Why do organizations need to migrate from legacy SIEM tools?
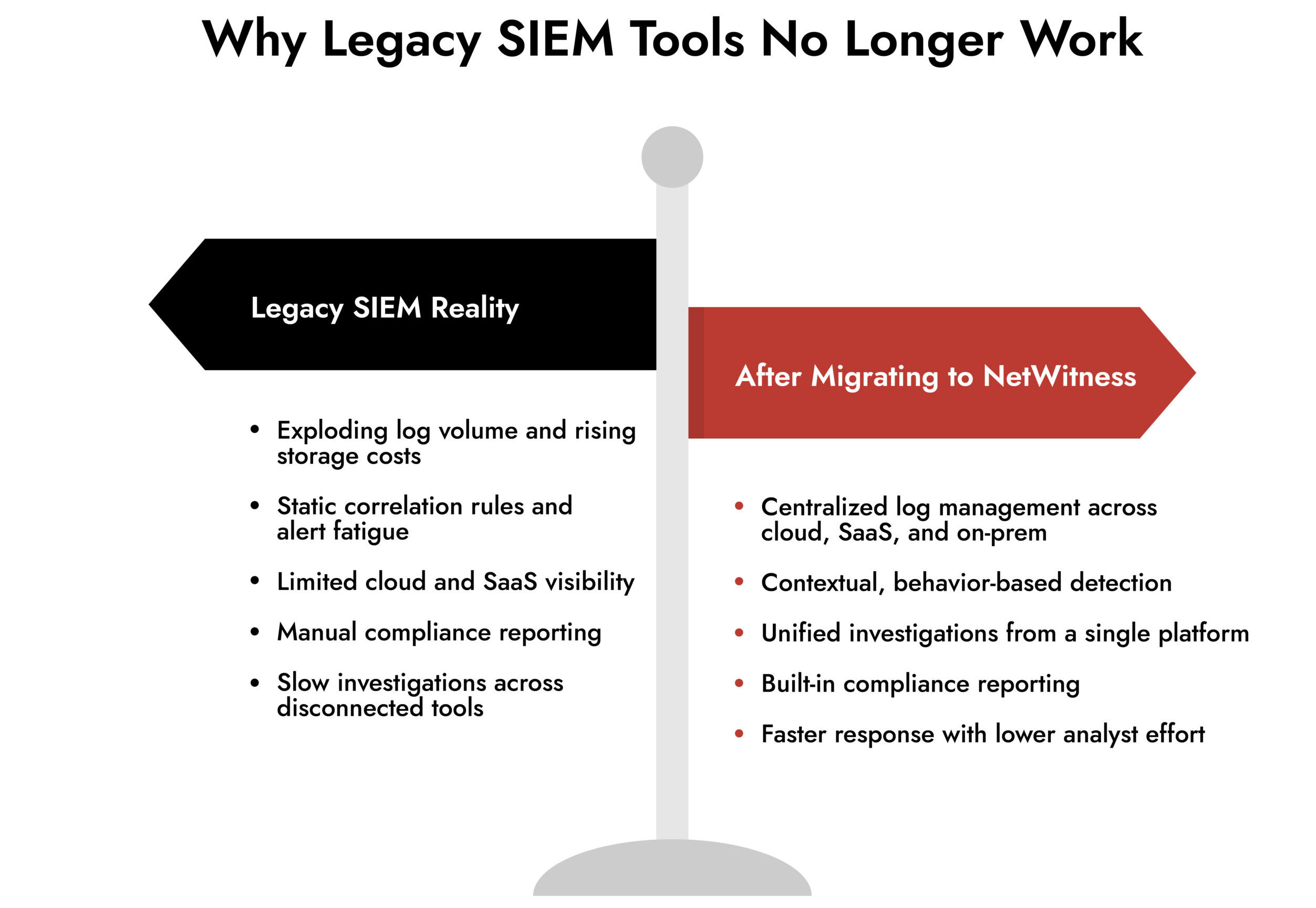
Organizations outgrow legacy SIEM tools when log volumes increase, cloud visibility becomes fragmented, and detection quality declines. Older SIEM platforms rely on static rules, costly storage, and manual workflows that do not scale across modern cloud, SaaS, and hybrid environments. Migrating to a modern SIEM platform like NetWitness helps restore visibility, reduce alert fatigue, and improve investigation and compliance efficiency.
Most SIEM migrations are triggered by friction, not ambition.
Alert fatigue keeps rising. Log volumes spike overnight. Cloud visibility feels bolted on instead of native. And every new integration adds cost and complexity. Legacy SIEM tools were never built for this operating reality. They were designed for static infrastructure, predictable data flows, and rule-heavy detection models that do not scale.
Migrating to a modern SIEM platform like NetWitness is less about replacing a tool and more about fixing how security intelligence actually works across today’s environments.
This guide breaks down how to migrate from legacy SIEM tools to NetWitness in a way that reduces risk, improves detection quality, and simplifies operations instead of adding another layer of overhead.
Why Organizations Outgrow Legacy SIEM Tools
Most legacy security information and event management SIEM tools struggle in three areas.
First, log management becomes expensive and slow. As data volumes increase across cloud, SaaS, and hybrid environments, teams end up storing massive amounts of logs they rarely use because searching them is painful.
Second, detection quality degrades. Static correlation rules generate alerts without context, forcing analysts to pivot across multiple tools just to understand what happened.
Third, compliance becomes a manual burden. Reporting frameworks like SOX, PCI, HIPAA, or NERC require constant tuning and manual evidence collection.
The result is predictable. Analysts spend more time managing the SIEM than using it to detect and respond to threats.
What Changes with a Modern SIEM Platform Like NetWitness
NetWitness SIEM was built to address the limitations that define legacy SIEM solutions.
Instead of treating log collection, detection, and investigation as separate workflows, NetWitness unifies them in a single platform.
Key differences include:
- Centralized log management across public cloud, SaaS applications, and on-prem environments
- Dynamic parsing and metadata creation at capture time, reducing the need for heavy normalization
- Threat intelligence enrichment built directly into ingestion, not bolted on later
- Compliance-ready reporting templates aligned to major regulatory frameworks
- Flexible deployment models, including on-prem, virtual, and cloud deployments across AWS and Azure
This architectural shift is what makes migration practical rather than disruptive.
Step 1: Audit Your Current SIEM Implementation
Before migrating, you need a clear picture of how your current SIEM tools are actually used.
Focus on operational reality, not documentation.
Identify:
- Log sources that actively support investigations
- Alerts that consistently lead to real incidents
- Compliance reports required by auditors
- Performance bottlenecks and storage cost drivers
- Manual enrichment or investigation steps analysts perform outside the SIEM
This step prevents the most common migration mistake: moving low-value data just because it exists.
Step 2: Define Migration Scope Around Use Cases, Not Data Volume
A successful SIEM implementation does not start with “ingest everything.”
It starts with high-impact use cases.
Typical starting points include:
- Identity abuse and suspicious authentication activity
- Cloud workload and SaaS monitoring
- Lateral movement detection across the SIEM network
- Regulatory reporting automation
NetWitness supports hundreds of log sources, including AWS, Azure, Office 365, Salesforce, and common infrastructure platforms. This allows teams to onboard the right data first and expand coverage as value is proven.
Step 3: Migrate Log Collection Without Breaking Operations
Log ingestion is often the most sensitive part of SIEM migration.
NetWitness simplifies this through broad protocol support, including Syslog, ODBC, SFTP, FTPS, and SNMP, combined with automated log source discovery and flexible parsing.
Instead of forcing full normalization upfront, NetWitness uses patented dynamic parsing to extract meaningful metadata at capture time. This accelerates detection and investigation while reducing onboarding friction.
For teams coming from rigid legacy SIEM tools, this alone shortens migration timelines significantly.
Top SIEM Use Case for Threat Detection
-Uncover hidden threats with unified log and event analysis.
-Centralize security monitoring across endpoints, network, and cloud.
-Speed up detection and streamline incident response with correlated alerts.
-Empower your SOC with actionable insights and compliance-ready reporting

Step 4: Rebuild Detection with Context, Not Rule Sprawl
Legacy SIEM solutions rely heavily on static rules that require constant tuning. As environments change, those rules either break or flood the SOC with noise.
NetWitness enriches log data with context and threat intelligence at ingestion. That means detections are built on behavior and relationships, not isolated events.
During migration:
- Retain only legacy rules that consistently produce high-quality alerts
- Replace brittle correlations with metadata-driven detection
- Validate detections against real investigation workflows
This approach reduces alert volume while improving detection accuracy, a pattern consistently reported by NetWitness customers.
Step 5: Simplify Compliance and Reporting
Compliance is often the quiet driver behind SIEM migrations.
NetWitness includes prebuilt reporting templates aligned to frameworks such as SOX, PCI, HIPAA, and NERC. Logs can be stored locally to meet regional or regulatory requirements while still being viewed centrally for unified visibility.
For many organizations, this shifts compliance from a manual monthly process to a continuous, automated workflow.
Step 6: Integrate NetWitness into Your Existing Security Stack
A SIEM platform should act as the investigation hub, not an isolated system.
NetWitness supports SIEM integration with:
- SOAR platforms for automated response
- Threat intelligence feeds for enrichment
- Ticketing and case management systems
- Identity and access platforms
This allows organizations to preserve existing investments while improving detection and response workflows.
Step 7: Validate in Parallel and Decommission Legacy SIEM Tools
NetWitness supports modular SIEM deployment, making parallel operation straightforward.
During validation, compare:
- Alert quality and false positive rates
- Investigation time and analyst effort
- Visibility across cloud, SaaS, and on-prem environments
- Compliance reporting effort
Once NetWitness consistently meets operational and compliance requirements, legacy SIEM tools can be safely retired.
The Role of Automation in SIEM Migration
Automation is not just a post-migration benefit. It plays a critical role during migration itself.
NetWitness automation supports:
- Faster log source onboarding
- Automated enrichment and context building
- Guided investigation workflows
This reduces dependence on specialized SIEM engineers and helps teams scale without increasing headcount.
Final Takeaway
Migrating from legacy SIEM tools is not about chasing new features. It is about restoring trust in your security data.
NetWitness delivers centralized log management, faster detection, simplified compliance, and flexible deployment across modern enterprise environments. When migration is approached incrementally and use-case driven, organizations see immediate improvements in visibility, analyst efficiency, and security outcomes.
Frequently Asked Questions
1. Why should organizations migrate from legacy SIEM tools?
Legacy SIEM tools cannot scale with modern threats or environments. They create alert noise, slow investigations, and limited visibility across cloud and siem network activity. Modern siem solutions improve detection accuracy and response speed on a single SIEM platform.
2. How does NetWitness simplify SIEM migration?
NetWitness supports phased siem implementation, letting teams run legacy and new detections in parallel. Its unified approach reduces complexity and replaces multiple siem security tools with one platform.
3. How does NetWitness support cloud and hybrid environments?
NetWitness enables siem integration across on-prem, cloud, and hybrid environments. Security teams get consistent visibility and detection without managing separate security information and event management SIEM tools.
4. What role does automation play in SIEM migration?
Automation reduces manual rule management, speeds investigations, and helps modern SIEM platform deployments scale. It ensures siem cyber security teams maintain coverage during migration.
5. What are the biggest challenges in legacy SIEM migration?
Common challenges include data normalization, rule migration, and maintaining visibility across siem network and cloud sources. A phased approach helps minimize risk and disruption.
Choose the Right SIEM with Confidence
Evaluate vendors using a comprehensive, expert-built checklist.
Identify must-have SIEM features for complete visibility and faster detection.
Compare capabilities to ensure scalability, automation, and integration.
Make informed decisions with NetWitness’ proven SIEM guidance.