What are the most impactful network detection and response use cases in enterprise security?
Network detection and response proves its value when attackers start behaving like insiders. Not loud. Not obvious. Just moving quietly across your environment.
These are the use cases that actually matter:
- Detecting Lateral Movement and Internal Reconnaissance: After initial access, attackers scan, test permissions, and pivot. Watching internal network traffic is often the only reliable way to catch that movement early.
- Visibility Into Encrypted Traffic Without Breaking It: Most traffic is encrypted now. Strong NDR security solutions don’t need to decrypt everything. They analyze behavior, patterns, and session metadata to spot what doesn’t belong.
- Monitoring Cloud, Hybrid, and Containerized Environments: Infrastructure changes constantly, especially in cloud deployments. Network detection and response solutions provide consistent visibility across on-prem and cloud without relying only on logs.
- Improving Incident Response Through High-Fidelity Forensics: When something goes wrong, assumptions slow you down. The best NDR solutions preserve session data so teams can reconstruct events instead of guessing.
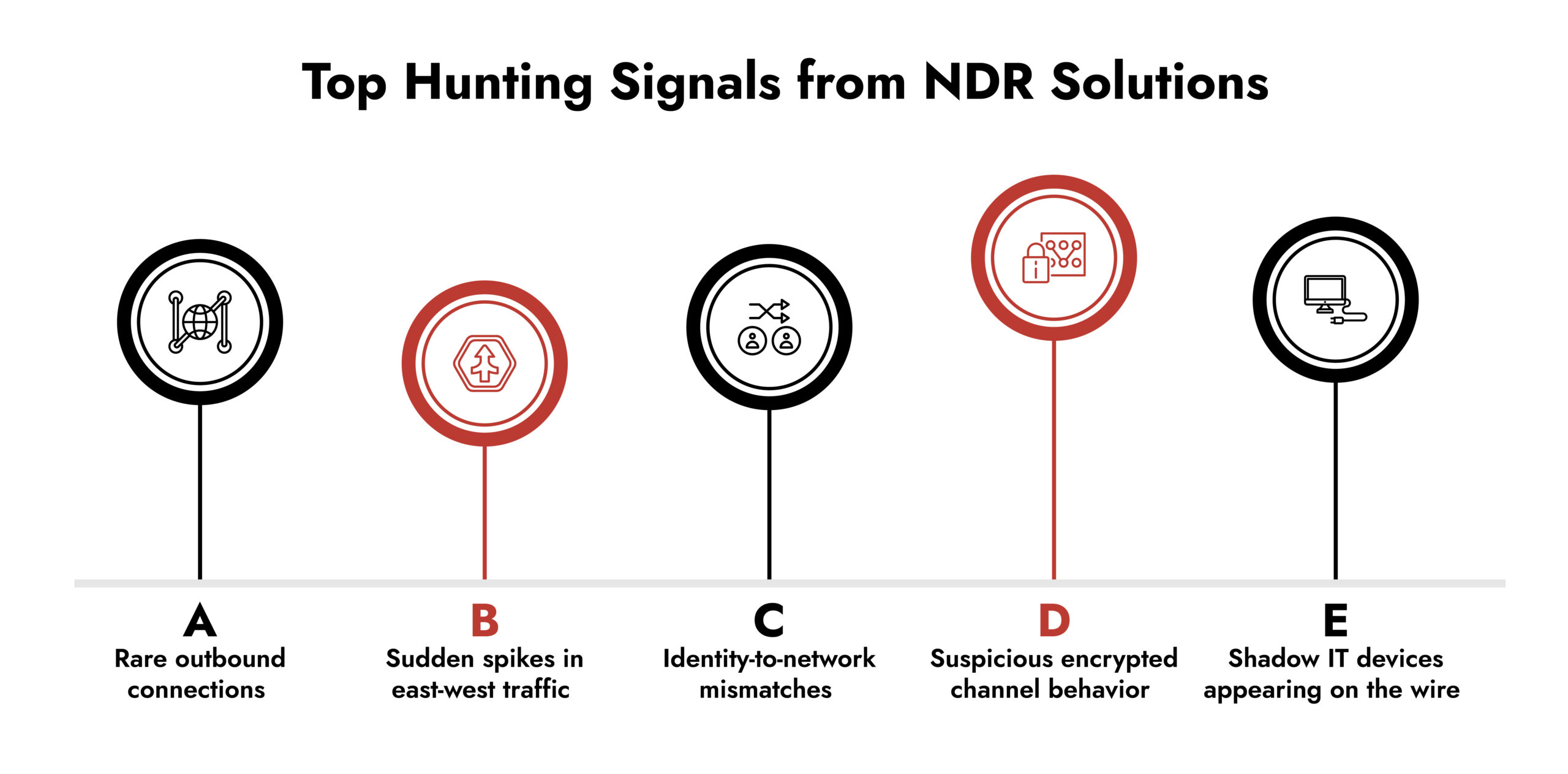
- Proactive Threat Hunting and Early Detection: Threat hunters need evidence, not noise. The best NDR for security operations teams delivers historical context and real communication paths to validate suspicious activity.
That’s where modern network detection and response use cases shift from theory to operational advantage.
Introduction: Why Network Detection and Response Solutions Matter Now
Recently, most of today’s attacks do not use “signature” attacks. Rather, they enter into your network by exploiting exposed services, hiding in encrypted communications, and moving data in and out of the network while acting as valid traffic. Therefore, the use of NDR solutions is critical for network-based cybersecurity.
NDR solutions operate by monitoring actual communication between network devices, user identities, applications, and workloads on the network and detecting zero-day exploits, living-off-the-land activity, and fileless malware that do not use traditional AV tools and traditional logging mechanisms.
The term “Network Detection and Response” (NDR) was coined in 2020, with the functionality of these tools evolving from solely providing traffic statistics (Network Traffic Analysis or NTA) to also providing the ability to proactively detect, investigate and respond to suspicious events using evidence from the network due to the increasing sophistication of cyber threats, including Advanced Persistent Threats (APTs).
As network traffic is composed of more than 80% of network traffic is composed of encrypted data, NDR capable solutions analyze encrypted traffic by employing network telemetry data, including metadata, session information and protocols, rather than relying on decryption to establish a sense of safety, speed and compliance.
NDR capable tools utilize observed traffic data to establish a baseline of normal behavior for a given network to subsequently identify anomalous behaviors such as outbound connections to suspicious destinations, inbound sessions from unexpected sources and the unauthorized movement of data.
By 2030, the global NDR marketplace is projected to be valued at USD 5.82 billion, expanding from an estimated USD 3.68 billion in 2025, thereby providing NDR vendors with an elevated level of competition for providing enterprise organizations with advanced visibility into their multi-network environment.
Best-in-class NDR tools collect a substantial number of raw packets and packet session data to assist security teams in gaining greater visibility into network behavior, identifying the movement of sensitive data, and validating incident response through verifiable evidence and not just through speculation.
Integrating with Security Information and Event Management (SIEM), Endpoint Detect and Response (EDR) and Security Orchestration Automation and Reporting (SOAR) solutions enables security teams to enhance their overall security posture by linking detection data with what actually occurred on the network and facilitating response measures through previously established workflows.
What is a Network Detection and Response Solution in Cybersecurity?
A Network Detection and Response (NDR) solution is a cybersecurity tool that continuously monitors network traffic for malicious activity, anomalous activity or policy violations.
Unlike traditional signature based systems, network detection response solutions use network evidence, protocol analysis and behaviour/context coupled with analytics and threat intelligence, and other detecting suspicious patterns like command and control activity, data exfiltration, unauthorised inbound access, insider threats, lateral movement.
Rather than mainly relying on machine learning models as traditional systems generally do; modern NDR security solutions concentrate on session-based visibility, reconstruction of artifacts and packet-based inspection to uncover attacker behaviour blended in normal traffic.
A vast number of cloud-native NDR platforms today utilize sensors to passively collect and analyze full-fidelity network traffic (multiprate, multicomplexes, multilayered) across all ports and protocols in physical, virtual and cloud-proven physical infrastructures without causing disruption to operational efficiencies.
Emerging as recently as the early 2010s, NDR is one of the three components of the SOC visibility triad (along with endpoint detection response, or EDR, and security information event management or SIEM) designed to provide authoritative network evidence supporting endpoint and log-based telemetry findings through the triad’s use of a common evidence approach (network).
Key Capabilities of the Best NDR Solutions
Key features and benefits of leading network detection and response solutions include:
- Real-time visibility into ingress and egress network traffic and threats
- Evidence-driven response capabilities to support blocking, isolation, or containment workflows
- Continuous monitoring across users, devices, and network technologies from data center to hybrid and cloud-supported environments
- Integration with SOAR to operationalize detections
- Evolution from basic traffic analysis to investigation-grade detection and response
- Support for security leadership by reducing investigation time and uncertainty
These capabilities define what differentiates top NDR solutions 2026 from legacy monitoring tools.
The 5 Most Impactful Use Cases of NDR Solution for 2026
Use Case 1: Detecting Lateral Movement and Internal Reconnaissance
Attackers rarely stay still. Once they gain access, they scan, pivot, and escalate. Network detection and response solutions expose this activity by observing peer-to-peer communications and protocol usage at the network level.
Lateral movement is hard to detect. Many tools were not made to analyze east-west network traffic with full session visibility. Network behavior analysis allows security teams to baseline normal communication and immediately spot deviations such as unauthorized SMB sessions, Kerberos spraying, or unusual database queries.
Why this matters:
- Reconnaissance activity is clearly visible in session metadata
- Privilege misuse becomes obvious when correlated with actual network access paths
- MITRE ATT&CK techniques are easier to validate when network evidence is preserved
This remains one of the most critical network detection and response use cases for enterprises.
Use Case 2: Visibility Into Encrypted Traffic Without Breaking It
Encrypted traffic dominates enterprise networks. Modern NDR security solutions analyze this traffic using session characteristics and behavioral indicators, not payload decryption.
Instead of decrypting TLS 1.3 or SaaS traffic, advanced best NDR solutions rely on JA3/JA4 fingerprints, certificate attributes, flow timing, packet sizes, and protocol compliance.
Why this matters:
- Malware families can be identified through network fingerprints
- Suspicious activity stands out via rare destinations and abnormal session behavior
- Data exfiltration attempts can be detected even when disguised as HTTPS
Encrypted visibility is a defining requirement when evaluating NDR vendors.
Use Case 3: Monitoring Cloud, Hybrid, and Containerized Environments
Cloud environments are dynamic, but behavior still leaves traces.
Modern cloud native NDR platforms provide consistent visibility across on-prem, hybrid, and cloud-supported deployments by analyzing real network traffic rather than relying solely on flow logs.
Why this matters:
- Visibility unifies AWS, Azure, GCP, and data center environments
- Suspicious service-to-service communication becomes detectable
- Identity-based controls can be verified through observed behavior
This is why cloud visibility defines the best NDR for security operations teams managing distributed infrastructure.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.
Use Case 4: Improving Incident Response Through High-Fidelity Forensics
Incident response requires evidence.
Leading network detection and response solutions preserve packet-level and session-level data so responders can reconstruct events accurately.
During an incident, teams must answer:
- How did the attacker get in?
- Where did movement occur?
- What data was accessed?
- Is activity still present?
Why this matters:
- Entire attack chains can be rebuilt
- Containment can be validated by confirming traffic cessation
- Investigation timelines become fact-based
This capability separates standard monitoring tools from best NDR solutions.
Use Case 5: Proactive Threat Hunting and Early Detection
Threat hunting depends on observing attacker behavior. Communication. Scanning. Data movement.
Network detection and response provides investigators with historical session evidence and behavioral context to test hypotheses using real data.
Why this matters:
- Stealthy threats surface earlier
- False positives decline when validated with evidence
- Investigations rely on observable behavior, not probability
Proactive detection remains one of the most strategic network detection and response use cases heading into 2026.
Where NetWitness Fits In
NetWitness strengthens these use cases by delivering full packet capture, session reconstruction, and port-agnostic visibility across hybrid and cloud-supported environments.
Its platform aligns with the evolving expectations for top NDR solutions 2026, combining behavioral context, threat intelligence, and investigation-grade network evidence across network, endpoint, logs, identity, and cloud sources.
By integrating SIEM, SOAR, and UEBA, it supports best NDR for security operations teams that require verifiable evidence rather than alert volume.
Conclusion: Why Network Detection and Response is Core to Modern Security
Strong network detection and response solutions give security teams clarity rooted in evidence. They expose attacker entry points, reveal data movement, simplify encrypted analysis, and support decisive response.
As threats evolve, attackers still depend on communication. And communication always leaves traces in network traffic.
Organizations evaluating best NDR solutions should prioritize visibility depth, encrypted traffic analytics, cloud-native coverage, and investigation-grade evidence. That is what defines the top NDR solutions 2026 and differentiates serious NDR vendors from surface-level tools.
Frequently Asked Questions
1. What are the top use cases of NDR solutions?
They focus on detecting north-south threats such as command-and-control traffic, data exfiltration, and zero-day exploitation, along with lateral movement, encrypted traffic analysis, cloud and hybrid monitoring, improved incident response, and proactive threat hunting.
2. Which industries benefit most from the top 5 NDR solution use cases?
Industries with distributed environments – finance, healthcare, telecom, government, and manufacturing – benefit the most. They rely on strong visibility, network threat detection, and behavioral analytics to manage high-risk traffic.
3. What security challenges do the top 5 NDR use cases address?
They address blind spots in north-south traffic, including command-and-control communications, data exfiltration, exploitation of public-facing services, and webshell activity, along with encrypted traffic visibility, internal reconnaissance, cloud sprawl, hybrid-network complexity, and slow incident validation. NDR in cybersecurity provides the real-time network visibility needed to detect and investigate these threats.
4. Can NDR monitor encrypted network traffic?
Yes. Modern NDR solutions analyze encrypted traffic using metadata, fingerprints, and behavioral indicators rather than decryption. This approach maintains privacy while still detecting threats hidden in TLS channels.
5. Which companies offer trial versions to test the top 5 NDR use cases?
Many providers offer evaluation programs, including on-prem and cloud-based testing environments. Enterprises typically run proof-of-value engagements to validate real network detection and response performance.
6. Which NDR solutions provide automated response features for the top 5 use cases?
Some tools integrate with SOAR platforms to automate isolation, blocking, and enrichment steps. The value comes from connecting network detection and response solutions to broader response playbooks.
7. Where can I find detailed case studies on the top 5 use cases of NDR tools?
Case studies are available from trusted cybersecurity research groups, government advisories, and independent analysts like Gartner and NIST, offering evidence-backed insight into network threat detection use cases.
8. Which managed security service providers support the top 5 NDR use cases?
Most MSSPs now incorporate NDR in their service stack to monitor hybrid environments, detect lateral movement, and support forensic investigations. These services often enhance existing cybersecurity network security programs.