What are the various deployment models available for SIEM (Security Information Event Management) solutions?
SIEM solutions can be utilized as on-site, cloud-hosted, or mixed platforms. On-premises SIEM (Security Information Event Management) gives complete control over data and infrastructure, cloud SIEM delivers scalability and easier management, while hybrid SIEM merges both to facilitate compliance, centralized security event oversight, and visibility across on-prem and cloud settings.
Introduction
Security teams don’t suffer from a lack of data. They suffer from too much of it.
Every application, endpoint, cloud workload, and network device continuously generates logs. Without the right security event and incident management strategy, teams lose visibility, investigations slow down, and critical threats slip through unnoticed.
This is where a modern SIEM solution changes the equation.
A SIEM platform centralizes telemetry, correlates activity across environments, and transforms raw security data into actionable intelligence. Instead of manually reviewing disconnected alerts, analysts gain contextual visibility into threats, insider activity, suspicious behavior, and attack progression in real time.
Today’s SIEM tools in cyber security are no longer limited to log collection. They now support automation, behavioral analytics, advanced threat detection, compliance reporting, and accelerated incident response.
This blog breaks down the major SIEM deployment models, explains how SIEM architecture impacts security operations, and highlights the SIEM capabilities organizations should prioritize when evaluating modern security platforms.
What SIEM Solutions Actually Do
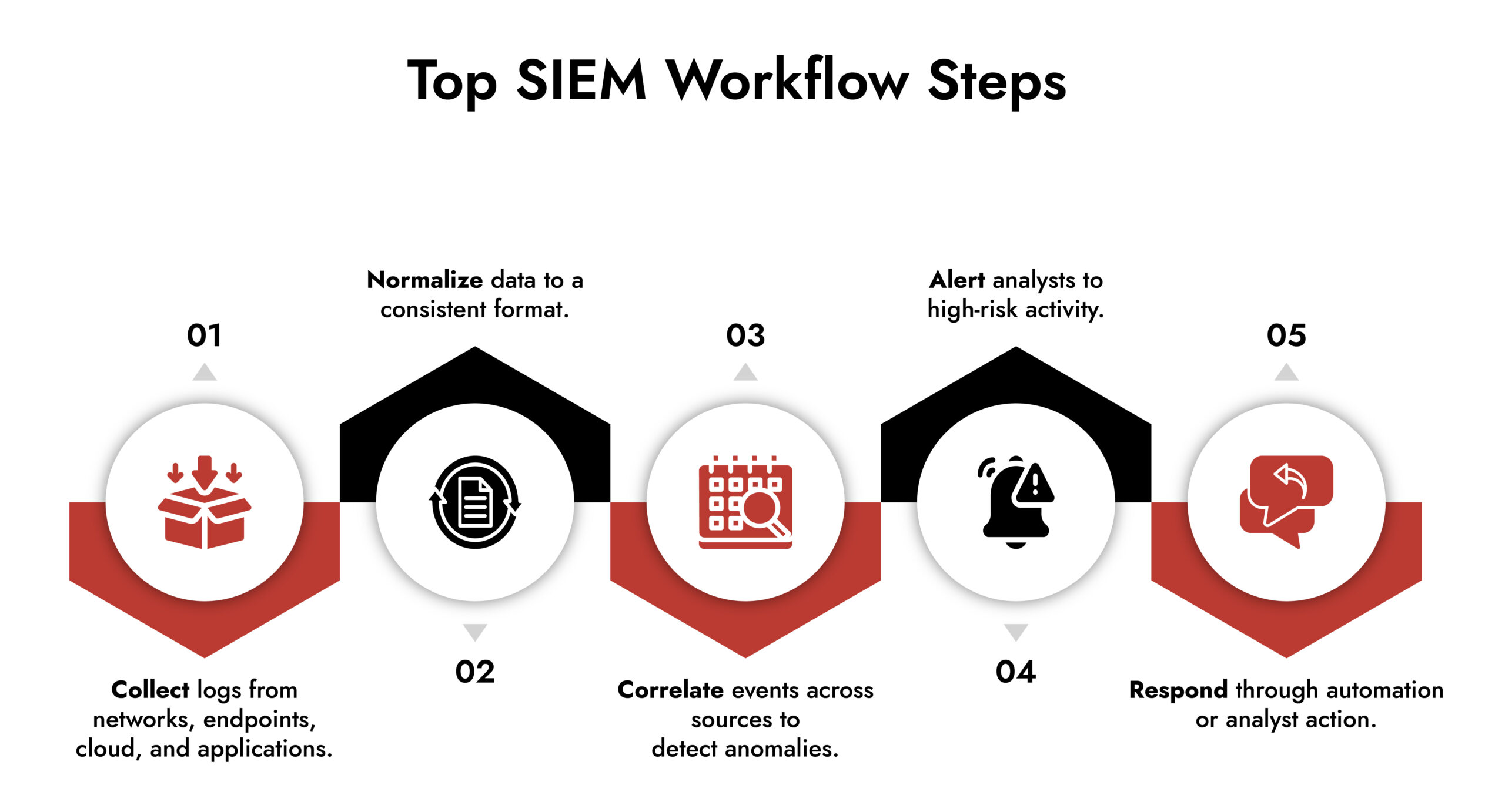
At its core, security event management revolves around awareness and context.
A security information event management (SIEM) system collects logs from network devices, endpoints, cloud resources, and applications. It standardizes the data, connects activities from different sources, and emphasizes behaviors that appear suspicious only when considered collectively.
This is where security log management stops and real analysis begins. Logs alone are historical records. A SIEM analyzes them in real time, helping teams understand what matters now, not after an incident review.
Modern SIEM cyber security platforms also automate parts of detection and response. That shift matters because attackers move faster than manual processes can keep up with.
3 Types of SIEM Solutions
1. On-Premises SIEM Architecture
An on-premises SIEM architecture runs entirely within your own data center. You manage the hardware, storage, upgrades, and performance tuning.
This model is common in regulated industries where data control is mandatory. From a compliance standpoint, it’s straightforward. From an operational standpoint, it requires skilled teams and ongoing investment.
On-premises SIEM prioritizes control. The tradeoff is complex.
2. Cloud-Based and SIEM Cloud Security Platforms
Cloud-based or SaaS-based SIEM cloud security solutions shift infrastructure responsibility to the vendor. Scaling is easier. Updates happen automatically. Your team focuses on detection instead of maintenance.
This model works well for organizations operating in limited regions. For global enterprises, compliance is becoming more complex. Many regulations require that logs remain within national borders, which makes it essential to evaluate how cloud SIEM monitoring services handle localized data storage and processing.
3. Hybrid Security Information and Event Management (SIEM)
Hybrid SIEM deployments combine on-premises and cloud environments. Sensitive data stays local, cloud-generated data stays in the cloud, and analysis happens centrally.
For many enterprises, this is the most practical option. It supports compliance while still delivering unified visibility across environments. Analysts get context without sacrificing control.
| Deployment Type | Primary Advantage | Key Consideration | Ideal Use Case |
| On-Premises SIEM | Full control over data and infrastructure | Requires significant in-house maintenance and scaling | Highly regulated industries needing strict data residency |
| Cloud-Native SIEM | Rapid deployment and elastic scaling (best suited for a single region) | Regional privacy laws may require logs to remain in-country, limiting cross-region collection | Organizations operating mainly within one region or with localized compliance needs |
| Hybrid SIEM | Keep on-prem data on-prem and cloud logs in the cloud, but analyze all from a single pane of glass | Requires careful integration to maintain unified visibility and compliance | Enterprises balancing regulatory requirements with the need for centralized analysis |
Capabilities That Matter Across SIEM Services
Regardless of deployment model, effective SIEM services share a few essentials:
- Advanced analytics to surface real threats
- Automation to reduce response time
- Scalable SIEM architecture to handle growing data volumes
- Integration with EDR, NDR, and SOAR to strengthen SIEM monitoring services
- Built-in reporting to support compliance and audits
If these aren’t in place, deployment choice won’t compensate.
NetWitness SIEM within the Enterprise Security Framework
NetWitness SIEM is designed for situations where lacking visibility is not tolerable.
As a SIEM security solution designed for enterprises, it collects data from networks, endpoints, cloud services, and applications. Advanced analytics subsequently reveal threats that would typically merge with regular activity.
Analysts operate from a consolidated perspective rather than toggling between tools, leading to quicker decision-making and improved SIEM cyber security results.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.

Core Advantages of NetWitness SIEM Solutions
Sophisticated analysis and behavior recognition
Machine learning and behavioral analytics detect anomalies that conventional security event management tools overlook, such as insider threats and initial-stage attacks.
Thorough integration throughout the security environment
Native integrations link NetWitness with EDR, NDR, and SOAR platforms, enhancing comprehensive SIEM monitoring services and facilitating automated responses.
Rapid-scale inquiry
Indexed data lake features enable analysts to swiftly search large quantities of security log management data in seconds, significantly decreasing investigation time.
Adaptable, business-ready SIEM framework
NetWitness facilitates on-premises, cloud, and hybrid setups, enabling organizations to tailor SIEM architecture to meet compliance and operational requirements.
Integrated compliance and reporting
Ready-made reports for PCI DSS, HIPAA, GDPR, and SOX streamline audits and lessen manual workload.

Choosing the Right SIEM Deployment Strategy
Choosing a SIEM solution is no longer just a compliance decision.
The right SIEM platform becomes a central layer for threat detection, analytics, visibility, and response orchestration.
Whether organizations choose cloud-native, hybrid, on-premises, or fully managed SIEM deployment services, the priorities remain the same:
- Visibility
- Detection accuracy
- Automation
- Scalability
- Integration
NetWitness delivers these capabilities through a flexible SIEM architecture built for modern enterprise environments.
Frequently Asked Questions
1. What is a SIEM security tool?
A SIEM security tool is a security information event management platform that collects, correlates, and analyzes logs to detect threats and support incident responses.
2. What is the relationship between SIEM tools and playbooks?
SIEM tools collect, analyze, and correlate security events, while playbooks automate predefined response actions. Together, they improve SIEM incident management by accelerating investigations, reducing manual effort, and standardizing response workflows across security operations.
3. What’s the top SIEM for operational technology?
The best SIEM platform for operational technology environments depends on visibility, protocol support, and integration depth. Platforms like NetWitness are often used because they combine network visibility, behavioral analytics, and enterprise-scale SIEM capabilities across IT and OT environments.
4. What are the key differences between leading SIEM products?
Leading SIEM products differ in analytics maturity, scalability, automation, deployment flexibility, compliance support, and integration capabilities. Some SIEM tools focus heavily on cloud monitoring, while others prioritize deep network visibility and advanced threat detection.
5. Which SIEM platforms prioritize actionable alerts over raw log data?
Modern SIEM solutions increasingly prioritize contextual analytics over raw log aggregation. Platforms with AI-driven detection, behavioral analytics, and automated enrichment help reduce alert fatigue and surface actionable incidents faster.
6. Are there SIEM tools with advanced analytics for insider threat detection?
Yes. Many enterprise SIEM tools in cyber security now include behavioral analytics and machine learning capabilities specifically designed to detect insider threats, privilege misuse, credential abuse, and anomalous user behavior.
Evaluate Your SIEM Strategy with Confidence
Use a structured, expert-driven checklist to assess next-gen SIEM platforms. Understand which capabilities matter most for visibility, detection speed, and operational efficiency. Compare vendors effectively and choose a SIEM that scales with your business and security needs.