Key Takeaways:
- Healthcare is a top cyber target because medical records are highly valuable
- Legacy systems and connected medical devices expand the attack surface, yet often cannot be easily patched or replaced.
- Downtime in healthcare patient safety, which is why ransomware is especially dangerous for hospitals.
- Human factors remain a major risk, with insider errors and phishing contributing to a large share of breaches.
- Compliance does not equal security as meeting HIPAA requirements alone won’t stop modern attacks.
- Behavior-based detection and continuous visibility are critical for identifying threats early in complex healthcare environments.
- Strong fundamentals matter: MFA, encryption, segmented networks, and tested backups significantly reduce risk.
- Healthcare organizations benefit from specialized cybersecurity partners like NetWitness, who understand clinical workflows and regulatory pressures.
In 2023, 725 healthcare data breaches were reported to HHS, exposing over 133 million patient records (IBM Security, 2023). The average cost was $10.93 million per breach, which is the highest of any industry for thirteen straight years (Ponemon Institute/IBM, 2023).
The healthcare industry is growing at an extraordinary rate, but most organizations are still struggling with legacy systems and nonexistent cybersecurity measures. Others are grappling with solutions that are incompatible with their unique requirements.
NetWitness has over 2 decades of experience working with the healthcare industry and understands its challenges. While working with the industry closely, NetWitness has seen what an effective solution cybersecurity in healthcare must look like in healthcare.
In this blog, we leverage industry experience to answer questions like how cybersecurity is different in healthcare, what type of data makes it a prime target, what type of attacks the industry is vulnerable to, what the best practices are to improve cybersecurity, and how NetWitness can help you.
What Types of Data Make Healthcare a Prime Target for Cyberattacks?
According to the Trustwave Global Security Report, a single medical record sells for around $250 on the dark web, whereas a stolen credit card sells for about $5.40.
An electronic health record is a treasure trove of data, as it includes your full name, social security number, address, birth date, insurance information, credit card information, complete medical history, prescriptions, diagnoses, and genetic information. And, if you have tests done through your employer, then the related details are also exposed.
Then there’s the Internet of Medical Things. It is projected that the IoMT market will hit $187 billion by 2028 (Fortune Business Insights, 2023), which is impressive, but is also a colossal security risk.
Source: Veriti
Why Is Cybersecurity in Healthcare Different from Other Industries?
The healthcare industry works differently but they often end up with enterprise security platforms designed for tech companies or banks. Moreover, overheads such as upgrades, maintenance, and training are often not accounted for.
The challenges that cybersecurity solutions need to address for the healthcare industry are:
1. The Uptime Problem
Emergency departments run 24/7, and one of the biggest security challenges is their inability to take the systems offline. Therefore, if there is any software update or patch, scheduling a maintenance window for the healthcare organization is challenging.
2. Legacy Systems
In 2020, Palo Alto Networks surveyed more than 1.2 million medical devices, of which 83% were running on outdated platforms.
Medical devices are typically expected to operate for at least 20 to 30 years owing to the high costs. During this period, often the software support expires or is made redundant. Therefore, there is no simple upgrade option for them.
Replacing it also may not be economically viable, or sometimes, there is a huge waiting list for the device. During this period, the devices and the healthcare institutions are exposed to cyberattacks.
3. Regulatory Complexity
The healthcare industry is constantly under pressure from regulatory bodies like HIPAA.
The Office for Civil Rights can fine up to $1.5 million per violation category annually (HHS.gov, 2023). For willful neglect, it’s $50,000 per record exposed.
Data breaches incur regulatory action, such as fines or business disruptions as well as reputational damage.
4. Poor Training
According to Verizon’s 2023 Data Breach Investigations Report, 58% of healthcare breaches involve insiders or business partners.
A big reason for such a huge number is the lack of training and awareness. The attackers also leverage the fact that the nurses and doctors are stressed and tend to respond quickly to urgent-sounding messages.
What Are the Most Common Cyber Threats in Healthcare?
The attacks on healthcare institutions are on the rise, and to curb them, one must first understand what these attacks are.
Ransomware and Malware:
According to Sophos’s State of Ransomware in Health 2024, the 67% of healthcare institutions were attacked in 2024, a 60% increase from 2023.
Ransomware and malware have the potential to shut down the entire hospital by attacking and encrypting the data. Modern ransomware groups also increase the stakes by stealing the data before encrypting the files.
Phishing
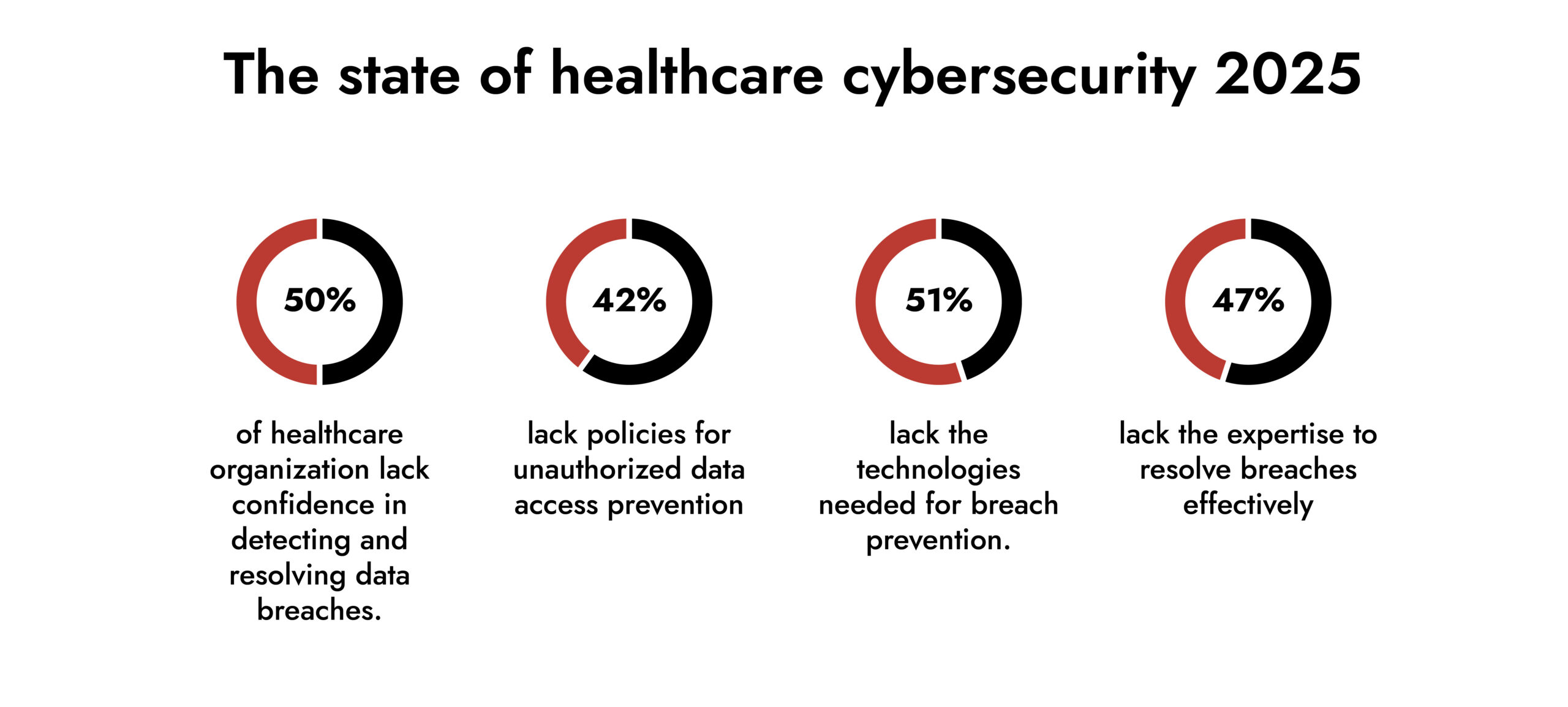
According to a survey by the HIMSS Healthcare Cybersecurity Survey in 2024, 63% of the surveyors reported general email phishing incidents, 34% SMS phishing, 34% spear phishing and more.
Source: 2024 HIMSS Healthcare Cybersecurity Survey
Insider Threats
35% percent of healthcare breaches involve insiders (Verizon DBIR, 2023). This number is a huge indicator for healthcare institutions to strengthen cybersecurity in healthcare not only to prevent external actors but also insider threats.
Three categories of insider threats:
- Malicious insiders who steal data to sell it
- Negligent employees who snoop on patients, family members, neighbors, or ex-spouses. It also includes people who accidentally email PHI to the wrong person or lose unencrypted laptops.
- Compromised credentials where attackers are using legitimate employee logins.
Medical Device Vulnerabilities
Connecting medical equipment such as IV infusion pumps, imaging devices, and patient monitors has helped the industry enhance clinical efficiency. However, it is a cybersecurity risk, thanks to outdated software or poor encryption. Such vulnerabilities, when breached, are a threat to patient safety as the attacker can manipulate the devices as well.
Why Is Ransomware Especially Dangerous in Healthcare?
In 2021, Springhill Medical Center in Alabama got hit with ransomware. Their fetal monitoring systems went down. Teiranni Kidd, who delivered an unresponsive child, has pressed charges claiming that if the monitors had been working, staff would have detected fetal distress and performed an emergency C-section.
Ransomware in healthcare doesn’t just shut down email or lock up file shares; it stops patient care. Hospitals need constant access to electronic health records, diagnostic imaging, lab systems, and connected medical devices. When those get encrypted, doctors can’t pull up patient histories. Labs can’t deliver results. The ER can’t see what medications someone is allergic to. Attackers bet on the fact that when patient safety is on the line, hospitals will pay.
The tech environment makes it worse. Because the healthcare organizations have legacy systems running software that hasn’t been patched in years, because it’s certified for medical use and updates would break compliance. Medical devices on the network that cannot be updated without voiding warranties. Networks designed for clinical workflows, not for containing threats.
When ransomware hits, it spreads through all of it and locks down the exact systems clinicians need to do their jobs. The damage doesn’t stop at IT. Patients get diverted to other hospitals. Surgeries get canceled. Staff revert to paper charts. HHS launches investigations. Lawsuits pile up. The media runs stories. And the trust patients had in your organization? That takes years to get back.
Unmask GenAI Threats — Get Ahead of the Curve

What Are Best Practices for Improving Cybersecurity in Healthcare?
To address the unique challenges that the healthcare industry faces, they need a risk-driven, integrated security approach:
1. Strengthen Visibility Across the Environment
Continuous visibility across networks, endpoints, cloud workloads, and medical devices is critical for early threat detection. Hospitals operate in a complex network of clinical systems, legacy infrastructure, third-party applications, and medical devices.
Monitoring activities across this distributed attack surface helps security teams to identify suspicious behavior, such as lateral movement or unusual data access.
Improved visibility also enables faster investigation and response, helping healthcare organizations contain incidents while continuing clinical operations.
2. Stop Relying on Traditional Signature-based Detection
Traditional antivirus is no longer enough, but healthcare keeps subscribing to it because it checks a compliance box.
Here’s the problem: by the time a ransomware signature exists, thousands of organizations have already been hit. The signature-based approach is inherently reactive. If the attackers modify their malware even slightly, your endpoint protection fails to recognize it.
What healthcare needs is behavioral detection systems that look for weird patterns rather than known malware signatures.
Look for:
- AI and machine learning that understand healthcare workflows
- Threat intelligence that is specific to healthcare
- Automated response that can isolate threats without waiting for someone to click a button
- Full packet capture for when you need to figure out what the hell happened
3. Multi-Factor Authentication
MFA blocks 99.9% of automated attacks according to Microsoft.
Modern MFA doesn’t have to be painful. Biometric authentication, mobile push notifications, and hardware tokens for high-privilege accounts. There are also single sign-on solutions that eliminate password fatigue. Find something that works for your workflow, but implement it.
4. Robust Encryption
Encryption transforms patient data into an unreadable format that can be accessed only with a decryption key.
Healthcare providers should encrypt data stored on servers or devices, as well as when transmitted over networks.
The challenge is implementation across complex healthcare environments with legacy systems that may not support modern encryption standards. It is advisable to start with the most sensitive data first, and then work your way through the rest of the environment.
5. Schedule Regular Backups
Set up the 3-2-1 backup rule: three copies of data, two different media types, one off-site. But add a fourth, one copy that’s immutable. Use a write-once-read-many storages mode that ransomware cannot encrypt.
To maintain the backups:
- Test your backups quarterly.
- Test restoring data from them.
- Time how long it takes to restore data
This will keep you aware of how much time your data will be restored in the event of an attack. The backups should also be protected with strong authentication. Attackers specifically target backup systems now because they know that’s your recovery path.
6. Secure Connected Medical Devices
Connected medical devices are everywhere in modern healthcare. They improve patient care, but they also expand your attack surface dramatically.
Many of these devices run outdated operating systems that can’t be patched without breaking FDA compliance or voiding warranties. Some still use default credentials that can’t be changed. Others have no security features at all because they were designed for isolated networks.
What you can do:
- Implement access controls requiring credentials before device use
- Network segmentation to isolate medical devices from other systems
- Regular firmware updates when possible (work with vendors on this)
- Monitoring unusual device behavior or network traffic
- Inventory of all connected devices with risk assessments
7. Ongoing Training
Generic security awareness training doesn’t work. Make training relevant to actual jobs. Show the radiology tech what a phishing email targeting their department looks like. Show the billing clerk how invoice fraud specifically works in healthcare.
What actually works:
- Monthly simulated phishing with realistic healthcare scenarios with fake IT password resets, vendor invoices, patient referrals, and appointment confirmations
- Role-specific training because billing staff face different threats than ER doctors
- Easy reporting mechanisms so staff can flag suspicious emails without feeling stupid
- No blame culture as people won’t report incidents if they’re afraid of getting in trouble
8. Conduct Regular Security Audits
Regular security audits help identify vulnerabilities before attackers exploit them. A good healthcare security audit includes both IT systems and connected medical devices.
What to audit:
- Software vulnerabilities and patch status
- Access controls and user permissions
- Network segmentation effectiveness
- Connected device security posture
- Physical security of data centers and equipment
- Third-party vendor access and security practices
The threat landscape is dynamic; regular audits are a must to protect your systems.
9. Fortify Against External and Internal Threats
Most security programs focus heavily on external threats, viz., ransomware, phishing, and network intrusions. But insider threats are just as dangerous and often harder to detect.
A big risk is careless or compromised insiders. Staff clicking phishing links, using weak passwords, or falling victim to social engineering are very common in healthcare environments.
Protection strategies:
- Only access PHI through secure connections
- Lock computers when not in use
- Regular monitoring of unusual data access patterns
- Principle of least privilege – people only have access to what they need for their jobs
10. Work With Cybersecurity Experts
Cybersecurity is complex, and healthcare has unique requirements that make it even more complicated. Most healthcare organizations don’t have the internal expertise to handle this alone.
The right partner brings:
- Experience with HIPAA and other healthcare regulations
- Understanding of connected medical device challenges
- 24/7 monitoring and threat detection
- Incident response capabilities
- Regular security assessments and vulnerability testing
11. Stay Compliant with Regulations
HIPAA sets baseline standards for protecting patient privacy and PHI security. The regulations tell you what minimum protection you must have.
Key regulations to understand:
- HIPAA Privacy and Security Rules
- HITECH Act breach notification requirements
- State-specific privacy laws (especially if you operate in multiple states)
- FDA guidance for medical device security
- Industry-specific frameworks like HITRUST
12. Building a Culture of Security Awareness
All of these technical controls and security practices mean nothing if your organization doesn’t have a culture that values security.
This starts at the top. Leadership must demonstrate that security is a priority through actions.
But it also means every employee understands their role in protecting patient data. From the CEO to the environmental services staff, everyone needs to recognize that security is everyone’s responsibility.
Regular communication about security topics. Recognition for employees who identify threats or follow security best practices. Open discussion when incidents occur without fear of blame. Making security part of “how we do things here” rather than an afterthought or checkbox.
Why NetWitness?
NetWitness stands out because it is built for the realities of cybersecurity in healthcare. Unlike traditional tools that rely on endpoint agents, NetWitness provides passive, network-level visibility, enabling continuous monitoring of legacy systems, medical devices, and critical infrastructure without disrupting patient care.
Its strength lies in context-aware detection. NetWitness understands clinical workflows, reducing false positives by distinguishing normal clinical access from suspicious behavior. This allows security teams to focus on real threats, including ransomware, insider activity, and zero-day attacks—often detected before damage occurs.
NetWitness also simplifies regulatory compliance with forensic-grade, tamper-proof logging and prebuilt reporting for healthcare frameworks, while enabling rapid, evidence-backed incident response. With full packet capture, automated investigations, and controlled response actions that protect uptime, NetWitness delivers security that works with healthcare constraints—not against them.
In environments where downtime risks lives, NetWitness provides protection that healthcare can trust.
Threat Intelligence: The Key to Higher Security Operation Performance
Unlock the full potential of your Security Operations Center with deeper visibility, faster detection, and smarter response. This whitepaper explores how modern threat intelligence elevates SOC maturity and helps organizations stay ahead of evolving adversaries.