How does automation improve SOC efficiency?
Automation helps boost SOC efficiency by removing repetitive manual work from investigations. It can enrich alerts, gather evidence, open or update cases, trigger notifications, run playbooks, and execute approved containment steps. This helps analysts spend less time on routine tasks and more time responding to real threats.
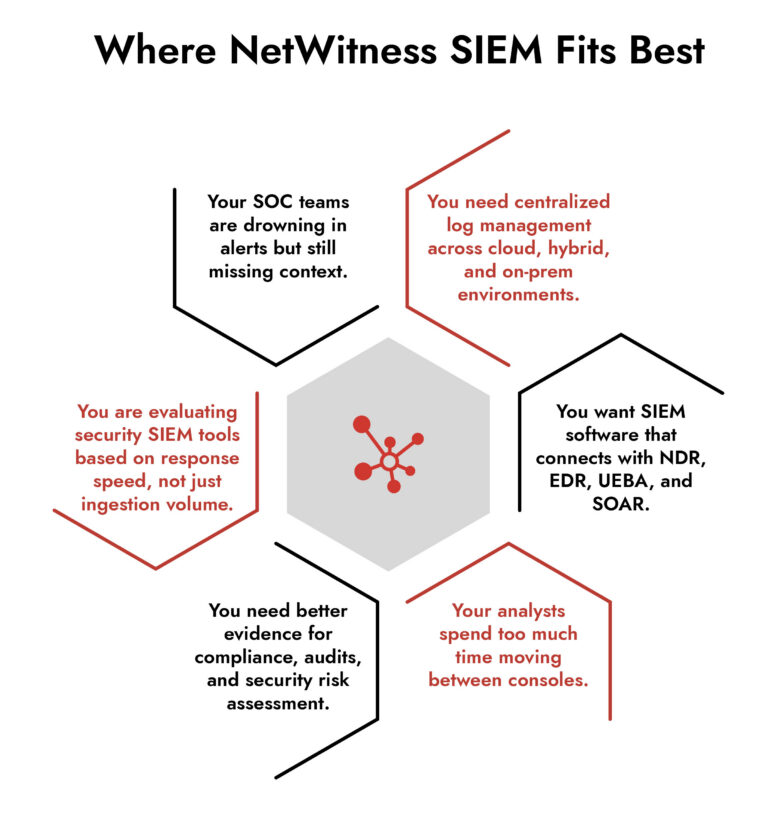
Most SOC teams are not short on alerts. They are short on time, context, and confidence.
Every day, the security operations center is expected to sort through authentication events, endpoint activity, network traffic, cloud logs, SaaS activity, compliance data, and threat intelligence. On paper, that should improve visibility. In practice, it often creates the opposite problem: too many signals and consoles that then need manual stitching before an analyst can answer basic questions: is this real, and what do we do next?
NetWitness SIEM software offers centralized log management, enriched metadata, behavioral analytics, threat intelligence, and response orchestration to help analysts see more, pivot faster, and act with better context.
Why Are SOC Teams Facing Alert Overload?
SOC teams are facing alert overload because modern security environments generate more signals than analysts can investigate. Every login, endpoint action, cloud event, network connection, SaaS activity, and policy violation can produce telemetry. That volume is useful, but only if the SOC can quickly separate routine activity from real risk.
The bigger issue is that many alerts arrive without enough context. And, data sits across different tools. Analysts have to spend valuable time piecing the story together manually. That slows triage, increases fatigue, and makes it easier for high-priority threats to get buried under low-value noise.
This is why SIEM software matters. A strong security SIEM does more than collect alerts. It means giving analysts a clearer investigative path across logs, network, endpoint, user behavior, and threat intelligence so they can move faster from “something happened” to “this is what happened, this is the risk, and this is what we should do next.”
What NetWitness SIEM Changes for SOC Teams
NetWitness SIEM software unifies logs, packets, endpoints, NetFlow, user behavior, and threat intelligence, with real-time enrichment that includes business context and ML/UEBA analytics. NetWitness describes this as a way for analysts to detect known and unknown threats, prioritize based on organizational impact, and reconstruct attacks more completely.
A basic SIEM can tell you that something happened. A stronger security SIEM helps explain what happened, where it started, what else it touched, how risky it is, and what action should happen next.
For SOC teams, it means that instead of beginning every investigation with a pile of disconnected alerts, analysts can start with enriched and correlated evidence.
1. Centralized Log Management Without Losing Investigative Context
Organizations invest in SIEM software primarily for its centralized log management. But centralization alone is not enough. If the SIEM simply hoards raw events, all that the SOC teams do is move the noise to a different place.
NetWitness SIEM software centralizes and manages logs from more than 350 sources across on-premises, cloud, and hybrid environments. It also uses dynamic parsing and metadata enrichment at capture time, which helps analysts search, correlate, and investigate faster.
That helps in two ways:
- It supports visibility across distributed environments. Modern enterprises rarely have one clean perimeter. They have cloud platforms, SaaS applications, identity systems, remote users, data centers, and third-party tools. SOC teams need one place to see activity across that estate.
- Enriched metadata gives analysts a better starting point. Instead of manually interpreting their meaning, they can work with normalized, searchable, contextualized data.
2. Faster Triage through Risk-Based Prioritization
A noisy SOC is risky. If every alert is flagged as urgent, analysts are forced to make fast judgment calls with incomplete information. Low-value alerts steal time from high-risk investigations. Real threats get delayed because the queue is crowded.
NetWitness addresses this with enrichment, analytics, and prioritization. Its evolved SIEM materials describe real-time enrichment with business and threat intelligence to help prioritize based on actual business risk.
That is especially important for buyers because SIEM value is not measured by how many alerts it can generate. It is measured by whether the SOC can consistently identify the alerts that matter.
A port scan against a low-value test system is one thing. Suspicious authentication, unusual endpoint behavior, lateral movement, and network communication tied to a sensitive business asset is something very different. The SIEM software should help analysts see that difference quickly.
3. AIin SIEM Tools: Useful When it Explains the Evidence
AI in SIEM tools is often discussed like a magic layer that solves detection. That is not how mature SOC teams should evaluate it.
The practical value of AI is better baselining, anomaly detection, prioritization, and explanation. NetWitness uses machine learning and behavioral analytics across security data, including logs, packets, endpoint, and cloud telemetry. Its cybersecurity data analytics page describes unsupervised ML for asset discovery, behavioral baselines, anomaly detection, contextual enrichment, and dynamic risk scoring.
AI in SIEM tools should help analysts answer:
- Is this behavior normal for this user, host, or peer group?
- Is this event isolated, or part of a broader attack path?
- Does the risk justify immediate containment?
- Can the analyst explain the decision to leadership, audit, or incident response?
Choose the Right SIEM with Confidence
4. Connecting SIEM,NDR,EDR, SOAR, and UEBA into One Workflow
Many SOC teams already own strong tools. The problem is that those tools often work in parallel rather than together.
NetWitness is designed as a broader threat detection and response platform with SIEM, NDR, EDR, SOAR, and UEBA modules. NDR is used for full packet visibility and session reconstruction, SIEM for instant visibility into log data, centralized log management, cloud and SaaS log monitoring, and suspicious activity detection that can evade signature-based tools.
As real attacks do not stay inside one telemetry type, this interconnected system matters.
A compromised identity may appear first in authentication logs. Lateral movement may show up in network traffic. Malware execution may surface on the endpoint. Data staging may require packet or session reconstruction. Response may require containment actions, ticket updates, user disablement, or firewall changes.
NetWitness EDR adds full execution context for endpoint processes, process tree reconstruction, behavioral analytics, threat intelligence enrichment, MITRE ATT&CK mapping, and automated actions such as containment, blocking, and artifact collection.
For SOC teams, this reduces one of the most painful parts of investigation: moving between tools just to rebuild the story.
5. Automation That Reduces Repetitive Work
Automation does not replace analysts; it helps them dedicate time to more important tasks.
When the analysts are stuck in repetitive work, such as evidence gathering, ticket creation, severity updates, notifications, containment handoffs, and post-incident documentation, they are unable to give time to more critical tasks. As a result, real threats keep getting missed.
NetWitness supports intelligent automation, guided workflows, and orchestration across more than 500 tools. It accelerates incident response, reduces manual workload, and provides consistent, repeatable processes.
Frequently Asked Questions
1. What are the typical costs associated with deploying a SIEM solution?
The cost of deploying a SIEM solution usually depends on
- data volume
- number of log sources
- deployment model
- retention requirements
- integrations
- professional services
- ongoing tuning
2. What features in a SIEM solution help simplify SOC workflows?
The most useful features include
- centralized log management,
- event normalization,
- dynamic parsing,
- metadata enrichment,
- behavioral analytics,
- risk scoring,
- threat intelligence,
- case management,
- automation, and
- integrations with endpoint, network, cloud, and identity tools.
3. Can SIEM solutions integrate with other security tools?
Yes. Modern SIEM solutions should integrate with security tools across endpoint, network, identity, cloud, ticketing, threat intelligence, and response systems.
4. How does centralized visibility help SOC teams?
Centralized visibility helps SOC teams see activity across users, assets, applications, cloud services, endpoints, and network traffic in one place. This reduces tool switching and helps analysts understand whether an alert is isolated or part of a larger attack.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.





