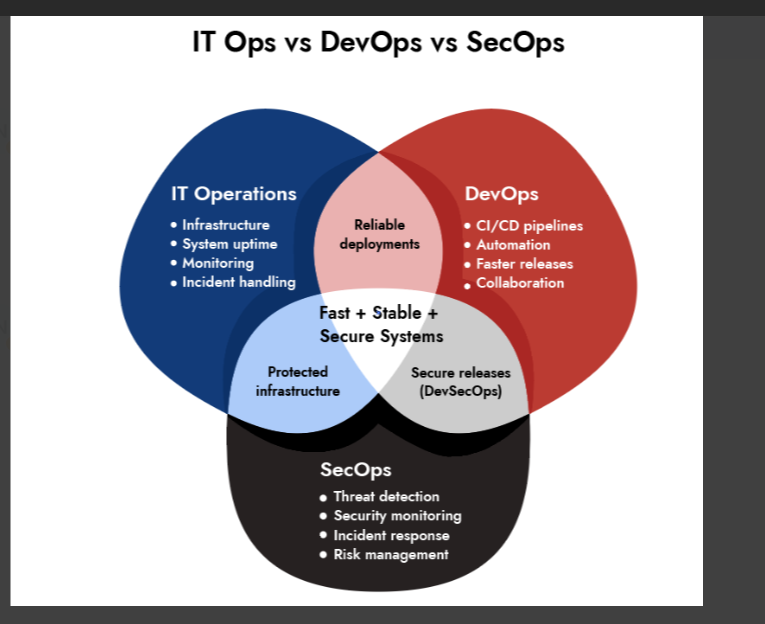
IT Operations vs DevOps vs SecOps — What’s the Difference?
- IT Operations (IT Ops) keeps systems running. It manages infrastructure, ensures uptime, handles incidents, and maintains stability across networks, servers, and applications.
- DevOps focuses on speed and efficiency in software delivery. It brings development and operations together through automation, shared ownership, and continuous deployment practices.
- SecOps (Security Operations) protects the environment. It continuously monitors for threats, detects vulnerabilities, and responds to security incidents through a SOC and security tools.
Introduction
There’s a conversation that happens in almost every growing tech company at some point. Usually after something breaks. The server’s down, or the latest deployment killed production, or someone’s asking why a phishing attack got through undetected. And suddenly three different teams are on a call, everyone’s defensive, and nobody can quite agree on whose problem this actually was.
That’s the IT Operations, DevOps, and SecOps confusion in a nutshell.
These aren’t just different job titles. They’re different ways of thinking about technology, what matters, what gets prioritized, and what “success” even looks like on a regular Tuesday. Getting them confused doesn’t just create awkward org charts. It creates real gaps that attackers exploit, customers feel, and auditors love pointing out.
So let’s sort it out properly.
What Is IT Operations?
Information technology operations is the oldest of the three. Long before DevOps or SecOps existed as concepts, IT ops teams were keeping servers alive, networks stable, and businesses functional. The mandate hasn’t changed much: keep everything running.
IT operations management is built around reliability. The team owns the infrastructure, responds to outages, and makes sure the business can function without disruption day in, day out.
IT Operations Roles and Responsibilities
The scope is broad. A typical IT ops team is responsible for:
- Infrastructure management – servers, networks, storage, cloud environments
- Monitoring and alerting – tracking system health and catching issues before users do
- Incident response – diagnosing and resolving outages or degraded performance
- Patch and update management – keeping systems current and secure
- Backup and disaster recovery – making sure data survives when hardware doesn’t
- End-user support – the helpdesk function that keeps employees productive
IT ops teams traditionally run on structured change management. Change Advisory Boards, approval workflows, documented runbooks. That’s not bureaucracy for the sake of it infrastructure changes that go wrong can take companies offline for hours. Caution is baked in by necessity.
The problem is that caution and speed don’t always coexist. When software teams started shipping code daily instead of quarterly, the old model started creating friction the business couldn’t afford. That friction is what DevOps was born to solve.
What Is DevOps?
DevOps is what happens when the wall between development and operations becomes too costly to maintain.
For years, developers wrote code and handed it off to operations. Operations ran it, got paged when it broke things, and had no say in how it was built. The two teams worked toward the same product from completely different angles, with almost no shared context. Slow releases, avoidable outages, and a steady blame cycle were the results.
DevOps flips the model. Instead of a handoff, there’s shared ownership. Developers care about how their code behaves in production. Operations gets involved earlier in the development cycle. Everyone works from the same dashboards and responds to the same incidents.
What DevOps Actually Changes
- Culture — shared ownership of building and running software, not separate kingdoms
- Automation — CI/CD pipelines, infrastructure as code, automated testing reduce human error and release fear
- Speed — deployment frequency goes up; time from code commit to production goes down
- Feedback loops — problems get caught in minutes, not weeks after a release
One thing DevOps does not replace is IT operations management. Infrastructure still needs to be managed. Networks still need configuration. DevOps changes how teams collaborate around that infrastructure not whether it needs attention.
Teams that buy DevOps tools without changing how people work together just end up running broken processes faster. The tooling follows the culture, not the other way around.
What Is SecOps?
When DevOps took off, teams shipped faster genuinely, impressively faster. And that speed created a security problem almost nobody planned for.
Traditional security teams were built for a slower world. They assumed time to review changes, run assessments, and sign off before anything went live. When deployment cadences shifted from quarterly to daily, security got left behind. Vulnerabilities shipped alongside features. Security debt accumulated quietly. Attackers noticed.
SecOps (Security Operations) is the operational response to that gap. It treats security not as a periodic audit, but as a continuous function. Real-time monitoring, active threat detection, and incident response fast enough to actually contain damage before it spreads.
The core of most SecOps functions is the Security Operations Center the SOC.
Security Operations Center (SOC): How It Works
A Security Operations Center is where threat monitoring and response actually happens. Analysts watching dashboards, triaging alerts, and hunting for threats that haven’t triggered alarms yet. Mature SOCs run 24/7 because attackers don’t observe business hours.
The Security Operations Center Framework
The framework every serious SOC team runs on has three pillars:
- People
| Tier | Role | Responsibility |
| Tier 1 | SOC Analyst | Alert triage, separating real threats from noise |
| Tier 2 | Senior Analyst | Deep investigation of confirmed incidents |
| Tier 3 | Threat Hunter | Proactive hunting for undetected threats |
| — | SOC Manager | Team coordination, executive communication during incidents |
- Process
Who does what when a ransomware alert hits at 3am? How does the SOC escalate to legal or the executive team during a live breach? Without documented, drilled playbooks, even a talented team becomes inconsistent under pressure. Process is the layer most organizations underinvest in and it shows when something serious happens.
- Technology
This is where security operations center tools become critical. A functional SOC typically runs on a stack that includes:
- SIEM (Security Information and Event Management) – Platforms like Netwitness, Splunk, Microsoft Sentinel, or IBM QRadar aggregate logs from across the environment, correlate events, and surface anomalies invisible at the individual system level
- SOAR (Security Orchestration, Automation, and Response) – Tools like Netwitness, Palo Alto XSOAR automate repetitive response tasks alert enrichment, ticket creation, initial containment freeing analysts to focus on decisions that actually require judgment
- EDR (Endpoint Detection and Response) – Platforms like CrowdStrike Falcon or Sentinel One monitor device behavior and catch threats that signature-based tools completely miss
- Threat Intelligence Platforms – External feeds that contextualize what attackers are actively doing, what infrastructure they’re using, and whether it’s relevant to your environment
The combination of these information technology security solutions is what separates a SOC that catches breaches early from one that finds out about them in the news.
Uncover the Top Threats Shaping Industrial Network Security
- Emerging threats targeting industrial control systems (ICS)
- Ransomware and supply chain risks in OT environments
- Hidden attack paths across converged IT/OT networks
- Real-world trends impacting critical infrastructure security

IT Operations vs DevOps vs SecOps: Side-by-Side
Same organization, same infrastructure, genuinely different priorities. Here’s how they actually compare:
| IT Operations | DevOps | SecOps | |
| Primary Goal | Stability and uptime | Faster, reliable software delivery | Security monitoring and threat response |
| Core Question | Is everything running? | Can we ship faster without breaking things? | Are we under attack and would we know? |
| Key Metric | Uptime %, MTTR | Deployment frequency, lead time | MTTD, MTTR (detect and respond) |
| Mindset | Stability over change | Change through automation and ownership | Assume breach, verify everything |
| Works Closest With | Every team using infrastructure | Development and operations | IT, legal, compliance, executive teams |
The tension between these mindsets is real. IT ops wants stability, which means resisting unnecessary change. DevOps wants speed, which means constant change. SecOps wants full visibility into all of it which requires the cooperation of both. Getting all three to work together without anyone feeling overruled takes deliberate organizational design.
The real challenge isn’t just aligning priorities. In practice, that alignment is less about structure and more about shared visibility. When IT Ops, DevOps, and SecOps rely on different data sets and disconnected tools, coordination breaks down quickly. A unified view across logs, network, and endpoint activity helps bridge that gap and enable those teams to operate from a shared source of truth. This is what ultimately allows stability, speed, and security to coexist without constant trade-offs.
— Ibrahim Badawi, NetWitness
Where the Lines Are Starting to Blur
DevSecOps is the most prominent overlap. It embeds security directly into the DevOps pipeline instead of treating it as a gate at the end of a release. Static code analysis during builds, dependency vulnerability scanning, container security checks before anything reaches production. Security moves left closer to development where problems are cheapest to fix.
In practice, this requires developers to actually act on security tooling output, which requires security teams to make that output useful rather than overwhelming. Neither side finds it easy initially. But organizations that get it working ship faster and safer simultaneously.
AIOps is changing how IT operations management works using machine learning to predict failures before they happen and cut through alert noise. Increasingly, the same underlying monitoring data is being used by both IT ops and SecOps teams, just looking for different types of problems.
SOC-as-a-Service is making security operations center capabilities accessible to mid-sized companies that can’t justify building an in-house team. The framework is the same; the delivery model changes.
Why the Distinction Matters More Than You’d Think
Role confusion in this space has real consequences.
Organizations that assume IT ops covers security end up discovering the gap during a breach. Teams with strong IT operations management but no DevOps practices fall behind competitors shipping five times faster. DevOps teams without SecOps integration build up vulnerability debt that compounds silently with every release.
The organizations that get it right treat these as complementary disciplines not competing ones. IT Operations provides the stable foundation. DevOps builds the delivery engine on top of it. SecOps makes sure the whole thing doesn’t become an attack surface.
Each depends on the others. A SOC trying to monitor an environment IT ops doesn’t fully understand is working half-blind. A DevOps team shipping into infrastructure that SecOps can’t see is building fast in the wrong direction. And IT ops running without DevOps and SecOps involvement is managing for yesterday’s problems.
The Bottom Line
IT Operations keeps the infrastructure alive. DevOps makes sure new software reaches users without killing it. SecOps makes sure nobody hostile gets to decide how either story ends.
They’re not interchangeable. They’re not even competing. They’re three disciplines that work best when they’re built around each other sharing context, overlapping on tooling, and aligned on what a healthy, high-performing, secure environment actually requires.
Start with clarity on what each team owns. Everything else headcount, tools, frameworks follows from that. Confusion about roles is expensive. Getting it right upfront isn’t.
Frequently Asked Questions
1. What is IT Operations (IT Ops)?
IT Operations manages and maintains IT infrastructure to ensure systems run smoothly, securely, and without interruption.
2. What is the main difference between IT Ops, DevOps, and SecOps?
- IT Ops: stability and uptime
- DevOps: speed and delivery
- SecOps: security and threat response
3. How do DevOps and SecOps work together?
They integrate security into development through automated testing, continuous monitoring, and shared workflows (DevSecOps).
4. What are the responsibilities of IT Operations teams?
Managing infrastructure, monitoring systems, handling incidents, ensuring uptime, and supporting users.
5. How do IT Ops, DevOps, and SecOps collaborate?
They share tools, data, and workflows to align infrastructure, development, and security for faster and safer operations.
6. What does SecOps do in an organization?
SecOps monitors systems, detects threats, and responds to incidents using a security operations center (SOC) and related tools.
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.