Why does poor log visibility make lateral movement hard to detect?
Poor log visibility prevents security teams from seeing how attackers move between systems using legitimate credentials and normal tools. When network logs, identity logs, and system events are incomplete, delayed, or disconnected, lateral movement blends into normal activity. This allows attackers to escalate privileges, pivot quietly, and expand access before detection occurs.
Most breaches don’t start loud. They start quiet, partial, and easy to miss. And in almost every case, the reason attackers get comfortable moving around your environment is the same: poor log visibility. Poor log visibility, often caused by fragmented or incomplete SIEM logging, gives attackers the space they need to move quietly and expand access.
When logs are incomplete, delayed, or disconnected, defenders lose the ability to see how attackers pivot, escalate privileges, and blend into normal activity. Lateral movement thrives in the dark. This blog breaks down how weak log visibility enables stealthy attacks, why traditional approaches fall short, and what security teams need to do differently.
Why Log Visibility is the Backbone of Detection
Log visibility is not just about collecting data. It depends on consistent SIEM logging that provides continuous, reliable insight into what is happening across your environment in near real time.
Every authentication attempt, service interaction, file access, API call, and network connection leaves a trace. Network logs, system logs, identity logs, and application logs together form the narrative of an attack. When that narrative is fragmented or missing chapters, attackers gain room to maneuver.
Poor visibility usually shows up in a few common ways:
- Logs are collected from only a subset of systems
- Network monitoring is inconsistent across environments
- Log aggregation is delayed or incomplete
- Log processing strips context to save storage
- Log analysis happens only after alerts fire
Each of these gaps weakens detection. Combined, they create blind spots attackers actively exploit.
How Lateral Movement Really Happens
Lateral movement is rarely dramatic. Attackers do not usually spray exploits across the network. Instead, they move slowly, impersonating legitimate users and processes.
A typical path looks like this:
- Initial access through phishing, exposed credentials, or a misconfigured service
- Credential harvesting or token theft
- Internal reconnaissance using normal admin tools
- Accessing adjacent systems using valid credentials
- Repeating the process until high value assets are reached
At every step, logs exist that could expose the activity. Authentication logs show unusual access patterns. Network logs reveal connections between systems that rarely talk. Application logs expose privilege misuse.
But only if those logs are visible, correlated, and analyzed in context.
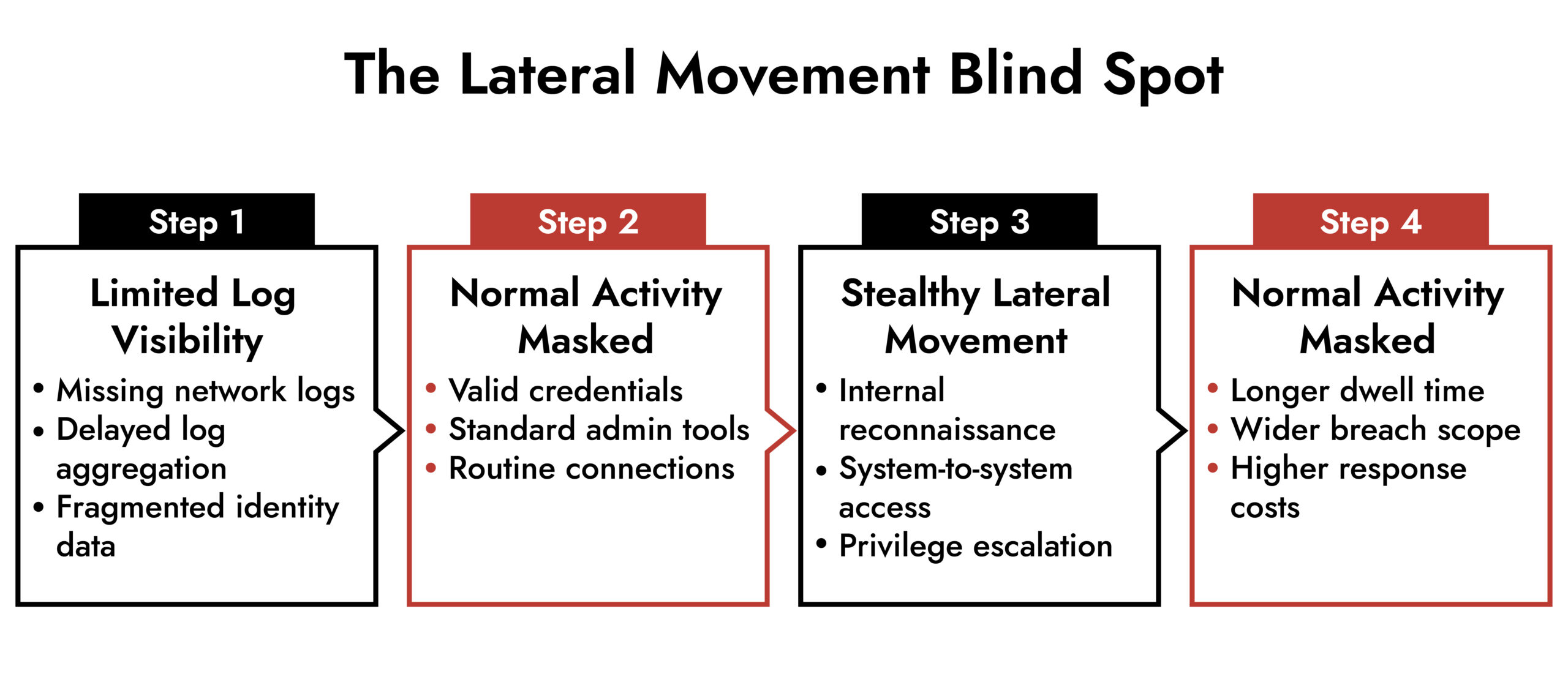
How Poor Log Visibility Enables Lateral Movement
When log visibility breaks down, attackers gain three major advantages.
1. They blend into normal behavior
Without full log coverage, defenders rely on partial signals. An authentication event may look legitimate in isolation. A network connection might seem routine without historical context.
Attackers exploit this by using built-in tools, legitimate credentials, and approved protocols. Without strong log monitoring and log visualization, these actions appear normal.
For example:
- A service account accessing multiple servers may not trigger alerts if logs are missing from key systems
- Remote access between hosts may go unnoticed if network logs are sampled or delayed
Poor visibility turns suspicious behavior into background noise.
2. Detection happens too late
Many organizations still treat log analysis as a reactive process. Logs are stored but not actively monitored. By the time an alert fires, lateral movement has already occurred.
Delayed log aggregation compounds the issue. If logs arrive minutes or hours late, SOC teams lose the ability to respond while the activity is happening.
Stealthy attackers depend on this delay. They know investigations start after damage is done.
3. Investigations lose context
Even when an alert is triggered, poor visibility slows investigations.
Missing logs force analysts to guess. Disconnected log sources make it difficult to reconstruct timelines. Inconsistent log formats complicate correlation.
Instead of answering key questions quickly, analysts get stuck asking:
- Was this user already compromised?
- Is this connection part of a larger pattern?
- How far did the attacker move?
Without complete log visibility, every answer takes longer. Attackers gain time.
Role of Network Monitoring in Exposing Stealthy Movement
Deep insight into Network traffic is critical for detecting lateral movement because it reveals interactions between systems, not just activity on individual hosts.
Strong network monitoring exposes:
- East-west traffic inside the network
- Unexpected protocol usage
- Rare or first-time connections
- Beaconing behavior and lateral scanning
When network monitoring is limited to perimeter traffic, internal movement becomes invisible. Attackers can pivot freely once inside.
High quality network information, combined with behavioral analysis, make lateral movement much harder to hide. Missing logs force analysts to guess. Disconnected log sources make it difficult to reconstruct timelines. Inconsistent log formats complicate correlation.
Simplify Log Management and Threat Detection with NetWitness® Logs
-Centralize and analyze logs from across your environment in one platform.
-Detect threats faster with real-time visibility and automated correlation.
-Reduce noise through advanced filtering and context-driven analytics.
Why Traditional Log Management falls Short
Many log environments struggle because they were built for compliance, not detection.
Common issues include:
- Log collection focused on servers but not identity, SaaS, or cloud workloads
- Log processing that removes fields needed for investigation
- SIEM log management tuned for volume reduction rather than visibility
- Static rules that miss low-and-slow behavior
Log visualization is often treated as optional. Dashboards exist, but they do not highlight relationships, timelines, or anomalies that matter for lateral movement.
The result is a log environment that technically exists but fails when it matters most.
What Effective Log Visibility Actually Looks Like
Strong log visibility is not about collecting everything blindly. It is about collecting the right logs, preserving context, and making them usable.
Effective environments share a few traits:
- Comprehensive log aggregation across identity, endpoints, networks, cloud, and applications
- Real-time or near real-time log monitoring
- Enriched logs that preserve user, asset, and session context
- Log analysis that focuses on behavior, not just events
- Visualizations that expose movement paths and timelines
When log visibility improves, lateral movement stops being invisible. Patterns emerge early. Small anomalies stand out.
How SIEM Helps Close Log Visibility Gaps
A modern SIEM plays a central role in improving log visibility by unifying SIEM logging across network, identity, endpoint, and cloud data sources.
Effective SIEM log management should:
- Normalize and correlate network information with identity and endpoint data
- Support scalable log processing without stripping investigative value
- Enable behavioral analytics for lateral movement detection
- Provide visual workflows that speed investigations
SIEM becomes the control plane for log visibility. Not just a storage layer, but an active detection engine.
When paired with strong network monitoring and consistent log collection, SIEM turns fragmented data into a coherent attack story.
The Business Impact of Poor Log Visibility
Stealthy attacks are not just a technical problem. They are a business risk.
Poor log visibility leads to:
- Longer dwell time
- Larger breach scope
- Higher investigation and recovery costs
- Increased regulatory exposure
- Loss of trust with customers and partners
Executives often focus on prevention tools, but detection is what limits damage. Log visibility is the foundation of that detection.
Closing Thoughts
Attackers move laterally because they can. They stay stealthy because defenders cannot see clearly.
Improving log visibility is one of the highest impact changes security teams can make. It does not require chasing new threats or reinventing architecture. It requires treating logs as active intelligence, not passive records.
When network information, identity data, and system events are visible, correlated, and analyzed in real time, lateral movement stops being subtle. It becomes detectable. And detectable threats are stoppable.
Frequently Asked Questions
1. What is log visibility in cybersecurity?
Centralized log management is the process of collecting, normalizing, storing, and analyzing logs from across an organization’s systems in a single platform. It provides unified visibility into activity across endpoints, networks, cloud services, and applications.
2. How does poor log visibility enable lateral movement?
By aggregating logs from multiple sources, centralized logging enables correlation and behavioral analysis. This helps security teams identify suspicious patterns that would be missed when logs are reviewed in isolation.
3. What types of logs are most important for detecting lateral movement?
SIEM log management adds analytics, correlation rules, and threat intelligence to centralized logs. This allows automated detection, faster triage, and more effective investigations across distributed environments.
4. How does poor log visibility affect SOC investigations?
Without centralized siem log management and log processing, SOC teams waste time chasing incomplete data. Investigations slow down, timelines break, and attackers stay active longer.
5. Can SIEM help overcome log visibility gaps?
Yes. SIEM improves log visibility by unifying siem logging, log aggregation, and log monitoring. With built-in log visualization and network monitoring, teams gain the context needed to detect lateral movement faster.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.