What is network data loss prevention and why is it important?
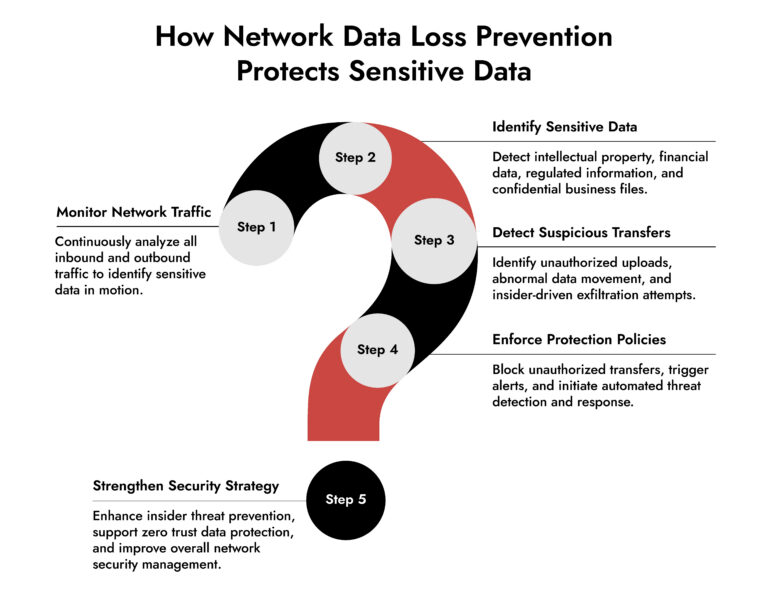
Network data loss prevention (network DLP) monitors and analyzes network traffic to detect and prevent unauthorized transfers of sensitive data. It protects information such as intellectual property, financial records, and personal data while it moves across the network.
Network DLP is important because traditional security tools focus on protecting systems, not data in motion. By combining network traffic monitoring, network device monitoring, and policy enforcement, network DLP helps organizations prevent insider threats, detect data exfiltration, and support zero trust data protection strategies.
Introduction
Sensitive data no longer stays inside defined boundaries. It moves constantly across endpoints, cloud services, internal systems, partner networks, and unmanaged environments. Every movement creates risk. And most breaches today are not caused by sophisticated malware alone. They happen because sensitive data leaves the network unnoticed.
This is where network data loss prevention becomes essential.
Unlike traditional controls that focus on blocking external threats, network DLP focuses on protecting the data itself. It monitors network traffic, identifies sensitive information in motion, and stops unauthorized transfers before exposure occurs.
In modern enterprise environments, network data loss prevention is no longer optional. It is a foundational component of network security monitoring, insider threat prevention, and zero trust data protection.
Why Traditional Security Controls Fail to Protect Data in Motion
Most organizations already use firewalls, endpoint tools, and access controls. But these controls were designed to protect systems, not data movement. Here’s the gap. Firewalls allow approved traffic. Endpoint tools monitor individual devices. Access controls govern authentication.
None of these provide deep visibility into what data is actually moving across the network.
This creates blind spots in:
- Internal lateral movement
- Cloud uploads and downloads
- Unauthorized data transfers
- Insider-driven data exfiltration
- Shadow IT and unmanaged applications
Without network traffic monitoring, security teams cannot answer critical questions:
- What sensitive data is leaving the network?
- Who is accessing and transferring it?
- Where is it being sent?
- Is the transfer legitimate or malicious?
Network data loss prevention solves this by inspecting traffic at the network level.
What Network Data Loss Prevention Actually Does
Network data loss prevention monitors, analyzes, and controls sensitive data as it moves across enterprise networks. It works by combining network traffic monitoring, data classification, and policy enforcement.
Core capabilities include:
1. Inspecting Network Traffic for Sensitive Data
Network DLP analyzes traffic in real time to detect:
- Personally identifiable information (PII)
- Financial data
- Intellectual property
- Confidential business documents
- Regulated data
This visibility is critical for enterprise network monitoring tools to identify risk in motion.
2. Detecting Unauthorized Data Transfers
Network DLP identifies suspicious behaviors such as:
- Data uploads to unauthorized cloud services
- Transfers to external servers
- Large or unusual data movement patterns
- Data transfers outside business hours
This strengthens threat detection and response capabilities.
3. Enforcing Data Protection Policies
Network DLP can:
- Block unauthorized transfers
- Alert security teams
- Log and investigate activity
- Trigger automated response workflows
This transforms network security management from passive monitoring to active protection.
Network Data Loss Prevention vs Endpoint DLP: Why Both Are Needed
Endpoint DLP protects data on individual devices. Network DLP protects data in transit. Both serve different but complementary roles.
Endpoint DLP focuses on:
- Files stored locally
- USB transfers
- Copy and paste activities
- User behavior on specific devices
Network DLP focuses on:
- Data moving across the network
- Transfers between internal systems
- Data sent to cloud platforms
- External communications and uploads
Endpoint tools cannot see traffic from unmanaged devices, cloud services, or internal network transfers. Network DLP provides this missing visibility.
Together, they enable comprehensive insider threat prevention and data protection coverage.
Why Network DLP Is Critical for Insider Threat Prevention
Insider threats are one of the hardest risks to detect because insiders already have access. These threats include:
- Employees exfiltrating intellectual property
- Compromised user accounts
- Accidental data exposure
- Privileged user misuse
Traditional security tools often miss these risks because they focus on external threats. Network data loss prevention identifies insider threats by monitoring actual data movement patterns.
For example, network DLP can detect when:
- An employee uploads sensitive files to personal cloud storage
- A user transfers large volumes of data to an external server
- Sensitive data is accessed outside normal workflows
- Unauthorized systems attempt to receive internal data
Combined with network device monitoring and network security monitoring, this provides early detection before damage occurs.
How Network DLP Supports Zero Trust Data Protection
Zero trust assumes no user, device, or system should be automatically trusted. But zero trust is incomplete without visibility into data movement. Network data loss prevention enables zero trust data protection by enforcing policies based on:
- Data sensitivity
- User behavior
- Network activity
- Transfer destination
Instead of trusting network location, network DLP evaluates the data itself. This ensures sensitive data remains protected regardless of where it moves. When combined with network segmentation, organizations can restrict sensitive data flows to authorized paths only.
How Network DLP Enhances Threat Detection and Response
Network DLP strengthens threat detection and response by providing context that other tools miss.
Security teams gain visibility into:
- Data exfiltration attempts
- Lateral movement involving sensitive data
- Suspicious internal transfers
- Unauthorized external communications
This improves investigation accuracy and response speed. For example, if an attacker compromises a user account, network DLP can detect unusual data transfers even if the attacker uses legitimate credentials. This enables faster containment and reduces breach impact.
The Role of Network Device Monitoring and Network Traffic Monitoring
Network data loss prevention depends on deep network visibility. This is achieved through:
Network device monitoring
This tracks activity across network infrastructure including:
- Routers
- Switches
- Servers
- Network gateways
It identifies where data flows and which devices are involved.
Network traffic monitoring
This analyzes actual traffic moving across the network. It reveals:
- Data transfers
- Communication patterns
- Protocol usage
- Suspicious or abnormal behavior
Together, these capabilities provide the foundation for effective network security monitoring and data protection.
How Network DLP Strengthens Overall Network Security Management
Network data loss prevention improves network security management by enabling proactive control over sensitive data.
Key benefits include:
- Complete visibility into data movement – Security teams understand where sensitive data travels across environments.
- Improved insider threat prevention – Network DLP detects insider-driven data exfiltration early.
- Stronger compliance and regulatory protection – Network DLP helps enforce policies for protecting regulated data.
- Faster threat detection and response – Security teams can identify and stop data exfiltration in real time.
- Reduced risk of data breaches – Sensitive data is protected even if attackers bypass other defenses.
How Network DLP Fits into a Modern Security Architecture
Network data loss prevention works alongside other security controls to create layered protection.
It integrates with:
- Enterprise network monitoring tools
- Network performance management systems
- SIEM platforms
- Threat detection and response solutions
- Network security monitoring tools
- Network segmentation controls
This creates unified visibility across network activity, data movement, and potential threats. Instead of relying on isolated tools, organizations gain coordinated protection.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.
Why Modern Enterprises Are Prioritizing Network Data Loss Prevention
As cloud adoption, remote work, and digital transformation accelerate, sensitive data moves more frequently across distributed environments. This increases the risk of data exposure. Network data loss prevention ensures organizations can:
- Monitor all data movement
- Prevent unauthorized transfers
- Detect insider threats
- Enforce data protection policies
- Support zero trust security strategies
Without network DLP, security teams operate without visibility into one of the most critical risk areas. Data in motion.
Strengthening Network Data Loss Prevention with Unified Network Visibility
Network data loss prevention is most effective when combined with deep network visibility and threat detection capabilities. Modern security platforms integrate network traffic monitoring, network device monitoring, and threat detection into a single system.
This enables organizations to:
- Monitor all network activity
- Detect sensitive data movement
- Identify insider threats early
- Investigate incidents faster
- Enforce zero trust data protection
A unified approach ensures sensitive data remains protected across the entire network, not just individual systems.
Conclusion
Data is the primary target in modern cyberattacks. Protecting systems alone is no longer enough. Organizations must protect the data itself, especially while it moves across the network. Network data loss prevention provides the visibility and control required to detect, monitor, and prevent unauthorized data transfers.
When combined with network security monitoring, network segmentation, network device monitoring, and threat detection and response, network DLP becomes a critical pillar of modern security strategy.
Organizations that implement network data loss prevention gain stronger insider threat prevention, improved data protection, and greater confidence in their ability to prevent breaches.
Frequently Asked Questions
1. What is network data loss prevention? ortant for intrusion detection?
Network data loss prevention is a security capability that monitors network traffic to detect, prevent, and control the unauthorized transfer of sensitive data. It inspects data in motion and enforces policies to protect confidential information.
2. How does network DLP differ from endpoint DLP?
Network DLP protects data as it moves across the network, while endpoint DLP protects data stored or accessed on individual devices. Network DLP provides visibility into data transfers between systems, cloud services, and external destinations.
3. Why is network DLP critical in modern security strategies?
Network DLP is critical because it provides visibility into sensitive data movement across distributed environments. It helps detect insider threats, prevent data exfiltration, and support zero trust data protection.
4. What types of data does network data loss prevention protect?
Network data loss prevention protects sensitive information such as intellectual property, financial data, personal data, confidential documents, and regulated information.
5. How does network data loss prevention help prevent insider threats?
Network data loss prevention monitors user activity and detects suspicious data transfers. It identifies unauthorized uploads, unusual data movement, and abnormal behavior patterns, helping security teams prevent insider-driven data exfiltration.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.