Compliance Logging in 2026: What is Most Important
A correct way to have compliance-ready logging best practices also means more than just storing logs; There is structured log data, real-time monitoring of logs and the ability to connect events with incident response. The regulators will want log records proving detection and response capabilities, not just records of activity for august 2026. In aligning an Enterprise Logging Strategy to compliance controls an organization will have fewer audit hurdles, and will save time when responding to breaches and therefore produce a measurable security benefit through their logging practices.
Introduction
Compliance audits no longer fail because of missing policies. They fail because of weak logging best practices.
As we start the year 2026, regulators are looking for not only raw logs, but also evidence of context, evidence of the ability to trace back all the points of origin of that data, and evidence from organizations of how they identify and deal with threats in a live environment. This will shift the focus of logging from simply what’s happening on the back-end of the operation of the organization to a key part of the strategic control of the operation and how that relates to risk management and incident response.
Numerous businesses continue to capture enormous volumes of log data but find it difficult to determine how to convert that information into these examples for use as an evidence source. This disconnect between what you have in your logs compared to what is needed to represent as evidence creates operational (and potentially regulatory) exposure. The difference between successfully passing or failing at a financial audit frequently lies only in the answer to one basic inquiry exhibited in the logs: What happened? When did it happen? Why did it happen?
Now let’s take a look at how you can build an effective logging policy that meets the auditor’s standard of review.
Why Logging Best Practices Now Define Compliance Readiness
Compliance frameworks have evolved. Logging is no longer a checkbox, it’s a verification mechanism.
Regulations like PCI DSS 4.0, updated ISO 27001 controls, and NIST guidelines now emphasize:
- Event traceability across systems
- Real-time detection capabilities
- Log integrity and retention policies
As indicated by the National Institute of Standards and Technology, effective logging is required to support security monitoring and forensic investigations. On the other hand, analysts point out that organizations that fail to have centralized log visibility often suffer from increased breach containment times.
What this really means is simple: If your logging best practices don’t support detection and investigation, they don’t support compliance either.
Core Components of Logging Best Practices in 2026
A compliance-ready logging strategy starts with structure. Without it, even the best logging tool becomes noise.
1. Define What to Log (and Why)
Start with intent, not volume. Every log should map to a security or compliance requirement.
Focus areas:
- Authentication and access events
- Privileged activity
- Network traffic anomalies
- Endpoint behavior
- Configuration changes
This ensures your logging data directly supports audit controls and incident response workflows.
2. Standardize and Normalize Logging Data
Raw logs from different systems don’t speak the same language. Normalization makes log analysis possible at scale.
Best practices:
- Apply consistent timestamps and time zones
- Enrich logs with user, asset, and threat context
Without normalization, your log monitoring becomes fragmented and unreliable.
3. Centralize Logging with Scalable Logging Software
Distributed logs create blind spots. Centralization eliminates them.
A modern logging software platform should:
- Aggregate logs from cloud, on-prem, and hybrid systems
- Enable high-volume ingestion without data loss
- Enable real-time querying and correlation
This is where a strong enterprise logging strategy really starts to come together, with visibility across your entire attack surface.
4. Ensure Log Integrity and Tamper Protection
Logs are evidence. If they can be altered, they lose value.
Compliance requires:
- Write-once-read-many (WORM) storage
- Cryptographic integrity checks
- Access controls and audit trails
Regulators increasingly verify whether your logging best practices protect logs from insider threats and post-breach manipulation.
5. Align Log Retention with Regulatory Requirements
Retention policies must balance compliance and cost.
Examples:
- PCI DSS: Minimum 1 year retention, 3 months immediately accessible
- Financial regulations: 5-7 years is common
- Critical infrastructure: Longer retention periods for forensic analysis
Your logging tool should accommodate tiered storage and management without impacting access.
Building an Enterprise Logging Strategy That Supports Incident Response
Logging without response is just documentation. A strong enterprise logging strategy connects logs directly to action. This means integrating logging with detection and response workflows.
Key capabilities:
- Real-time alerting based on behavioral anomalies
- Automated correlation of endpoints, networks, and user activity
- Investigation workflow that’s connected to log analysis
When done right, your logs don’t just record incidents, they drive incident response.
Simplify Log Management and Threat Detection with NetWitness® Logs
-Centralize and analyze logs from across your environment in one platform.
-Detect threats faster with real-time visibility and automated correlation.
-Reduce noise through advanced filtering and context-driven analytics.
Common Pitfalls That Break Logging Best Practices
Most failures aren’t technical. They come from how logging is designed, owned, and operationalized.
Logging Without Context, Not Logging Volume- Regulations often require extensive logging data collection and long-term retention. The gap appears when that data lacks structure and context.
- Raw logs without enrichment slow down log analysis
- Critical signals get buried despite active log monitoring
- Audit trails exist, but don’t translate into usable evidence
Strong logging best practices ensure logs are normalized, enriched, and ready for correlation.
Siloed Logging Tools Create Blind Spots- Disconnected logging tools fragment visibility across environments.
- No unified view across endpoints, network, and cloud
- Limited ability to correlate events across systems
- Delayed detection due to isolated data streams
An effective enterprise logging strategy requires centralized collection integrated with SIEM-driven correlation.
Lack of Ownership Weakens Logging Best Practices- When no team owns logging end-to-end, consistency breaks down.
- Logging policies vary across systems
- Retention and access controls become inconsistent
- Compliance gaps emerge during audits
Clear ownership ensures that logging best practices are enforced, measured, and continuously improved.
Poor Alignment with Risk Management Reduces Impact- Logging should reflect what matters most to the business. Without alignment, it becomes operational overhead.
- Logs don’t map to high-risk assets or critical workflows
- Alerts lack prioritization based on business impact
- Incident response becomes reactive instead of targeted
Mature logging best practices connect logging data directly to risk management priorities, ensuring both compliance and security outcomes are met.
The Role of Advanced Log Analysis and Monitoring
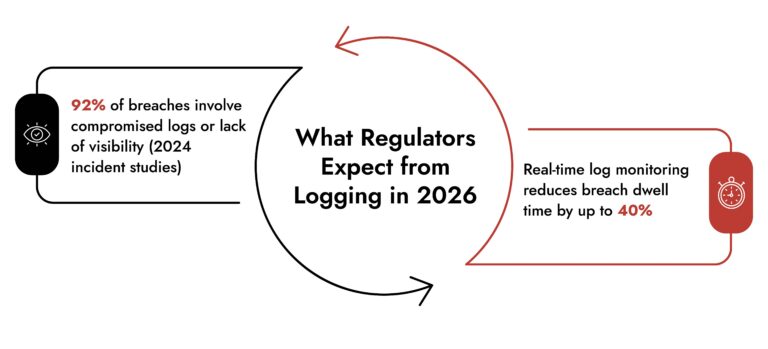
Speed matters. Delayed detection increases both breach impact and regulatory risk.
Modern log analysis goes beyond keyword searches. It uses:
- Behavioral analytics
- Machine learning-driven anomaly detection
- Correlation across multiple data sources
At the same time, continuous log monitoring ensures:
- Immediate detection of suspicious activity
- Faster investigation timelines
- Stronger audit trails
According to recent government advisories, organizations with real-time monitoring capabilities detect threats significantly earlier than those relying on periodic reviews.
How NetWitness Supports Compliance-Ready Logging
A compliance-ready logging strategy requires more than storage, it requires intelligence.
The NetWitness SIEM module brings together logging data, analytics, and response workflows in a unified platform.
Key capabilities:
- High-fidelity collection of logging data across endpoints, networks, cloud, and identity systems.
- Parsing of all logs into a unified data model, regardless of source, enabling consistent structure and context.
- Real-time correlation across devices and environments for faster threat detection.
- Continuous log monitoring with behavior-driven alerting.
- Deep, investigation-ready log analysis with enriched context.
- Built-in workflows that connect detection directly to incident response.
- Native support for compliance reporting and audit validation.
What stands out is the ability to move from logs to action. Instead of treating logs as static records, the platform enables dynamic incident response workflows tied directly to your enterprise logging strategy.
Practical Example: Turning Logs into Audit Evidence
Consider a financial services firm preparing for a regulatory audit.
Without structured logging best practices, they face:
- Incomplete access logs
- No clear audit trail for privileged users
- Delayed visibility into suspicious activity
They collect logging data, but it sits in silos. There’s no correlation, no prioritization, and no way to prove effective incident response.
After implementing a centralized logging pipeline integrated with a SIEM platform like NetWitness SIEM:
- Logs from endpoints, network, and identity systems are aggregated and normalized.
- The SIEM correlates events across multiple data sources in real-time.
- Behavioral patterns trigger alerts, not just static rules.
- Analysts use enriched log analysis to reconstruct attack timelines within minutes.
- Continuous log monitoring ensures immediate visibility into high-risk activity.
Result: Audit teams get clear, traceable evidence. Security teams move faster. The organization shifts from reactive logging to a measurable enterprise logging strategy that supports both compliance and risk management.
Conclusion
Back in 2006, logging was mainly an administrative function for a company; now it is a major element for business control.
Great logging practices will not just provide a company with visibility (in terms of providing a record of actions), but it also allows a company to have proof (meaning that it can identify issues such as risk, manage its response to issues in real-time and have sufficient documentation to be able to meet any auditing or compliance objectives it has).
The movement is to have logging become a mechanism to make decisions, not just develop a record of activity. If your company is not able to integrate all three parts of logging, then it is time to re-think your methodology for log management.
Depending on your company’s position in terms of geography, it is probably best to start small. Standardization and centralization need to be completed first.
Frequently Asked Questions
1. What is a compliance-ready logging strategy?
A compliance-ready logging strategy provides structured logging data that is both safe and adheres to the regulations driven by the compliance framework needed to produce a log audit trail; as well as support for incident response efforts; and provide real-time log monitoring.
2. What regulations require logging?
Regulations that govern the responsibilities of companies include PCI-DSS, ISO 27001, and those that have been issued by NIST which require logs of user activity, logs to be created to identify and mitigate any security threat to the company, and that logs be maintained for an audit trail of user activity.
3. What are logging best practices for compliance logging in 2026?
Centralized logging, data normalization, real-time monitoring, and secure log storage are some of the industry standard best practices for logging compliance. These practices include using logs as part of workflow for incident response and log analysis.
4. What challenges do organizations face compliance logging?
Organizations often struggle with managing large amounts of log data, breaking down logging data from various tools that don’t communicate, and monitoring logs effectively.
5. What tools are used for compliance-ready logging?
Many organizations utilize SIEM platforms, advanced logging software, and analytical log devices to provide central log storage, log analysis, and compliance reporting.
6. How does logging support incident response?
Logs are critical to providing evidence in investigations; therefore, implementing specific logging best practices allows for increased speed in accessing information pertaining to an event and determining if there is a threat during confidence based on findings when an incident response action is taken.
Choose the Right SIEM with Confidence