What is Spear Phishing?
Regular phishing involves sending a million emails, using generic bait such as a fake bank alert, a shipping notification, and hoping that a small percentage of recipients click without thinking. The attackers don’t know or care who you are.
Spear phishing inverts that completely. The attacker knows exactly who they’re targeting. They know your job title, who you report to, which vendors your company uses, and what projects are currently in progress. The email they send doesn’t feel like spam; it feels like something a colleague or a trusted partner might actually send you.
When it works, the consequences go well beyond a stolen password. Attackers can install malware, move through an organization’s systems for weeks undetected, trigger fraudulent wire transfers through what’s called business email compromise, or quietly exfiltrate sensitive data while IT has no idea anything is wrong.
Companies are spending more on cybersecurity than ever before, and attackers are still walking right through the front door with just a well-crafted email.
According to the 2025 Verizon Data Breach Investigations Report, phishing shows up in 36% of confirmed breaches, and human involvement plays a role in 68% of incidents. With all the investment in security tools, awareness training, and email filters, the numbers are striking.
Spear phishing is causing the most damage with its targeted, researched, and personalized approach. It’s worth understanding why it keeps working, because the “employee training” doesn’t actually hold up under scrutiny.
Why Spear Phishing Works in 2026
The easy answer is “people click things they shouldn’t.” That answer is both true and useless. The more honest answer is that several things have converged to make spear phishing attacks dramatically harder to catch, and it has less to do with employee carelessness than with structural gaps in how security teams operate.
Old Patterns Are Gone: For years, awareness training pointed people toward obvious red flags: broken English, weird formatting, a sense of manufactured urgency, and requests that seem slightly off. Those cues don’t apply to modern spear phishing. AI-generated content has made it effortless to produce emails that read as if they came from a native speaker who knows your industry. What used to take hours of careful crafting now takes seconds and costs nothing.
OSINT is Easy: Attackers don’t need sophisticated tools to research a target. LinkedIn alone surfaces job titles, reporting structures, team names, and vendor relationships. People casually mention ongoing projects in posts without thinking twice. Company websites and press releases fill in the rest, partnerships, executive names, growth announcements. The research that once took days of careful manual work can now be done in under an hour, often with some level of automation. By the time a spear phishing email reaches you, the person who sent it has context about your role and your organization that most of your own coworkers don’t have.
Identity is Now the Attack Surface: The shift to cloud-first operations and remote work has fundamentally changed what a “secured perimeter” means. Once an attacker has a valid set of credentials and an active session, they look indistinguishable from a legitimate user. There’s no malware to detect, no unusual process running, no anomalous network traffic in the traditional sense.
MFA is No Longer Enough on Its Own: Multi-factor authentication was the right move, and it raised the bar significantly. But adversary-in-the-middle phishing kits have evolved to work around it. These tools proxy the real login page in real time: you enter your credentials, complete the MFA challenge, and the attacker’s kit captures your authenticated session token before you even land on the real page. You logged in successfully. So did they. Standard TOTP codes and push notifications don’t protect against this.
The Security Stack is Fragmented: This is probably the most underappreciated root cause. Most organizations have an email gateway, an endpoint detection tool, a SIEM tool or log aggregator, and some form of identity monitoring. Each of these tools sees a slice of what’s happening. None of them sees the full picture. And in most security operations centers, no one is looking at all that data together in real time. The attack chain might look completely benign in each tool, but only when you stitch those events together across a timeline that the pattern becomes obvious. And by the time anyone does that, the damage is usually already done.
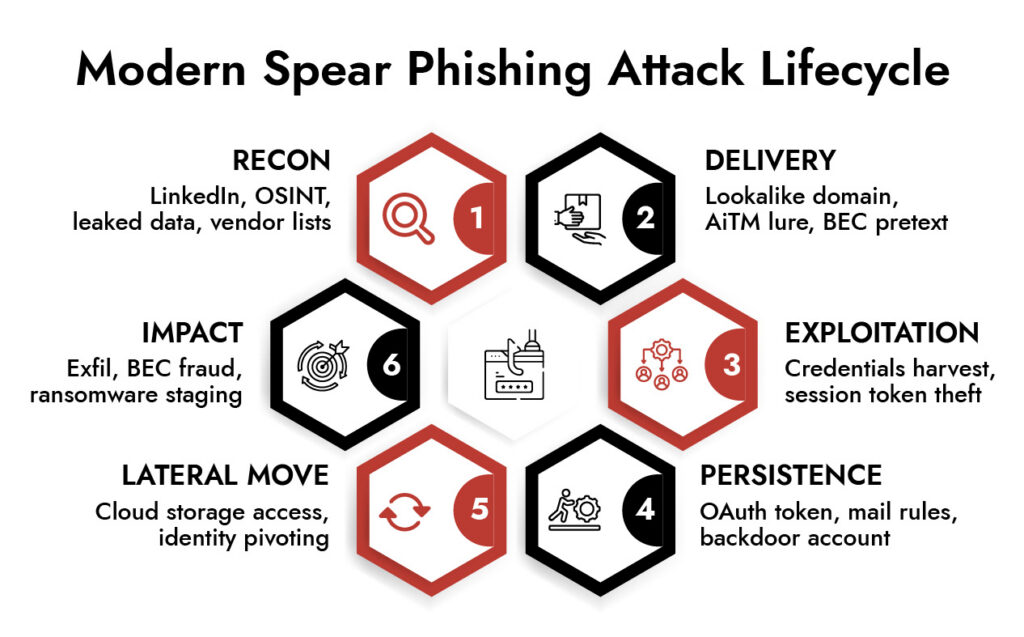
What Actually Happens During an Attack
It helps to walk through how a real spear phishing campaign unfolds, because most people’s mental model stops at “someone clicked a bad link.”
It starts well before any email is sent. The attacker builds a target profile, who handles financial approvals, who has access to sensitive systems, and who’s likely to act quickly without second-guessing a request. Senior finance and HR staff are prime targets not because they’re less security-conscious, but because they have the authority to move money, approve access changes, or take actions with significant consequences.
The delivery itself is where most organizations believe their controls are strongest, and where attackers have adapted most aggressively. Advanced phishing emails often arrive through legitimate cloud platforms; the link points to a SharePoint folder or a Google Drive document, not some sketchy domain the email filter would catch. Some campaigns use QR code instead of links, bypassing URL scanning entirely by shifting the “click” to the user’s phone, where enterprise security tools often have less visibility. Because spear phishing volumes are tiny, they never trigger the volume-based heuristics that catch bulk campaigns.
Once someone engages and credentials are captured, the attacker’s next priority is staying in. This is done quietly, using features the platform was designed to have. An inbox rule that automatically moves security notifications to a folder you never check. A secondary recovery email is registered on the account. An OAuth application granted access that survives even a password reset. None of this looks alarming in isolation. All of it ensures that even if the initial compromise is detected, the attacker isn’t actually locked out.
Then comes the slow phase, lateral movement that can stretch across days or weeks. The attacker reads email threads to understand relationships, approval workflows, and what requests would seem normal coming from this account. They look for shared drives, financial systems, and HR platforms. They identify service accounts or shared mailboxes with broad access. The whole time, they’re operating below the threshold that would trigger any individual alert.
Where Current Defenses Fall Short
Email detection tools are tuned for bulk campaigns with known-bad signatures. A low-volume, highly customized attack using a link to a legitimate cloud service doesn’t match any pattern in the rulebook. It gets delivered.
Identity monitoring typically flags anomalies based on IP addresses and geographic location. An attacker using a captured session token from a location that looks normal or using a residential proxy to appear local looks like a legitimate user. Nothing fires.
Alert correlation is where the real failure lives. Email events, identity events, endpoint activity, and cloud access logs all sit in separate tools. No one has a view that connects “this user clicked a link in an email three days ago, authenticated from an unusual device, accessed the finance folder for the first time, and initiated outbound data transfer” as a single coherent narrative. An analyst who has to manually open four different consoles and build that timeline themselves is unlikely to catch it fast enough to matter.
The mean time to detect an email-originated intrusion is still over eleven days. In that window, an attacker can accomplish almost anything they came to do.
What Defense Actually Looks Like When it Works
The answer isn’t adding more point solutions to an already crowded stack. It’s changing the approach to visibility and detection.
The organizations that catch spear phishing attacks before they turn into incidents share a few things in common. They can look at email, endpoint, identity, and cloud activity from a single analytical plane — not as separate streams managed by separate teams in separate tools. They’ve moved from signature-based detection toward behavioral baselines, which means they’re not asking “does this match a known-bad pattern” but “is this person doing something they’ve never done before?” And when a potential incident is flagged, investigation takes minutes rather than days, because analysts aren’t starting from scratch manually correlating events.
There’s also an authentication piece that can’t be skipped. Deploying phishing-resistant authentication, FIDO2 passkeys rather than TOTP codes or push notifications, closes the adversary-in-the-middle gap that standard MFA leaves open. This is one of the highest-leverage technical controls available right now for organizations that haven’t made the switch.
None of this eliminates spear phishing as a threat. Attacks targeting human judgment will always have a chance of succeeding because human judgment is imperfect, and that’s not a solvable problem. But the gap between “we have all the telemetry we need to catch this” and “we actually caught it before it caused damage” is an engineering and process problem, and those are solvable. Most organizations have the data. What they’re missing is the ability to connect it fast enough to act.
Break down silos and accelerate investigations by connecting SIEM, NDR, and EDR into a single, intelligent workflow.
- Unified visibility across logs, endpoints, and network traffic
- Correlated insights to uncover multi-stage attacks faster
- Reduced alert fatigue with prioritized, high-fidelity alerts
- Seamless analyst workflows from detection to response
Frequently Asked Questions
1. How is spear phishing different from regular phishing?
Regular phishing is high volume and low customization — millions of identical emails cast as wide a net as possible. Spear phishing is the opposite: low volume, individually crafted, targeting specific people at specific organizations. That’s what makes it so much harder to catch. There’s no pattern to recognize, no volume threshold to trip, and the email feels personally relevant rather than generically suspicious.
2. Does MFA help with spear phishing?
MFA significantly raised the bar and is still worth deploying. The problem is that adversary-in-the-middle phishing kits have evolved specifically to work around it. They proxy the real login page in real time, intercept your authenticated session after you complete MFA, and let the attacker continue the session without your credentials. FIDO2 passkeys are the authentication standard that actually closes this hole — but widespread deployment is still limited.
3. How do attackers gather information for spear phishing?
Primarily: who has the authority to take high-impact actions quickly? Finance staff who can initiate transfers, HR staff who can update banking details for payroll, executives whose identity can be used to pressure others. The research phase uses publicly available information — LinkedIn, company websites, press releases, conference speaker listings, and data from prior breaches available on dark web markets — to build a profile that makes the eventual email feel completely plausible.
4. What are the risks of spear phishing for enterprises?
A successful spear phishing attack is often just the entry point for something larger. Once attackers have established access, they can deploy ransomware, conduct slow and quiet data exfiltration, use the compromised account to attack your vendors or customers, trigger fraudulent payments, or create regulatory exposure if sensitive data is involved. The initial phishing email might cost you almost nothing to ignore in the moment. What comes after it is where the real damage accumulates.