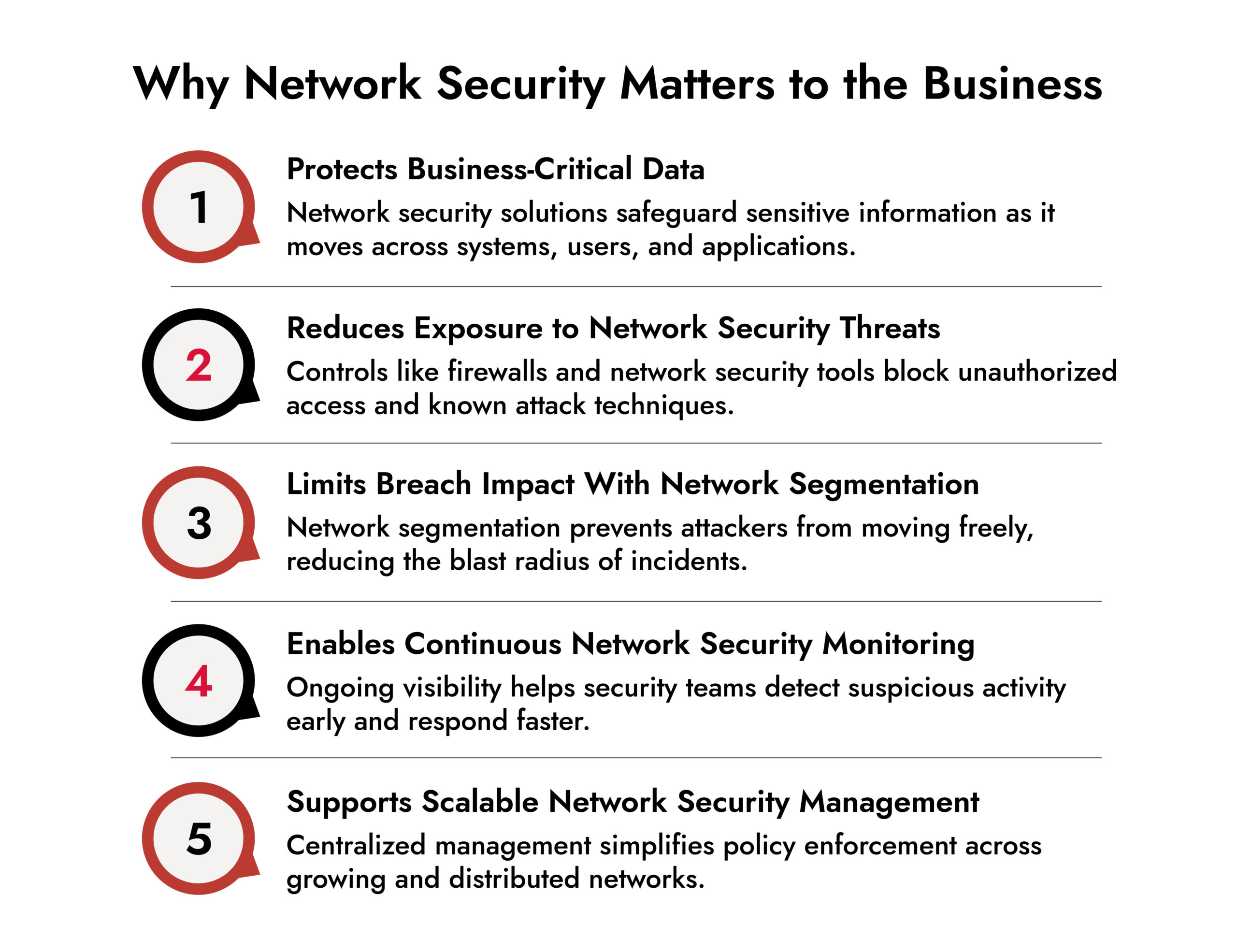
Why does your organization need network security?
Organizations need network security to protect critical data, applications, and operations from evolving network security threats. As networks expand across cloud, remote users, and third parties, network security solutions help control access, enable network security monitoring, reduce lateral movement through network segmentation, and support effective network security management to minimize downtime, data loss, and business disruption.
Introduction
Modern networks carry everything an organization depends on. Business data, customer information, applications, and internal communications all move across the network. If that network is compromised, attackers don’t just steal data. They disrupt operations, move laterally, and often stay hidden for long periods.
Network security exists to prevent that. It is a layered approach that controls access, monitors activity, protects data, and limits the impact of attacks when something slips through.
What Is Network Security?
Network security is the combination of technologies, policies, and processes used to protect a network from unauthorized access, misuse, disruption, and data loss.
At a practical level, network security focuses on three core goals:
- Protect access so only trusted users and devices can connect
- Maintain visibility into what is happening on the network
- Limit damage by containing threats quickly
This is why effective network security solutions are never built around a single tool. They rely on multiple controls working together.
Why Network Security Is Important
Network security threats have changed significantly over the last decade. Attackers no longer rely on loud exploits or obvious malware. They use stolen credentials, legitimate tools, and encrypted traffic to blend in.
This makes network security critical for several reasons:
- Networks are now distributed across cloud, remote users, and third parties
- A single compromised endpoint can expose the entire environment
- Downtime and data loss have direct financial and reputational impact
Strong network security management reduces risk, improves resilience, and gives security teams the visibility they need to respond quickly.
The Different Types of Network Security
Each type of network security plays a specific role. Bullets help highlight the purpose, but the explanation shows how each control actually protects the network.
1. Network Access Control (NAC)
Network Access Control determines who and what can connect to the network.
- Device and user validation
NAC checks device identity, user credentials, and security posture before granting access. This helps block unknown or non-compliant devices.
- Reduced attack surface
By limiting access at the entry point, NAC prevents compromised endpoints from becoming an easy way into the network.
NAC is especially important in environments with remote work, contractors, and unmanaged devices.
2. IT Security Policies
IT security policies define how network security is applied and enforced.
- Clear rules for access and usage
Policies specify who can access what, under which conditions, and from where.
- Consistency during incidents
When an incident occurs, policies guide response actions and prevent confusion or delay.
Without strong policies, even advanced network security solutions are applied inconsistently.
3. Application Security
Application security protects the software that runs on the network.
- Protection against application-level attacks
This includes securing web applications and APIs that attackers often target first.
- Reduced internal exposure
A vulnerable application can give attackers legitimate access to internal systems. Application security helps close that gap.
As more business logic moves to applications, this layer becomes increasingly important.
4. Vulnerability Management
Vulnerability management focuses on identifying and fixing weaknesses before attackers exploit them.
- Visibility into exposed systems
Regular scanning helps teams understand which systems are vulnerable and why.
- Risk-based prioritization
Not all vulnerabilities are equal. Vulnerability management helps teams focus on what matters most.
This turns network security from reactive to proactive.
5. Network Penetration Testing
Penetration testing evaluates how well network security controls hold up under attack.
- Real-world attack simulation
Pen tests attempt to bypass controls the way a real attacker would.
- Validation of existing defenses
The results show whether firewalls, segmentation, and monitoring actually work together.
Penetration testing reveals gaps that automated tools often miss.
6. Data Loss Prevention (DLP)
Data Loss Prevention protects sensitive data as it moves across the network.
- Monitoring data movement
DLP tools track files, emails, and uploads to prevent unauthorized sharing.
- Reducing insider and accidental risk
Many data leaks happen by mistake. DLP helps prevent those incidents.
DLP is critical for organizations handling regulated or sensitive information.
7. Antivirus Software
Antivirus software provides baseline protection against known threats.
- Detection of common malware
Signature-based detection stops a large volume of low-effort attacks.
- Reduced background noise
Blocking common threats allows teams to focus on more advanced network security threats.
Antivirus is not sufficient alone, but it remains a necessary layer.
8. Endpoint Detection and Response (EDR)
EDR expands endpoint security beyond basic malware detection.
- Behavior-based monitoring
EDR looks for suspicious actions rather than known signatures.
- Investigation and response capabilities
Security teams can analyze incidents and take action directly from the endpoint.
EDR is critical because endpoints are often the first point of compromise.
9. Email Security
Email security protects users from one of the most common attack vectors.
- Phishing and malware prevention
Email security tools analyze messages for malicious intent.
- Reduced initial compromise
Fewer successful phishing attacks mean fewer attackers inside the network.
Strong email security lowers overall network security risk.
10. Wireless Security
Wireless security protects networks that operate beyond physical boundaries.
- Secure authentication and encryption
These controls prevent unauthorized access to Wi-Fi networks.
- Detection of rogue access points
Monitoring helps identify unauthorized wireless devices.
Without wireless security, attackers can bypass physical controls entirely.
11. Intrusion Detection and Prevention Systems (IDS/IPS)
IDS and IPS monitor network traffic for malicious activity.
- Detection of suspicious patterns
IDS alerts teams to potential attacks or misuse.
- Active blocking of threats
IPS can stop malicious traffic before it causes damage.
These systems add depth to network security monitoring.
12. Network Segmentation
Network segmentation divides the network into controlled zones.
- Limited lateral movement
Segmentation prevents attackers from moving freely once inside.
- Reduced blast radius
Even if one segment is compromised, others remain protected.
Segmentation is one of the most effective ways to reduce breach impact.
13. Security Information and Event Management (SIEM)
SIEM centralizes security data across the network.
- Log and event correlation
SIEM connects data from multiple sources to reveal patterns.
- Faster detection and investigation
Centralized visibility improves response time and accuracy.
SIEM is a cornerstone of modern network security management.
14. Web Security
Web security protects users from web-based threats.
- Blocking malicious websites
URL filtering reduces exposure to known threats.
- Protection from unsafe downloads
Web inspection helps stop malware delivery.
Web security complements email and endpoint protection.
15. Multifactor Authentication (MFA)
MFA strengthens identity-based security.
- Protection against stolen credentials
Even if passwords are compromised, MFA blocks access.
- Reduced account takeover risk
MFA addresses one of the most common network security threats.
It is one of the simplest and most effective controls available.
16. Virtual Private Network (VPN)
VPNs secure remote access to the network.
- Encrypted communication
VPNs protect data as it travels over public networks.
- Controlled remote connectivity
Access can be limited and monitored.
VPNs remain widely used, especially with network security providers for small business environments.
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.
How These Network Security Types Work Together
Individually, each type of network security solves a narrow problem. Together, they determine whether an organization can actually stop an attack or just document it after the damage is done.
The key idea is layered defense with shared context. Attackers don’t move in straight lines, so defenses can’t live in silos.
Here’s how these controls work together across a typical attack lifecycle.
1. Preventing Unauthorized Access at the Entry Point
The first layer focuses on stopping attackers before they get in.
- Network Access Control, Multifactor Authentication, and IT security policies work together to control who can connect and under what conditions.
- Email security and web security reduce the likelihood of phishing-based entry, which is still the most common initial access method.
- VPNs and secure remote access controls protect users connecting from untrusted networks.
If these layers do their job, many attacks never progress beyond the first step. But prevention alone is never enough.
2. Reducing Exposure When Prevention Fails
Assume a credential is stolen or a device is compromised. This is where containment matters.
- Network segmentation limits where an attacker can go next, preventing unrestricted lateral movement.
- Application security ensures that even authenticated access does not automatically translate into system-level control.
- Wireless security prevents attackers from bypassing internal controls through unsecured access points.
This layer doesn’t stop compromise. It limits blast radius. That distinction matters.
3. Detecting Suspicious Activity Early
Once attackers are inside, detection speed becomes the difference between a minor incident and a major breach.
- IDS/IPS identify suspicious traffic patterns and exploitation attempts.
- Endpoint Detection and Response detects abnormal behavior on compromised devices.
- Network security monitoring provides visibility into east-west traffic that perimeter tools miss.
These tools generate signals. But signals alone are not insight.
4. Turning Signals into Context and Action
Detection tools are only effective when events are connected.
- SIEM aggregates logs, alerts, and telemetry from across the network, endpoints, applications, and access layers.
- Correlation reveals patterns such as credential misuse followed by lateral movement and data access.
- Vulnerability management adds context by showing whether suspicious activity aligns with known weaknesses.
This is where network security shifts from alert-driven to investigation-driven.
5. Limiting Data Exposure and Business Impact
Even during an active incident, damage can still be controlled.
- Data Loss Prevention helps prevent sensitive data from leaving the network.
- EDR response actions isolate compromised endpoints.
- Segmentation controls prevent attackers from reaching high-value systems.
At this stage, network security is no longer about stopping an attack. It’s about preserving business continuity.
Conclusion
Network security is often misunderstood as a shopping list of products. Firewalls, antivirus, SIEM, EDR, VPN. Buy enough tools, and the network should be safe.
That approach no longer works.
Modern networks are dynamic, distributed, and constantly changing. Attackers exploit the gaps between controls, not the controls themselves. This is why effective network security management focuses on how layers interact, not how many exist.
The most resilient organizations take a different approach:
- They control access aggressively
- They assume compromise is possible
- They limit lateral movement by design
- They prioritize visibility over volume
- They integrate detection with response
Whether you’re evaluating enterprise-grade network security solutions or working with network security providers for small business environments, the goal is the same.
Build a network security architecture where prevention, detection, and response reinforce each other. Not because it looks good in a diagram, but because when something goes wrong, and it will, the network can absorb the hit and keep running.
Frequently Asked Questions
1. How do I find my network security key?
The network security key usually refers to your Wi-Fi password. It can be found on the router label, router settings, or saved network settings on connected devices.
2. How do firewalls contribute to network security?
Firewalls control incoming and outgoing traffic based on defined rules, reducing exposure to unauthorized access and common network security threats.
3. How does network segmentation improve security?
Network segmentation limits lateral movement by isolating systems, reducing the impact of breaches and preventing attackers from spreading.
4. Which types of network security help detect advanced threats?
IDS/IPS, SIEM, network security monitoring tools, and EDR are most effective at detecting advanced and stealthy attacks.
5. How should organizations choose the right network security types?
Organizations should assess risk, prioritize visibility, and select layered network security solutions that align with their size, environment, and operational capacity.
If you want, I can now adjust keyword density, tighten this to a specific word count, or tailor it toward small business or enterprise audiences.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.