How SQL Injection Impacts Security, and What Actually Prevents it?
- SQL injection is the malicious act of manipulating database queries using unsafe input.
- Most SQL injection attacks are actually the result of basic vulnerabilities such as unvalidated inputs or the construction of dynamic queries.
- SQL injection prevention techniques include parameterized queries, input validation, and the use of the least privilege principle.
- SQL injection prevention techniques are no longer enough; the best way to protect against the attack is to monitor the system.
- Organizations that implement secure coding and monitoring techniques can reduce the impact of the attack.
Introduction
There’s a specific irony in the way SQL injection consistently appears in breach reports. It’s not something recent. It’s not complex. And still, it keeps functioning.
Recent data reinforces that this isn’t anecdotal. According to Verizon 2024, injection attacks still rank among the top three initial access vectors in web application breaches. The pattern hasn’t shifted. Attackers continue to exploit the same gaps because those gaps still exist.
In various sectors, attackers continue to take advantage of fundamental query manipulation to reach confidential data, circumvent defenses, and discreetly retrieve information gradually. Recent alerts from OWASP and CISA acknowledge a consistent trend: injection vulnerabilities continue to be among the most targeted weaknesses in corporate settings.
The problem isn’t a lack of awareness. It’s implementation. Security teams face intricate systems, burdened with outdated code, hasty integrations, and uneven controls. At some point in that stack, input processing fails. That’s everything an attacker requires
SQL Injection: Prevention vs Detection (Why Both Matter)
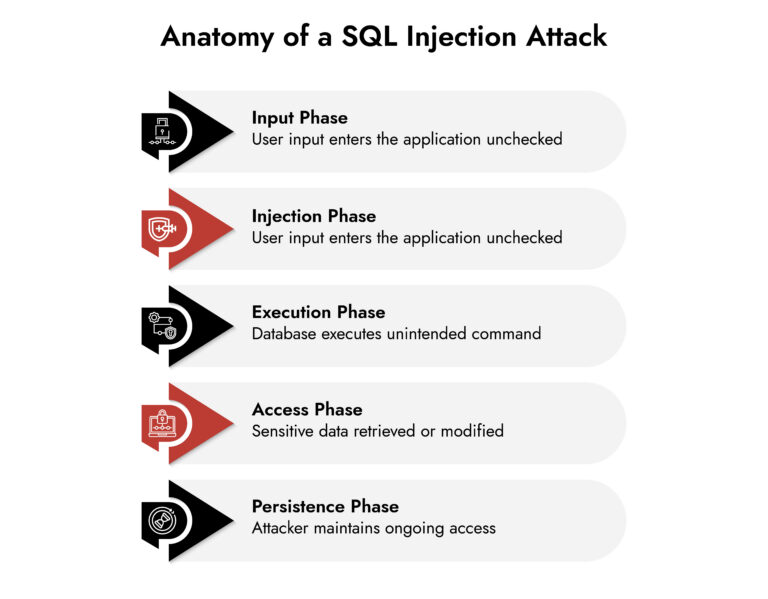
SQL injection happens when an application treats user input as executable database code. Attackers exploit this to read, modify, or delete data without authorization. The mechanics are simple. The impact is not.
Prevention: Your First Line of Defense
Prevention aims to remove any exposure to vulnerabilities prior to that exposure being realized. In order to combat SQL injection at its source, use one or more of the following methods:
- Using parameterized queries or prepared statements.
- Enforcing rigorous validation of all input data at all entry points.
- Implementing the principle of least privilege on database access to restrict users’ ability to view or enter data into a database.
- Avoiding dynamic SQL creation.
An effective implementation of one or more of these methods will greatly reduce the risk associated with SQL injection attacks.
The Reality: Prevention isn’t Perfect
Even well-governed environments carry gaps:
- Legacy code that bypasses modern standards
- APIs introduced without full security validation
- Missed edge cases in input handling
That’s where most SQL injection attacks succeed. Not because controls don’t exist, but because they’re not universal.
Detection: What Saves You When Prevention Fails
Detection focuses on identifying and containing the attack in real time.
- Monitor database query behavior for anomalies
- Correlate application activity with backend data access
- Detect unusual data extraction patterns
- Trigger alerts for suspicious query execution
This is how you block SQL injection attacks after they begin, before they escalate.
Where NetWitness Adds Value
NetWitness becomes critical in this phase. It provides:
- Deep visibility into network traffic, logs, and data movement
- Behavioral detection of abnormal queries and access patterns
- Cross-layer correlation between application inputs and database activity
- Faster response, reducing attacker dwell time
What this really means is simple: prevention reduces the chance of a breach. Detection determines whether it becomes one. In modern environments, both are non-negotiable.
Why SQL Injection Still Works in 2026
At its core, SQL injection exploits a simple failure: applications don’t clearly separate user input from executable queries. That sounds basic. It is. But the reality inside enterprise systems is anything but simple.
Here’s where things break:
- Applications still construct dynamic queries under time pressure
- Developers assume upstream validation exists when it doesn’t
- APIs introduce new, less-visible entry points
- Legacy components bypass modern security controls
The result is predictable. An attacker finds one weak input, injects a crafted query, and the database responds as if it’s business as usual. No alarms. No friction. Just data exposure.
What Major SQL Injection Breaches Actually Teach Us
1. The Smallest Gap is Enough
Most successful SQL injection attacks don’t involve complex chains. They rely on a single vulnerable input. A login field. A search parameter. An overlooked API endpoint. Once that entry point exists, the database becomes the attack surface. The takeaway is uncomfortable: scale doesn’t protect you. Precision does.
2. Prevention Failed First. Detection Failed Longer.
In breach investigations aligned with guidance from NIST, a consistent issue shows up: attackers weren’t stopped early, and they weren’t detected quickly. That gap comes from:
- No runtime SQL injection check
- Lack of visibility into query behavior
- No correlation between application logs and database activity
Prevention didn’t hold. Detection didn’t compensate. That’s where damage compounds.
3. Legacy Systems Quietly Expand Risk
Even organizations with strong modern practices carry hidden exposure. Old modules. Deprecated APIs. Third-party integrations that no one fully owns anymore. These areas often:
- Skip parameterized queries
- Lack proper validation
- Fall outside regular security testing
Attackers don’t go after your best-defended systems. They go after the ones you’ve stopped thinking about.
4. Data Loss is the Real Impact
When SQL injection succeeds, systems rarely crash. Instead, attackers extract data gradually:
- Customer records
- Credentials
- Financial data
- Internal operational data
This shifts the impact from disruption to exposure. Regulatory penalties, legal consequences, and long-term trust erosion follow. And by the time it’s detected, the damage is already done.
The financial impact reflects that shift. The 2024 IBM Security report states an average global breach cost of $4.45 million, with data exfiltration-driven attacks taking longer to detect and contain. When SQL injection enables silent data access, costs rise not from downtime but from delayed discovery.
SQL Injection Prevention: What Holds Up in Practice
SQL injection prevention isn’t theoretical. The fundamentals are well-established. The problem is consistency.
The controls that work are straightforward:
- Parameterized queries instead of dynamic SQL
- Strict input validation across all entry points
- Escaping user inputs where necessary
- Least privilege access at the database level
- Avoiding direct query construction in application logic
But here’s the nuance. These controls only work when applied everywhere. One exception reintroduces the risk.
What to Look for in a Unified Security Platform
- Cut through tool sprawl with a practical evaluation framework.
- Compare platforms based on visibility, detection accuracy, and automation.
- Validate real-world performance across hybrid and cloud environments.
- Make confident, risk-aligned security decisions.
How Can We Prevent SQL Injection in Modern Architectures
Modern systems don’t rely on a single application layer. They span APIs, services, and distributed components. Preventing SQL injection in this context requires coordination, not isolated controls.
Shift Security Earlier in the Lifecycle
- Embed automated SQL injection check in CI/CD pipelines
- Enforce secure coding standards through code reviews
- Block vulnerable builds before deployment
Expand Visibility Beyond the Application
- Monitor database query patterns
- Track anomalies in query execution
- Identify unusual access behavior in real time
Treat APIs as First-Class Attack Surfaces
- Validate all input at API gateways
- Test API endpoints for injection vulnerabilities
- Apply consistent controls across services
Build Feedback Loops
- Feed incident data back into development
- Continuously refine validation and detection rules
What this really means is simple: prevention must evolve with architecture.

How to Block SQL Injection Attacks Without Blind Spots
Blocking SQL injection attacks isn’t about a single control layer. It’s about eliminating blind spots.
That includes:
- Application inputs
- API requests
- Backend query execution
- Data movement across systems
The most effective strategies combine:
- Web application firewalls for known patterns
- Behavioral analytics for unknown patterns
- Real-time monitoring for query anomalies
Static defenses catch what’s expected. Behavioral detection catches everything else.
Where NetWitness Strengthen SQL Injection Defense
Even strong SQL injection prevention can fail under real-world conditions. That’s where detection becomes critical. NetWitness focuses on capturing and correlating activity across networks, endpoints, and logs. That capability directly addresses what most environments lack: context.
Here’s how it changes the equation:
Full Visibility into Activity
- Captures network traffic and logs
- Tracks how queries move through systems
- Identifies unusual access patterns
Correlation Across Layers
- Connects application behavior with backend database activity
- Highlights anomalies that isolated tools miss
Faster Response
- Enables investigation of suspicious activity quickly
- Reduces attacker dwell time
- Supports forensic analysis for containment
This doesn’t replace prevention. It reinforces it. When SQL injection slips through, visibility determines whether it becomes a breach or a contained incident.
SQL Injection Mitigation Strategies 2026
The next phase of SQL injection mitigation strategies 2026 reflects a shift in how applications are built and attacked.
What’s Driving Change
- AI-assisted attack generation increases payload variation
- API-first architectures expand entry points
- Cloud-native systems introduce distributed query paths
What Needs to Adapt
- Real-time behavioral monitoring of database activity
- Context-aware validation at every input layer
- Integrated detection and response across environments
Security teams that treat SQL injection as a solved problem will fall behind. Those that adapt continuously will reduce both likelihood and impact.
Conclusion
SQL injection persists because it exploits something fundamental: trust in input. The technical fixes are well known. The execution gaps are where risk lives.
Strong organizations don’t assume prevention is enough. They build layered defenses:
- Secure coding to reduce exposure
- Continuous testing to catch gaps early
- Real-time detection to limit impact
- Rapid response to contain threats
The difference between a network vulnerability and a breach isn’t whether SQL injection exists. It’s how quickly it’s identified and controlled. If there’s a shift worth making, it’s this: stop treating prevention as the finish line. It’s just the starting point.
Frequently Asked Questions
1. What is SQL injection?
SQL injection is a technique where attackers insert malicious SQL queries into application inputs, allowing them to manipulate databases and access or modify sensitive data.
2. How to protect from SQL injection attack?
To protect against a SQL injection attack:
- Use parameterized queries
- Validate and sanitize all inputs
- Restrict database permissions
- Monitor query behavior in real time
3. How do I prevent SQL injection attacks?
To prevent SQL injection attacks, one can follow secure coding best practices and also make use of automated testing and monitoring.
4. What role does secure coding play in SQL injection prevention?
Secure coding best practices can be very effective in preventing the execution of the input received by the system as SQL code itself. It plays a major role in SQL injection prevention.
5. What frameworks help address SQL injection risks?
OWASP and NIST are the frameworks that can be used to implement secure coding best practices and monitor the system.
6. How to block SQL injection attacks effectively?
To block SQL injection attacks:
- Deploy WAFs for known threats
- Monitor database queries for anomalies
- Correlate activity across systems
- Use detection platforms for real-time visibility
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.






