Process at a Glance - What You’ll Do
- Capture and visualize all traffic flows
- Establish what normal looks like
- Use metadata and packet analysis to spot anomalies
- Correlate signals across time and systems
- Validate events and enable response
Introduction
Network traffic contains the story of every connection that happens in your environment. Every session, every protocol, and every byte transferred is a potential signal of attacker activity. That’s why a network traffic monitor remains core to real detection – it tracks activity that endpoint logs and alerts often miss.
Enterprise networks now generate massive data volumes. Encryption rates exceed 80% of all internet traffic, forcing deeper inspection of behavior and flow metadata, not just payloads.
Our key differentiator is simple: we collect and retain all network traffic, not just metadata or selective smart PCAP. Full-fidelity capture enables multi-baseline behavioral analysis with real evidence, higher confidence, and fewer false positives.
Why Network Traffic Monitor Matters for Intrusion Detection
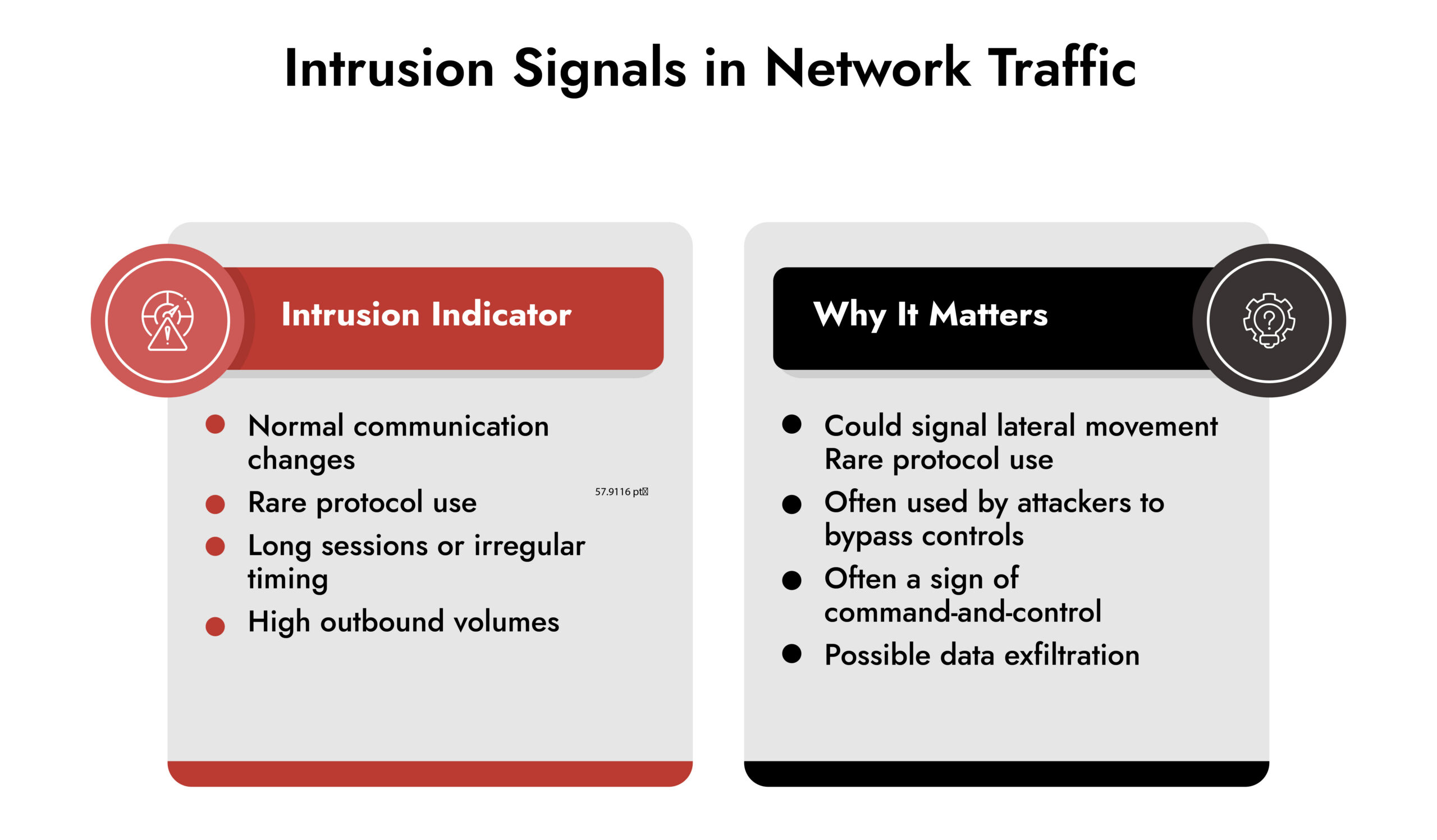
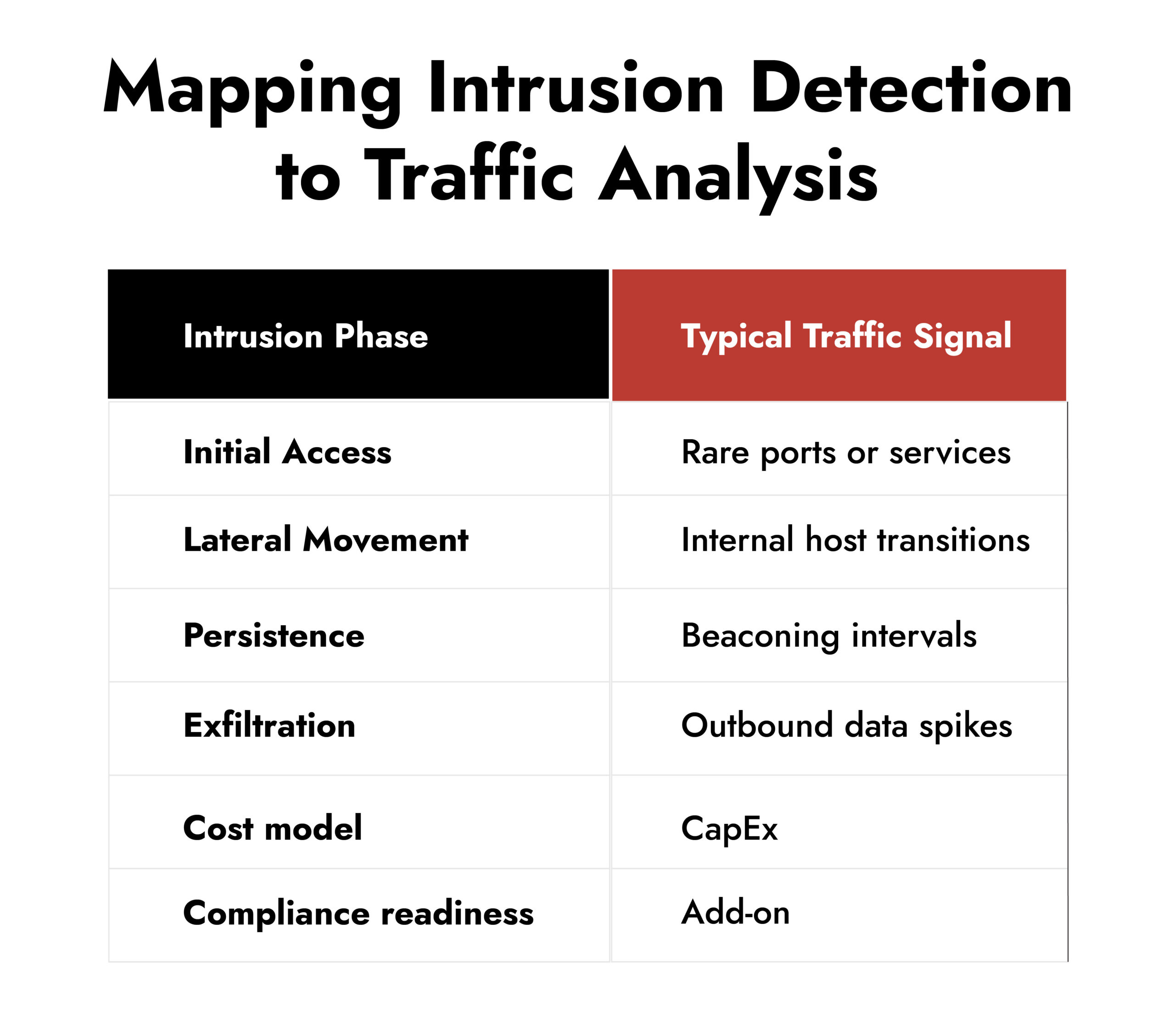
Hidden lateral movement. Encrypted command-and-control channels. Sessions that almost look legitimate. Traditional security controls miss these because they rely on signatures or endpoint logs. Traffic analysis sees what actually traverses the network.
Real-world trend data backs up: many organizations cite lack of visibility as a top barrier to effective detection. In the broader network traffic analysis market, enterprise security and threat detection account for more than 30% of adoption, and that share continues to grow.
Example: An attacker with valid credentials may log in and spin up a reverse shell. Endpoint logs might only show a login event. Network traffic data reveals the ongoing session, irregular protocol use, and unexpected connections, which together signal compromise.
As we said, every byte counts and often the weakest signals are those that hide the greatest threats and can enable early detection. It is essential to collect and record everything to allow in-depth analysis and logical deductions that provide a complete view of the attack scenario. Only the full picture helps to reduce dwell time for an attack and explains how to apply the right remediations preventing recurrence of the same incident.
— Alessio Alfonsi, Sales Engineer, NetWitness
The Practical Workflow for Detecting Intrusions in Network Traffic
Build Visibility First (You Can’t Detect What You Don’t See)
True visibility goes beyond flow logs. It includes:
- East-west (internal) and north-south (internet) flows
- Hybrid cloud segments
- Encrypted sessions
- IoT and microservices traffic
Most enterprises overlook lateral flows until it’s too late. That’s where threat actors often propagate.
Example: In a mid-size enterprise, segmented VLANs meant internal traffic wasn’t logged centrally. A lateral movement using internal SMB calls went unnoticed for weeks because visibility only existed at perimeter firewalls.
Visibility should capture session metadata, endpoints, timing, and protocol context, not just packet counts.
Establish Baselines and Network Behavior
A baseline is your map of normal. Without it, you chase noise instead of threats.
A practical baseline should capture multiple behavioral dimensions, including:
- Typical communication paths between critical assets
- Expected protocol distribution within each subnet
- Normal session duration ranges
- Average and peak connection sizes
- Time-of-day activity patterns
A behavioral analysis system does not label activity as malicious on its own. It highlights deviations. The distinction between benign and malicious behavior becomes clearer when multiple baselines across different entities are evaluated together within a unified analytical framework.
A deviation in a single baseline often produces false positives. Operations teams patch systems at odd hours. Admins use uncommon ports during maintenance. But when deviations occur simultaneously across multiple baselines – protocol, timing, session length, data volume, peer relationship – confidence increases and false positive rates drop. That layered signal gives analysts something actionable.
To build effective baselines, the system must extract rich metadata from network traffic, not just a minimal flow record. Port and IP alone are insufficient. Session duration, byte counts, directionality, protocol metadata, encryption attributes, and response behavior all matter. Shallow telemetry produces shallow detection.
Example: Asset A normally communicates with Asset B over HTTPS on port 443 during business hours. Sessions average under 2 MB and last less than three minutes.
Now consider this shift:
- An SSH connection appears between the same assets
- It occurs late at night
- The session runs significantly longer than historical norms
- The connection transfers a much larger volume of data than typical interactions
A port change alone could reflect legitimate maintenance. A time deviation alone might be an approved job. A large transfer could be a backup activity. But when port, time, duration, and connection size all diverge from established baselines simultaneously, the probability of malicious lateral movement or staging activity increases materially.
This is where mature network behavior analysis becomes operationally valuable. Not because it flags anomalies. Because it correlates behavioral deviations across entities and elevates the ones that matter.
Packet-Level Inspection Where it Counts
Once you identify an anomaly, packet-level inspection confirms intent.
Packet analysis isn’t always about full capture. It’s about targeted validation, such as:
- Confirming a suspicious C2 channel
- Identifying protocol misuse
- Inspecting malformed headers
Packet analyzers help decode content and context within sessions. They let you see header flags, handshake anomalies, and other fine-grained signals that flows alone don’t reveal.
Example: A server responding to DNS over HTTPS traffic from an unexpected source might look normal at the flow level. Only packet inspection tools that record all network traffic can fully reconstruct what was exfiltrated and accurately assess incident criticality. Partial metadata or selective capture leaves gaps that undermine confidence and response.
Correlate Signals Across Time and Systems
Anomaly detection in isolation produces noise. Correlation makes sense out of context.
Combine insights like:
- Authentication logs
- Network anomalies
- Endpoint telemetry
- Threat intelligence
This multi-signal correlation amplifies true positives and suppresses incidental noise.
Example: A spike in outbound encrypted connections alone isn’t enough. If that spike follows an abnormal login and unusual lateral flows, it’s highly suspicious.
What matters is not rule-based correlation, but the ability to aggregate data from multiple sensors within a single platform. That unified view enables accurate forensic reconstruction and accelerates incident response.
Using a Network Traffic Monitor to Investigate and Respond to Intrusions
Detection without actionable context still slows response. Your goal is to turn signals into decisions.
Good network traffic analysis should:
- Support rapid investigation
- Provide evidence for containment
- Tie directly into response workflows
Detection should not end at an alert. It should trigger context-rich analysis that teases apart attacker behavior from benign anomalies.
In enterprise environments, teams prioritize not just finding issues but understanding them quickly. That means structured metadata, timelines, session views, and clear relationships between events.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
Where Advanced Traffic Monitoring Makes the Difference
Comprehensive traffic analysis bridges gaps left by isolated tools. It provides the evidence and clarity teams need to act confidently under pressure.
One effective model combines behavioral baselines with selective deep packet inspection and correlation across telemetry sources. This isn’t about replacing existing tools, it’s about enriching them with reliable network context.
Look for capabilities that include:
- Session and Content reconstruction
- Protocol awareness
- Hybrid environment support
- Metadata and payload-aware analysis
Real teams win when they see the full story in motion, not just alerts in isolation.
Common Pitfalls That Undermine Detection
Even sophisticated setups fail when practices lag. Watch out for:
- Gaps in visibility (e.g., east-west traffic blind spots)
- Overreliance on perimeter data
- Treating individual alerts as conclusive
- Ignoring temporal and correlation context
Fix practices before adding tools – good data practices enable effective intrusion detection.
Conclusion
Network traffic is the richest source of truth on what happens inside your infrastructure. Done right, network traffic monitoring reveals attack paths before damage escalates. It exposes subtle patterns, validates suspicions, and empowers decisive action.
Don’t rely on alerts alone. Make network traffic analysis a central part of your network detection and response strategy.
If you want to elevate your detection capability, start by refining visibility, establishing behavioral baselines, and correlating signals with context-rich data.
Frequently Asked Questions
1. Why is analyzing network traffic important for intrusion detection?
Analyzing network traffic reveals hidden attacker activity that endpoint tools miss, showing communication patterns, protocol anomalies, and unexpected sessions that indicate intrusions.
2. How to detect intrusion in the network?
Detect intrusions by monitoring traffic, establishing baselines, inspecting packets where needed, and correlating events across logs, behavior, and network flows.
3. What are common indicators of intrusion in network traffic?
Indicators include unusual internal connections, rare protocol use, unexpected data flows, beaconing patterns, and session anomalies detectable through network traffic analysis.
4. What tools are used to analyze network traffic for intrusions?
Professionals use flow collectors, packet analyzers, behavioral analytics engines, and network traffic monitoring tools that aggregate and interpret session and metadata.
5. What is the difference between IDS and network traffic analysis?
An IDS generates alerts based on predefined rules. Network traffic analysis interprets flows and behavior across time, making it suited to spot unknown, evolving threats.
6. Can a network traffic monitor work in cloud and hybrid environments?
Yes. Modern network traffic monitoring supports hybrid and cloud traffic sources, enabling visibility across on-prem, cloud, and distributed segments.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.