What is Threat Intelligence?
Threat intelligence is crucial in modern cybersecurity, enabling early threat detection and proactive risk mitigation. It transforms raw data into actionable insights, allowing organizations to monitor networks continuously, analyze detected threats, and maintain full visibility across endpoints and cloud environments. This visibility supports adaptive defense strategies against evolving cybercriminal tactics.
Platforms like NetWitness deliver real-time intelligence, improving speed and accuracy in detecting, investigating, and responding to threats.
Introduction
Cyber threat fighters face new challenges as cybercriminals improve their tactics. Organizations need strong cyber threat protection to keep sensitive data safe. Threat intelligence is key for managing cyber threats. It helps companies understand their risks and analyze their threat landscape. By using cyber threat intelligence, IT teams can create tools to spot network threats. They can also learn about attacker behaviors and respond effectively.
This guide explains how cyber threat intelligence can help. It aids in threat analysis. It also improves monitoring. Additionally, it supports cloud-based defense strategies. This enables organizations to detect and respond to threats quickly.
Understanding Threat Intelligence
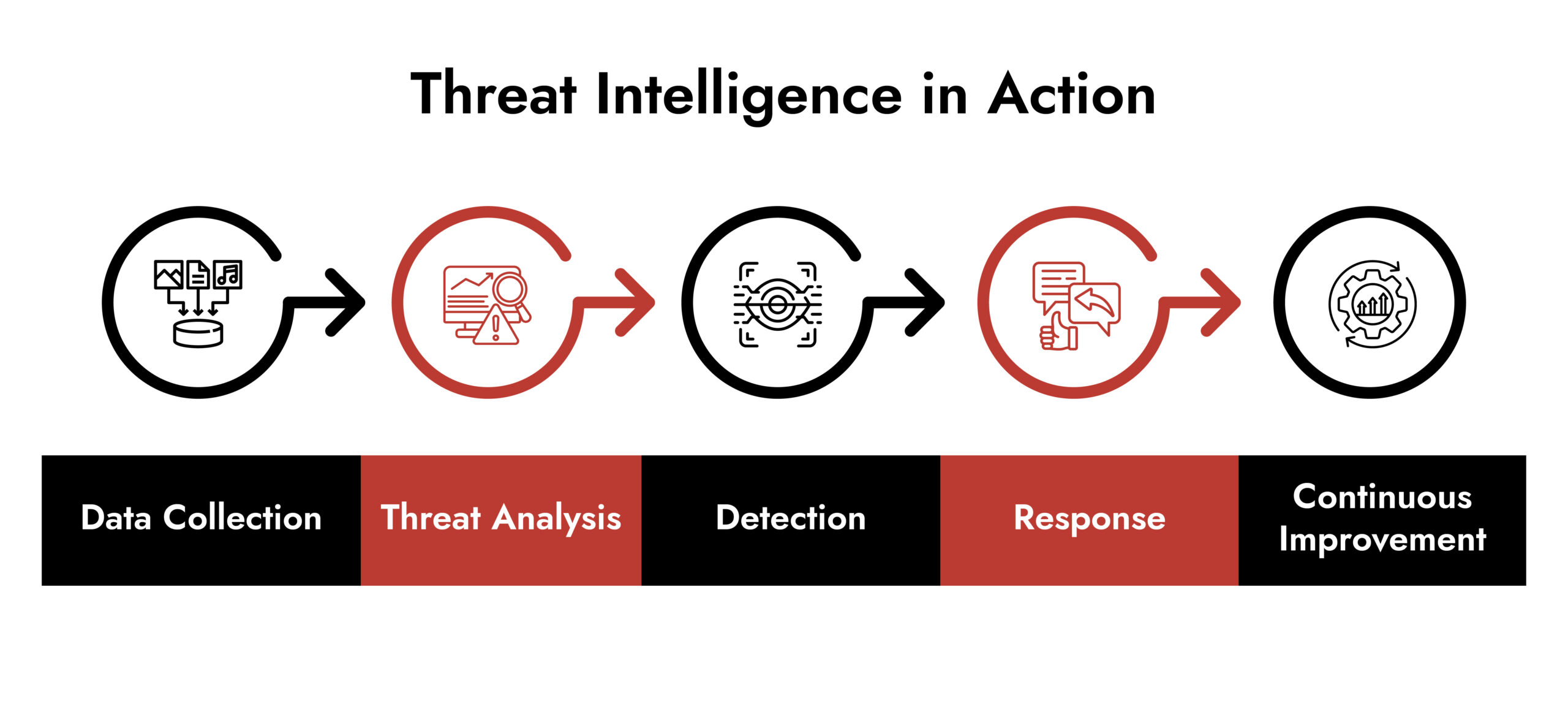
A good way of looking at threat intelligence is to think about it as being the “context,” as opposed to its volume (the amount of data) that you get back from using threat intelligence. In essence, it is a continuous, ongoing cycle of collecting, analyzing and disseminating cyber threat information. The information will include information about how cyberattacks use techniques, the vulnerabilities they actively exploit, indicators of compromise and newly emerging attack patterns.
There is a common theme within threat intelligence: when leveraged correctly, you are able to move away from just reacting to incidents and rather begin to take a more proactive approach in managing your risks. You will also be able to make more informed decisions with regard to your priorities and responses to an incident through the security lifecycle.
Strategic Threat Intelligence:
Strategic threat intelligence encompasses long-term risk and planning. In Strategic Threat Intelligence, there is insight into the trends of threats, motivations of attackers and how the threat landscape is changing within all industries and all geographic areas.
It provides executive leadership teams with a basis to shape security strategy and security budget allocation and to engineer/design resilient architectures. Because the function of the cloud will continue to change, it is especially important as well to determine what is the best method for implementing cloud threat defense and to ensure adaptability as the cloud evolves.
Operational Threat Intelligence:
Operational Threat Intelligence is based on what is immediately being accomplished; this includes providing threat information on active threat campaigns, active exploitation and emerging threats that must be acted on now by security teams and organizations. The benefits include a proactive method for conducting daily threat monitoring activities to allow a team to respond quickly to threats before they become a cyber incident.
Tactical Threat Intelligence:
The technical detail that Tactical Threat Intelligence provides is the analytical information used directly by the analyst, including the indicators of compromise, malware signatures, IP addresses, domains, and attack methods. This information allows for real-time detection of threats as well as for a better understanding of how to analyze those threats through the use of hands-on techniques. Tactical threat intelligence is a necessary part of an organization’s effective cyber threat security operations.
Sources of Threat Intelligence
Effective threat intelligence depends on diverse, high-quality data sources. Combining multiple sources provides deeper visibility into threats
- Open Source Intelligence (OSINT): Publicly available data from blogs, white papers, forums, and social media, helping identify trends and early warning signs.
- Human Intelligence (HUMINT): Insights from cybersecurity experts, researchers, and trusted partners, offering context on potential threats.
- Technical Intelligence (TECHINT): Data from network logs and devices, enabling detailed analysis of threat activity.
- Cyber Intelligence (CYBINT):Information on cyber adversaries, attack methods, malware, and vectors, guiding defense strategies for cloud and network environments.
Integrating OSINT, HUMINT, TECHINT, and CYBINT creates a comprehensive approach to threat validation and mitigation across the enterprise.
Importance of Threat Intelligence: Early Threat Detection
Threat intelligence helps organizations spot threats before they escalate, reducing response time, business impact, and recovery costs. It enables teams to:
- Identify attacker patterns instead of isolated alerts.
- Prioritize real threats over noise.
- Detect known threats faster through automation.
By revealing attacker goals, techniques, and paths, intelligence allows proactive defense rather than blind reaction. It also supports smarter decisions:
- Strategic intelligence focuses on resources on key risks.
- Tactical intelligence accelerates incident response and containment.
Additionally, threat intelligence aids compliance by meeting requirements for continuous monitoring and risk awareness, demonstrating security maturity.
The Value of Threat Intelligence in Modern Cyber Defense
Today’s threat landscape is complex and fast-moving. Organizations face ransomware, insider threats, supply chain attacks, cloud-native threats, and nation-state actors.
Defending against these risks requires more than tools. It requires intelligence.
Threat intelligence refers to analyzed information about threat actors, attack techniques, vulnerabilities, and emerging trends. It transforms security operations from reactive to proactive, strengthening cyber threat security at every layer.
Threat intelligence delivers value by:
- Acting as an early warning system
- Enabling proactive defense adjustments
- Supporting tailored incident response
- Strengthening compliance and reporting
This intelligence-driven approach is essential for building the best cloud threat defense strategies that scale with modern infrastructure.
Emerging Trends in Threat Intelligence
Threat intelligence is rapidly evolving as cybercriminals adapt to new technologies and tactics. Artificial intelligence (AI) and machine learning (ML) will play a pivotal role in enhancing threat analysis, enabling faster and more accurate pattern detection across vast datasets. With organizations increasingly shifting workloads to the cloud, cloud-focused cloud threat defense will become a priority. Cloud-native intelligence will address challenges such as dynamic assets, gaps in shared responsibility models, and identity-driven attacks.
Automation will continue to expand through Security Orchestration, Automation, and Response (SOAR) platforms, reducing manual intervention and ensuring greater consistency in cyber threat management. As the number of connected devices grows, IoT-specific threat intelligence will gain importance, requiring continuous monitoring to mitigate expanded attack surfaces. Finally, intelligence sharing will become more standardized, fostering cross-industry collaboration to strengthen collective cybersecurity and resilience.
360° Cybersecurity with NetWitness Platform
– Unrivaled visibility into your organization’s data
– Advanced behavioral analytics and threat intelligence
– Threat detections and response actionable with the most complete toolset
NetWitness and Threat Intelligence
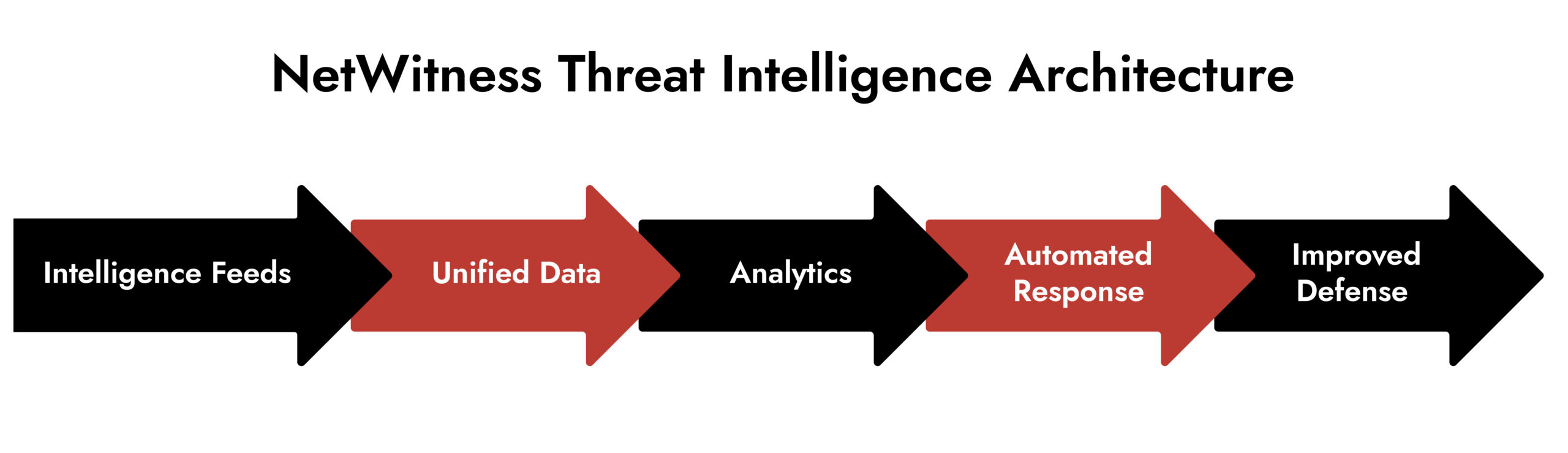
- Focus on Threat Intelligence – NetWitness integrates threat intelligence as a core element in security deployments.
- Enhanced Visibility and Transparency – Combines analytics, automation, and threat intelligence for comprehensive environmental insight.
- Unified Data Model – Brings together multiple data types into a single model, enabling analysts to assess threats in an organizational context.
- Real-Time Visibility – Helps minimize response time to suspicious events through continuous monitoring.
- Automated Analytics with Machine Learning – Quickly identify fraud and threat patterns. Ensure consistent and effective responses.
- Real-Time Intelligence Feeds – Ingests live threat data to proactively monitor and understand potential impacts. Supports ongoing defense against evolving cyber threats.
- Continuous Processing for Resilience – Enables organizations to stay ahead of emerging risks and strengthen security posture.
Conclusion
Cyber threats are relentless and complex – defense demands speed, visibility, and context. Threat intelligence delivers all three, automating detection of known threats so teams can focus on the unknown. This drives proactive defense, faster response, smarter decisions, and scalable security. With intelligence-driven capabilities, NetWitness empowers organizations to strengthen cloud defenses and stay ahead of evolving attacks. Threat intelligence isn’t just protection, it’s a strategic advantage. Request your NetWitness demo today.
Frequently Asked Questions
1. What is cybersecurity's definition of threat intelligence?
The act of collecting and investigating data regarding current and potential cyber threats is called “threat intelligence” in cybersecurity. It allows businesses to learn about expected behaviors of the attacker, monitor potential risk, as well as enable businesses to develop the appropriate level of cyber threat protection for the risk of attack. Instead of having to react after an event has occurred, teams can gain an understanding of the threat and use that understanding to develop means of responding quickly and efficiently to potential threats.
2. What role does threat intelligence play in cyber threat management?
By introducing context into security data, threat intelligence enhances cyber threat management. Threat intelligence allows security teams to give greater priority to alerts that represent actual threats and allows the security team to better defend against active threats, which helps lessen noise on alerts, increase the timeliness of threat response and support more informed decision-making about cybersecurity activities across an organization.
3. Why should organizations be concerned about threat monitoring in cloud environments?
Cloud environments continue to evolve, and they continue to introduce new workloads, new identities, and new services, increasing the attack surface for organizations to secure the possibility of a cyberattack. Continuous threat monitoring enables organizations to have visibility into suspicious behavior in cloud infrastructure. Continuous monitoring of threat intelligence creates the foundation for effective cloud threat defense by enabling organizations to identify misconfigurations, compromised identities, and malicious activities as soon as they occur.
4. What is the difference between threat intelligence and threat analysis?
Threat intelligence consists of data about attackers, their tactics, and the indicators of their activities, while threat analysis provides a way for cybersecurity professionals to use that intelligence in order to establish potential risk and response strategies. While threat intelligence provides the data, threat analysis uses the data to create actionable solutions to protect against cyber threats.
5. How does behavioral analytics strengthen detection?
By connecting data from various sources (i.e., networks and cloud systems), threat intelligence improves the ability to see what is happening regarding the potential threat in context rather than being seen as standalone alerts. This allows for improved speed to detect, more accurate investigations, and greater strength to protect the organization from cyber threats.
6. What makes a successful strategy for defending the cloud against potential threats?
To be successful, a cloud threat defense strategy must combine continuous visibility (the ability to see everything going on around your cloud environment), intelligence-led detection (the use of intelligence–based data to guide detection efforts), and automated response (the use of automated technologies to identify and respond to cyber threats). The role of threat intelligence in this process is to identify known attack patterns, highlight new risks, and highlight the most pressing threats in the dynamic cloud environment.
Threat Intelligence: The Key to Higher Security Operation Performance
Unlock the full potential of your Security Operations Center with deeper visibility, faster detection, and smarter response. This whitepaper explores how modern threat intelligence elevates SOC maturity and helps organizations stay ahead of evolving adversaries.





