What defines a high-performing IT security solution today
An effective IT security solution cannot be described simply as a collection of tools. However, it should rather be considered a complete system providing visibility, detection, investigation, and reaction in hybrid environments efficiently and swiftly. The difference between functionality and success can be measured by efficiency and swiftness of decision making.
Introduction
For most companies, it’s not the problem of having no security tools. It’s the problem of too many security tools that fail to communicate.
This is the harsh reality that influences modern security strategies. The best possible IT security solution doesn’t merely identify risks. It correlates, prioritizes, and directs the incident response process for all the endpoints, networks, cloud environments, and users. Otherwise, there would be unnecessary noise, delays in response, and greater risks to the organization.
As stated by the National Institute of Standards and Technology (NIST), successful cybersecurity requires constant monitoring, swift detection, and collaborative incident response. However, many companies lack complete visibility.
The change here is obvious. Modern enterprise security requires integration, intelligence, and clarity. Let’s explore what capabilities we need.
Top Capabilities of a Modern IT Security Solution for Enterprises
Centralized Visibility Across the Entire Attack Surface in an IT Security Solution
An IT security solution must provide a single, coherent view of activity across environments. Without centralized visibility, teams operate in silos and attackers exploit that.
This means:
- Aggregating telemetry from endpoints, networks, cloud services, and identity systems.
- Normalizing data for consistent analysis.
- Enabling real-time and historical visibility.
Why it matters:
- IBM Security reports that organizations with mature visibility reduce breach lifecycle by over 61 days.
- Fragmented data delays investigation and increases dwell time.
In practice, strong enterprise IT security solutions unify logs, packets, flows, and behavioral signals into one operational view. This is not convenience. It is operational necessity.
Advanced Threat Detection and Response Capabilities in IT Security Solutions
Detection without response is just noise. A capable IT security solution must identify threats and enable immediate, informed action.
Core detection capabilities include:
- Behavioral analytics to identify anomalies.
- Signature-based detection for known threats.
- Machine learning models for unknown attack patterns.
Response capabilities should include:
- Automated containment (endpoint isolation, credential revocation)
- Case management workflows
- Forensic investigation support
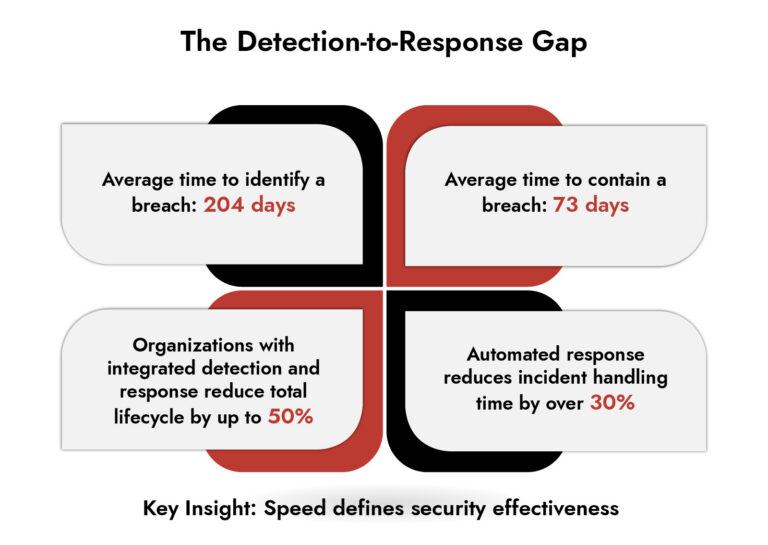
What this really means is faster decisions. According to the Cybersecurity and Infrastructure Security Agency (CISA), reducing response time directly limits the blast radius of attacks.
Strong cybersecurity solutions integrate detection and response into a continuous loop, not separate processes.
Integrated Security Monitoring Tools Within an IT Security Solution
An IT security solution should not depend on manual correlation across tools. It must embed security monitoring tools that provide context-rich insights.
Key monitoring capabilities:
- Real-time alerting with risk scoring
- Correlation across multiple data sources
- Noise reduction through prioritization
Why this matters:
- Security teams face alert fatigue daily.
- Without prioritization, critical threats get buried.
According to Gartner, organizations that implement integrated monitoring reduce false positives by up to 90%.
Effective security operations platforms shift focus from alert volume to actionable intelligence.
Network Security Tools That Go Beyond Perimeter Defense
Traditional perimeter-based security is no longer sufficient. A modern IT security solution must include deep network security tools that inspect internal traffic and lateral movement.
Capabilities to expect:
- Full packet capture for forensic analysis
- Network traffic analysis (NTA)
- East-west traffic visibility
Why this matters:
- Many attacks operate inside the network after initial access.
- Visibility into lateral movement is critical for containment.
Real-world example: In ransomware attacks, initial compromise often goes unnoticed. The real damage happens during lateral movement. Without network-level visibility, detection comes too late.
Strong enterprise IT security solutions treat the network as a primary detection layer, not just a transport medium.
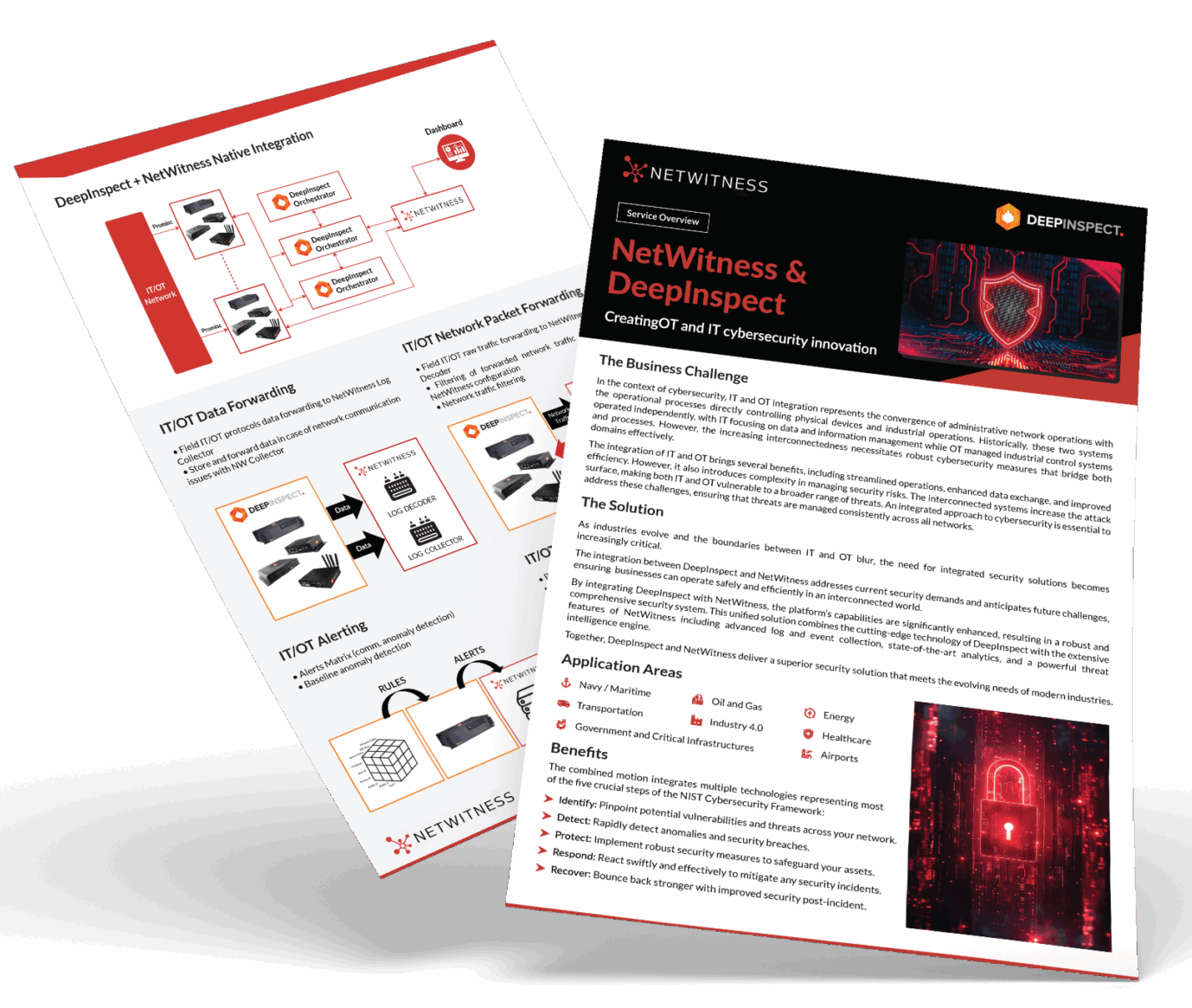
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.
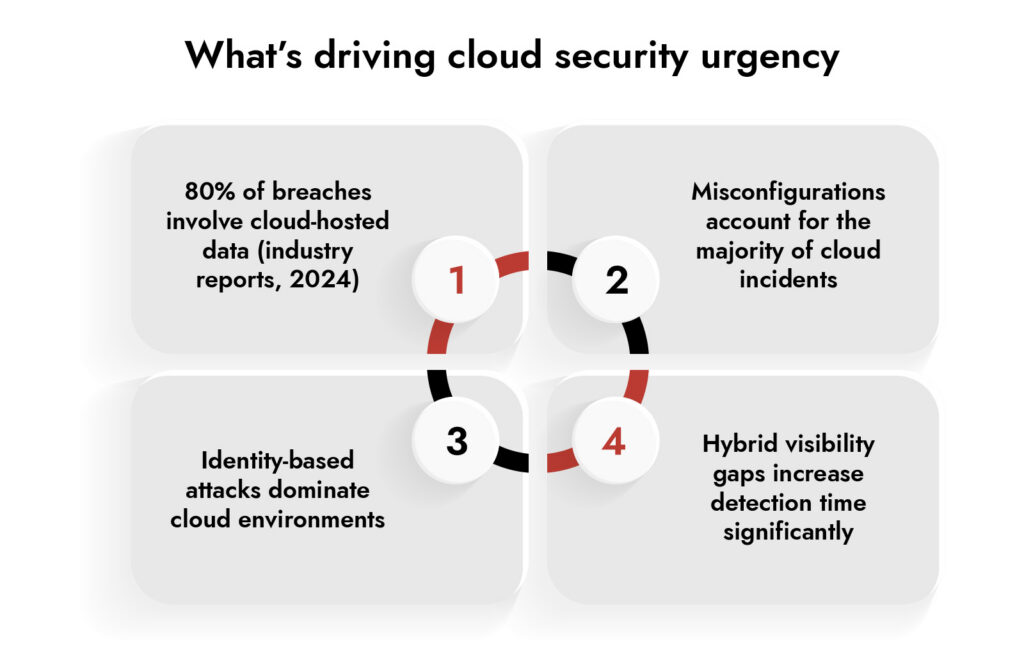
Cloud Security Solutions Built into the IT Security Solution
Cloud environments expand the attack surface. An IT security solution must include embedded cloud security solutions, not bolt-ons.
Core cloud capabilities:
- Visibility into SaaS, IaaS, and PaaS environments
- Misconfiguration detection
- Identity and access monitoring
Why this matters:
- According to National Security Agency (NSA), misconfigurations remain a leading cause of cloud breaches.
- Cloud activity often lacks traditional logging depth.
Modern cybersecurity tools must extend seamlessly into cloud environments without creating visibility gaps.
Automation and Orchestration in an IT Security Solution
Manual processes slow everything down. A strong IT security solution embeds automation across workflows.
Key automation capabilities:
- Incident triage and enrichment
- Playbook-driven response actions
- Integration with external tools and systems
Why this matters:
- Security teams face talent shortages
- Repetitive tasks consume critical time
According to Gartner, automation can reduce incident response time by up to 80%.
What this really means is scale. Automation allows security operations to keep up with attack volume without increasing headcount.
Built-in IT Risk Management Solutions for Decision Clarity
Security without context leads to poor decisions. An IT security solution must include IT risk management solutions that align security findings with business impact.
Capabilities to expect:
- Risk scoring based on asset criticality
- Mapping threats to business functions
- Compliance and reporting alignment
Why this matters:
- Not all alerts are equal.
- Decision-makers need prioritization based on impact, not volume.
Strong enterprise IT security solutions translate technical signals into business-relevant insights.
Open Architecture and Integration Flexibility in an IT Security Solution
No enterprise operates in isolation. A modern IT security solution must integrate with existing cybersecurity tools and infrastructure.
Key requirements:
- API-driven architecture
- Integration with SIEM, SOAR, EDR, and third-party tools
- Support for custom workflows
Why this matters:
- Tool sprawl is a reality.
- Replacing everything is not feasible.
The goal is orchestration, not replacement. Effective security operations platforms act as a central nervous system for security operations.
Where NetWitness Fits in This Equation
NetWitness delivers a unified IT security solution designed around visibility, detection, and response.
What stands out:
- Deep packet inspection and full network visibility.
- Integrated SIEM, NDR, and endpoint capabilities.
- Advanced threat detection and response workflows.
- Support for hybrid and cloud environments.
This, in essence, translates to clarity of operations. Teams would be able to work with a consistent platform that would link detection, investigation, and response together without needing to use multiple cybersecurity products.
NetWitness closely follows NIST and CISA standards by emphasizing continuous monitoring and incident response.
Conclusion
A strong IT security solution does more than detect threats. It enables clarity, speed, and control. The capabilities outlined here are not optional anymore. They define whether an organization can respond to modern threats effectively or stay stuck reacting too late.
Here’s the bottom line: consolidation, visibility, and intelligence drive outcomes. The right enterprise IT security solutions don’t just protect systems. They enable confident decision-making under pressure.
If your current setup still relies on fragmented tools and manual processes, it may be time to rethink the foundation.
Frequently Asked Questions
1. What are enterprise IT security solutions?
Enterprise IT security solutions refer to software solutions designed to secure an organization’s entire IT ecosystem. They involve the integration of several cybersecurity solutions within one platform.
2. What are the key capabilities of a strong IT security solution?
An effectively created IT security solution comprises of a number of features, including but not limited to centralization of visibility, threat detection/response capabilities, security monitoring tools, network security, cloud security, automation tools and risk management tools.
3. Why is centralized visibility important in IT security?
Centralized visibility enables security personnel to observe all areas of their environment via one single platform (the solution). Without the use of centralized visibility, there is hidden threat within silos, thus increasing time-to-detect and data-exposure risk.
4. How can enterprises choose the right IT security solution?
When choosing an IT Security Solution, Enterprises must assess the compatibility of the security solution with regard to other systems the Enterprise already operates; determine whether the Security Solution can operate in a hybrid environment; determine whether the security solution provides real-time visibility; and determine whether the security solution supports/responds quickly to various types of incidents. They should also examine the scalability/automatic capabilities of the security solution.
5. What challenges do enterprises face in implementing security solutions?
Organizations face numerous challenges when implementing Security Solutions, including fragmentation of tools; challenges in integration of security solutions; shortage of technical/resources to manage security solutions; and excessive alerts generated by security solutions. Good Enterprise IT security solutions address these issues via automation and a unified view of the organization.
6. How do cybersecurity solutions improve threat detection and response?
Modern cybersecurity solutions leverage behavioral analytics, artificial intelligence and machine learning while providing real-time monitoring to help you detect and prevent threats from growing into major problems. In addition, modern cybersecurity solutions also have built-in response features that aid in the swift containment of any threats and mitigating any harm caused by an attack.
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.