What should enterprises look for when choosing a SIEM solution in 2026?
Enterprises should prioritize SIEM solutions that enable complete visibility, accurate detection, and fast investigation across modern hybrid environments. The most important capabilities include:
- Unified visibility across network, endpoints, cloud, and identity systems to eliminate blind spots and provide full investigative context
- Fast threat detection and investigation workflows that help SOC teams quickly identify root cause and assess impact
- Advanced network security monitoring and telemetry correlation to detect lateral movement, command-and-control activity, and sophisticated attacks
- Scalable architecture that supports hybrid and multi-cloud environments without compromising performance or detection speed
- Strong integration and automation capabilities to work seamlessly with existing security tools and accelerate incident response
Modern SIEM platforms must go beyond log collection. They should enable security teams to detect threats earlier, investigate them thoroughly, and respond with confidence.
Introduction
Security operations have fundamentally changed.
Enterprises are no longer defending a fixed perimeter. Their attack surface now spans hybrid cloud infrastructure, remote endpoints, SaaS applications, identities, and east-west network traffic. Every login, packet, process, and API call creates telemetry. Hidden inside that telemetry are early signals of compromise.
The role of top SIEM solutions for enterprises is to capture those signals, correlate them, and enable fast, confident response.
But here’s the reality most security leaders face. Many top SIEM tools still operate like log warehouses. They generate alerts without providing investigative clarity. They show symptoms, not root cause.
Modern enterprises need SIEM platforms that deliver:
- Deep network security monitoring
- Full telemetry correlation across hybrid environments
- True unified threat detection and response
- Scalable cloud SIEM solutions
- High-confidence investigations, not alert noise
Here’s the thing most vendor comparisons miss: SIEM platforms are no longer judged by how many logs they can store they’re judged by how quickly they help a team understand an attack and decide what to do next. That’s the lens this guide uses.This guide examines the best SIEM tools for enterprises in 2026, including platforms built for real SOC operations at enterprise scale.
What Defines an Enterprise SIEM Platform in 2026
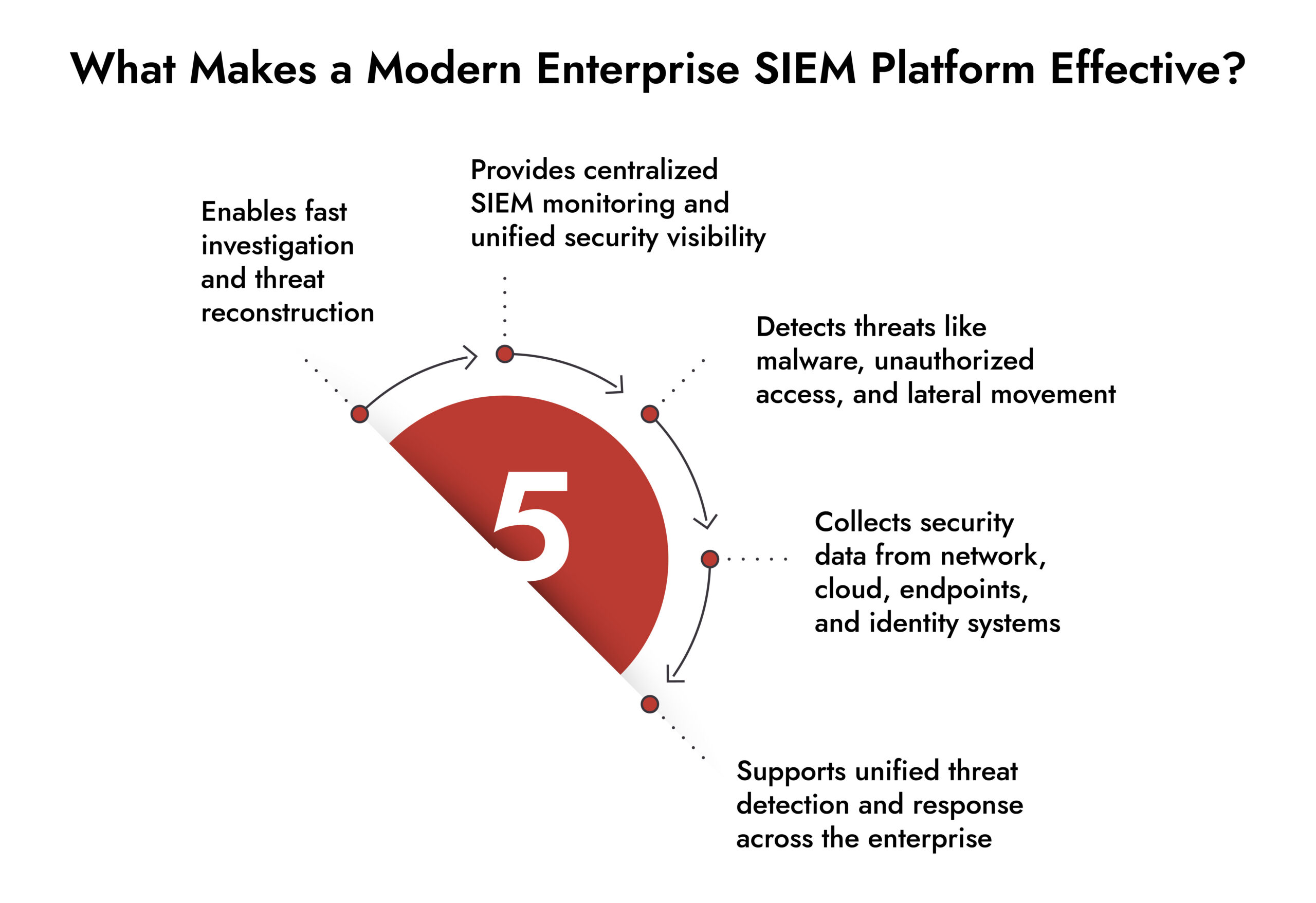
Before evaluating vendors, it’s important to understand what makes a SIEM enterprise-ready in 2026.
Enterprise-grade SIEM security solutions must provide visibility across multiple telemetry layers:
| Telemetry Type | Why It Matters |
| Network traffic | Detect lateral movement and command-and-control activity |
| Endpoint telemetry | Identify malware execution and persistence |
| Identity activity | Detect credential abuse and privilege escalation |
| Cloud workloads | Monitor SaaS, IaaS, and container environments |
| Logs and events | Provide context across systems and applications |
| Threat intelligence | Correlate known attacker behaviors |
The strongest SOC SIEM platforms unify these sources into a single investigative workflow.
This enables security teams to answer the most important questions quickly:
- How did the attacker enter?
- What did they access?
- How far did they move?
- What is the business impact?
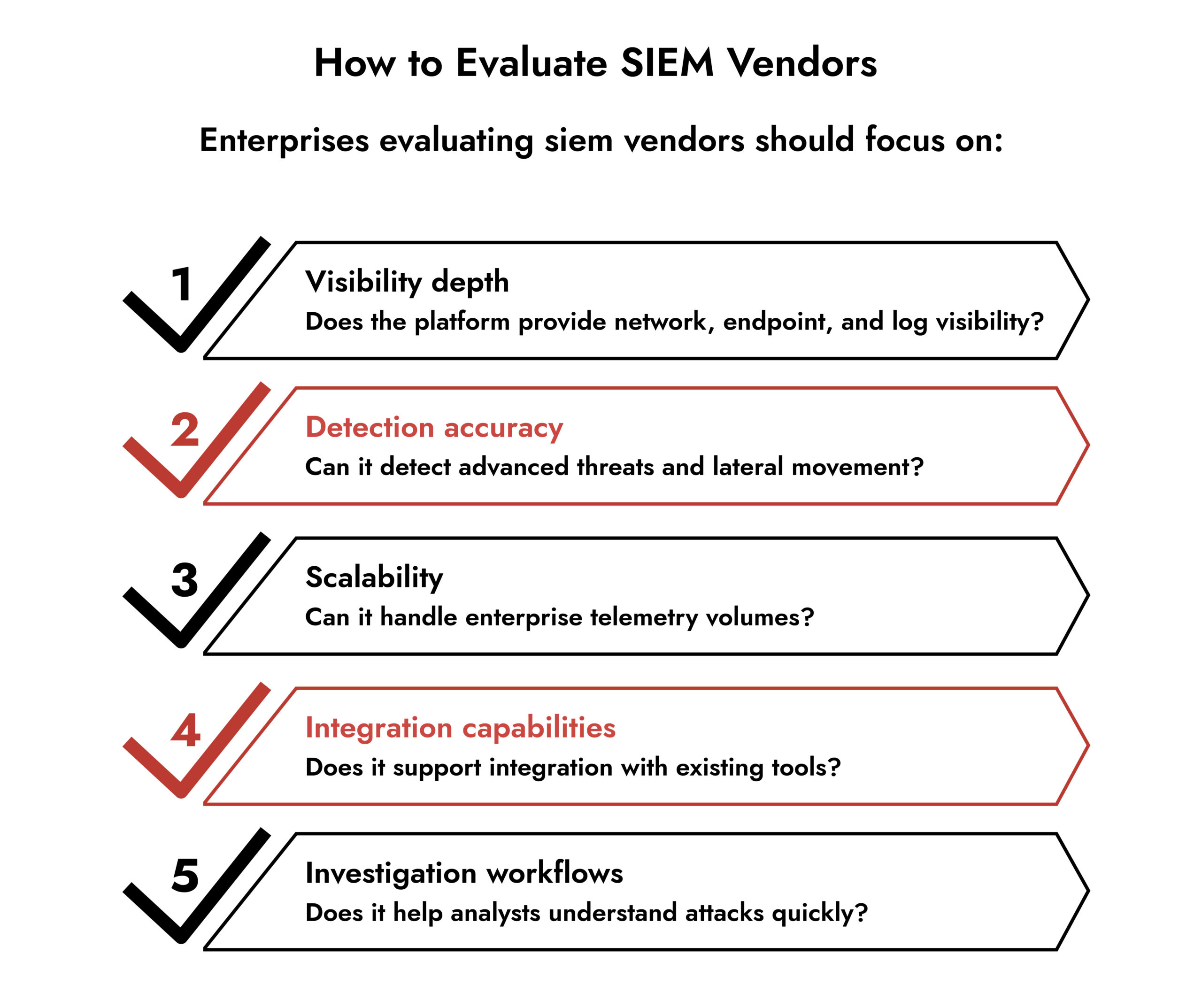
What to Prioritize When Evaluating SIEM Vendors
The telemetry coverage matters, but so does how the platform handles what it ingests. When making a confident, future-proof SIEM choice, prioritize unified log management across endpoints, networks, cloud platforms, and existing security stacks plus machine learning, behavioral analytics, and AI-driven investigation capabilities to detect sophisticated threats, reduce false positives, and accelerate root cause analysis.
Beyond features, ask the right operational question. When evaluating SIEM platforms, security leaders should ask: does this platform unify detection, investigation, and response in a single operational layer, or am I still assembling workflows across products? The answer will determine whether your team spends its time fighting threats or fighting its own tools.
A few other practical factors worth weighing:
Deployment model: Cloud-native SIEMs offer faster onboarding and lower infrastructure overhead. Self-hosted options give more control but require dedicated management resources.
Team size and expertise: Small security teams should focus on automation, alert prioritization, and UEBA for maximum impact with limited staff. Large enterprises should prioritize scalability, compliance automation, and custom rule creation to handle complex operations.
Types of SIEM tools: Modern SIEM solutions broadly fall into three categories traditional on-premises platforms (like LogRhythm), cloud-native platforms (like Microsoft Sentinel and Google Chronicle), and unified SecOps platforms that blend SIEM with XDR, SOAR, and behavioral analytics (like Cortex XSIAM and NetWitness). Knowing which type fits your environment narrows the evaluation significantly.
Top 10 SIEM Solutions for Enterprises in 2026
1. NetWitness Platform
Purpose-built for deep enterprise visibility and forensic-level investigations.
Unlike SIEM tools that rely primarily on logs, NetWitness captures and analyzes:
- Full network packets
- Logs across infrastructure
- Endpoint telemetry
- User and entity behavior
This gives SOC teams the ability to reconstruct attacks with precision.
Key capabilities:
a. Full packet capture for network visibility
Most SIEM tools analyze summaries of network traffic. NetWitness analyzes full packets, allowing security teams to see exactly what occurred during an attack.
This enables detection of:
- Command and control communication
- Data exfiltration attempts
- Lateral movement
- Encrypted threat patterns
b. Unified visibility across network, logs, and endpoints
NetWitness integrates multiple telemetry layers into one platform. This eliminates investigative blind spots and accelerates root cause analysis.
c. Advanced threat detection and investigation
Security teams can trace attacks from initial compromise to impact using unified investigation workflows.
d. Enterprise scale and performance
Designed to handle high-volume telemetry environments across hybrid infrastructure.
Best for: Enterprises that require deep visibility, threat reconstruction, and advanced investigation capabilities.
2. Microsoft Sentinel
Microsoft Sentinel is a cloud-native cloud SIEM solution built on Azure.
It provides strong visibility into:
- Azure workloads
- Microsoft 365 environments
- Identity activity through Entra ID
- Microsoft Defender security telemetry
Strengths
- Native integration with Microsoft ecosystem
- Strong cloud visibility
- Built-in automation capabilities
- Scalable cloud architecture
Best for: Cloud-first enterprises using Microsoft infrastructure.
3. Splunk Enterprise Security
Splunk is one of the most widely adopted SIEM security tools in enterprise environments.
It provides flexible log ingestion, search, and analytics.
Strengths
- Powerful search capabilities
- Large integration ecosystem
- Flexible analytics engine
- Mature threat detection workflows
Best for: Large enterprises with dedicated SOC teams.
4. IBM QRadar SIEM
IBM QRadar provides strong event correlation and compliance-focused capabilities.
It is widely used in regulated industries.
Strengths
- Strong correlation engine
- Compliance reporting capabilities
- Threat intelligence integration
- Mature enterprise deployment support
Best for: Enterprises with strict regulatory requirements.
5. Google Chronicle Security Operations
Chronicle is built on Google’s cloud infrastructure and designed for speed and scalability.
Strengths
- Extremely fast search performance
- Long-term telemetry retention
- Strong cloud analytics capabilities
- High scalability
Best for: Large-scale cloud environments.
6. Palo Alto Cortex XSIAM
Cortex XSIAM combines SIEM, XDR, and automation into one platform.
Strengths
- Automated investigation workflows
- Integrated endpoint and network telemetry
- AI-driven threat detection
- Unified security operations
Best for: Enterprises seeking automation-driven SOC operations.
7. Cisco Secure Cloud Analytics
Cisco provides strong network telemetry and behavioral analysis.
Strengths
- Strong network visibility
- Behavioral detection capabilities
- Integration with Cisco infrastructure
Best for: Enterprises with Cisco network infrastructure.
8. Exabeam Security Analytics
Exabeam focuses heavily on user behavior analytics.
Strengths
- Insider threat detection
- Behavior-based threat analysis
- Investigation timelines
Best for: Identity-driven detection strategies.
9. Securonix SIEM
Securonix provides AI-driven threat detection and analytics.
Strengths
- Behavior analytics capabilities
- Cloud-native architecture
- AI-based detection models
Best for: AI-driven security operations.
10. LogRhythm SIEM Platform
LogRhythm offers balanced SIEM functionality and automation.
Strengths
- Integrated automation
- Strong compliance reporting
- Flexible deployment options
Best for: Enterprises seeking balanced SIEM capabilities.
Evaluate Your SIEM Strategy with Confidence
Use a structured, expert-driven checklist to assess next-gen SIEM platforms. Understand which capabilities matter most for visibility, detection speed, and operational efficiency. Compare vendors effectively and choose a SIEM that scales with your business and security needs.

Enterprise SIEM Visibility and Investigation Capability Overview
| Capability | Why It Matters | NetWitness Advantage |
| Log analysis | Provides baseline visibility | Supported |
| Endpoint telemetry | Detect malware and persistence | Supported |
| Network telemetry | Detect lateral movement | Deep packet inspection |
| Threat reconstruction | Understand attack sequence | Full attack reconstruction |
| Unified investigation | Faster incident response | Integrated workflows |
| Hybrid environment support | Enterprise scalability | Fully supported |
This depth of visibility is critical for modern threat detection because most enterprise attacks unfold across multiple systems, not a single point of entry. Attackers may enter through a compromised credential, move laterally across the network, escalate privileges on endpoints, and access sensitive data in cloud workloads. Without unified visibility across these layers, security teams see only isolated alerts instead of the full attack sequence.
Deep, correlated telemetry allows SOC teams to reconstruct attacker activity, understand how the compromise occurred, identify what was impacted, and respond with precision. This reduces investigation time, improves detection accuracy, and prevents attackers from remaining undetected inside enterprise environments.
Why Enterprises Are Moving Toward Unified SIEM Platforms
A unified SIEM platform centralizes and correlates telemetry from multiple security layers including network traffic, endpoints, cloud workloads, identities, and logs into a single investigative and detection environment. Instead of operating as a standalone log management tool, a unified SIEM connects diverse telemetry sources to provide complete visibility and a single source of truth for security operations.
This unified approach allows security teams to detect threats faster, investigate incidents more accurately, and understand the full scope of attacker activity without switching between multiple tools.
Fragmented visibility creates risk.
Security teams often use separate tools for:
- Logs
- Network monitoring
- Endpoint security
- Cloud monitoring
This slows investigations and creates blind spots. Unified siem security solutions eliminate this fragmentation. They allow teams to detect threats faster and respond more effectively.
A unified SIEM platform does not necessarily replace the existing security stack; rather, it serves as an integration and a visibility layer that brings together telemetry across network, endpoint, cloud, identity, and application environments.
For enterprises, the goal is not tool consolidation on its own, but operational cohesion. A unified approach reduces investigative friction, improves cross-domain correlation, and enables analysts to pivot seamlessly across data sources without stitching context manually.
As environments grow more distributed, organizations are prioritizing platforms that enhance alerts fidelity, streamline detection workflows, and strengthen the response procedure which will ultimately improving overall SOC effectiveness and security posture.
Conclusion
The effectiveness of a SIEM platform comes down to one thing: how quickly and accurately it helps your security team understand what happened and act on it.
There is no single best SIEM tool for every organization. The right platform depends on whether you need broad compliance logging, modern cloud detection, a unified SecOps workflow, or deep customization for a mature SOC. Microsoft-heavy environments will often land on Sentinel. Mature detection engineering teams lean toward Splunk. Organizations that need forensic-grade network visibility alongside log correlation benefit most from platforms like NetWitness.
What matters most is matching the platform’s architectural philosophy to your team’s actual workflows not just checking feature boxes on a vendor sheet.
Frequently Asked Questions
1. What defines an enterprise SIEM solution in 2026?
An enterprise SIEM provides unified visibility across network, endpoint, cloud, and identity telemetry while enabling fast detection, investigation, and response.
2. How is AI changing SIEM platforms in 2026?
AI improves threat detection accuracy, reduces alert noise, and accelerates investigation workflows.
3. What challenges do enterprises face when deploying SIEM?
Common challenges include integration complexity, data volume management, and ensuring complete visibility.
4. How should enterprises evaluate SIEM vendors?
Enterprises should evaluate vendors based on visibility depth, scalability, detection capabilities, and integration support.
5. What are the best SIEM integration tools for cloud environments?
For cloud environments, the strongest SIEM tools are those with native integrations into cloud platforms rather than bolt-on connectors. Microsoft Sentinel integrates directly with Azure, Microsoft 365, and Entra ID without custom code. Google Chronicle (Security Operations) is built for petabyte-scale cloud log processing. Palo Alto Cortex XSIAM unifies cloud, endpoint, and network telemetry through a single automated platform. For organizations that need deep packet-level visibility alongside cloud log analysis, NetWitness adds network forensic depth that cloud-native SIEMs typically lack. The right choice depends on your existing cloud stack, your team’s technical depth, and whether you need compliance-grade logging, behavioral detection, or full forensic reconstruction.
Choose the Right SIEM with Confidence
Evaluate vendors using a comprehensive, expert-built checklist.
Identify must-have SIEM features for complete visibility and faster detection.
Compare capabilities to ensure scalability, automation, and integration.
Make informed decisions with NetWitness’ proven SIEM guidance.





