What is a Security Operations Center (SOC)?
A Security Operations Center is a team that keeps an organization’s digital environment safe. It’s the place where security analysts watch over networks, look for anything suspicious, and step in before a small issue becomes a real problem. A SOC brings together people, processes, and the right tools to protect critical systems and keep information secure and available. In short, it’s the frontline team that holds the line while attackers constantly look for a way in.
Introduction
SOC or Security Operations Center is a term you will be hearing a lot of because it is an essential part of any organization that uses multiple technologies (e.g., cloud-based systems, remote-access devices, mobile devices, etc.). The SOC is responsible for keeping track of a lot of information from many different sources and reporting its status to senior management.
In this blog post, we will explain everything you need to know about SOC, including what they do and how they operate behind the scenes.
We’ll provide an overview of the tools available for the operation of a SOC, the staff necessary to operate a SOC, and the daily SOPs of a typical SOC. We’ll also outline a few of the best practices that can help organizations detect potential threats more rapidly, respond to them more effectively, and continuously improve their capabilities to respond to security events. You should consider this blog post a very useful introduction to how SOC supports the overall functioning of contemporary cybersecurity. 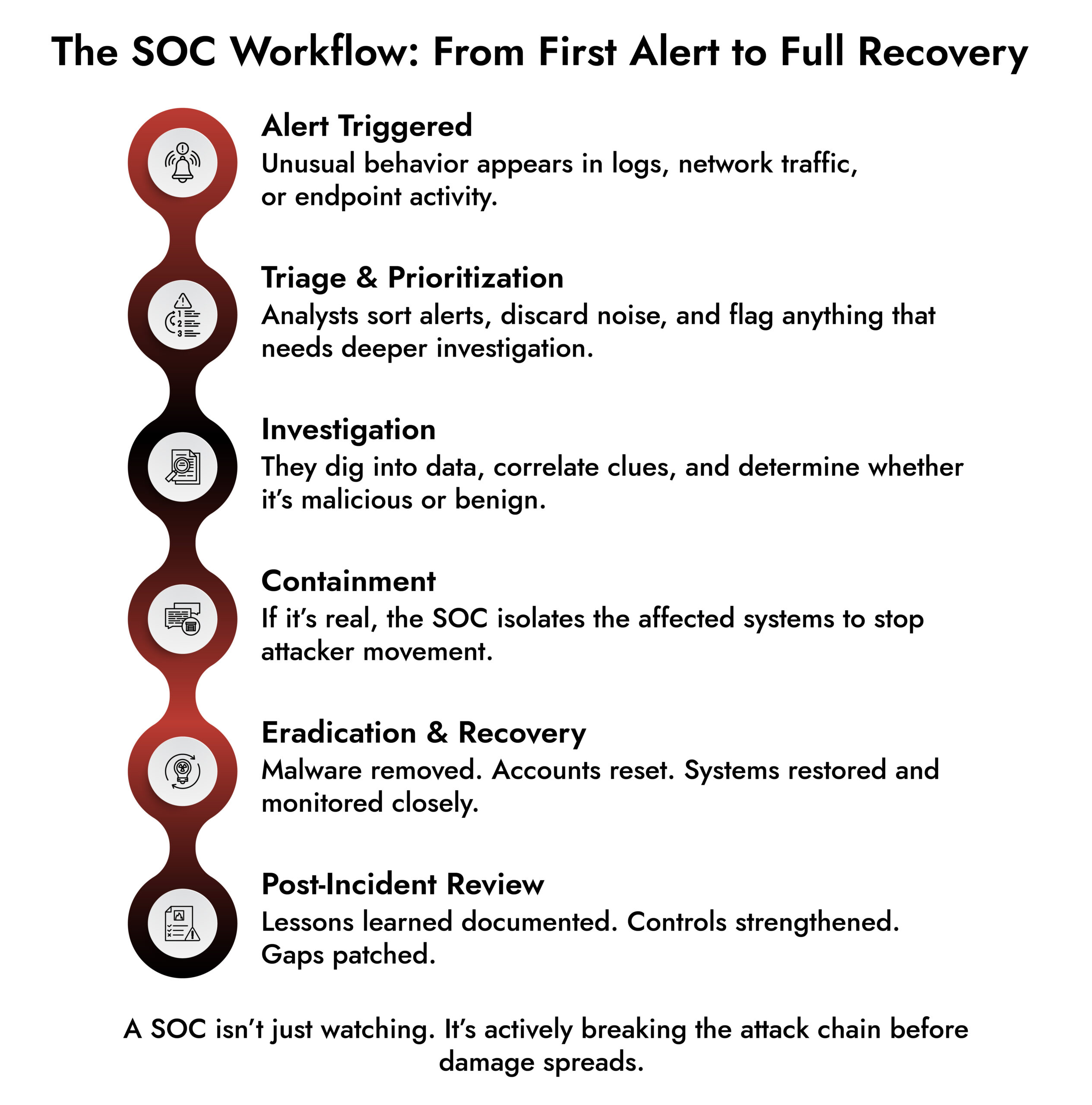
Why a SOC Matters
If you’ve ever wondered why companies invest heavily in SOC teams, here’s the simple answer: the threat landscape isn’t slowing down. Attackers move fast. A SOC helps organizations stay one step ahead.
Here’s what a strong SOC brings to the table:
Proactive Threat Mitigation: Attackers now no longer force their way in but hide or move quietly and linger. The job of a SOC is to detect and mitigate these early and stop them before they can do significant damage.
Rapid Incident Response: In the event of a breach, every moment counts. A SOC can minimize the time between when “an event occurs” and when “it has been contained.”
Around-the-clock Monitoring: Attacks happen 24 hours a day, 7 days a week. The SOC constantly monitors systems, including network traffic, logs on all servers, endpoints, and cloud environments.
Forensic Insight: In the aftermath of an incident, the SOC will provide details surrounding the event, what occurred, how it was executed, and how to prevent a recurrence.
Vulnerability Management: While a SOC can provide reactive resources, they can also identify any vulnerabilities present and assist the organization in addressing these vulnerabilities.
Threat Intelligence: A SOC keeps abreast of threat actors and their techniques and attack patterns, so they are not surprised in the future.
To sum it up: The SOC is the digital protector of today’s businesses. Without one, the risk of being compromised grows exponentially.
SOC Tools and Technologies
To have strong Security Operations Center (SOC) operations, the SOC must have the best available technology to power those operations. The core technologies powering the SOC operations include:
1. SIEM – Security Information and Event Management
The SIEM is the primary technology that collects logs from sources throughout your environment. SIEMs also allow security analysts to identify any unusual or suspicious behavior from these logs.
2. IDS/IPS – Intrusion Detection and Prevention Systems
These technologies support the security analyst by collecting and monitoring the incoming/outgoing network traffic to identify suspicious activities. IDS provides security alerts for suspicious activities, while IPS provides a real-time response by blocking an attack that was detected by an IDS.
3. Endpoint Detection and Response – EDR
With their accessibility, endpoints make an easy target for cybercriminals. The EDR tools allow security teams to monitor endpoints for legitimate usage and identify abnormal or atypical behaviors, as well as isolate quarantined devices and minimize their damage before they cause further harm.
4. Threat Intelligence Platforms
Threat intelligence platforms are a collection of threat data collected from a variety of sources including, but not limited to, threat feeds, public indicators of compromise, and industry reports. Security analysts use this data to help predict where future attacks will take place.
5. Automation and Orchestration – SOAR
Security Orchestration Automation and Response (SOAR) enable security analysts to automate the manual processes associated with repetitive tasks performed on multiple security tools and construct the proper workflows for security analysts to enable all of the security technologies to work together in concert with each other so that analysts end up spending more time performing investigations rather than clicking on buttons.
6. Case Management System
A Case Management System (CMS) serves as a “workspace” for the security operations center. A CMS will house all the information about security incidents, evidence collected, notes recorded, and status updates so that SOC personnel do not drop any critical evidence of a security incident.
Best Practices for a Strong SOC
A high-performing SOC isn’t built overnight. Here are the practices that keep it efficient and ready for anything:
Incident Lifecycle Management: Clear steps for identifying, analyzing, containing, and recovering from threats.
Threat Hunting: Actively looking for hidden threats instead of waiting for alerts.
Defined Playbooks: Pre-built responses that guide analysts through the right actions quickly and consistently.
Regular Training: Threats evolve fast. SOC teams stay sharp with continuous learning and real-world exercises.
Constant Improvement: Tools, rules, and processes must be updated frequently to stay ahead of emerging threats.
SOC Challenges and How Teams Solve Them
Running a SOC isn’t easy. Here are the biggest challenges most teams face:
Evolving Threats: Attackers experiment constantly. SOCs rely on threat intelligence and analytics to track new tactics.
Shortage of Skilled Professionals: Security talent is hard to find. Organizations bridge the gap with better training, automation, and managed services.
Data Overload: Huge volumes of logs can overwhelm analysts. SIEM systems and automated triage help cut through the noise.
Complex Compliance Requirements: From GDPR to industry-specific rules, SOCs help maintain compliance through monitoring, reporting, and policy enforcement.
Tool Integration Issues: Many organizations accumulate tools that don’t talk to each other. SOAR security help unify the stack
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.
The Benefits of Implementing a SOC
When a SOC is running well, the entire organization feels the impact:
- Lower cybersecurity risk
- Faster and more coordinated incident response
- Better visibility across networks and endpoints
- Easier compliance reporting
- Long-term cost savings by avoiding large-scale breaches
A SOC is more than a security function, it’s a strategic investment in operational stability.

Where SOCs are Heading Next
Cybersecurity changes quickly, and SOCs are evolving with it. Here are the trends shaping the future:
- AI and Machine Learning
- Automated detection, smarter analytics, and faster investigations.
- Cloud-Based SOC Models
- Security that scales with hybrid and multi-cloud environments.
- Threat Intelligence Sharing
- More collaboration across industries to spot patterns early.
- IoT Security
- More devices mean more attack surfaces. SOCs now monitor everything from laptops to industrial sensors.
NetWitness: A Strong Partner for Modern SOCs
NetWitness has been a reputable brand in cybersecurity for a valid purpose. As attackers become more sophisticated, NetWitness has consistently enhanced its features to assist SOC teams in staying ahead.
What distinguishes NetWitness is its capacity to integrate visibility throughout the whole environment – logs, network traffic, endpoints, cloud, and also IoT devices. This coherent data model, along with automated analytics and SOAR features, provides analysts with a comprehensive view rather than disjointed insights.
The majority of vendors continue to assemble solutions in various ways. NetWitness SOC offers a cohesive platform that organizations can implement as SaaS, on-premises, or through a managed service. Regardless of whether you’re managing an established SOC or creating one from the ground up, NetWitness provides the insight, agility, and knowledge required to prevent intrusions, allowing for more restful nights
Conclusion
A Security Operations Center (SOC) is now an essential part of protecting any modern organization. A SOC that is well-run will reduce risk, improve detection capabilities, simplify compliance requirements and provide business continuity when the threat environment changes daily.
NetWitness combines everything an organization needs for building an SOC into a single integrated solution: Detection, Analytics, Automation and Incident Response. An organization’s SOC will no longer be a reactive entity; they will now be able to proactively defend against threats before they occur.
If you want to strengthen your organization’s security posture, NetWitness can help.
Frequently Asked Questions
1. What is a Security Operations Center?
A security operations center (SOC) is a centralized hub where security experts observe, identify, examine, and react to cyber threats. It integrates individuals, workflows, and security operations center technologies to help organizations uphold robust protection against cyber threats.
2. What are the main roles and responsibilities of a SOC?
SOCs have many duties and responsibilities, including but not limited to monitoring cyber/internet activities (network traffic), assessing cyber alert(s), performing forensics investigations (during a breach), managing vulnerabilities, making incident response plans and executing incident responses. SOCs use threat intelligence, automation and managed service providers (MSPs) to identify, protect and secure the organizations’ digitized assets.
3. What are the different types of security operations centers?
There are three (3) forms or deployments of SOCs:
- An internal SOC that is fully managed by the organization
- A Managed Security Service (MSSP) provider that is externally managed
- A virtual SOC that is managed via the cloud, and as such, does not contain a dedicated physical building or location
- A hybrid SOC that is composed of internal and external resources, allowing for an increase in flexibility within organizations.
4. What tools are used in a SOC?
A variety of tools are employed in today’s Security Operations Centre (SOC):
- SIEM (Security Information and Event Management)
- IDS/IPS (Intrusion Detection & Prevention System)
- EDR (Endpoint Detection and Response)
- Threat Intelligence Platforms
- SOAR (Security Orchestration, Automation & Response)
- Case Management System
These tools enhance the SOC’s ability to protect the organization’s network, facilitate timely responses to security events, and enable continuous operational efficiencies.
5. What is the SOC framework?
The Security Operations Centre (SOC) Framework encompasses how a SOC operates, including its functions (such as monitoring for threats), processes, tools, roles & responsibilities of the people working in it, incident response procedures, vulnerability management procedures, incident reporting, and continual improvement of its processes to maintain an effective level of coverage for all security concerns.
6. How does a SOC improve cyber defense?
An SOC combines its cybersecurity strategies with the best available technology and personnel trained in providing cyber security solutions. It provides an organization with:
- Proactive detection and mitigation of threats;
- Immediate response to incidents when they occur;
- Continual monitoring of their network and endpoints;
- Assistance with compliance with legal requirements placed upon the organization; and
- Input into the strategic decisions of cybersecurity.
7. What is the difference between a SOC and a cyber security operations center?
A Cyber Security Operations Center is another name for a SOC. It highlights the SOC’s role in combating cyber threats, IT security, and other security operations solutions, and creating a secure operating environment for the organization.
8. How does the SOC operate in the IT and OT environments?
SOCs manage and protect both IT and OT (Operational Technology) environments through Security Operations Solutions and give the organization the ability to see and understand their entire network, including all types, including Industrial Control Systems, cloud services, IoT devices, and organizations, equally in terms of overall security across all organizational levels.
9. Why are SOC networks so important to security?
The security of SOC networks is critical to security because SOCs are among the primary targets of cyber threats. SOCs must continuously monitor network activity for suspicious activity, allow for immediate response to identifying potential intrusions, minimize risk of data breach, and prevent interruption/rescheduling of operations based on cyber threat incidents.
10. How can SOCs provide organizations with secure operations solutions?
SOCs can provide organizations with a wealth of secured operations solutions through integrated platforms like NetWitness, which provide a complete suite of threat detection, threat analysis and threat response tools. Such platforms include automation, SOAR capabilities and enhanced visibility and analytics, which not only provide SOCs with the capability to effectively protect digital assets but also improve compliance, reduce risk and increase operational efficiency for the cybersecurity operations of the business.




