What is the difference between traditional network monitoring tools and network traffic analysis software?
Traditional network monitoring tools, such as NetFlow collectors, SNMP-based performance monitors, and bandwidth utilization dashboards, are engineered to answer operational questions. Is the link saturated? Is this application experiencing latency? These are valuable questions for network operations teams, but they’re almost entirely irrelevant for security investigations.
Network traffic analysis software is purpose-built for a different question entirely: is this traffic consistent with legitimate behavior, or does it suggest compromise?
The SOC teams are always overwhelmed with the volume of alerts from various tools. But the problem is that none of them tells the full story. That’s where network traffic analysis tools come in. Not as another alert source to manage, but as a fundamentally different kind of visibility layer. The one that tells you what’s actually happening on the network, across every segment, whether or not an endpoint agent was there to see it.
What Are Network Traffic Analysis Tools?
Network traffic analysis tools continuously capture, inspect, and analyze network communications to identify suspicious patterns and abnormal behavior. They look for active threats in real time and across historical records. They work at the packet, flow, and session level to give SOC teams a comprehensive view of what’s happening inside their infrastructure.
They baseline behavior and activities for different asset classes and user groups. If there are any deviations from them, they raise alerts. They don’t care whether an attacker has disabled an endpoint agent or bypassed a firewall rule — if traffic crosses the network, the tool sees it.
Modern network traffic analysis software combines deep packet inspection with behavioral analytics, machine learning-driven anomaly detection, and telemetry correlation across on-premises, cloud, and hybrid environments.
In practical SOC terms: think of network traffic analysis tools as the institutional memory of your network. Your endpoint tools tell you what happened on a machine. Your NTA platform tells you what that machine was doing with everything else — and whether that behaviour looks like a threat.
Why Network Traffic Analysis Tools Matter for Modern SOC Operation
Understanding why these tools matter requires understanding how modern attackers actually behave. The initial compromise is usually the easy part. What attackers spend most of their time doing is moving laterally through environments, escalating privileges, establishing persistence, and exfiltrating data. The good part is that all of these activities generate network communication.
The challenge is that this communication is often designed to look legitimate.
Traditional tools such as SIEM rules, endpoint detection rules, and IDS signatures rely on known patterns and threshold-based alerting. That works well for commodity threats. But for threats that apply even basic operational security practices or evasion techniques falls short in several specific ways:
- East-west traffic is largely invisible. Most perimeter-focused tools never see lateral movement between internal systems.
- Encrypted traffic creates blind spots. TLS encryption, which is now the norm, obscures payload inspection for legacy tools.
- Fragmented telemetry hides the full picture. Individual alerts don’t tell you that three different systems have been communicating with the same suspicious external IP across a 72-hour window.
- Dwell time goes undetected. Without continuous behavioral baseline, slow-moving threats can persist for weeks before triggering anything.
Network traffic analysis tools have become essential in modern enterprise cybersecurity because they provide visibility where many traditional controls fall short. Attackers today rely on stealthy lateral movement, encrypted communication, and legitimate protocols to avoid detection. Endpoint alerts alone rarely show the full attack path. By analysing packet data, behavioural patterns, and historical network telemetry, these tools help SOC teams uncover hidden threats, validate incidents faster, and contain breaches more effectively. They also offer investigation context that improves response accuracy and forensic confidence. In complex hybrid environments, network traffic analysis is no longer an optional capability.
— Ibrahim Badawi, Sales Engineer, NetWitness
How Network Traffic Analysis Tools Work
A mature network traffic analysis tool operates across several overlapping layers. Let’s understand how these layers work:
- Packet Inspection: NTA captures raw packet data from networks, SPAN ports, or inline sensors. It extracts metadata, including source and destination IPs, ports, protocols, session characteristics, and more.
- Network metadata analysis: Instead of saving every packet, NTA records the attributes of each network conversation. It includes data like who talked to whom, over which protocol, for how long, and how much data was transferred. This is a computationally efficient method that helps scale across high-volume environments.
- Behavioural anomaly detection is where the analytical intelligence lives. The platform builds statistical baselines for assets, users, protocols, and traffic flows over time, then identifies deviations that exceed expected thresholds or match threat behaviour profiles.
- Telemetry correlation ties these layers together across environments. Modern network detection and response tools are designed to ingest telemetry from hybrid infrastructure and correlate it into unified investigation timelines.
Common SOC Use Cases for Network Traffic Analysis Tools
Concrete operational scenarios are useful for building internal business cases and training analysts on what to look for. Here are the cases that help:
Ransomware Propagation Detection – NTA platforms detect the internal reconnaissance and lateral movement that precedes ransomware execution days before encryption begins. SMB scanning patterns, credential relay activity, and anomalous staging behavior are visible at the network layer even when endpoints are compromised.
C2 Beaconing Identification – Command-and-control communication has distinctive characteristics such as periodic intervals, unusual destination domains, and non-standard protocol usage, which network behavioral analysis surfaces reliably. Even encrypted C2 channels leave metadata signatures that trained models detect.
Insider Threat Investigation – When an insider begins moving data toward external destinations, the network sees it first. Large outbound transfers to personal cloud services, access to file repositories outside normal job function, or communication to competitor domains all appear in network telemetry before they appear in HR reports.
Cloud Workload Communication Analysis – Cloud environments create new east-west traffic that traditional on-premises tools never see. NTA platforms that ingest VPC flow logs can detect compromised cloud instances communicating with unusual external endpoints or accessing sensitive storage buckets outside normal application patterns.
Threat Hunting Support – Proactive threat hunting requires queryable historical telemetry. Hunters use NTA platforms to search for indicators of compromise across weeks of network history, test hypotheses about attacker presence, and validate whether specific TTPs were executed in the environment.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
How Network Traffic Analysis Tools Improve SOC Efficiency
For SOC managers, the conversation about network traffic analysis tools often comes down to a practical question: will this improve my team’s operational effectiveness in ways I can actually measure? The answer, when these platforms are deployed well, is yes.
- Reduced alert fatigue: One of the largest productivity destroyers in any SOC is the volume of low-context, poorly prioritised alerts. Good Network traffic analysis platforms don’t just generate more alerts — they correlate detections into higher-fidelity incidents, suppress duplicate observations, and surface the signals that actually warrant analyst attention.
- Faster investigation workflows: The biggest time sink in most incident investigations isn’t detection — it’s data retrieval. A mature NTA platform provides unified, searchable network telemetry that collapses this process from hours to minutes. When an analyst can instantly see every connection a compromised host made over the last 30 days, the investigation scope becomes clear quickly.
- Improved mean time to respond: Faster detection and faster investigation directly compress the time between initial compromise and contained response. Network threat detection tools that surface lateral movement early change containment outcomes.
- Stronger forensic confidence: When incidents go to legal, compliance, or executive review, the quality of evidence matters. Network telemetry provides a level of forensic integrity that endpoint logs alone can’t match — particularly when endpoint agents have been tampered with or weren’t deployed on affected systems.
A mature NTA platform provides unified, searchable network telemetry that collapses this process from hours to minutes: an approach exemplified by NetWitness Network Detection and Response, which enables analysts to reconstruct activity across the network with full-fidelity metadata and packet insights.
Challenges Security Teams Face Without Network Traffic Analysis
East-west blindness is the most critical gap. Most breaches involve significant lateral movement before reaching their ultimate target. Without visibility into internal network communications, security teams are essentially watching the front door while attackers move freely through the building.
Encrypted traffic is effectively invisible. TLS encryption — which now accounts for the overwhelming majority of enterprise traffic — protects legitimate communications and malicious ones equally. Without network analysis capabilities designed for encrypted environments, a substantial portion of the attack surface simply cannot be monitored effectively.
Dwell time accumulates silently. Without continuous behavioral baselining, there’s no reliable way to detect slow-moving threats that deliberately stay below alert thresholds. Attackers who understand that speed triggers detection will operate at a pace that conventional tools never flag.
Threat hunting has no foundation. Proactive threat hunting requires historical network telemetry to search. Without it, hunting programs are reduced to endpoint-only investigations that miss the lateral movement, exfiltration, and C2 activity that live exclusively on the network layer.
Conclusion
Advanced threat detection doesn’t fail because organizations lack alerts. It fails because the alerts that exist don’t provide visibility into the network layer where most of the meaningful attacker activity actually happens.
Network traffic analysis tools address this gap not by generating more alerts, but by providing visibility built on continuous observation of network behavior, historical telemetry depth, and detection logic that surfaces attacker activity even when it’s designed to look legitimate.
For SOC teams, the operational impact is concrete: faster investigation timelines, stronger forensic confidence, detection of threats that endpoint and perimeter tools miss, and a proactive hunting capability that doesn’t depend on waiting for something to break through a rule.
The environments that get compromised and stay compromised for the longest are the ones where attackers had freedom of movement that nobody was watching. Network traffic analysis tools are the ones that close that window.
Frequently Asked Questions
1. Why are network traffic analysis tools important for modern threat detection?
Because modern attackers don’t stay in one place. They move laterally through networks, use legitimate protocols to disguise their traffic, and deliberately operate in the gaps between your other detection tools. Network traffic analysis tools are built to catch unknown patterns, by establishing what normal looks like and flagging what deviates from it. They’re particularly critical because so much enterprise traffic is encrypted, cloud and hybrid environments have created huge new blind spots, and dwell times for undetected breaches remain concerningly long.
2. How do NTA tools support SOC teams?
They give analysts a complete record of network activity. Therefore, instead of spending hours pulling logs from five different systems to reconstruct what happened, an analyst can query unified telemetry and get the answer. With investigation context already attacked, they are able to provide high-fidelity detections.
3. Do network traffic analysis tools detect insider threats?
Yes, and this is actually one of the areas where NTA tools add unique value. Insider threats almost always generate network activity that falls outside normal behavior patterns. Because NTA tools baseline what “normal” looks like for each user and system over time, they’re well-positioned to flag deviations that suggest insider threat activity, even when the individual activities might appear innocuous in isolation.
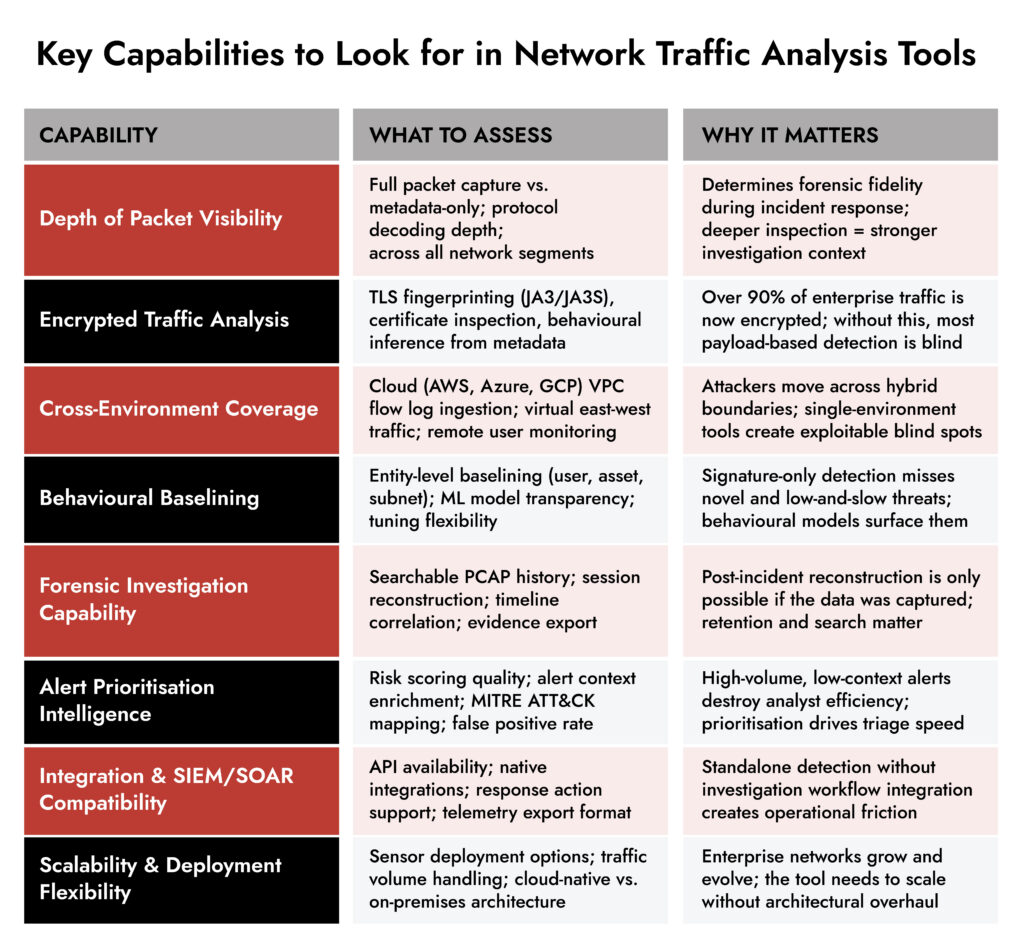
4. How do you select the best network traffic analysis tool?
Start with your actual environment, not the vendor’s demo environment. The most important questions are:
- Does it cover all your network segments, including cloud and remote access?
- How does it handle encrypted traffic?
- What’s the quality of the alert context it produces?
- How does it integrate with your existing SIEM, SOAR, and investigation workflows?
A tool that does fewer things but does them with high fidelity and low noise will serve your SOC better than a comprehensive platform that produces alerts your team can’t effectively triage.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.