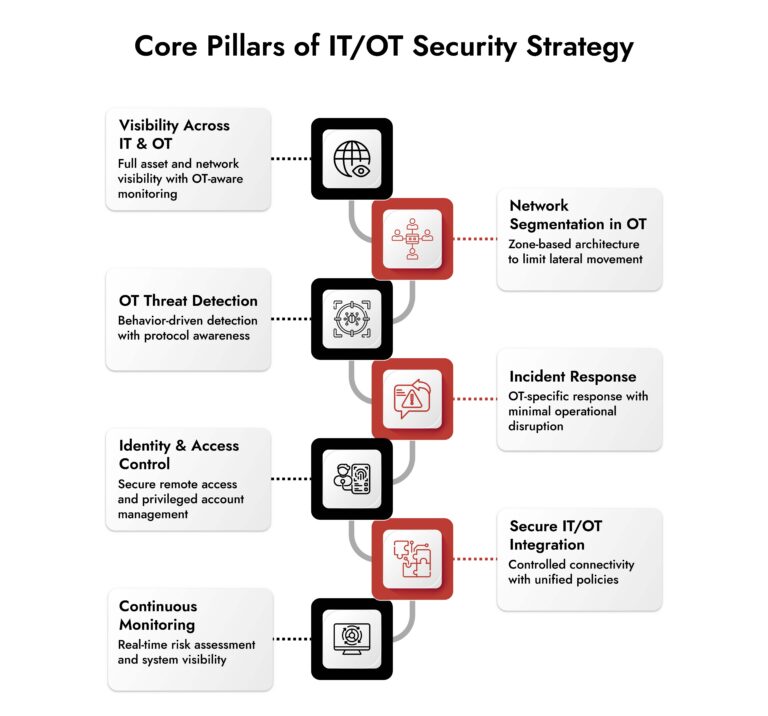
What is an IT/OT security strategy?
An IT/OT security strategy is a structured approach to protecting both IT systems and operational technology networks from cyber threats. It focuses on improving visibility, enabling OT threat detection, applying network segmentation in OT, and implementing incident responses to ensure secure and reliable operations across connected environments.
Why IT OT Security Is No Longer Optional
Walk into any modern plant or utility environment and you’ll see convergence in action. SCADA systems talking to cloud dashboards. PLCs feeding analytics engines. Remote access everywhere.
What this really means is simple:
your operational technology cyber security posture is now directly tied to your IT exposure.
And the risk is not theoretical anymore.
Attackers are targeting OT because downtime is expensive, safety is critical, and legacy systems are easier to exploit.
This is where a structured IT OT security framework becomes essential.
Pillar 1: Full Visibility Across IT and OT Environments
You cannot secure what you cannot see. Most organizations still operate with fragmented visibility. IT teams monitor endpoints and logs. OT teams rely on isolated systems and manual checks.
That gap creates blind spots.
A strong OT security strategy starts with unified visibility across:
- Industrial protocols (Modbus, DNP3, OPC)
- Network traffic between IT and OT layers
- Asset inventory across legacy and modern systems
- User activity and remote access
This is where best network monitoring for operational technology plays a critical role. You need tools that understand industrial environments, not just traditional IT traffic.
Without this, ot threat detection becomes reactive instead of proactive.
Pillar 2: Network Segmentation in OT Environments
Flat networks are one of the biggest risks in OT. Once an attacker gains access, lateral movement becomes easy. That’s how small breaches turn into plant-wide disruptions. Network segmentation in OT is not just a best practice. It is a containment strategy.
Key approaches include:
- Separating IT and OT networks with secure gateways
- Creating zones and conduits based on criticality
- Restricting communication between systems using least privilege
- Monitoring traffic between segments continuously
Done right, segmentation ensures that even if one system is compromised, the damage stays contained.
This is a core requirement in any serious IT OT cybersecurity framework.
Pillar 3: Context-Driven OT Threat Detection
Traditional security tools often fail in OT environments because they don’t understand industrial behavior.
In IT, anomalies are easier to define. In OT, a slight deviation in a process can either be normal or a sign of manipulation.
That’s why ot threat detection needs to be context-aware.
Effective detection includes:
- Behavioral baselining of industrial processes
- Protocol-aware anomaly detection
- Correlation between IT alerts and OT signals
- Real-time monitoring of control system commands
The goal is not just to detect threats.
It is to detect threats before they impact operations.
This is where choosing the best cybersecurity for operational technology networks becomes critical.
Pillar 4: Incident Response Built for OT Realities
Here’s where most strategies fall apart. Traditional incident response assumes systems can be isolated or shut down quickly. In OT, that’s not always possible.
Stopping a system could mean:
- Production loss
- Safety risks
- Regulatory consequences
So your incident response strategy must be tailored for OT environments.
That includes:
- Predefined playbooks for OT-specific scenarios
- Coordination between IT, OT, and safety teams
- Forensic capabilities that don’t disrupt operations
- Clear escalation paths for critical incidents
Speed matters. But in OT, precision matters more than speed.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.
Pillar 5: Strong Access Control and Identity Management
Remote access is one of the biggest attack vectors in OT environments.
Vendors, engineers, third-party contractors all need access. But unmanaged access creates risk.
A mature OT security strategy includes:
- Role-based access control across IT and OT
- Multi-factor authentication for remote connections
- Session monitoring and recording
- Strict control over privileged accounts
This is especially important when working with multiple OT security vendors and external partners. Access should never be assumed. It should always be verified.
Pillar 6: Secure Integration Between IT and OT Systems
Convergence is inevitable. But integration without security is dangerous. Organizations often connect IT and OT environments for efficiency, without aligning security controls.
That’s where many of the best companies for IT OT security integration stand out. They focus on:
- Secure data exchange between IT and OT systems
- Unified policy enforcement
- Cross-environment visibility and analytics
- Risk-aware integration architecture
The goal is not just connectivity. It is secure, controlled, and observable connectivity.
Pillar 7: Continuous Monitoring and Risk Assessment
OT environments are not static. New devices have been added. Firmware changes. Network paths evolve. Threats adapt. A one-time assessment is not enough.
Continuous monitoring should include:
- Real-time asset discovery
- Vulnerability tracking across OT systems
- Configuration drift detection
- Ongoing risk scoring
This is where log management tools and industrial monitoring platforms work together to provide actionable insights. When done right, this becomes the backbone of long-term operational technology cyber security.
Choosing the Right OT Security Vendors
Not all vendors are built for OT. When evaluating the best companies for IT OT security integration, the focus should go beyond features. Many traditional tools struggle with:
- Legacy systems
- Proprietary protocols
- Availability constraints
When evaluating OT security vendors, focus on:
- Deep understanding of industrial environments
- Support for OT-specific protocols
- Non-intrusive deployment models
- Strong integration with IT security tools
The best cybersecurity for operational technology networks is not the most feature-rich.
It is the one that fits your environment without disrupting operations.
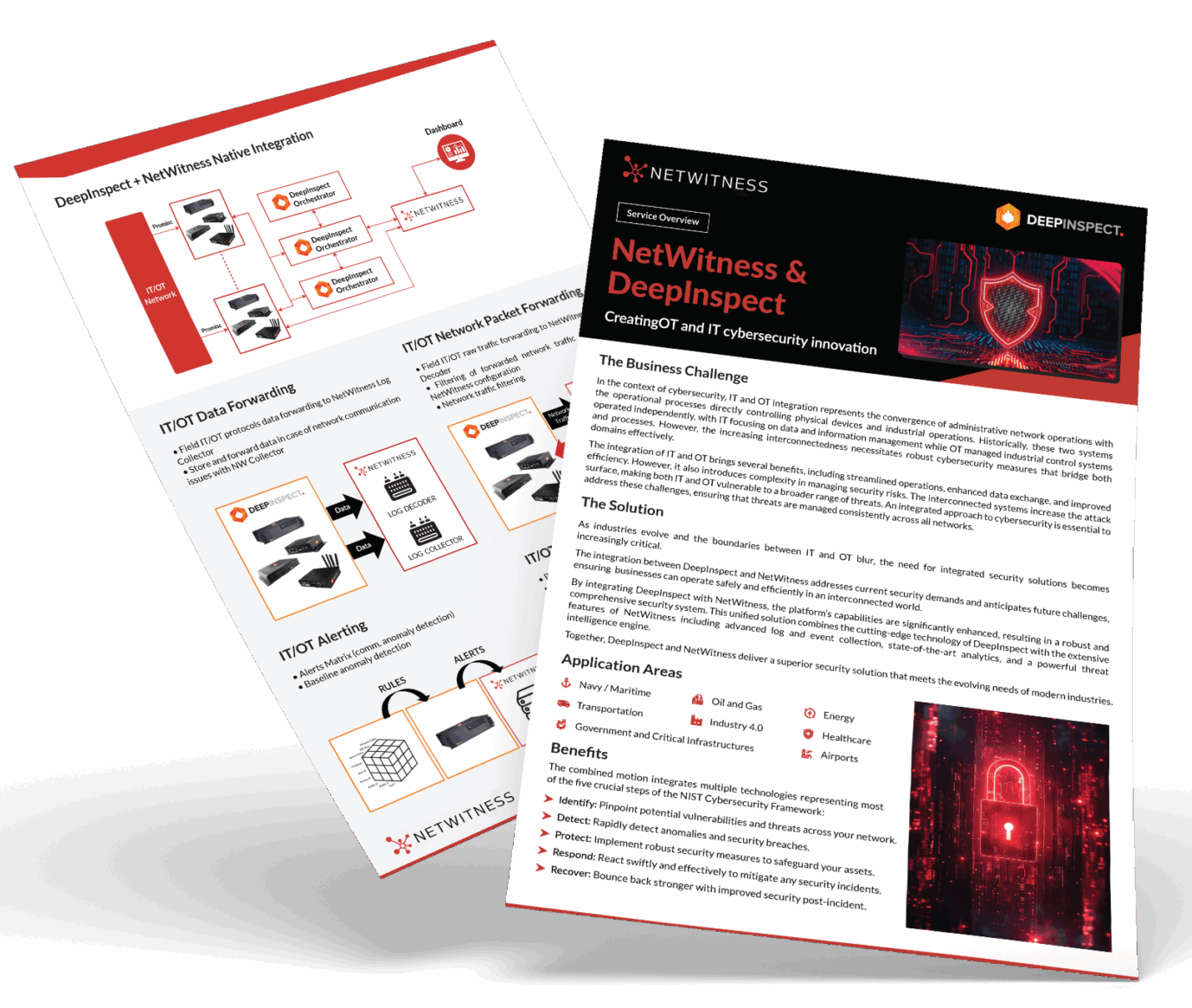
Where NetWitness Strengthens Your IT OT Security Strategy
Most IT OT security strategies look solid on paper but fall apart in execution. Among the best companies for IT OT security integration, the difference comes down to execution. Most strategies fail because tools don’t work together in practice. The gap is always the same. Disconnected tools. Fragmented visibility. Slow response.
NetWitness closes that gap.
- Sees everything in one place with deep network visibility across IT and OT
- Understands threats in context by combining network, log, and endpoint data
- Connects IT attacks to OT impact so nothing is investigated in isolation
- Enables faster, coordinated response without disrupting operations
This is the shift: from managing separate security layers to running a unified detection and response system built for converged environments.
Building a Practical IT OT Cybersecurity Framework
Let’s bring it all together. A strong IT OT cybersecurity framework is built on:
- Unified visibility across environments
- Segmented and controlled network architecture
- Context-aware threat detection
- OT-specific incident response
- Identity and access control
- Secure IT-OT integration
- Continuous monitoring and risk management
Miss one of these, and the entire strategy weakens.
Conclusion
Most organizations think IT OT security is about adding more tools. It’s not. It’s about building a system where visibility, control, and response work together across environments that were never meant to be connected. That’s the real challenge and also, the real opportunity.
Because the organizations that get this right don’t just reduce risk. They gain resilience, operational confidence, and the ability to scale securely in an increasingly connected world. Because in the end, the advantage doesn’t come from more tools. It comes from working with the best companies for IT/ OT security integration that can turn disconnected systems into a coordinated defense.
Frequently Asked Questions
1. What are the core pillars of an IT/OT security strategy?
The core pillars include visibility across IT and OT systems, network segmentation in OT, OT threat detection, incident response tailored for operational environments, identity and access control, secure IT/OT integration, and continuous monitoring.
2. Why is visibility important in IT/OT security?
Visibility allows organizations to identify assets, monitor network activity, and detect threats early. Without it, blind spots increase the risk of undetected attacks in operational technology environments.
3. How does network segmentation improve OT security?
Network segmentation in OT limits attacker movement by isolating systems into controlled zones. This reduces the impact of breaches and helps protect critical industrial processes.
4. What is the importance of incident response in IT/OT security?
Incident response ensures organizations can quickly detect, contain, and recover from cyber incidents without disrupting operations. In OT environments, it also helps maintain safety and compliance.
5. How can organizations build an effective IT/OT security strategy?
Organizations should adopt a structured IT OT cybersecurity framework that includes visibility, segmentation, threat detection, incident response, access control, secure integration, and continuous monitoring, supported by the right OT security vendors and tools.
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.