Why Is Cybersecurity Effectiveness Important?
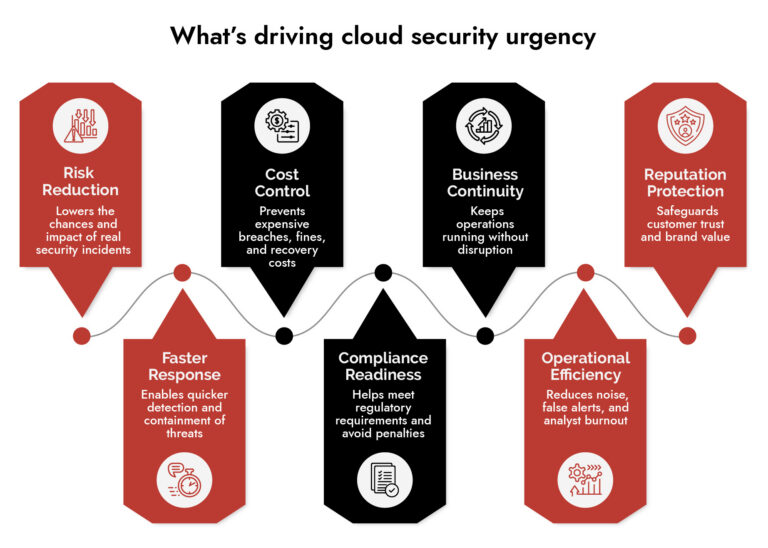
Cybersecurity effectiveness matters because it focuses on reducing real risk, not just managing alerts. It helps organizations prevent financial losses, maintain business continuity, and protect customer trust. Effective cybersecurity services also improves detection and response speed, reduces false positives, and ensures compliance with regulations. In short, it turns security operations from activity-driven to outcome-driven, where the goal is fewer successful attacks and faster recovery when incidents occur.
Why Most Cybersecurity Services Teams Are Measuring the Wrong Things
Talk to most security teams about success, and they will tell you: number of alerts handled, tickets closed, tools deployed. It sounds rigorous. It isn’t.
What the numbers are telling you is the teamwork busyness. What they do not say is whether an organization is really safer. By 2026, the businesses that are serious about cybersecurity services have ceased to equate activity with effectiveness and they have created measurement frameworks that can demonstrate the distinction.
Here’s what that looks like in practice.
Alert Counts Don’t Measure Cybersecurity Risk Assessment
For years, security teams measured themselves on volume. More alerts monitored, faster tickets closed, higher percentage of endpoints covered these became the headline stats in board decks. The logic made sense on the surface: if we’re catching more, we’re doing better.
The problem is that high alert volume without detection of quality scoring gives you a false sense of safety. A team drowning in 10,000 weekly alerts, 40% of which are false positives, isn’t more secure than a team handling 2,000 alerts that are 95% accurate. They’re just more exhausted.
This is the core shift happening across mature security operations in 2026: from measuring output to measuring outcomes. The question isn’t how many alerts fired it’s whether the right threats were caught, contained, and prevented from recurring. That’s where cybersecurity risk assessment comes in. Without a clear baseline of what your actual risk exposure looks like, you’re optimizing in the dark.
The Seven SOC Metrics That Actually Matter
Security Operations Centers are now focusing on a tighter set of indicators that directly connect to risk reduction. Here’s what’s being tracked in SOC network security and why each one matters:
- Mean Time to Detect (MTTD)
Speed of threat identification after a compromise occurs. In 2026, this metric is always paired with detection quality scoring because a fast Mean Time to Detect means nothing if half the detections are noise. The goal is catching real threats fast, not just triggering rules fast.
- Mean Time to Contain (MTTC)
How quickly a threat is isolated once identified. Regulatory pressure has made this urgent the SEC’s 4-day reporting requirement and CIRCIA’s 72-hour rule mean that slow containment carries direct legal and reputational consequences. Automation-driven containment is the primary lever mature SOCs are pulling here.
- Dwell Time
How long an attacker moves around undetected. These correlates directly with breach severity the longer the dwell time, the worse the damage. A declining dwell time trend is one of the clearest signals of SOC maturity.
- False Positive Rate
The percentage of alerts that turn out to be non-actionable. This matters for two reasons: operational accuracy and analyst retention. Teams grinding through mountains of false positives burn out, and burnout means institutional knowledge walks out the door. Tracking this metric seriously is also tracking workforce stability.
- Automation Coverage Rate
The percentage of response tasks handled by SOAR or AI-driven workflows without human intervention. Mature security operations center teams are seeing over 50% reductions in response time through automation. If your SOC is still manually triaging everything, this metric exposes exactly where efficiency is being lost.
- Incident Response Completion Time
Full lifecycle from initial detection through complete recovery. Boards in 2026 are asking for total resolution time, not just how fast detection happened. A company that detects fast but takes three weeks to fully recover still has a problem.
- Alert Triage Time
How quickly alerts get classified and escalated. Monitored through backlog volume and escalation speed. When triage slows down, the whole detection pipeline backs up, which means active threats wait longer before anyone acts on them.
How to Present Cybersecurity Solutions ROI to Your Board
Technical metrics are useful internally. They don’t move boards. What moves boards is financial risk quantification, and that’s where the conversation about cybersecurity ROI has fundamentally changed.
The model most enterprises are using now is Return on Security Investment (ROSI):
ROSI = (Risk Reduction Value – Security Investment Cost) ÷ Security Investment Cost
Here’s a concrete example: a $150,000 cybersecurity awareness program that reduces a $2 million phishing risk by 70% delivers a 833% ROSI. That’s a number a CFO understands without a glossary.
Alongside ROSI, organizations are using FAIR (Factor Analysis of Information Risk) and Annualized Loss Exposure (ALE) models both rooted in rigorous cybersecurity risk assessment to translate technical risk into projected financial impact. The math is straightforward multiplying the cost of a single incident by the probability it occurs in a given year. What comes out is a number that belongs on a balance sheet, not just a security dashboard.
This translation layer is what separates cybersecurity services teams that get budget from those that fight for it every year.
What to Look for in a Unified Security Platform
- Cut through tool sprawl with a practical evaluation framework.
- Compare platforms based on visibility, detection accuracy, and automation.
- Validate real-world performance across hybrid and cloud environments.
- Make confident, risk-aligned security decisions.
The Hidden Metric in Every Cybersecurity Platform
Here’s something most measurement frameworks miss: your security analysts are themselves a leading indicator of organizational resilience.
Progressive SOCs now track alert fatigue trends, escalation friction, and cognitive load as part of their operational metrics. The reasoning is straightforward. When analysts are overwhelmed, they make more errors. When they burn out, they leave and with them goes the institutional knowledge of your environment that no cybersecurity software or cybersecurity platform can replicate.
An analyst who’s been with your organization for three years knows which alert patterns are actually concerning in your specific infrastructure. That knowledge doesn’t show up on any dashboard. Protecting it does.
Third-Party Risk and Why Your Advanced Cybersecurity Solutions Must Cover It
Third-party risk measurement has become significantly more rigorous. Your security posture is only as strong as the weakest link in your partner ecosystem, and in 2026, boards know it.
The key vendor metrics enterprises are now tracking:
- Average vendor security rating – quantified external scores across the third-party ecosystem
- Mean Time for Vendor Incident Response (MTTVR) – how quickly partners acknowledge and begin remediating vulnerabilities
- Percentage of vendors with valid compliance certifications (SOC 2, ISO 27001) – a baseline hygiene check that’s becoming non-negotiable
The question isn’t just whether your own cybersecurity services are working. It’s whether your entire supply chain meets a consistent security baseline. The organizations getting this right are using advanced cybersecurity solutions that can score and monitor vendor posture continuously, not just at contract renewal.
What Board Reporting Looks Translating Cybersecurity Software Data into Board-Level Business Language
The shift from technical to business language is most visible in how security teams communicate upward. Here’s what that translation looks like in practice:
Old framing: Deployed EDR on 5,000 endpoints.
New framing: Reduced ransomware risk by 60%, protecting $15 million in annual revenue.
Old framing: 95% patch compliance achieved.
New framing: Critical vulnerabilities closed within 48 hours, maintaining PCI compliance and avoiding potential $500,000/month in fines.
The three headline metrics boards care about: Quantified Risk Exposure (financial estimates of unmitigated risk), Cost Avoidance (the financial impact prevented), and peer benchmarking that shows where the organization sits relative to industry. These aren’t soft metrics. They’re the same language every other business function uses to justify investment, and the right cybersecurity services platform should make producing this reporting automatic, not manual.
Emerging Cybersecurity Technologies in 2026
A few measurement trends worth watching as they move from early adoption into mainstream practice:
Cloud Misconfiguration Rate: The percentage of cloud resources deviating from secure baselines. As organizations run more infrastructure in the cloud, this becomes a direct indicator of DevSecOps maturity and a growing priority for teams evaluating advanced cybersecurity solutions built for cloud-native environments.
Zero-Trust Control Coverage: Tracking what percentage of defined zero-trust controls are actually implemented and active, not just planned or partially deployed. This is one of the areas where cybersecurity services are evolving fastest, with platforms now capable of mapping control gaps in real time.
Playbook Effectiveness: How often incident response playbooks succeed without manual intervention. This replaces tool-count metrics with a direct measure of operational readiness. Security operations center tools that integrate automated playbook tracking are increasingly standard in mature environments.
Post-Incident Transparency: Tracking which incidents bypass detection and why. The most mature security operations teams powered by modern cybersecurity technologies treat failure metrics as the most important data they collect because that’s where improvement actually starts.
What Effective Cybersecurity Services Actually Look Like in 2026
Cybersecurity service measurement in 2026 is about one question: are we actually reducing risk, or are we just generating activity? The organizations getting this right have stopped optimizing metrics that look good in reports and started measuring things that improve decisions, protect people, and translate directly into financial outcomes.
The cybersecurity solutions are better. The frameworks are sharper. The board expectations are higher. The gap between organizations that measure what matters and those that measure what’s easy is only going to widen.
If your security operations center is still leading with alert counts and ticket closure rates, you already know what needs to change.
Frequently Asked Questions
1. What are the key cybersecurity metrics used in 2026?
MTTD, MTTR, dwell time, false positives, and risk reduction. These reflect how quickly and effectively threats are detected and handled.
2. What role do SOC metrics play in cybersecurity?
SOC metrics measure detection speed, response efficiency, and analyst performance using security operations center tools in SOC network security environments.
3. How do enterprises measure cybersecurity ROI?
By comparing investment in cybersecurity solutions and platforms against reduced incidents, faster response, and lower operational risk grounded in formal cybersecurity risk assessment methodology.
4. How do enterprises benchmark cybersecurity performance?
Using industry frameworks, peer comparisons, and internal baselines supported by cybersecurity risk assessment and continuous monitoring through a unified cybersecurity platform.
5. What tools help measure cybersecurity effectiveness?
Cybersecurity software such as SIEM, SOAR, and integrated cybersecurity platforms provide visibility into threats, response, and overall performance. Advanced cybersecurity solutions now extend this to vendor risk and cloud misconfiguration tracking as well.
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.