What is the difference between network monitoring and network detection?
Network monitoring focuses on infrastructure performance, uptime, and device health using network monitoring software and real time network monitoring tools. Network detection, commonly delivered through Network Detection and Response (NDR) solutions, analyzes network traffic for malicious behavior, lateral movement, and cyber threats. Monitoring protects availability, while detection protects against breaches.
Introduction
For years, organizations relied on network monitoring software to keep systems stable and available. That worked when outages were the biggest concern. Today, outages are only half the story. The real risk is what moves quietly across your network without triggering a performance alarm.
That is where the difference between network monitoring and network detection becomes critical. They sound similar. They both analyze traffic. They both generate alerts. But they serve fundamentally different purposes. If you are building modern SOC network visibility, you need to understand where one stops and the other begins. Let’s unpack it properly.
What Is Network Monitoring?
Network monitoring focuses on performance, uptime, and infrastructure stability.
Its primary job is to answer operational questions:
- Are routers and switches functioning correctly?
- Is application latency within SLA limits?
- Is bandwidth usage unusually high?
- Are devices online and responsive?
Most network monitoring tools collect telemetry such as:
- CPU and memory utilization
- Interface throughput
- Packet loss
- Latency
- Device health metrics
A typical network monitoring application relies on SNMP, NetFlow, and log-based data collection. It provides dashboards and alerts when thresholds are exceeded.
The Core Objective: Stability
Real time network monitoring ensures that outages, congestion, or hardware failures are detected immediately.
If a server crashes at 2 a.m., monitoring tools generate alerts.
If bandwidth spikes beyond normal limits, administrators are notified.
If latency increases, the operations team investigates.
This layer is essential for business continuity. Without it, organizations cannot maintain uptime. But here’s the limitation. Monitoring tells you something changed. It does not always tell you whether that change is malicious.
What Is Network Detection?
Network detection shifts the focus from performance to protection. Instead of asking, “Is the network healthy?” it asks, “Is someone attacking us?”
Network Detection and Response, often abbreviated as NDR, analyzes network traffic for signs of malicious behavior. Unlike traditional monitoring, NDR solutions inspect patterns, behaviors, and anomalies within traffic flows.
This includes:
- East-west lateral movement inside the network
- Suspicious DNS activity
- Command-and-control communications
- Data exfiltration attempts
- Encrypted traffic anomalies
Through advanced Network traffic analysis and behavioral baselining, NDR platforms detect threats that do not break systems but quietly exploit them.
The Core Objective: Threat Identification and Containment
Network detection is designed for SOC analysts. It provides:
- Behavioral anomaly detection
- Threat intelligence correlation
- Risk scoring and prioritization
- Investigation context
- Response workflows
Where monitoring relies on static thresholds, Network Detection and Response uses dynamic baselines.
For example: A sudden 40 percent bandwidth spike might be normal during a product launch. But encrypted outbound traffic to a rare foreign domain at midnight? That is suspicious.
Monitoring might ignore it. NDR will not.
Network Monitoring vs. Network Detection: A Clear Comparison
To simplify, here is how they differ across core dimensions.
| Category | Network Monitoring | Network Detection |
| Primary Goal | Performance & uptime | Threat detection & response |
| Typical Users | IT operations | SOC analysts |
| Alert Type | Threshold-based | Behavior-based |
| Data Focus | Device metrics & traffic volumes | Traffic behavior & threat indicators |
| Key Technology | Network monitoring software | NDR solutions |
| Outcome | Prevent outages | Prevent breaches |
What this really means is this:
Monitoring protects availability.
Detection protects data.
You need both.
Where Network Security Monitoring Fits
Network security monitoring, often abbreviated as NSM, sits closer to detection than traditional monitoring. It combines:
- Continuous traffic collection
- Packet capture
- Log aggregation
- Threat analysis
Unlike pure network monitoring tools, Network security monitoring platforms retain traffic metadata for forensic analysis. This capability becomes critical during investigations. When a breach is suspected, SOC teams must reconstruct what happened:
- How did the attacker enter?
- What systems were accessed?
- What data left the environment?
- Was lateral movement successful?
Without deep Network traffic analysis, these questions are difficult to answer. This is why strong SOC network visibility increasingly depends on NDR solutions rather than basic monitoring applications.
Why Traditional Network Monitoring Falls Short for Security
Network monitoring software was not built to detect sophisticated threats. It was built to ensure devices stay online. Attackers understand this. Modern adversaries:
- Blend into normal traffic
- Use encrypted channels
- Move laterally using legitimate credentials
- Avoid triggering performance thresholds
A network monitoring application may detect a server outage caused by ransomware. But by that point, the damage is done. Detection tools, on the other hand, may identify:
- Suspicious privilege escalation
- Abnormal internal communication patterns
- Beaconing behavior
- Data staging activity
The earlier the detection, the lower the impact.
DORA Compliance with NetWitness® Network Detection & Response (NDR)
Strengthen Digital Operational Resilience with Deep Network Visibility
Meet EU DORA requirements with continuous network monitoring, advanced threat detection, and automated response across complex financial environments.
Real Time Network Monitoring vs. Real Time Threat Detection
Both operate in real time. But they watch for different signals. Real time network monitoring observes performance fluctuations. Real time detection observes behavioral deviations. For example:
- Monitoring sees increased traffic.
- NDR analyzes whether that traffic matches normal patterns.
- Monitoring detects a spike in outbound connections.
- NDR determines whether those connections resemble command-and-control activity.
This layered approach reduces false positives and improves decision quality inside the SOC.
How Network Detection Strengthens SOC Operations
Modern SOC teams face alert fatigue. Thousands of alerts per day. Many of them low priority.
Network Detection and Response platforms help by:
- Prioritizing alerts based on risk
- Correlating network behavior with threat intelligence
- Providing investigation context
- Automating response actions
Instead of chasing raw alerts, analysts receive structured threat narratives. This improves:
- Mean Time to Detect
- Mean Time to Respond
- Investigation accuracy
- Analyst productivity
Stronger detection directly translates to stronger SOC network visibility.
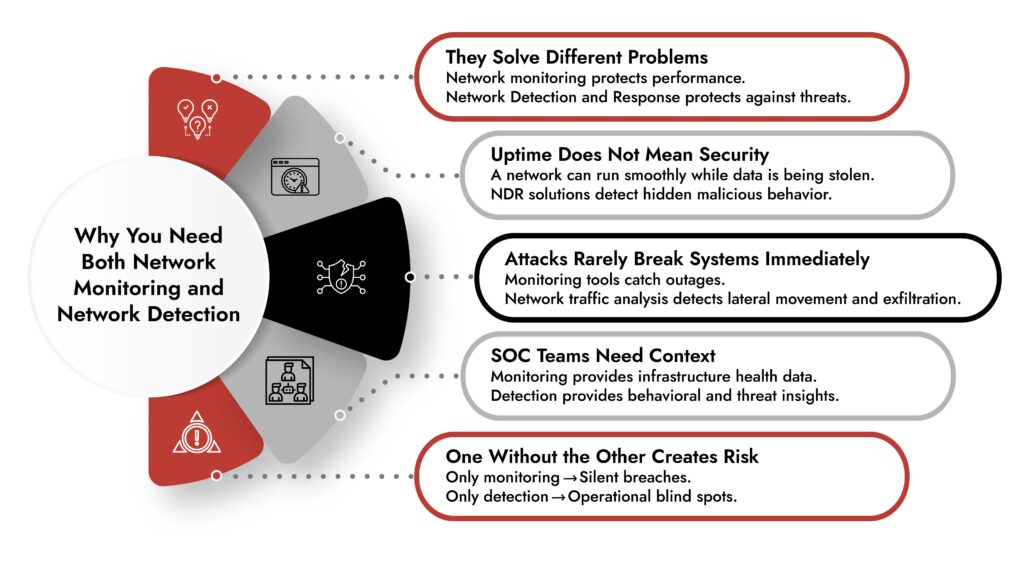
Do Organizations Really Need Both?
Yes. And here’s why.
If you rely only on network monitoring tools: You may maintain uptime but miss silent breaches.
If you rely only on NDR solutions: You may detect threats but overlook operational instability.
Organizations need:
- Network monitoring software for infrastructure health
- Network Detection and Response for threat identification
- Integrated dashboards for unified visibility
Together, they create both operational resilience and security resilience. Think of it this way.
Monitoring keeps the engine running.
Detection ensures no one is tampering with it.
The Evolution Toward Integrated Visibility
The line between monitoring and detection is narrowing. Modern platforms increasingly integrate:
- Network traffic analysis
- Endpoint telemetry
- Cloud visibility
- User behavior analytics
Cyber threat monitoring tools now incorporate AI-driven analytics, making detection faster and more accurate. Organizations that combine performance data with security analytics achieve stronger outcomes because they see the full picture.
For example: If a server shows high CPU usage and NDR detects suspicious encryption processes simultaneously, that correlation speeds containment. Isolated tools create blind spots. Integrated visibility reduces them.
Choosing the Right Approach
When evaluating network monitoring software or NDR solutions, ask:
- Does it provide deep packet or metadata inspection?
- Does it baseline normal behavior?
- Does it support encrypted traffic analysis?
- Can it integrate with SIEM and SOAR platforms?
- Does it improve SOC network visibility?
The goal is not to replace monitoring. It is to strengthen detection without sacrificing performance visibility. Security maturity today is measured not just by uptime but by detection speed and investigative clarity.
Final Takeaway
Network monitoring answers: Is the network functioning properly?
Network detection answers: Is someone exploiting it?
Traditional network monitoring solution focuses on infrastructure health such as uptime, latency, bandwidth usage, and device status. It helps IT teams maintain stability and prevent outages.
Network Detection and Response (NDR) focuses on analyzing network traffic to identify suspicious behavior, attacker movement, and potential breaches. It helps security teams detect threats that performance monitoring tools are not designed to catch.
The terms can sometimes sound similar because both observe network traffic. The difference is in the goal. Monitoring focuses on performance visibility, while NDR focuses on security visibility and threat detection.
In modern environments, organizations rely on both capabilities. Monitoring ensures the network stays operational, while NDR ensures attackers cannot operate inside it unnoticed. Together, they turn network visibility into both operational awareness and active security defense.
Frequently Asked Questions
1. What is the main difference between network monitoring and network detection?
Network monitoring focuses on performance, uptime, and infrastructure health. Network detection focuses on identifying malicious activity within network traffic using behavioral analytics and threat intelligence.
2. Do organizations need both network monitoring and network detection?
Yes. Network monitoring maintains operational stability, while Network Detection and Response protects against cyber threats. Both are necessary for complete visibility and resilience.
3. How does network detection help SOC teams?
Network detection improves SOC network visibility by identifying lateral movement, command-and-control traffic, and suspicious behaviors. It reduces false positives and speeds up investigation and response.
4. Can network monitoring tools detect cyber attacks?
Traditional network monitoring tools may detect traffic anomalies, but they are not designed for deep security analysis. Dedicated NDR solutions are more effective at detecting advanced threats.
5. Is Network Detection and Response (NDR) the same as network monitoring?
No. Network Detection and Response is a security-focused capability designed to detect and respond to threats. Network monitoring is primarily concerned with performance and availability.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.