Difference Between Advanced Threat Detection and Traditional Detection?
Now that we know what each of the approaches mean, let’s look into the differences:
1. Detection Method
Traditional detection works on a simple concept of matching threat signatures to alert to an intrusion. It works only when the threats are known, but zero-day exploits easily pass through.
Advanced Threat Detection builds a model of normal behavior and flags whenever an activity deviates from that. The threats need not be known or documented beforehand. If it is behaving differently than expected, the investigation is triggered.
2. Speed
According to IBM’s 2025 Cost of a Data Breach Report, traditional tools take 212 days to detect a threat and 72 days to contain it. Modern advanced threat detection and response platforms shrink that time considerably. They enable automated correlation, and AI-driven triage accelerates investigations from days to minutes. Automated response workflows contain the threat while human investigation is just getting started.
3. Coverage
Traditional tools work around a specific fixed pre-defined boundary, typically the network edge. It worked with on-premises systems where the perimeter was well defined. But with the adoption of cloud and hybrid environments, the traditional perimeters have vanished. Advanced threat detection is designed to work across endpoints, network traffic, cloud environments, email, and identities.
4. Alert Quality
Traditional security tools may see up to 10,000 alerts per day. Unfortunately, most of them could be false positive or low-priority events. However, SOC cannot risk overlooking any of them and end up being burnt down for actual alerts that matter.
AI threat detection addresses this by correlating the alerts, grouping it by attack chain, and scoring them by severity for analysts’ attention. This initial triage and context building cuts down the noise and allows analysts to work on critical alerts.
5. Response Method
Traditional tools are limited to detection and alerting. The response needs manual intervention. This could mean delays due to unavailability or lack of expertise.
Advanced threat detection and response can design automated response workflows that get triggered the moment a high-confidence threat is identified.
| Traditional Detection | Advanced Threat Detection | |
| What it catches | Known threats with documented signatures | Known and unknown threats, including zero-days |
| Detection speed | Months to days | Hours to minutes |
| Coverage | Network perimeter, specific chokepoints | Endpoints, network, cloud, email, identity |
| Unknown threats | Blind | Behavioral modeling identifies anomalies |
| Alert volume | High noise, manual triage | AI-prioritized, high-confidence incidents |
| Response | Manual, analyst-dependent | Automated containment + human oversight |
| APT visibility | Minimal | Core design requirement |
360° Cybersecurity with NetWitness Platform
– Unrivaled visibility into your organization’s data
– Advanced behavioral analytics and threat intelligence
– Threat detections and response actionable with the most complete toolset
What Should Enterprises Look for in an Advanced Threat Detection Solution?
The market has many options of advanced threat detection solutions to choose from. Here are the factors you should consider:
1. Behavioral Analytics – True behavioral analytics that build baselines per-entity, per user, per device, and per application, and not organization-wide thresholds.
2. End-to-end Visibility – The platforms should provide complete visibility across your environment. It should cover cloud as well as endpoints. If it covers only endpoints or only network traffic, sooner or later, there will be blind spots.
3. Automated Response – Automation is important to ease the manual workload and allow analysts to focus on strategic tasks. However, high-impact actions such as taking a critical server offline should require human approval. Platforms that offer graduated automation, like automatic action for low-risk containment, human-in-the-loop for consequential decisions.
4. Easy Integrations – Advanced threat detection requires multiple tools to come together, and hence integration with SIEM, SOAR, etc should not be additional overhead. If integration requires significant custom development, you should probably rethink your choice.
5. Depth on Advanced Persistent Threat Detection – The platform should be able to detect living-off-the-techniques where attackers use legitimate tools like PowerShell, WMI, or remote management utilities to avoid malware signatures. This differentiates mature platforms from immature ones as it is one of the hardest problems in AI cybersecurity threat detection.
NetWitness is built around how good SOC teams actually work — not how vendors assume they do. Instead of surfacing isolated alerts, it captures logs, packets, and endpoint telemetry across hybrid environments so analysts can trace an attack from first entry to last action, rather than piecing together fragments from disconnected tools. The full picture — identity, network, cloud, endpoints — comes together in one place.
Behavioral analytics backed by machine learning handles the alert noise problem. Real anomalies get surfaced. False positives get filtered. Analysts spend time on things that actually warrant attention, not chasing down events that go nowhere.
For security teams weighing an advanced threat detection system, NetWitness hits a balance without piling on complexity.
Conclusion
Attackers are way ahead in crafting sophisticated and evasive attacks. Advanced persistent threats and AI-powered reconnaissance are changing the threat landscape as we speak. Advanced threat detection platforms are the only appropriate counter to AI-powered attacks.
Traditional tools have done their bit and still find a place in today’s security stack, but they need copious technical support to stand against today’s adversaries. The enterprises today don’t have a choice but to make a shift towards modern threat detection and response platforms. They need to switch from reactive to proactive, from perimeter-focused to behavior-focused, and from managing alerts to knowing what is actually happening in their environment.
Frequently Asked Questions
1. How does Advanced Threat Detection use AI and machine learning?
AI in security has generated a lot of interest, and it is worth looking at what works. Here are a few use cases of AI and machine learning in advanced threat detection.
- Behavioral Baselines Modeling: AI is used widely for machine learning models. It is adept at consuming historical data across users, devices, and applications to document what is normal. When something deviates from this normal, the model highlights it in no time.
- Anomaly Detection at Scale: A human analyst can keep in mind a few dozen variables at a time, but an ML model tracks thousands of behavioral signals simultaneously. It genuinely detects anomalies better than a human reviewer.
- Alert Prioritization: AI threat detection algorithms can process raw alerts faster and help analysts with a prioritized alert list, grouped by likely attack chain, with context attached. This impact on SOC operations accelerates responses and guarantees more security.
- Cross-layer Correlation: Fragmented telemetry is not useful unless it is correlated to a recognizable attack pattern. AI cyber threat detection correlates automatically across data sources that would take an analyst hours to manually correlate.
According to IBM’s 2025 Cost of a Data Breach Report, organizations using AI and automation identified and contained breaches 80 days faster than those who did not.
2. How does Advanced Threat Detection improve SOC efficiency?
Advanced threat detection solutions do the initial triage and correlation, bringing down the signal-to-noise ratio. It also helps accelerate the response by automating the response workflows. A good solution also enables proactive threat hunting thus improving the overall SOC efficiency.
3. Do mid-sized companies also need advanced threat detection?
It works for both. Given that mid-market companies are increasingly targeted precisely because attackers assume their defenses are weaker, this is worth taking seriously regardless of company size. AI threat detection platforms have become significantly more accessible with pricing and deployment models that fit any organization.
Unmask GenAI Threats — Get Ahead of the Curve