What defines the best OT security solutions?
The best operational technology security solutions combine deep asset visibility, native industrial protocol analysis, behavioral threat detection, and non-intrusive deployment capabilities. They provide IT/OT correlation for unified threat visibility, scale across distributed environments, and align to OT-specific compliance frameworks. Critically, they are purpose-built for the availability-first, legacy-rich reality of industrial environments.
According to Dragos, ransomware attacks on OT and ICS environments increased by 60% in 2024. Additionally, a 2026 industry analysis found that only 30% of OT networks have adequate visibility in place.
The IBM X-Force Threat Intelligence Index 2024 found that manufacturing displaced finance as the most attacked industry for the third consecutive year, with OT environments at the center of that shift.
Those statistics represent production shutdowns, safety incidents, regulatory investigations, and in some cases, physical damage to equipment that takes months to replace.
Implementing Operational Technology Security Solution is a necessity that cannot be ignored. In fact, the real question is whether the tools already deployed, or under evaluation, are actually built for the environment they’re supposed to protect.
Why Applying IT Security Logic to OT Environments Keeps Failing
IT and OT security are fundamentally different and have their own set of priorities, constraints, and consequences.
In IT, confidentiality typically leads. You’re protecting data: financial records, personal information, and intellectual property. In OT, that hierarchy inverts. Availability is non-negotiable. A turbine control system, a water treatment dosing pump, or a pipeline pressure regulator cannot tolerate unplanned downtime, regardless of the security reason. A solution that isolates a compromised PLC the way you’d quarantine an infected laptop isn’t securing the environment; it’s creating a different kind of incident.
Legacy systems compound the problem. The industrial environments most at risk aren’t running modern, patchable infrastructure. They’re running Windows XP embedded on hardware that’s been in continuous operation since 2007, talking to engineering workstations over protocols designed before anyone was thinking seriously about cyber threats. These systems were built to run for 20 years without interruption, and they do. That’s a feature, operationally. It’s a security liability when threat actors know that patching and replacement cycles don’t apply.
Then there’s the physical dimension. In IT security, misconfiguration typically causes a service disruption. In OT, it can trigger a pressure spike, a chemical release, or equipment damage. Security decisions in OT carry physical weight that most IT practitioners haven’t had to account for.
Finally, IT/OT convergence is accelerating all of this. Real-time production dashboards, remote monitoring, cloud-connected historians, digital twin platforms, and every integration that delivers operational value also creates an attack path. The traditional air gap that provided a degree of passive protection is largely gone in most modern industrial environments, and the security architecture that replaced it often weren’t designed with OT-specific threats in mind.
What the Best Operational Technology Security Solutions Need to Get Right
The vendor landscape has expanded considerably over the past few years, which makes evaluation harder rather than easier. Most platforms can demonstrate impressive capabilities in a controlled demo environment. These are the capabilities that separate serious platforms from the rest.
Passive Asset Discovery:
Most industrial organizations discover significant gaps in their asset inventories for the first time when a capable operational technology security solution runs passive discovery against their network. Devices that operations teams assumed were decommissioned years ago. Unauthorized connections between process zones. Remote access pathways that IT teams had no record of. This is a reflection of how OT networks evolved organically over decades, with additions and changes that don’t always get formally documented.
Active scanning in OT environments is genuinely risky. Some legacy PLCs and RTUs respond to unexpected network queries by halting, rebooting, or entering fault states. The right approach is to listen to traffic that’s already flowing and build a continuously updated inventory from observed communications rather than active interrogation. The best platforms do this and surface firmware versions, communication baselines, vendor relationships, and device behaviors that are essential context for everything that comes after.
Industrial Protocol Depth:
Modbus, DNP3, EtherNet/IP, PROFINET, IEC 61850, BACnet, OPC-UA are the languages industrial environments speak. A platform that doesn’t understand these protocols at the command level cannot tell you whether a Modbus write to a specific coil address is a legitimate control action or an attacker forcing a valve into an unsafe state. Those two events look identical to a tool that only sees TCP/IP.
Deep protocol awareness is the foundation for meaningful context. When an alert includes the specific function code, register address, and value of an anomalous command, and can tell you whether that command has ever appeared in that zone during normal operations, responders can make confident decisions. Without it, you’re generating alerts that require extensive manual investigation before anyone can determine whether they represent a real threat.
OT-Specific Threat Detection Capabilities:
Generic threat detection doesn’t translate to OT. A spike in Modbus read commands at an unusual hour might be completely normal during a planned maintenance window, or it might indicate reconnaissance by an attacker mapping your control system. Effective OT threat detection tools understand industrial process context. They distinguish between operational anomalies and security threats without flooding SOC teams with irrelevant alerts from normal production variation.
IT/OT Correlation:
The majority of OT compromises don’t begin in the OT network. They begin in IT through a phishing email, a vulnerable VPN endpoint, or a compromised contractor account, and then move laterally through whatever connections exist between the enterprise and operational networks. A security platform that monitors OT in isolation will miss the first phases of these intrusions entirely, seeing only the OT-side activity that occurs after the adversary has already achieved significant access.
For organizations where the IT/OT boundary has meaningful connectivity, it’s a core detection requirement. The platforms that do this well don’t just aggregate alerts from both environments; they correlate them, surfacing relationships between an anomalous IT event and subsequent OT activity that might not look suspicious in isolation.
Uncover the Top Threats Shaping Industrial Network Security
- Emerging threats targeting industrial control systems (ICS)
- Ransomware and supply chain risks in OT environments
- Hidden attack paths across converged IT/OT networks
- Real-world trends impacting critical infrastructure security

Unified Visibility:
Modern attacks don’t stay neatly within OT boundaries. Adversaries often use IT network footholds to pivot into OT environments. A solution that monitors OT in isolation will miss the early stages of these attacks. The most effective platforms provide unified visibility correlating IT and OT telemetry to give security teams a coherent view of threats that span both environments.
Compliance Alignment:
NIST SP 800-82, IEC 62443, NERC CIP, and sector-specific CISA guidance all require documented operational technology security solution controls. Organizations that treat compliance as a separate workstream from their security operations end up doing the same work twice: maintaining operational security visibility and separately pulling together audit evidence. The best platforms make compliance a byproduct of normal operations: continuous asset inventory feeds into documentation requirements, alert records map to incident logging obligations, and risk assessments are generated from the same data that drives operational decisions. That integration matters more as regulatory scrutiny of OT security increases.
Scalability Across Distributed Environments:
Most industrial organizations manage dozens or hundreds of sites, including remote substations, distributed manufacturing plants, offshore platforms, and pipeline compressor stations. A viable operational technology security solution needs to scale to this reality.
Conclusion
The OT security market has matured considerably, but the gap between what the best platforms deliver and what the average deployment actually achieves remains significant. Part of that is tool selection. A larger part is organizational: security programs that treat OT as an IT problem, or that optimize for compliance rather than actual threat detection, tend to underinvest in the capabilities that matter most.
NetWitness gets it right for OT security. They prioritize visibility and involve OT engineering teams in security architecture decisions rather than imposing IT-centric solutions. The solution understands the difference between a security anomaly and normal industrial process variation. Powered by DeepInspect, NetWitness OT solution alerts suspicious activity based on signature, rules, flexible and dynamic correlation in the OT network with native NDR. It is aligned with NIS2 and NIST guidelines and its unique storage space allows highly accurate forensic analysis of metadata and raw data.
Frequently Asked Questions
1. Why are specialized OT security solutions needed?
This is the question most organizations ask first, usually because the IT security stack already represents a significant investment. The honest answer is that IT tools can provide partial visibility into OT networks, for example, network traffic analysis tools can monitor traffic patterns, and a SIEM can aggregate logs from OT systems that produce them. What they can’t do is understand industrial protocols at the command level, maintain passive asset discovery that’s safe for fragile OT devices, or apply behavioral baselines that account for industrial process context. The gap matters most when you’re trying to detect sophisticated attacks, not routine malware. If your threat model includes nation-state actors targeting industrial infrastructure partial visibility isn’t adequate.
2. What features should enterprises look for in OT security solutions?
Start with visibility. An accurate, continuously updated asset inventory is the foundation everything else depends on. Before you can detect threats effectively, you need to know what’s on your network, how devices communicate normally, and where the IT/OT connections exist.
3. Which industries benefit most from OT security solutions?
Energy and utilities are the most targeted by sophisticated threat actors — the documented activity from groups like Volt Typhoon and Sandworm makes that clear. Manufacturing follows closely, driven primarily by ransomware groups who’ve discovered that operational downtime creates far more leverage than data exfiltration alone. Water and wastewater, transportation, and mining all face meaningful risk, and arguably face it with less mature security programs than the energy sector. The common thread across all of them is OT infrastructure that is increasingly networked, increasingly targeted, and consequential when compromised.
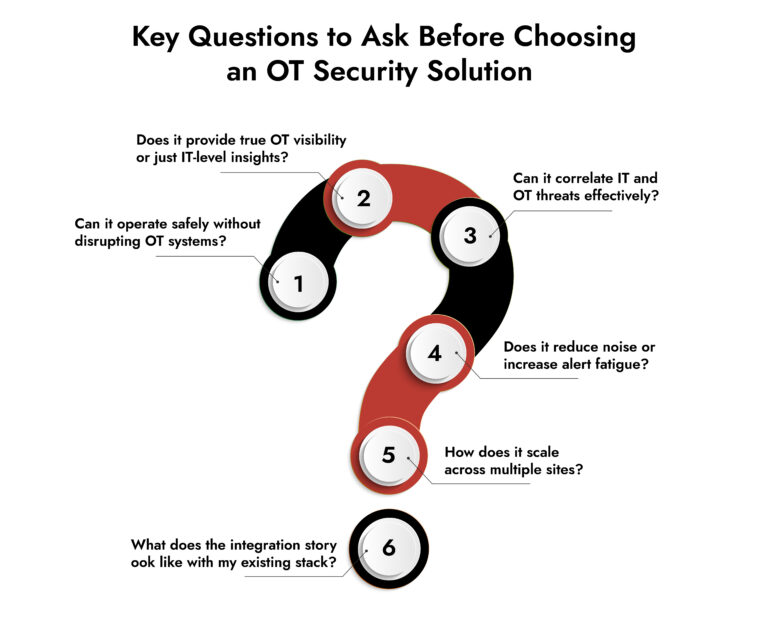
4. How can enterprises choose the right OT security solution?
A few approaches that actually work: require proof-of-concept deployments in your environment rather than demos in theirs, ask for documented case studies from organizations in your sector with comparable infrastructure, and bring in an independent OT security consultant to review vendor responses — not to select a vendor, but to pressure-test the claims. Vendor certifications and analyst rankings are useful context but not substitutes for operational validation. The platform that performs best in a controlled demo isn’t always the one that performs best in your environment.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security