Key Takeaways
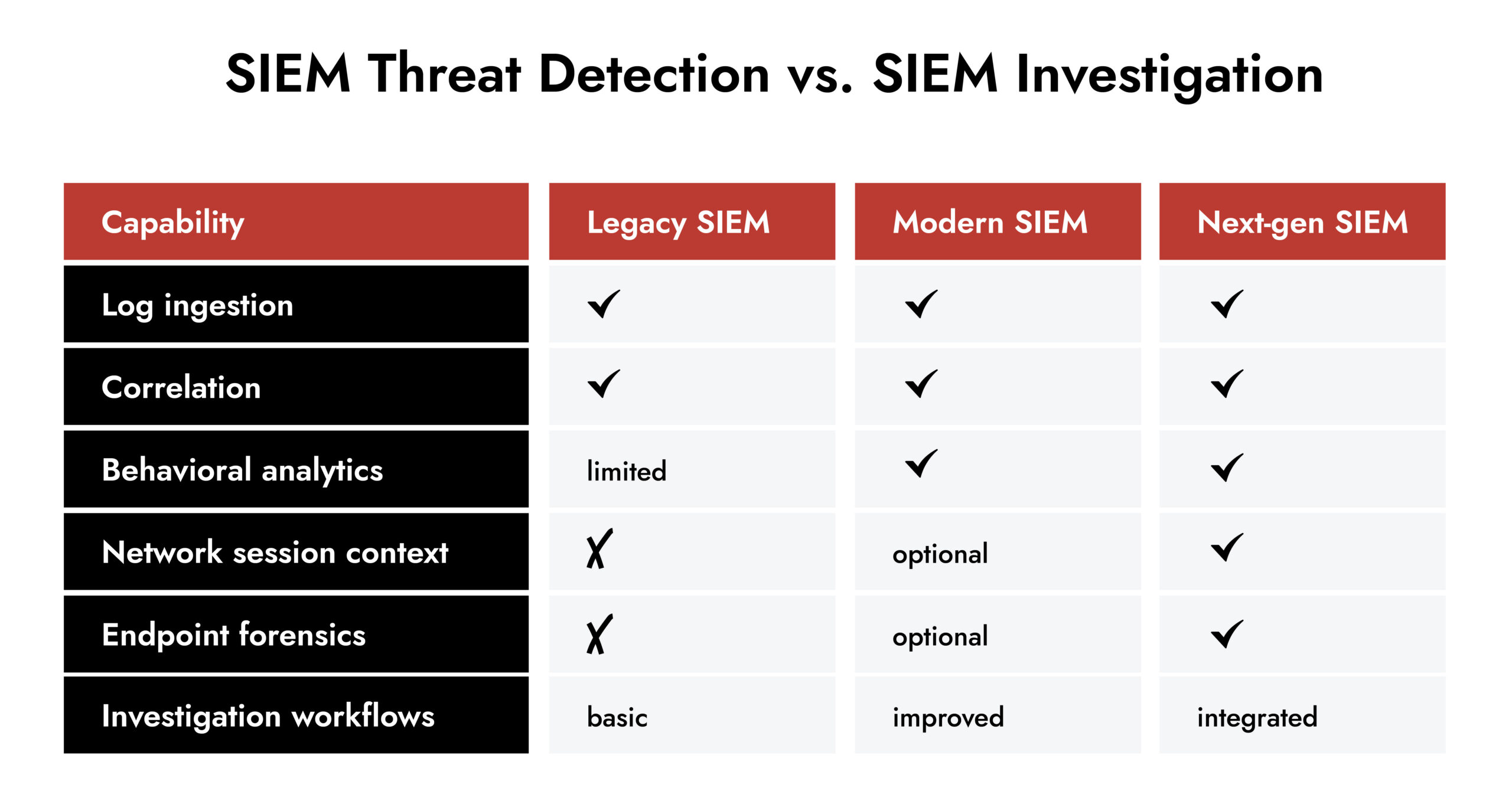
- SIEM tools have shifted from storage engines to investigation engines focused on context, behavior, and evidence.
- Integration with other telemetry (network, endpoint, cloud) now defines threat signal quality, not just log ingestion.
- Hybrid and cloud support are baseline expectations for enterprise SIEM solutions in 2026.
- NetWitness combines deep session context with enriched logs and analytics, offering superior investigation fidelity.
- Real-world data shows SIEM alone can miss critical techniques, which is why layered visibility matters.
Introduction
The main purpose for SIEM is to revolve around log aggregation and display it in a dashboard format. By 2026, this will have become a common (baseline) expectation of the product. What is most important is what you can do with this mountain of signals to create high confidence about the information contained so that either a human or automated workflow can utilize it.
Due to the rate of growth and change in the methods, techniques, and tooling available to attackers today, they are quicker and much harder to detect. The introduction of hybrid work patterns, fragmented cloud service models, and remote work enables the creation of many “blind spots” across all organization infrastructures that cannot be filled solely with traditional SIEM. The best tools in SIEM today allow for noise reduction, the unification of various signals into one signal, and the representation of the actual behavior of an attacker vs. just what would appear to be an attacker.
This comparison looks at the top SIEM tools available now, the threat detection capabilities they must deliver, and where platforms diverge, especially in how they support deep investigation and response.
What Makes a Leading SIEM Tool Today
Enterprise SIEM solutions must go beyond simple correlation. Here’s what sets the leaders apart:
- Unified visibility across cloud, on-prem, endpoint, and network telemetry.
- Behavioral analytics and context enrichment that cut false positives and surface meaningful threats quickly.
- Investigation depth and forensic evidence for busy SOC teams.
- Scalable architecture that handles massive data volumes without losing detail.
Stitching logs together isn’t enough. SOC teams need the ability to answer questions like: What exactly happened after that suspicious authentication? Which assets did the attacker touch? Did data leave the network? If your SIEM can’t give you those answers quickly, it’s just a log repository with noise.
The Trends Shaping SIEM in 2026
SIEM platforms are no longer judged by how many logs they can store. They’re judged by how quickly they help a team understand an attack and decide what to do next.
Three forces are driving this shift: hybrid infrastructure, telemetry depth, and AI-assisted decision-making.
Hybrid Environments are the Default
Enterprise infrastructure now spans on-prem systems, multiple cloud providers, SaaS platforms, and remote endpoints. Each layer produces its own signals, formats, and timelines. A SIEM that only centralizes logs without context forces analysts to manually stitch together activity across environments.
Modern enterprise SIEM solutions therefore prioritize correlation across identity, network, and workload activity. Detection increasingly depends on linking actions across boundaries rather than spotting a single suspicious event.
Example: A login from a new location isn’t suspicious by itself. Login followed by cloud API access, new role assignment, and outbound data transfer. The platform must understand sequence, not just events.
Detection is Moving from Events to Behavior
Older SIEM deployments relied on static correlation rules. They worked well for known attacks but produced overwhelming alert volumes as environments grew.
The current generation focuses on behavioral patterns instead:
- how accounts typically authenticate
- how services normally communicate
- how data is usually accessed
This shift reduces false positives and exposes stealthy activity such as credential misuse or living-off-the-land techniques that rarely trigger signature-based alerts.
AI is Changing the Role of the SIEM
The most significant change isn’t ingestion speed or storage scale. It’s how the system decides what matters.
AI-enabled SIEM tools continuously analyze activity patterns and assign risk based on context. Instead of triggering alerts from thresholds, they evaluate intent. Industry research shows AI-driven SIEM platforms can prioritize critical alerts, recommend response actions, and automate remediation, reducing alert fatigue for analysts.
Operationally, the workflow now looks different:
- Anomalous event → contextual evaluation
- Confirmed suspicious behavior → prioritized incident
- High-confidence malicious activity → automated containment
The SIEM becomes a triage partner rather than an alert generator.
Response is Becoming Part of Detection
Detection without action slows security operations. Modern security information and event management platforms increasingly connect analytics with response workflows.
When high-confidence activity appears, the platform can:
- disable compromised credentials
- isolate affected hosts
- block malicious connections
- trigger investigation playbooks
This shortens response time dramatically because decisions no longer wait in analyst queues.
What These Trends Mean
Top SIEM tools are evolving from monitoring systems into decision support systems.
The goal is no longer visibility alone.
The goal is clarity.
The strongest platforms combine broad telemetry, behavioral understanding, and guided response so analysts spend time validating impact instead of filtering noise.
That shift sets the stage for why investigation depth now matters more than alert volume, and why some platforms approach SIEM differently.
It is essential for SIEM vendors to enrich their systems with additional sensors capable of acquiring supplementary data from endpoints and network traffic beyond traditional logs. Advanced AI capabilities need to be integrated to enable the optimal use of all the valuable information collected. The use of AI must support analysts’ work, without attempting to replace their essential human expertise (capacity to think out of the box).
AI can enhance operational efficiency by providing analytical support during all the investigative analyses. It can help to prioritize alerts based on their criticality and on the confidence level, which depends on all contextual data provided by complementary sensors which they become so important.
— Alessio Alfonsi, Sales Engineer, NetWitness
1. NetWitnessSIEM
NetWitness stands out because it treats threat detection as a forensic problem first, not a rules problem.
Here’s how:
- It enriches logs at capture time with metadata that goes far beyond traditional normalization, boosting context and investigation speed.
- It integrates with rich telemetry sources and supports hybrid environments without forcing sampling or summarization.
- It gives analysts access to the “why” and “how” behind alerts, not just the “what.”
Example: A privileged credential is used to access sensitive data after hours. A conventional SIEM might alert authentication. NetWitness can tie that authentication to network session details and reveal command execution or data exfiltration patterns that originated across multiple systems – all in one investigation pane. That’s evidence, not guesswork.
Teams that need defensible incident narratives – whether for regulators or executive reporting – will see the difference in hours saved and confidence gained.
2. Advanced Enterprise SIEM Platforms
There are top SIEM tools in the market that have evolved from raw log collectors into highly scalable platforms with strong data lakes, analytics, and broad connector ecosystems.
Where they challenge teams:
- They ingest large volumes of telemetry but often struggle to surface meaningful security insight from it.
- Analysts receive alerts without enough analytical context to distinguish unusual activity from actual malicious behavior.
- Investigations still require manual correlation to determine scope and impact.
In practice, the limitation isn’t visibility alone, it’s the platform’s ability to highlight real anomalies and prioritize genuine problems inside massive data streams.
3. Cloud-Focused SIEM Tools
Cloud-native SIEMs are attractive for rapid deployment and elasticity. They handle auto-scaling ingestion and make integrating cloud SaaS logs easier than traditional systems.
Benefits:
- Quick time to value for cloud environments.
- Managed infrastructure simplifies operations.
Limitations:
- Many still depend on logs and event streams without the possibility to add more context and network visibility.
- Cost models based on data volume can spike as telemetry increases.
These tools are excellent in cloud-centric stacks and complement deeper visibility platforms.
4. Managed SIEM & SIEM-as-a-Service
Organizations with limited SOC resources often turn to managed SIEM offerings (sometimes with MDR). These packages include 24/7 monitoring, initial triage, and alert management by external experts.
Strengths:
- Offloads operational burden.
- Provides expert tuning without large internal teams.
Drawbacks:
- Less control over tuning; deeper investigations typically redirect back to internal teams once analysts need evidence.
This acquisition model suits organizations that need baseline threat detection and external coverage but not fine-grained control.
5. Modular and Open Framework SIEMs
Some enterprise environments build their SIEM around flexible or open frameworks, stitching together telemetry, analytics, and custom engines.
They offer:
- Extreme flexibility and customization.
- Lower licensing ties.
They demand:
- Skilled engineers and constant maintenance.
- High operational overhead.
These are rare at scale but appear where teams need bespoke visibility pipelines.

Choosing the Right Among Top SIEM Tool
There’s no one-size-fits-all solution, but there are questions that separate strong SIEM choices from weak ones:
- Can it unify telemetry without losing detail?
- Does it support hybrid environments natively?
- Can analysts reconstruct full incidents scope with evidence, not assumptions?
- Does it reduce noise and highlight genuine risk?
Answers to these questions tell you which SIEM tools list deserves your shortlist.
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.
NetWitness: Built for Investigation, Not Just Alerting
NetWitness approaches SIEM from a different starting point. Instead of asking how many alerts a platform can generate, it asks whether analysts can reconstruct what truly happened during an attack.
At its core, NetWitness is designed around evidence-driven security operations. It combines enriched log data with network, endpoint, and behavioral telemetry to give SOC teams a single, coherent investigation surface.
How NetWitness Actually Works in Practice
NetWitness enriches data ingestion. Logs aren’t just normalized; they’re contextualized with metadata that reflects user behavior, sessions, assets, and activity patterns. This allows detections to evolve beyond static rules and simple correlations.
For example, consider a compromised service account used across multiple systems:
- Traditional SIEM flags unusual authentication events.
- NetWitness correlates those events with network sessions, showing which systems the account accessed, what protocols or vulnerabilities were used, and whether data was staged or transferred.
- Analysts can replay activity, validate intent, and determine scope without exporting data into separate tools.
This matters when dealing with lateral movement, living-off-the-land techniques, or low-and-slow attacks that don’t trip obvious alerts.
Investigation Depth That Reduces Guesswork
NetWitness supports session reconstruction and packet-level visibility alongside log analytics. This allows SOC teams to:
- Validate alerts with actual traffic and behavior
- Trace attacker actions step by step
- Confirm whether suspicious activity resulted in data exfiltration or command execution
In regulated industries, this level of detail also supports incident reporting and post-incident reviews with defensible evidence, not assumptions.
Designed for Hybrid Enterprise Environments
Modern enterprises rarely operate in a single environment. NetWitness supports hybrid infrastructures by correlating:
- On-prem logs and network data
- Cloud telemetry from infrastructure and SaaS platforms
- Endpoint activity and user behavior
This unified view helps security teams detect threats that span environments, such as compromised credentials used to pivot between cloud and on-prem systems.
Analyst Control Over Detection and Response
NetWitness doesn’t hide detection logic behind opaque models. Analysts stay in control while automation handles repetitive work.
They can:
- Tune detections based on their environment
- Build custom content aligned to internal risk models
- Integrate workflows with SOAR and response tools without losing investigative context
- Use AI assistants such as the investigative chatbot and AI SOC agent to query incidents, summarize activity chains, and accelerate triage
Instead of replacing expertise, the platform reduces the mechanical effort around investigation – retrieving context, correlating activity, and outlining likely attack paths – so analysts focus on validation and decision-making.
This balance between automation and human oversight reflects how mature SOCs actually operate.
Why This Matters in 2026
As attackers increasingly blend into normal traffic and legitimate tools, signal quality matters more than alert volume. Platforms that combine deep visibility with contextual analytics give defenders a measurable advantage.
NetWitness stands out among top SIEM tools by focusing on how incidents are investigated, proven, and resolved, not just how quickly alerts fire.
Conclusion
By 2026, top SIEM tools should CISOs need SIEMs that provide visibility into the entire enterprise and assist in reconstructing the attacker’s activity. They should also provide investigators with evidentiary proof of the attacker’s activities to react immediately.
Platforms such as NetWitness provide the level of depth and structure analysts need to make informed decisions in an accurate and timely manner.
When your team is searching for modern tools for the purpose of detection and investigatory confidence, you should look for the platforms that can provide the level of context and abundant collection of evidentiary elements through logs and throughout the enterprise through the use of networks and endpoints.
Frequently Asked Questions
1. What defines a top SIEM tool in 2026?
A top tool unifies telemetry, enriches signals with context, supports hybrid infrastructure, and empowers analysts with clear evidence for detection and response.
2. What are the key capabilities expected from leading SIEM tools?
Expect deep log enrichment, behavioral analytics, threat prioritization, investigation workflows, and integration with network and endpoint data.
3. What are the top SIEM tools for enterprise security?
Enterprise SIEM solutions combine scalable data ingestion, hybrid visibility, analytics, and forensic support to detect, investigate, and respond to threats effectively.
4. What are the best SIEM tools available for small businesses right now?
Small businesses often benefit from cloud-based or managed SIEM services that simplify deployment and reduce operational load while providing baseline detection.
5. Which SIEM tools integrate well with cloud security services?
Modern SIEMs that offer native connectors for cloud platforms and correlate those signals back into a central investigation surface integrate best.
6. How can I find SIEM tools that specialize in automated incident responses?
Look for solutions with integrated workflow automation, threat playbooks, and orchestration capabilities that trigger containment actions and triage with evidence context.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.