Key Takeaways
- A network threat analysis demonstrates that attacker behaviors are often missed by endpoint and log-centric methods of detection.
- Real-world threats will utilize lateral movement between devices communicating with one another and will rely on encrypted communication and legitimate user credentials, instead of relying solely on malware.
- To understand attackers’ intent and impact, organizations should continue to seek network visibility via deep packet inspection.
- NetWitness provides detection of these types of threats via behavior, context, and evidence enabling the security personnel to respond quickly and confidently.
- Today’s SOCs investigate alert fatigue before implementing security operations using network forensics.
Introduction
Most breaches don’t start loud. They start polite.
A valid login. A familiar protocol. Traffic that looks routine enough to pass every control designed for yesterday’s threats. That’s why network threat analysis still decides whether an organization detects an intrusion early or explains it later.
What many security teams are feeling right now is not a tooling gap. It’s a visibility gap. When attackers live off the land, move laterally, and operate inside encrypted channels, endpoint alerts and logs tell only part of the story. The rest unfolds on the network.
This is where network threat analysis earns its place. Not as a legacy discipline, but as the layer that shows how threats actually move, communicate, and persist. This blog looks at real-world use cases where NetWitness uncovers activity others overlook and why that visibility changes outcomes.
Why Network Threat Analysis Still Anchors Detection
Attackers adapt faster than detection models. That’s not an opinion, it’s a pattern.
Recent CISA and NIST guidance (2024–2025) highlight a consistent trend: advanced intrusions rely on credential abuse, internal reconnaissance, and encrypted command-and-control. These techniques rarely trigger signatures. They blend into normal operations.
Network threat analysis focuses on behavior over time:
- How systems talk to each other
- Which protocols get used, misused, or stretched
- Where trust boundaries quietly erode
NetWitness applies network security analytics to these interactions, giving analysts evidence instead of assumptions.
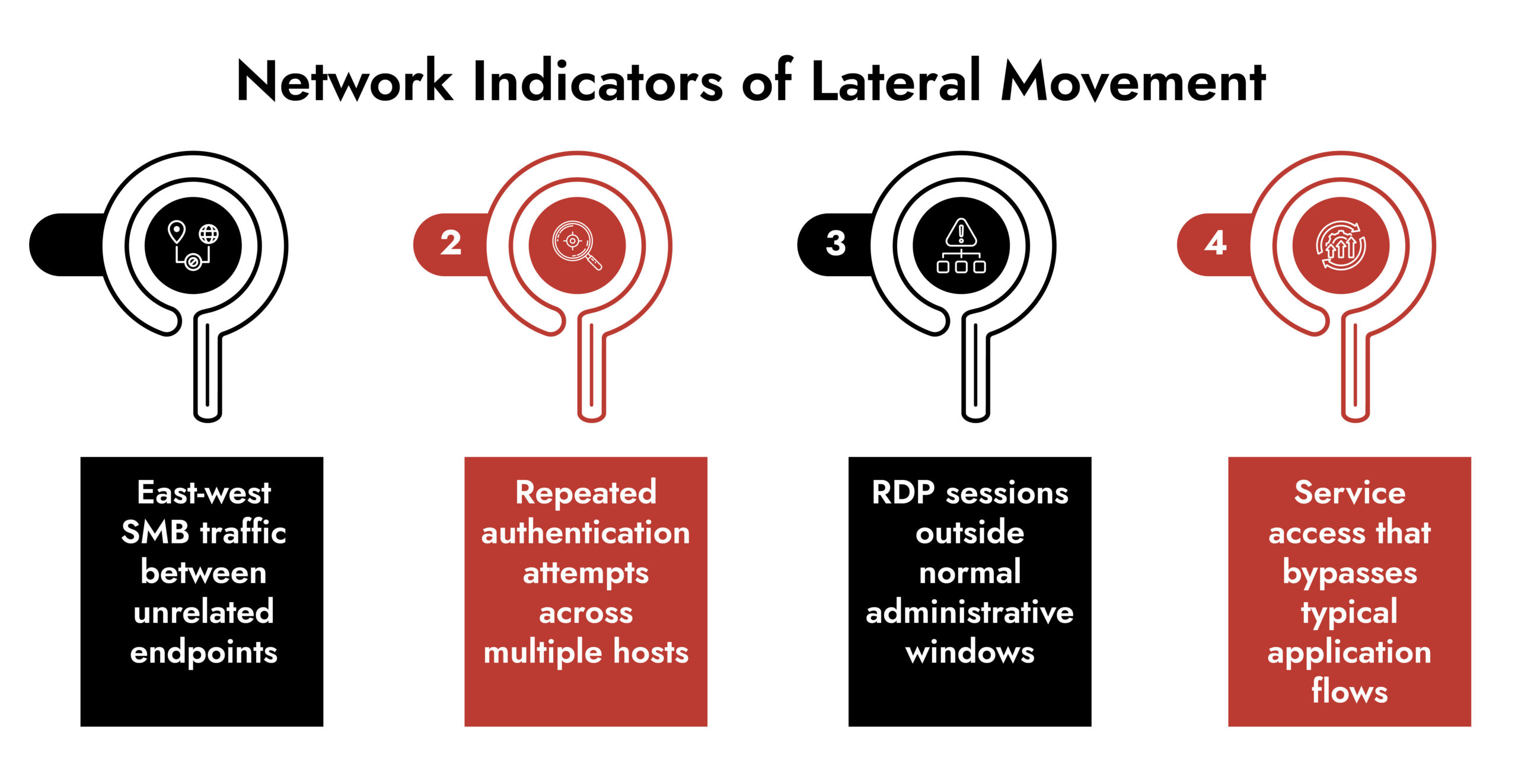
Use Case 1: Lateral Movement That Looks Legitimate
Lateral movement rarely announces itself. It mimics administration.
In a common enterprise breach scenario, an attacker compromises a user workstation through phishing. From there, they pivot internally using SMB and Kerberos, accessing systems the user technically has permission to reach.
Endpoint tools see nothing malicious. Identity systems see valid credentials.
Network threat analysis tells a different story.
With full network visibility, NetWitness identifies:
- Authentication sequences that deviate from normal access paths
- SMB and RPC activity between hosts that rarely communicate
- Kerberos service ticket usage inconsistent with role behavior
These signals expose lateral movement early, before privilege escalation turns access into control.
Use Case 2: Insider Threat Detection Without Guesswork
Insider threats are rarely about intent at first. They’re about behavior drift.
An engineer downloads more data than usual. A contractor accesses systems outside their scope. A user starts transferring files at odd hours using approved tools.
Traditional monitoring struggles because identities look valid and actions appear authorized.
Network threat analysis introduces context.
NetWitness correlates network traffic analysis with identity, device, and session behavior to show:
- Where data moves, not just who accessed it
- Which protocols carry sensitive information
- How behavior changes over time
This allows teams to investigate insider risk based on evidence, not suspicion.
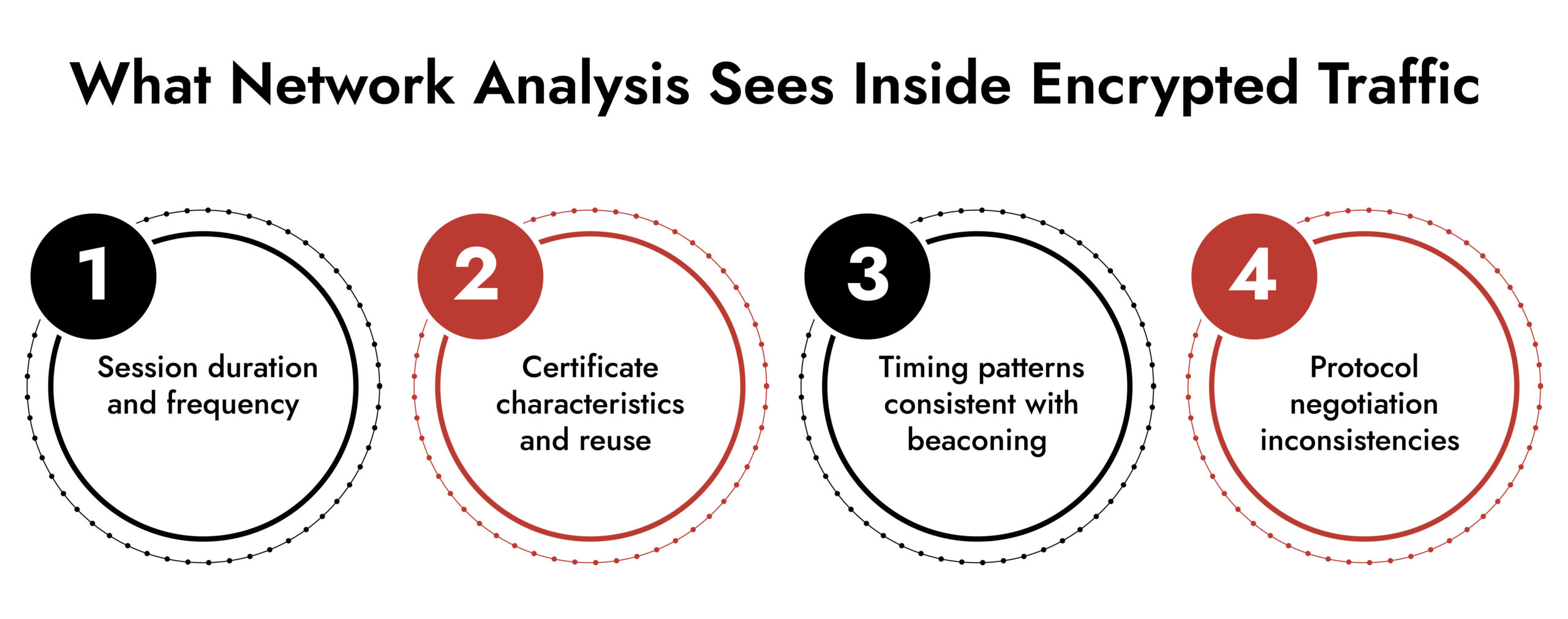
Use Case 3: Encrypted Traffic That Still Tells a Story
Encryption protects data. It doesn’t protect attackers.
Over 90% of enterprise traffic now uses TLS, and attackers rely on that cover. But encrypted sessions still carry behavioral fingerprints.
NetWitness uses deep packet inspection and metadata analysis to observe:
- TLS handshake anomalies
- Certificate reuse across unrelated hosts
- Beaconing intervals typical of command-and-control
This form of advanced threat detection works without decrypting everything, preserving performance and privacy while exposing malicious patterns.
Use Case 4: Third-Party Access and Supply Chain Exposure
Trust relationships are convenient. They are also dangerous.
Third-party vendors often receive network access that bypasses many controls. When those vendors become compromised, attackers inherit that trust.
Network threat analysis shifts the focus from access to behavior.
NetWitness monitors how third-party connections behave after authentication:
- Unexpected data transfers
- Access to systems outside contractual scope
- Network paths that violate established baselines
This visibility helps organizations detect supply chain compromise before it spreads internally.
Use Case 5: Threat Hunting Grounded in Network Evidence
Threat hunting fails when it starts with guesses.
Effective threat hunting starts with facts. Network forensics provides those facts.
With NetWitness, analysts hunt by:
- Reconstructing full network sessions
- Tracing attacker movement across time
- Pivoting from indicators to behavior
Threat hunting with NetWitness becomes an investigation workflow, not a keyword search exercise.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
How NetWitness Approaches Network Threat Analysis
NetWitness does not treat the network as a data source of last resort. It treats it as a foundation.
The platform focuses on three principles that align with how real attacks unfold.
Comprehensive Network Visibility- Traffic capture across on-prem, virtual, and cloud environments provides continuity, not blind spots.
Behavior-Driven Detection- Network security analytics identify deviations in how protocols, users, and systems interact over time.
Investigation-First Design- Network forensics allows analysts to validate findings, understand scope, and respond with confidence.
This approach supports Zero Trust network monitoring by continuously verifying behavior rather than assuming trust.
Why Network-Based Detection Still Defines SOC Maturity
Modern SOC teams face an uncomfortable reality: alerts are plentiful, clarity is not.
Network threat analysis restores that clarity.
Recent research shows that breaches affecting multiple environments can take roughly 276 days to detect and contain. That’s almost nine months of attacker freedom before decisive response. In practice, attackers are inside long before alerts ever surface. This makes network threat analysis non-negotiable, because traditional visibility and alerts alone aren’t enough.
Network monitoring and network traffic analysis give SOC teams:
- Faster detection of unknown threats
- Reduced false positives through behavioral context
- Stronger evidence for response and reporting
This is not about replacing endpoints or cloud controls. It’s about giving them backbone.
Conclusion
Attackers succeed when activity blends in. Network threat analysis breaks that illusion.
NetWitness helps teams find threats that do not set off alarms. It focuses on how systems talk, how trust is misused, and how behavior changes over time.
In an environment where stealth defines modern attacks, network visibility remains the difference between reacting late and responding early.
Frequently Asked Questions
1. What is network threat analysis?
Network threat analysis is the process of studying network behavior. It helps find harmful activity that avoids detection by endpoints and logs.
2. How does NetWitness detect threats other tools miss?
NetWitness threat detection uses network visibility, deep packet inspection, and behavioral analytics to uncover lateral movement, encrypted threats, and insider activity.
3. Which organizations benefit most from network threat analysis?
Enterprises with complex networks, third-party access, and regulatory exposure benefit most from advanced network threat analysis.
4. What real-world threats can NetWitness identify?
NetWitness identifies lateral movement, insider threats, command-and-control activity, data exfiltration, and supply chain compromise through network forensics.
5. Why is network-based detection critical for SOC teams today?
Network-based detection provides evidence-driven visibility, reduces dwell time, and enables confident incident response decisions.
6. How does threat intelligence enhance network threat analysis?
Threat intelligence adds external context to network behavior, improving prioritization and investigative accuracy.




