Key Takeaways:
- Firewalls are still a foundational system in network security.
- Firewalls deliver more value when integrated and not in isolation.
- Firewall-based protection includes traffic monitoring, policy enforcement, threat inspection, logging and alerting, and adapting to new trends.
- Firewalls must work in combination with identity, endpoint, and behavior-based tools to enforce traffic decisions dynamically rather than relying on static rules.
- Successful firewall integration requires technology, process, and people to work together.
Born in the 1990s, network firewall security was enough to safeguard the systems of that time. But today, is it enough to stand up to adversaries that have evolved way ahead of their time?
It is definitely not enough on its own, but it is a core component of a much larger, interconnected security ecosystem. Network security firewalls are still relevant today, but they become formidable only when integrated with other security systems.
As most of the organizations move to either cloud or hybrid work environments, integrating firewalls with existing network security tools has become essential for visibility, faster detection, and stronger response.
This blog dives into what network firewall security really means today, why integrating it with other network security tools is crucial, which security systems firewalls should integrate with, and which best practices ensure a successful integration.
What is Network Firewall Security?
In simple words, a firewall is a barrier between private networks and any other external network. It checks the network traffic against preset rules or policies and decides when it should be allowed, blocked, or inspected further.
Firewalls monitor, control, and enforce the security policies on network traffic entering or leaving the private network.
Firewall protection has evolved since it was introduced. Modern firewalls are capable of more than just packet filtering. Today, their features include:
- Deep packet inspection
- Application-level controls
- Intrusion prevention capabilities
- Threat intelligence feeds.
Firewalls reduce the attack surface and prevent unauthorized access, playing a role of frontline control.
What are the 5 Key Steps in Firewall-Based Network Protection?
Having a deep knowledge of how network firewall security actually works and protect helps security leaders to plan their integration requirements and improve operational outcomes. Here are the 5 ways in which firewalls protect:
Traffic Monitoring:
The main function of the network firewall security is to track the traffic entering and leaving the network. It collects information about source and destination IP addresses, ports, protocols, applications, and services to classify the traffic.
For SOC teams, this step of traffic monitoring and identification is important. When the traffic is accurately classified, security alerts carry richer context. This improves detection accuracy, faster investigation, and lower manual efforts.
Policy Enforcement:
Firewalls classify the traffic as to whether it should be allowed, blocked, or inspected further accordance with security policies. For organizations, this policy enforcement is a way to balance risk tolerance and operational reality. When the policies are overly permissive, the threat exposure increases. And overly restrictive policies hamper day-to-day operations. Well-designed policies help reduce unnecessary exposure while supporting business workflows.
Threat Inspection:
Traditional firewalls were designed for network traffic monitoring and policy enforcement, but today’s modern firewalls go beyond. They analyze the traffic for known attack patterns and suspicious activities. Hence, they can also help stop a wide range of threats at the network perimeter.
For SOC teams, this network firewall security activity acts as an early warning system. When combined with behavioral and endpoint data, the firewall’s findings can become valuable context for deeper investigation.
Logging and Alerting:
Firewalls generate detailed logs and alerts about traffic movement and policy violations. This telemetry is a high-fidelity data source for investigations, compliance reporting, and proactive threat hunting.
Adapting to Trends:
The security policies change continuously based on incidents, threat intelligence, and environmental changes. Adjusting firewalls’ policies ensures that defenses are always aligned with the current threat landscape. Regularly tuned firewalls are stronger as they are relevant, effective, and supportive of evolving security strategies.
Why is it Necessary to Integrate Firewalls with Existing Network Security?
Firewalls are effective, but there are many reasons why they need support from other tools. Modern attacks have evolved to exploit identities, endpoints, cloud services, and internal networks that cannot be handled with standalone firewalls. In isolation, firewalls are also limited in the context they can provide. They cannot fully represent how an attack unfolds across the environment, which is the need of the hour.
Integrating firewalls with existing security systems helps fill the real-world gaps, such as:
- Context Enrichment: Firewalls see the traffic that flows between the networks, but it is unable to understand who the user is, what happened before or after the traffic event, etc. The firewall output is a generic alert, such as “suspicious traffic detected,” without clarity on impact or intent.
- Faster Threat Detection and Response: Fragmented firewall telemetry means longer investigations about what happened, who did what, and more across other tools. With integration, the data is correlated with endpoint, identity, and network behavior data to accelerate detection. Enriched data also helps analysts trigger response workflows more quickly.
- Support for Zero Trust Network Security: Zero trust means no implicit trust across the network, internal or external. Firewalls work on the same principle but are limited to the network, which is not enough in today’s threat landscape. It needs to, therefore, extend its perimeter to identities, device posture, and behavioral analytics. In isolation, firewalls continue to enforce static rules. But by integrating it with other tools, they can enforce context-aware access decisions, which is foundational to zero-trust network security.
- Operational Efficiency: Firewall integration with other tools reduces tool sprawl, duplicate alerts, and manual workflows. It helps SOC teams to gain centralized visibility, and CISOs to gain clearer reporting and risk insights.
In conclusion, integration transforms firewall protection from a simple enforcement system into a strategic security sensor and control partner.
What Security Systems Should Firewalls Integrate With?
To strengthen the security systems, the network firewall security should be integrated with:
Security Information and Event Management (SIEM):
Firewall and SIEM integration enables centralized log collection, correlation, and long-term analysis. Firewall logs provide important network information that helps validate alerts, support compliance, and improve threat hunting. For SOCs, this integration is often the backbone of investigations.
Network Detection and Response (NDR):
Firewall and NDR integration brings behavioral visibility. NDR supports network firewall security in identifying abnormal traffic patterns, command-and-control activity, and lateral movement that may get missed by firewalls in isolation. This is particularly valuable in hybrid and east-west traffic scenarios.
Endpoint Security (EDR/XDR):
Firewall telemetry and endpoint data together create visibility around how threats communicate across the network. They help SOC teams trace attacks from initial access to movement and exfiltration. This end-to-end visibility boosts decision confidence and supports faster response.
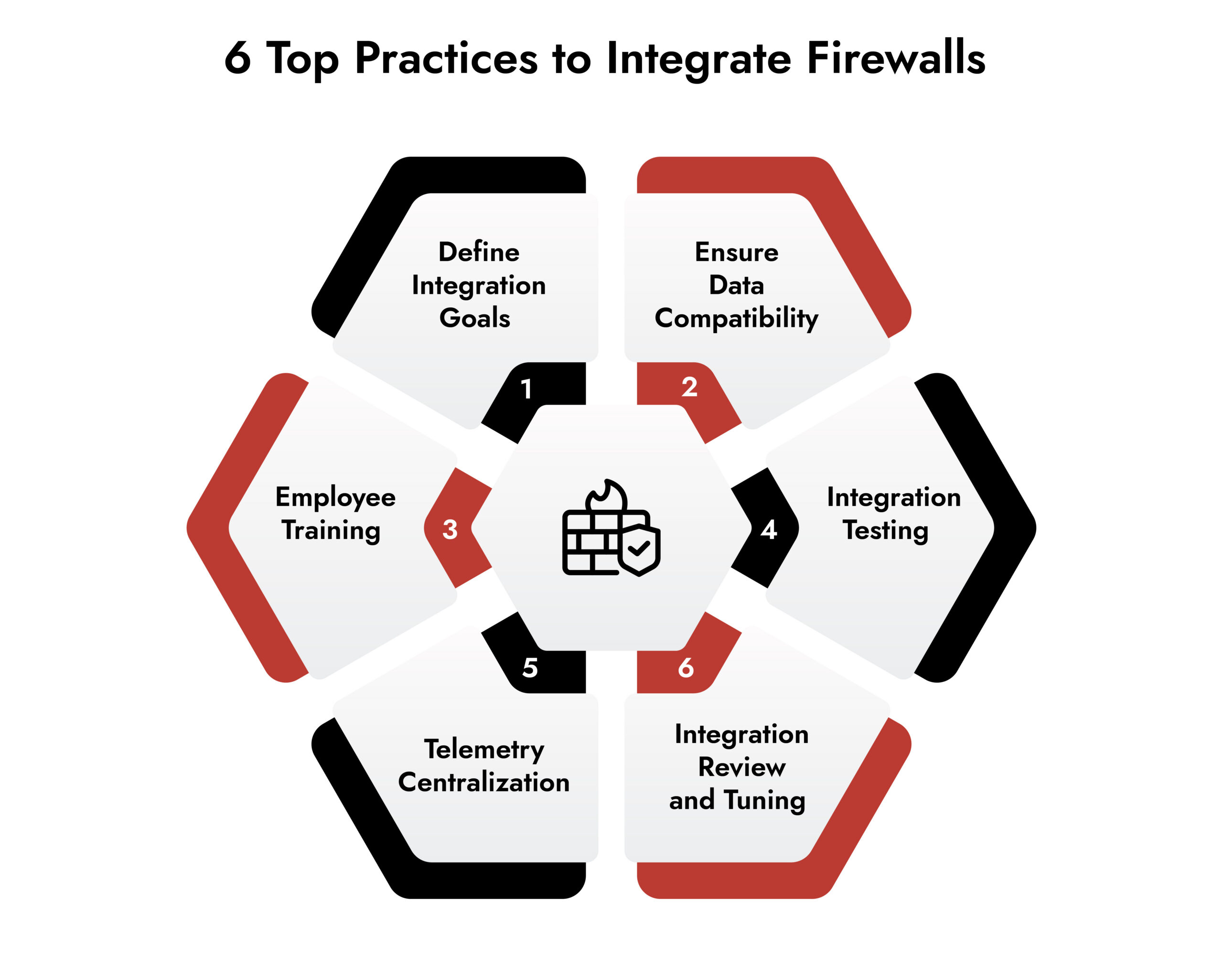
Best Practices to Integrate Firewall with Existing Network Security:
1. Define the integration goals:
Before integrating the firewall with any of your existing network firewall security systems, define what you want to achieve from the integration. The goals can include:
- Improving visibility across the network
- Improving detection rate or speed
- Reducing false positives
- Enabling automated response
This step helps align risk tolerance and business objectives through integration.
2. Ensure Data Compatibility
Each system speaks its own language, and integrating the two systems, without checking their compatibility, only leads to chaos. Integration is effective only if the data format generated by firewalls can be ingested by downstream systems.
3. Centralize Telemetry
One of the reasons why all the enterprise security systems should be integrated is to avoid fragmented data that does not show the whole picture of the attack. Hence, it is important to ensure that the firewall data is routed through a centralized visibility layer. It helps SOC teams to correlate firewall activity signals from endpoints, identities, and networks.
4. Test Integrations
Integration should be validated using realistic traffic patterns and incident scenarios. Testing helps ensure that the systems are behaving as expected and can meet the goals. Regular testing reduces the risk of failure during real-time runs.
5. Review and Tune Integrations
After deployment, integration should be monitored for log quality, alert volume, and policy overlaps to prevent blind spots and alert fatigue. The organizational policies also may undergo changes due to the threat landscape or regulatory requirements. Fine-tuning firewall policies and integration settings help ensure it is relevant and effective.
6. Employee Training
An integration will fail if the security team is unable to understand how to use the integrated firewall data. It is important to train them to understand the data and take actions in response. Empower them with clear documentation and training to reduce confusion and encourage adoption.
Conclusion
Firewalls have been a part of network security for decades, and their role is relevant even today. However, the way firewalls are used today needs to be changed; they need to work together with other tools in a network security ecosystem.
The result of this integration changes firewalls from just traffic enforcers to important sources of context and control. Its telemetry supports faster detection and response.
Ultimately, effective network firewall security is not about replacing firewalls or overloading them with expectations. It is about connecting it intelligently with a broader ecosystem in alignment with organizational goals. Enterprises that strategize integration by combining technology, processes, and people will be better positioned to face cyber risks.
About NetWitness Firewall Integration
NetWitness platform integrates with firewalls while preserving security posture and reliable visibility. It operates through clearly defined, controlled communication paths that align with zero trust principles and the existing firewall policies. This approach minimizes unnecessary exposure, protects the flow of critical security telemetry, and minimizes the risk of silent visibility gaps caused by misconfigured rules.
NetWitness Firewall integrations are easier to govern, audit, and maintain. They are designed to deliver consistent detection and response outcomes without compromising network controls.
DORA Compliance with NetWitness® Network Detection & Response (NDR)
Strengthen Digital Operational Resilience with Deep Network Visibility
Meet EU DORA requirements with continuous network monitoring, advanced threat detection, and automated response across complex financial environments.