Machine Learning-Based Threat Detection Explained
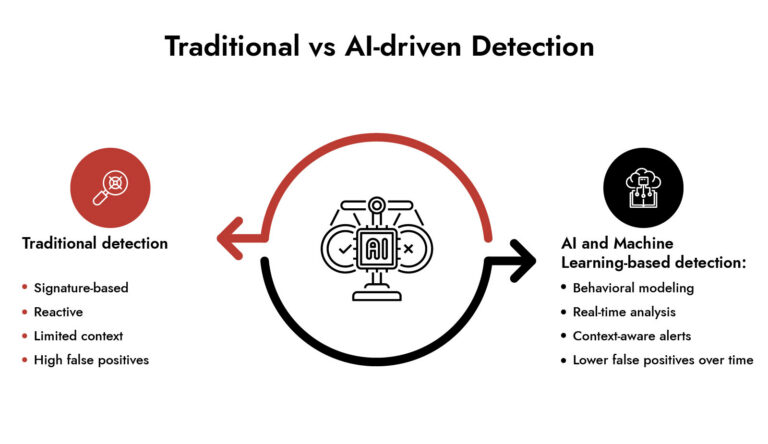
Artificial Intelligence and Machine Learning enable threat detection through the use of Machine Learning-based techniques for the detection of cyber threats. It creates a baseline of normal behaviour from an ongoing analysis of massive amounts of security data to identify patterns that vary from this baseline. It does not rely solely upon previously identified signatures, instead, it builds a dynamic baseline of activity over time across users, devices, and networks, which provides a method to create an alert when an event or activity occurs that varies from the expected behaviour defined by this baseline, in real time. This allows for detection of unknown and new threats that would not have been detected using traditional detection techniques.
Introduction
Security teams don’t struggle because they lack data. They struggle because they drown in it.
Security teams aren’t short on data, but they’re still slow to act. According to IBM Security, the average time to identify and contain a breach is 277 days. That’s nine months of attacker dwell time inside enterprise environments, often without triggering a single high-confidence alert. This is exactly where artificial intelligence and machine learning change the equation.
Modern threats don’t announce themselves. They blend in. They imitate normal behavior. And they evolve faster than manual rule updates can keep up. Traditional detection methods break under this pressure. What replaces them is a system that learns continuously.
NetWitness applies Artificial Intelligence and Machine Learning to shift detection from static rules to adaptive intelligence. Instead of asking “Do we know this threat?”, the system asks “Does this behavior make sense?”
That shift is what separates reactive security from real-time threat detection.
Artificial Intelligence and Machine Learning in Cybersecurity Threat Detection
Pattern recognition is what AI & ML brings into cybersecurity – the ability to analyze huge volumes of data in order to recognize abnormalities that cannot be detected by humans or signature-based detection systems.
In practice, here are three important aspects for which AI & ML technology provides great help:
- Detection of previously unknown or ‘zero day’ attacks.
- Decreasing alerts fatigue by prioritizing them.
- Identification of behavior abnormalities among people and systems.
This shift is no longer theoretical. According to Ponemon Institute, nearly 68% of organizations experienced at least one zero-day attack in the past year. That makes behavior-based detection a requirement, not an enhancement.
Instead of waiting for indicators of compromise, systems trained on Artificial Intelligence and Machine Learning analyze behavior in motion. They build baselines of “normal” activity and continuously refine them as environments evolve.
How NetWitness Uses Artificial Intelligence and Machine Learning for Unknown Threats
NetWitness uses AI and ML in their detection pipeline to discover unrecognized threats based on behavior without any pre-established signatures.
Here is an example of how this operates in the field:
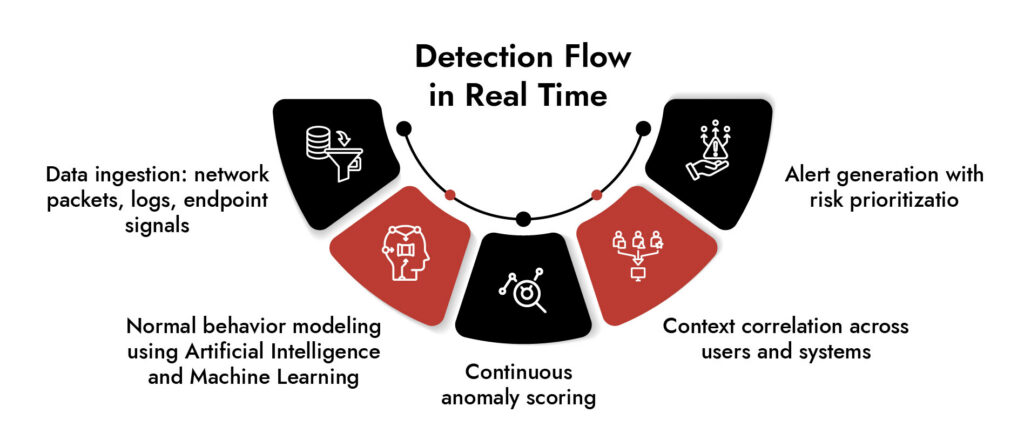
The solution continuously collects traffic, logs, endpoint indicators, and telemetry from cloud services. It then correlates that collection in real-time with the application’s AI/ML models.
The platform does not alert on a single event but, instead, reconstructs an entire set of attacks, which is critical since most attacks aren’t just one alert in isolation.
Key capabilities include:
- Behavioral clustering using Artificial Intelligence and Machine Learning
- Automated anomaly detection across network sessions
- Risk scoring based on deviation from baseline behavior
- Continuous learning from evolving traffic patterns
What makes this effective is not just detection, but context. A login attempt alone means little. A login attempt followed by unusual data movement across encrypted channels changes the story completely. This is where Artificial Intelligence and Machine Learning adds intelligence, not just alerts.
Machine Learning Threat Detection with Behavioral Analytics and Network Traffic Analysis
Machine learning threat detection works best when combined with behavioral analytics cybersecurity and deep network visibility.
NetWitness applies Artificial Intelligence and Machine Learning to both structured and unstructured telemetry, especially network traffic analysis. This allows it to detect threats hidden inside encrypted or fragmented data flows.
Instead of relying on static thresholds, the system builds behavioral fingerprints. These fingerprints evolve over time using Artificial Intelligence and Machine Learning, which helps detect:
- Lateral movement across systems
- Suspicious privilege escalation patterns
- Unusual data exfiltration behaviors
- Stealthy command-and-control communication
Behavioral analytics cybersecurity becomes significantly stronger when powered by continuous Artificial Intelligence and Machine Learning training loops. The system doesn’t just learn once. It learns constantly.
How Artificial Intelligence and Machine Learning Detect Unknown Threats
Data Sources Powering Artificial Intelligence and Machine Learning Models
Artificial Intelligence and Machine Learning is only as strong as the data it learns from.
NetWitness feeds its models with diverse telemetry sources:
- Full packet capture from network traffic analysis
- Endpoint behavioral logs
- Cloud workload telemetry
- Authentication and identity data
- Threat intelligence feeds
Each dataset strengthens the Artificial Intelligence and Machine Learning model’s ability to distinguish between normal and suspicious activity.
Real-Time Advanced Threat Detection and Zero-Day Discovery
The ability to identify an unknown anomaly quickly determines advanced threat detection capability.
Artificial Intelligence and Machine Learning come into play during such scenarios of zero-day detection.
As against identifying a known pattern, NetWitness identifies deviations from behavioral analysis. When a certain process behaves anomalously, it gets flagged by Artificial Intelligence and Machine Learning.
Why Machine Learning Improves Detection Accuracy
Why Artificial Intelligence and Machine Learning Matters for Modern Security Operations
Artificial Intelligence and Machine Learning changes how security teams operate at scale.
Instead of manually tuning thousands of rules, teams rely on adaptive models that evolve with the environment. This reduces noise and improves decision quality.
Key advantages:
- Faster detection of unknown threats
- Reduced alert fatigue in SOC environments
- Improved incident triage accuracy
- Continuous adaptation to new attack techniques
NetWitness Perspective: Where Artificial Intelligence and Machine Learning Becomes Operational
NetWitness applies Artificial Intelligence and Machine Learning as an embedded intelligence layer across its platform.
- Analysts see prioritized threats, not raw noise
- Attack paths are reconstructed automatically
- Network traffic analysis reveals hidden behaviors
- Behavioral analytics cybersecurity strengthens investigations
Conclusion
Cybersecurity is not only about gathering more information anymore, it’s about analyzing the behavior on machine speed.
AI and ML make it possible by converting unstructured telemetry data into intelligent insights. From behavioral security to network traffic analysis in real time, this technology creates an evolving detection layer that keeps up with the changes on the threat horizon.
NetWitness implements AI and ML to uncover the unknown threats at early stages.
Unmask GenAI Threats — Get Ahead of the Curve

Frequently Asked Questions
1. How does NetWitness use machine learning in cybersecurity?
NetWitness utilizes AI and machine learning to assess telemetry data from network, endpoint, and cloud sources in real-time to identify abnormal behavior.
2. What is machine learning-based threat detection?
Machine learning based threat detection is when Artificial Intelligence and Machine Learning compares suspicious behaviour with previously learned behaviour to determine if it is suspicious.
3. How does machine learning support zero-day threat detection?
Machine learning based threat detection will alert the user to changes in behavior or deviations from the norm without having to compare against a preestablished set of definitions (signatures) for an attack, making it possible to identify an unknown attack much earlier than if the user was using traditional detection methods.
4. What data sources are used for machine learning in cybersecurity?
Network traffic, endpoint logs, cloud telemetry, identity data, and threat intelligence feeds.
5. Why is machine learning important for modern cybersecurity strategies?
Because it enables adaptive, real-time detection of evolving threats that traditional systems miss.




