What should a good cybersecurity assessment test include?
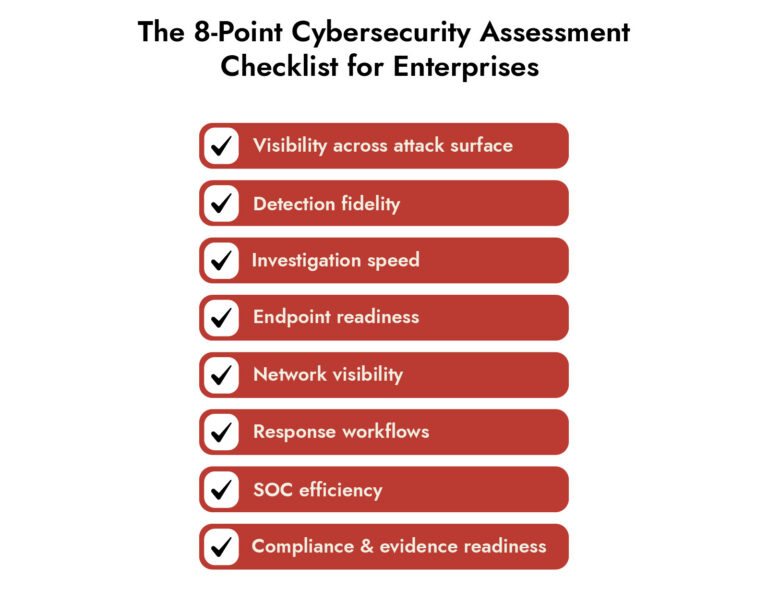
An enterprise cybersecurity assessment checklist should test eight things: visibility, detection fidelity, investigation depth, endpoint readiness, network visibility, response orchestration, analyst efficiency, and evidence readiness. If even two or three of those areas are weak, it points to a broader underlying issue.
Security leaders rarely struggle to take a cybersecurity assessment. The real challenge is trusting what the results actually mean.
Assessments that only confirm tool presence miss the operational question executives actually care about: whether the enterprise can reduce business risk under live-fire conditions.
A meaningful cybersecurity assessment should therefore do more than inventory tally. It should expose blind spots, weak telemetry, noisy detections, shallow investigations, manual response friction, and the hidden cost of fragmented cybersecurity tools.
What an Enterprise Cybersecurity Assessment Should Actually Measure
A mature cybersecurity risk assessment is not just a review of controls against a framework. It is an operational test of whether the security stack helps analysts answer the right questions quickly and with confidence.
At the enterprise level, the assessment should measure six outcomes:
- whether the organization has usable visibility across endpoint, network, cloud, identity, and log sources
- whether detections are accurate enough to reduce noise without missing meaningful attacker behavior
- whether analysts can reconstruct an incident without stitching together disconnected evidence by hand
- whether cybersecurity incident response workflows are repeatable, documented, and timely
- whether the SOC can scale without adding friction faster than headcount
- whether the security program produces measurable cybersecurity risk mitigation, not just more alerts
That framing aligns closely with current guidance. NIST CSF 2.0 emphasizes risk outcomes, while CISA’s incident response and SIEM/SOAR guidance reinforces the need for standardized response processes, centralized logging, and operationalized detection and orchestration.
Cybersecurity Assessment Checklist for Enterprises
1) Visibility Across the Attack Surface
Visibility is the foundation of every other judgment. If a security team cannot see control-plane events in the cloud, east-west traffic in the data center, identity activity in SaaS, or endpoint behavior outside the corporate network, the rest of the assessment becomes theoretical.
IBM reported that 30% of breaches in its 2025 study involved data spread across public cloud, private cloud, and on-premises environments.
What enterprise teams should evaluate:
- whether telemetry covers endpoint, network, identity, cloud control plane, SaaS activity, and critical business applications
- whether east-west network traffic, remote endpoints, and privileged administrative activity are visible
- whether log retention and search depth support investigation, forensics, and compliance requirements
- whether the environment can show what happened, not just what was logged
A common weakness appears when strong log collection is mistaken for full visibility. Log collection tools often miss lateral movement, encrypted traffic analysis, and unrecorded application behavior. Many enterprises only discover that gap during a major incident, when investigators need packet-level or session-level evidence that was never captured.
The 8-Point Cybersecurity Assessment Checklist for Enterprises
- Visibility across attack surface
- Detection fidelity
- Investigation speed
- Endpoint readiness
- Network visibility
- Response workflows
- SOC efficiency
- Compliance & evidence readiness
2) Detection Fidelity and Alert Quality
Enterprises struggle with too many alerts and still lack confidence, context, or investigative value. A cybersecurity assessment should examine whether detections help analysts prioritize real attacker activity or merely create operational drag.
What enterprise teams should evaluate:
- whether detections cover attacker behavior across identity, endpoint, network, and cloud rather than only static indicators
- whether high-volume alerts include enough context to support triage without multiple console pivots
- whether detection engineering is mapped to real attacker techniques and routinely tuned
- whether cybersecurity awareness efforts are measured by reporting speed and downstream attack interruption, not just training completion
A frequent enterprise failure mode is mistaking alert volume for detection maturity. High volume without confidence is not strong detection. It is outsourced uncertainty, handed to an already overloaded SOC.
3) Investigation Speed and Attack Reconstruction
Security leaders often discover that an alert may arrive quickly, but the investigation still stalls because evidence lives in separate tools, timelines must be built manually, and the SOC cannot reconstruct attacker movement without escalating to specialists.
Mandiant reported a global median dwell time of 11 days in M-Trends 2025. More telling, dwell time was 10 days when organizations discovered malicious activity internally but 26 days when external entities provided notification. Speed matters, but internally owned investigative depth matters more.
What enterprise teams should evaluate:
- whether analysts can move from alert to full attack timeline without exporting data into separate tools
- whether investigations can correlate identity, endpoint, network, and cloud evidence in one workflow
- whether historical search, session reconstruction, and artifact retrieval are available on demand
- whether tier-one and tier-two analysts can answer key scoping questions without waiting on engineering teams
4) Endpoint Readiness
Endpoint controls remain essential, but an enterprise assessment should go beyond agent coverage percentages. The real test is whether endpoint telemetry is deep enough to expose attacker behavior, whether remote systems remain visible, and whether response actions can be executed without delay.
Endpoint readiness must cover not only malware execution, but also behavioral anomalies, persistence, privilege use, lateral tooling, and remote response capability.
What enterprise teams should evaluate:
- whether endpoints remain visible when off-network, roaming, or hosted in cloud environments
- whether the platform captures process, file, registry, user, and network activity with sufficient forensic depth
- whether responders can isolate hosts, kill processes, quarantine artifacts, and preserve evidence quickly
- whether endpoint detections can be correlated with identity and network events for accurate scoping
5) Network Detection and Lateral Movement Visibility
Endpoint and log telemetry do not eliminate the need for network evidence. They simply change how often teams realize they needed it sooner. A strong cybersecurity assessment checklist should specifically test whether the organization can see internal movement, suspicious east-west communications, protocol abuse, and exfiltration patterns that may never appear clearly in endpoint or application logs.
What enterprise teams should evaluate:
- whether the environment can inspect and investigate internal traffic, not only ingress and egress
- whether lateral movement, command-and-control behavior, and suspicious protocol use are detectable
- whether packet, metadata, or session evidence is available for deeper forensic review
- whether network detections reduce ambiguity or simply create another alert stream
6) Response Orchestration and Workflow Maturity
Most enterprises have incident response plans. Fewer have response systems that behave consistently across real cases, business units, regions, and toolsets. A security assessment should examine the gap between documented cybersecurity incident response and operational response.
What enterprise teams should evaluate:
- whether response playbooks are connected to the tools analysts actually use
- whether case management, evidence capture, escalation, and approvals are consistent
- whether common containment actions are automated where appropriate and governed where necessary
- whether responders can document actions cleanly for legal, audit, and executive review
A recurring weakness is the manual handoff problem. Detection sits in one system, ticketing in another, enrichment in a third, and containment in yet another. The incident moves, but context does not. That is not a staffing issue. It is a workflow design issue.
7) Analyst Efficiency and SOC Scalability
A cybersecurity assessment should ask a blunt question: does the current stack make analysts better, or merely busier?
What enterprise teams should evaluate:
- how many console pivots are required to triage, investigate, and respond to a typical incident
- whether repetitive enrichment and validation tasks are automated
- whether detections arrive pre-correlated or require manual stitching
- whether staffing growth is improving outcomes or just absorbing platform complexity
Strong SOC scalability comes from better context, fewer handoffs, and more consistent workflows.
8) Compliance, Governance, and Evidence Readiness
Compliance still matters, but the enterprise assessment should treat it as an output of mature operations, not as proof of mature operations. Boards, auditors, regulators, and insurers increasingly expect evidence that the organization can demonstrate control effectiveness, incident traceability, and accountable response.
NIST CSF 2.0 ties cybersecurity activity to governance and enterprise risk management, while CISA’s response playbooks and logging guidance reinforce the need for standardized procedures, retained evidence, and centralized records that support both operational response and post-incident review.
What enterprise teams should evaluate:
- whether evidence is retained in a way that supports forensics, audit, and regulatory review
- whether incident records capture decisions, actions, timestamps, and scope changes
- whether control reporting can be backed by operational proof, not just policy assertions
- whether the program can defend its cybersecurity risk mitigation decisions to internal and external stakeholders
This is where many security assessments become misleading. They validate governance artifacts while failing to test whether the organization could actually defend its decisions after a serious breach.
Uncover the Dual Nature of AI in Cybersecurity
-Common AI misconceptions in cybersecurity
-Risks & limitations of AI-based tools
-Responsible AI adoption strategies

What Mature Enterprises Do Differently
Mature enterprises do not succeed by simply reducing the number of cybersecurity tools they use. They succeed by reducing the friction between them.
They unify telemetry so endpoint, network, cloud, identity, and log data can be analyzed together. Detection is driven by context, not alert volume. Analysts can pivot across evidence quickly, reconstruct attacks without manual stitching, and follow consistent response workflows. Success is measured in outcomes such as faster investigations, cleaner containment, and stronger cybersecurity risk mitigation.
This is why the market is shifting toward integrated detection and response. NetWitness enables this by unifying data collection and analysis across domains, allowing analysts to investigate, correlate, and respond within a single platform. It brings together visibility, detection, and response so teams can move from alert to resolution without operational gaps.
Frequently Asked Questions
1. What is a cybersecurity assessment checklist?
A cybersecurity assessment checklist is a structured way to evaluate whether an organization’s security program can identify exposures, detect threats, investigate incidents, and support response with enough speed and evidence to reduce risk.
2. Best cybersecurity assessment tools for small businesses
For small businesses, a smaller set of well-run tools covering vulnerability scanning, endpoint detection, email protection, secure configuration review, backup validation, and managed detection or incident response support, where internal staffing is limited, is well-suited.
3. How to choose a third-party cybersecurity assessment provider?
Enterprises should look for a cybersecurity services company or incident response partner that can demonstrate technical depth in forensics, detection engineering, cloud and identity investigation, reporting discipline, and executive communication during live incidents. Retainer terms, evidence handling, escalation speed, and post-incident improvement guidance matter as much as assessment methodology.
4. What tools are used for cybersecurity assessments?
Common tools include vulnerability scanners, attack surface management platforms, CSPM or CNAPP tools, EDR and NDR platforms, SIEM, SOAR, identity analytics, threat exposure validation, phishing simulation, and forensic investigation tools. The right mix depends on whether the assessment is focused on exposure discovery, cybersecurity awareness, cybersecurity incident response, or broader cybersecurity management maturity.
5. What role does compliance play in cybersecurity assessments?
Compliance helps define governance, evidence, and required controls. A true cybersecurity assessment tests whether those controls produce usable visibility, reliable detection, and defensible response under pressure.