What is Medusa Ransomware and how does it operate?
Medusa ransomware is a Ransomware-as-a-Service (RaaS) group active since 2021 that uses double extortion encrypting victim data with AES-256 while simultaneously stealing it and threatening public exposure if ransom isn’t paid. It gains access primarily through Medusa ransomware phishing campaigns and unpatched vulnerabilities, then uses legitimate tools like PowerShell and RDP to move laterally and avoid ransomware threat detection before deploying its payload.
Introduction
Majority of ransomware attacks do not introduce themselves. When encrypted files are displayed, and a ransom note is dropped on the screen, attackers already spent days or weeks behind the scenes within the network mapping systems, stealing data, and preparing to do the most harm possible.
Medusa ransomware has turned this quiet-before-the-storm approach into an art form.
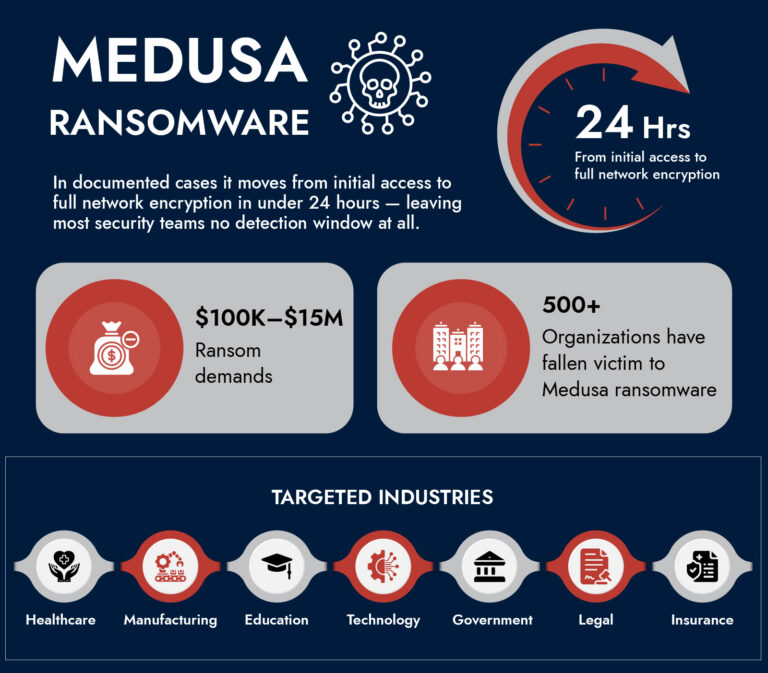
Since emerging in 2021, Medusa has grown from a niche threat into one of the most active ransomware operations of 2025. The FBI, CISA, and MS-ISAC issued a joint advisory on it in March 2025 a signal of how seriously the security community is taking it. With over 500 confirmed victims across healthcare, education, manufacturing, and financial services, and attacks surging 42% between 2023 and 2024, Medusa isn’t slowing down.
That is what makes Medusa really dangerous, here is the fact: it is not based on some exotic, never-before-seen techniques. It succeeds as it travels at a high speed, goes unnoticed, and strikes organizations that are not following the correct signals.
This blog breaks down what those signals are, where Medusa hides, and how threat detection and response built on behavioral intelligence can catch it before the encryption begins.
What Makes Medusa Different from Other Ransomware Threats
Not all ransomware groups are built the same. Medusa operates as a Ransomware-as-a-Service (RaaS) platform meaning developers build the tooling and recruit affiliates who carry out the actual attacks. Affiliates pay a cut of the ransom, and in return get access to infrastructure, negotiation support, and a leak site called the “Medusa Blog” where stolen data gets published if victims don’t pay.
This model matters for detection because it means the people executing the attack may vary, but the underlying tools and tradecraft stay consistent. That consistency creates detectable patterns.
What distinguishes Medusa at a technical level:
- Double (and sometimes triple) extortion: Data is encrypted and exfiltrated. Non-payment means public leaks and, increasingly, media notifications and DDoS attacks during negotiations.
- AES-256 and RSA encryption: Files get the .medusa extension. Without the attackers’ decryption key and there’s no public decryptor recovery without clean backups is nearly impossible.
- LOTL (Living off the Land) techniques: Medusa relies heavily on tools already present in the environment PowerShell, WMI, PsExec, RDP making malicious activity difficult to distinguish from legitimate admin work.
- Backup destruction: Before encrypting, Medusa deletes shadow copies, disables backup services, and targets over 280 Windows services. If your recovery plan depends on local backups, Medusa has already thought about that.
- Speed: Dwell time from initial access to encryption is often just days. In some 2025 incidents, the gap was measured in hours.
How a Medusa Ransomware Attack Actually Unfolds
Understanding the attack chain is the foundation of any solid detection strategy. Medusa doesn’t randomly appear on your network it follows a structured sequence, and every stage leaves traces.
Stage 1: Initial Access via Phishing or Exploited Vulnerabilities
The Medusa ransomware phishing campaign is one of its primary entry points. Attackers send carefully crafted emails that impersonate trusted entities IT support, vendors, financial institutions often with malicious attachments or links pointing to credential-harvesting pages. Spear-phishing variants target specific individuals, making them convincingly relevant and harder to flag on instinct alone.
Beyond phishing attacks, Medusa exploits unpatched vulnerabilities aggressively. Known targets include Microsoft Exchange (ProxyShell), ConnectWise ScreenConnect, Fortinet EMS, and GoAnywhere MFT. Medusa affiliates have been observed weaponizing newly disclosed CVEs within days of public release well before most organizations complete their patch cycles.
Initial access brokers (IABs) are another route. These are third parties who specialize in breaking into networks and selling that access to ransomware groups. Medusa pays anywhere from $100 to $1 million for a reliable foothold, which means even organizations that haven’t received a single phishing email may already have a compromised credential floating around on a criminal marketplace.
Stage 2: Establishing Persistence and Evading Detection
Once inside, Medusa works to stay invisible. Attackers use PowerShell with obfuscated payloads, often executing scripts directly in memory to avoid writing files to disk. They create new user accounts, disable security tools using BYOVD (Bring Your Own Vulnerable Driver) techniques, and reboot systems into Safe Mode to bypass endpoint protections.
This is where behavioral threat detection becomes critical. Standard signature-based tools won’t catch this because they’re looking for known malicious files and Medusa isn’t using them. What it is doing is creating patterns: unusual PowerShell execution, unauthorized account creation, unexpected driver installations, Safe Mode reboots. These are the tells.
Stage 3: Discovery and Lateral Movement
With persistence established, Medusa begins mapping the network. WMI queries gather system and user information. Tools like Advanced IP Scanner identify network topology. RDP is used for lateral movement and because RDP is a legitimate Windows tool, this traffic typically doesn’t raise alarms in environments without behavioral analytics.
Mimikatz or similar credential dumping tools extract passwords from memory, giving attackers access to additional accounts and systems. The goal is to reach domain controllers and backup infrastructure before triggering the final payload.
Stage 4: Data Exfiltration
Before encrypting anything, Medusa steals it. Rclone, Robocopy, and tunneling tools like Cloudflared or Ngrok proxy services are used to move data to external destinations. This is the leverage for the second half of double extortion if you rebuild from backups, they still have your data and they’ll publish it.
Network-level detection that watches for large, unusual outbound data transfers especially to cloud storage endpoints or proxy services catches this stage when endpoint tools miss it.
Stage 5: Encryption and Impact
The final stage is where Medusa announces itself. Shadow copies are deleted, backup services are stopped, and file encryption begins across the network. The ransom note (!!!READ_ME_MEDUSA!!!.txt) appears in affected directories, along with Tor site addresses for negotiation.
By this point, the window for containment without data loss is essentially closed. The entire value of a detection strategy is catching this before Stage 5.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security
Why Traditional Detection Misses Medusa
Most organizations have security tools. Most organizations that get hit by Medusa also had security tools. The problem isn’t the absence of technology it’s what the technology is looking for.
Signature-based detection compares files and traffic against a database of known threats. Medusa minimizes custom malware and instead uses tools that already have trusted signatures: PowerShell, WMI, legitimate RMM software like AnyDesk and ConnectWise. These sail past signature checks.
Alert fatigue is a real operational problem. Medusa’s use of living-off-the-land techniques generates a lot of activity that looks like routine administration. Without tuned rules that understand context who is running PowerShell, from where, doing what analysts drown in false positives and miss the genuine signals.
Slow patch cycles create the entry points that Medusa exploits. A monthly patching cadence is insufficient when Medusa affiliates can weaponize a newly disclosed vulnerability in days.
No visibility at the network level means exfiltration goes undetected. Many environments have good endpoint coverage but weak or absent network traffic analysis. Medusa’s data theft happens at the network layer.
What Effective Medusa Ransomware Detection Looks Like
Effective Medusa ransomware detection isn’t a single control it’s a layered approach that generates signal across multiple stages of the attack chain.
Behavioral Indicators to Monitor
At the endpoint:
- PowerShell execution with base64-encoded or obfuscated commands
- In-memory script execution (fileless activity)
- Installation of unknown drivers, especially those associated with EDR killers
- Volume Shadow Copy deletion (vssadmin delete shadows)
- Mass file renaming or modification events
- Unexpected Safe Mode reboots
- Creation of new local admin accounts
At the network level:
- Unusual RDP connections especially lateral, east-west movement between internal systems
- SMB enumeration across the network
- Traffic to Tor exit nodes or known Medusa infrastructure
- Large outbound data transfers to cloud storage (Rclone patterns, Ngrok proxies)
- DNS requests for unusual domains at odd hours
- Cloudflared tunnel activity
Authentication signals:
- Credential access from unexpected locations or hours
- Multiple failed logins followed by a success (brute-force pattern)
- Accounts accessing systems they’ve never accessed before
IOCs Worth Integrating
Your SIEM and EDR rules should include:
- File extensions: .medusa appended to encrypted files
- Ransom note filename: !!!READ_ME_MEDUSA!!!.txt
- Tor domains associated with Medusa negotiation infrastructure
- Known C2 domains and IP addresses from current threat feeds
- Rclone client strings in network traffic (SSH-2.0-rclone)
- Hash values from CISA’s March 2025 advisory (AA25-071A)
Threat intelligence feeds that update these IOCs continuously are more valuable than static rule sets Medusa affiliates rotate infrastructure and tooling regularly.
Why Threat Intelligence Matters Against Medusa
Reactive detection catches attacks in progress. Threat intelligence lets you anticipate them.
Medusa’s targeting isn’t random. It concentrates on high-value sectors healthcare, education, manufacturing, technology in the US, UK, Canada, and Australia, with expansion into new geographies including Georgia and Brazil. Organizations in these sectors should treat Medusa as an active, imminent threat rather than a theoretical one.
Operationalizing threat intelligence means:
- Ingesting current IOCs from CISA advisories, FBI bulletins, and commercial threat intel platforms into your detection stack automatically
- Mapping Medusa’s TTPs against your environment’s MITRE ATT&CK coverage to find visibility gaps
- Tracking affiliate activity Medusa’s RaaS model means new affiliates bring slightly varied tooling, and early warning intelligence about active campaigns gives defenders lead time
- Sharing indicators within your sector’s information sharing groups (ISACs)
Medusa’s phishing campaigns in 2026 are now incorporating AI-generated, highly personalized lures at scale. Generic phishing awareness training isn’t enough anymore. Organizations need email security tools capable of detecting behavioral anomalies in email not just known-bad links and attachments.
Building a Detection-First Response Posture
Early detection is only valuable if it leads to fast, structured response. Here’s what that looks like in practice.
Immediate Containment Triggers
Don’t wait for confirmation of full compromise to act. Any of these should trigger isolation and investigation:
- Detection of shadow copy deletion commands
- Unexpected Rclone or Robocopy activity on non-admin systems
- Mass file modification events (>100 files renamed in a short window)
- Outbound traffic to Tor or known Medusa C2 infrastructure
- EDR or AV kill attempts via driver installation
Response Playbook Essentials
A Medusa-specific playbook should cover:
- Detection and alerting – Which rules fire, who gets notified, what’s the escalation path
- Isolation protocols – How to segment affected systems without cutting off forensic visibility
- Evidence preservation – Memory captures (WinPMEM), disk images, and log preservation before remediation starts
- Out-of-band communications – Medusa monitors victim communication; assume primary channels may be compromised
- Regulatory notification – GDPR, HIPAA, or PCI-DSS timelines for breach reporting; coordination with CISA or FBI
- Recovery sequencing – Restore from clean, verified backups in an isolated environment; validate integrity before reconnecting systems
The 3-2-1 backup rule (three copies, two different media, one offsite) is non-negotiable when no public decryptor exists.
In practice, the difference between a contained ransomware event and a full-scale incident often comes down to how quickly teams can validate these signals and act with confidence. This requires not just predefined playbooks, but real-time visibility across network, endpoint, and log data to confirm suspicious behavior without delay. Organizations that can correlate these indicators early, significantly reduce dwell time and limit the blast radius. Having visibility across multiple mediums allows teams to understand full scope of the attack, and act decisively without relying on fragmented tools. This level of insight is what enables organizations to move from reactive response to controlled, confident containment.
—Ibrahim Badawi, Sales Engineer, NetWitness
Medusa Ransomware Prevention: What Reduces Your Attack Surface
Detection catches attacks in motion. Prevention reduces how often they get that far.
Patch management as a priority, not a schedule. Medusa exploits newly disclosed CVEs within days. A monthly cycle creates weeks of exposure. Critical internet-facing systems VPNs, RDP gateways, mail servers, file transfer tools need priority patching with near-real-time awareness of new disclosures.
MFA everywhere RDP and remote access tools exist. A compromised credential without MFA is an open door. With MFA, it’s a stopped attack.
Network segmentation. Medusa’s lateral movement depends on flat, permissive internal networks. Segmentation limits blast radius dramatically a compromise in one zone doesn’t automatically reach domain controllers and backup systems.
Restrict and monitor RMM tools. Medusa abuses AnyDesk, Splashtop, ConnectWise, and similar tools for persistence and lateral movement. If these tools aren’t authorized on a system, their presence is an immediate red flag. If they are authorized, their usage should be narrowly scoped and monitored.
Email security that goes beyond basic filtering. Given the sophistication of Medusa ransomware phishing campaigns now including AI-generated spear phishing at scale organizations need behavioral analysis on email, not just reputation filtering.
Least privilege access. If a compromised account can only access what that user legitimately needs, lateral movement becomes significantly harder. Regular access reviews should be standard.
How Netwitness Supports Medusa Ransomware Detection and Response
Medusa wins against organizations that have fragmented visibility good endpoint coverage here, weak network monitoring there, no real-time correlation between them. It loses against environments where every layer feeds into a unified detection picture.
Netwitness is built around exactly that kind of visibility. The platform delivers:
- Full-packet network visibility that catches Medusa’s data exfiltration behaviors Rclone patterns, Cloudflared tunnels, unusual outbound volumes that endpoint tools miss
- Behavioral threat detection that identifies living-off-the-land activity in context, flagging anomalous PowerShell execution and lateral RDP movement without generating noise from legitimate admin activity
- Integrated threat intelligence that keeps IOC feeds file hashes, Medusa C2 infrastructure, phishing domains continuously updated across detection rules
- UEBA (User and Entity Behavior Analytics) that surfaces credential-based attacks: impossible logins, unusual access patterns, accounts behaving outside their baseline
- Automated detection and response workflows that compress time-to-contain from hours to minutes
When Medusa moves fast, defenders need to move faster. That requires a platform where detection, investigation, and response happen in the same environment not across five disconnected tools.
Key Actions to Take Against Medusa
If Medusa isn’t already on your threat model, it should be. Here’s a practical starting point:
- Run a coverage gap analysis against Medusa’s MITRE ATT&CK TTPs from CISA advisory AA25-071A. Identify which techniques your current stack detects and which it doesn’t.
- Check your RDP and remote access exposure. Any RDP-accessible system that isn’t behind MFA and VPN is a primary target.
- Verify your backup posture. Are backups truly offline and immutable? Have you tested restoration recently? Shadow copy deletion is Medusa’s first move your backups need to survive it.
- Update your threat intelligence feeds. Static IOC lists go stale fast. Medusa rotates infrastructure regularly.
- Train specifically for phishing at scale. Generic awareness training isn’t enough. Run simulations using current Medusa lure tactics.
- Know your detection-to-containment time. If you don’t know how long it takes your team to isolate a compromised host after an alert fires, you don’t know your actual risk exposure.
Conclusion
Medusa is effective not because it’s technically unprecedented, but because it moves methodically through environments where detection is fragmented and response is slow. It uses tools defenders trust, moves at speeds that outpace traditional patching and response, and builds leverage through both encryption and data theft.
The answer isn’t panic it’s visibility. Comprehensive, behavioral, continuous visibility across endpoints, network, identity, and log data, tied to threat intelligence that reflects what Medusa is doing right now.
Detection before encryption is the only outcome worth building toward. Every other outcome negotiating, paying, rebuilding from scratch costs more.
The question isn’t whether your organization is on Medusa’s radar. Organizations in healthcare, manufacturing, education, and financial services are squarely in scope. The question is whether your detection posture is ahead of the attack chain or behind it.
Frequently Asked Questions
1. What is Medusa ransomware and how does it operate?
Medusa ransomware is a RaaS (Ransomware-as-a-Service) operation that encrypts victim files using AES-256, appends the .medusa extension, and simultaneously exfiltrates data for public leak threats. It spreads via phishing attacks, stolen credentials, and unpatched vulnerabilities, using legitimate system tools to evade ransomware threat detection.
2. How do I detect if my system is infected with Medusa ransomware?
Key signs to detect ransomware from Medusa include: files renamed with a .medusa extension, a ransom note named !!!READ_ME_MEDUSA!!!.txt, deleted Windows shadow copies, mass file modifications, and unusual outbound data transfers. Behavioral threat detection platforms catch these patterns before full encryption occurs.
3. Which cybersecurity companies offer protection against Medusa ransomware?
Companies offering Medusa ransomware prevention and threat detection and response include Netwitness, CrowdStrike, Darktrace, Armis, and Picus Security. Effective protection requires platforms combining endpoint detection, network traffic analysis, and real-time threat intelligence since Medusa bypasses signature-based tools by using legitimate Windows utilities.
4. Can I recover files encrypted by Medusa ransomware without paying?
Yes, but only if clean, offline backups exist. No public decryptor is available for Medusa ransomware. Recovery requires isolating affected systems, preserving forensic evidence, restoring from verified backups, and using threat intelligence to confirm full attacker eviction before going back online. Report the ransomware attack to CISA or the FBI.
5. How can enterprises prevent ransomware attacks like Medusa?
Enterprise ransomware prevention requires: patching critical CVEs within days, MFA on all remote access, network segmentation, advanced email filtering to block phishing attacks, and behavioral threat detection that catches living-off-the-land techniques. Feeding current threat intelligence into your SIEM keeps detection rules aligned with active Medusa campaigns.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.





