What matters most in network security selection?
Modern enterprises confront business-level risks while operating at the same time without any business-level tools. The ideal small business network security providers must provide constant threat detection, visibility throughout the network, and effective incident response. Instead of using separate solutions, contemporary providers have been required to integrate all three elements into one unified layer. This blog breaks down what those expectations look like in real terms, backed by current security frameworks and industry data.
Introduction
Cyberattacks no longer discriminate by size. In 2024, IBM’s Cost of a Data Breach Report confirmed the global average breach cost hit $4.88 million, and small businesses remain frequent targets due to thinner defenses and inconsistent monitoring.
This is where network security providers for small business become critical. Not as vendors, but as operational partners responsible for reducing blind spots, strengthening detection, and simplifying response.
The challenge is not availability of tools. It is clarity, knowing what “good” actually looks like in network security for business environments that can’t afford downtime, complexity, or guesswork.
Let’s break down what matters.
What Network Security Providers for Small Business Should Deliver
The expectation has shifted from “basic protection” to “continuous visibility and response readiness.”
Modern network security providers for small business should not just install tools. They should operationalize security across endpoints, cloud, and internal traffic.
At minimum, they must provide:
- Real-time network visibility across all traffic flows
- Continuous threat detection aligned with MITRE ATT&CK patterns
- Centralized monitoring instead of fragmented dashboards
- Fast incident triage with clear escalation paths
- Integration with existing IT and cloud infrastructure
What this really means is simple: security should work in the background without slowing down operations.
Core Capabilities in Network Security for Business
Strong network security for business environments depends on layered visibility and control.
A reliable network security solutions company should deliver capabilities that cover:
- Deep packet inspection and traffic analysis
- Behavioral analytics for anomaly detection
- Automated alert prioritization to reduce noise
- Log correlation across hybrid environments
- Identity-aware monitoring across users and devices
These capabilities reduce dependency on manual monitoring and improve response accuracy.
The reality is that most network security issues begin with visibility gaps, not lack of tools.
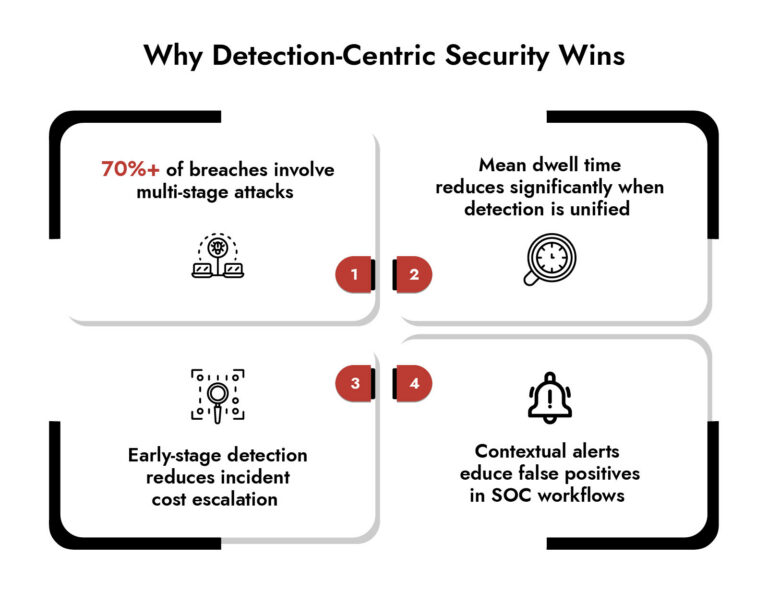
Network Security Monitoring Services That Actually Matter
Many providers claim monitoring, but not all monitoring is actionable.
Effective network security monitoring services should focus on three outcomes:
- Detection speed (how quickly threats surface)
- Context depth (how well alerts explain impact)
- Response readiness (how fast action can begin)
Modern SOC environments rely heavily on network security monitoring tools that consolidate:
- Flow analysis
- Endpoint signals
- DNS and packet-level inspection
- Cloud telemetry
According to NIST guidance (2024 updates to SP 800-61r3), organizations that integrate monitoring with response workflows reduce dwell time significantly compared to siloed systems.
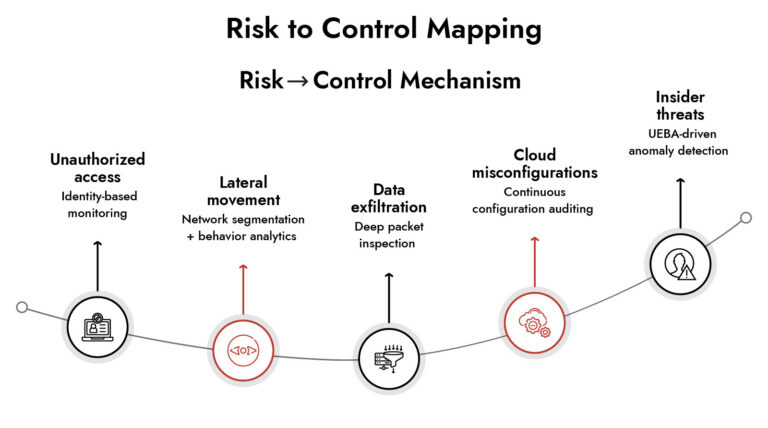
Network Security Risks Small Businesses Can’t Ignore
Most network security risks do not start with advanced attackers. They start with weak configurations, unmanaged assets, and unnoticed lateral movement.
Common network security problems include:
- Misconfigured cloud services
- Unmonitored remote access points
- Delayed patching cycles
- Shadow IT applications
- Weak segmentation inside internal networks
These network security threats often remain invisible until data exfiltration begins.
A strong network security system must therefore prioritize early detection over post-incident reporting.
Network Security Monitoring Tools and Detection Capabilities
Modern network security monitoring tools go beyond alert generation.
They focus on threat detection that connects context across systems:
- Correlating endpoint behavior with network activity
- Identifying encrypted traffic anomalies
- Detecting command-and-control patterns
- Mapping attack chains across hybrid environments
The shift is clear: from isolated alerts to connected intelligence.
This is where network security providers for small business must evolve toward unified detection models instead of fragmented toolsets.
Uncover the Top Threats Shaping Industrial Network Security
- Emerging threats targeting industrial control systems (ICS)
- Ransomware and supply chain risks in OT environments
- Hidden attack paths across converged IT/OT networks
- Real-world trends impacting critical infrastructure security

Choosing the Right Network Security Solution
Selecting a network security solution is not about feature count. It is about operational fit.
A practical evaluation framework:
- Can it reduce alert fatigue instead of increasing it?
- Does it unify visibility across cloud and on-prem environments?
- Can analysts trace an attack end-to-end without switching tools?
- Does it support automation without removing human control?
The strongest network security providers for small business are those that simplify complexity rather than adding layers.
How NetWitness Fits into Modern Network Security Needs
Modern security teams often struggle with fragmented visibility across hybrid environments. Platforms like NetWitness address this by focusing on deep packet-level visibility, behavioral analytics, and integrated detection workflows.
In practical terms, NetWitness aligns with what network security providers for small business are expected to deliver today:
- High-fidelity threat detection across network traffic
- Ability to analyze encrypted and unencrypted communications
- Correlation across endpoints, logs, and network behavior
- Investigation workflows designed for SOC efficiency
NetWitness also aligns with evolving security models highlighted in NIST and industry threat reports, especially around detection-driven security architectures rather than perimeter-only defense.
What stands out is not tool complexity, but investigative clarity. Analysts don’t just get alerts, they get context that helps reconstruct attack behavior faster.
Conclusion
Security is no longer about layering tools. It is about building clarity into every packet, every connection, and every anomaly.
The right network security providers for small business should act less like vendors and more like intelligence layers, helping organizations see what they previously couldn’t, and respond before damage spreads.
The real question is not whether threats exist. It is whether your network sees them early enough to matter.
Frequently Asked Questions
1. What are the essential services offered by network security companies?
Network security companies provide services such as threat detection, network monitoring, incident response, firewall maintenance, and vulnerability assessment among others to their clients.
2. How to choose network security providers for small business?
Consider the depth of network security provider visibility, network security monitoring services, integration, and risk reduction capabilities while making your selection without any complications.
3. Which network security providers offer zero-trust architecture services?
Zero trust is one of the key features provided by some of the best network security solutions company nowadays.
4. Find companies specializing in cloud network security
Find providers who concentrate on hybrid visibility, analyzing metadata, and integrating the cloud-based network security solution.
5. How to choose a network security provider for healthcare organizations?
Healthcare business needs high compliance, real-time network security monitoring tools, and high-level security measures.
Achieve NIS2 Compliance with Confidence
- Meet NIS2 requirements across IT and OT environments
- Detect and respond to threats in real time
- Streamline compliance reporting and audit readiness
- Reduce risk with continuous monitoring and analytics





