What are the latest insider threat statistics for 2026?
Most enterprises don’t lose data because defenses fail. They lose data because trust fails.
Recent industry reporting makes that clear:
- Sixty-eight percent of breaches involve human elements, like credential misuse or internal errors.
- Organizations, on average, presently spend over $17 million annually on incidents connected to insiders.
- Credential misuse continues to be one of the most frequently seen initial access methods identified by U.S. government and industry warnings.
- Insider cases often take significantly longer to detect because activity appears legitimate until behavior deviates from baseline.
What this really means is simple: perimeter defenses don’t see risk that already has access. That gap is exactly where structured insider threat management programs operate.
Introduction
The breach that hurts the most rarely begins with malware. It begins with access that looks legitimate.
A valid login. A trusted user. A routine file transfer.
That’s why insider threat management needs the same board-level attention as ransomware or state-backed attacks. The numbers make that clear. Verizon’s 2024 Data Breach Investigations Report revealed that 68% of breaches include a human factor. Ponemon’s study estimates that incidents related to insiders cost companies more than $17 million annually.
But behind those statistics are patterns most security leaders recognize immediately.
It’s rarely a dramatic espionage case. More often, it’s credential misuse that goes unnoticed. A contractor who keeps access longer than they should. A trusted employee who uploads sensitive files to a personal cloud drive to work faster. Or a compromised account moving quietly through systems because nothing about the login looks suspicious.
Insider risk cuts deeper than perimeter threats because it exploits trust. The activity blends into normal operations. This is precisely why managing insider threats needs to be deliberate, organized, and closely connected with detection, investigation, and response, rather than being viewed as an afterthought.
What Insider Threat Management Really Means
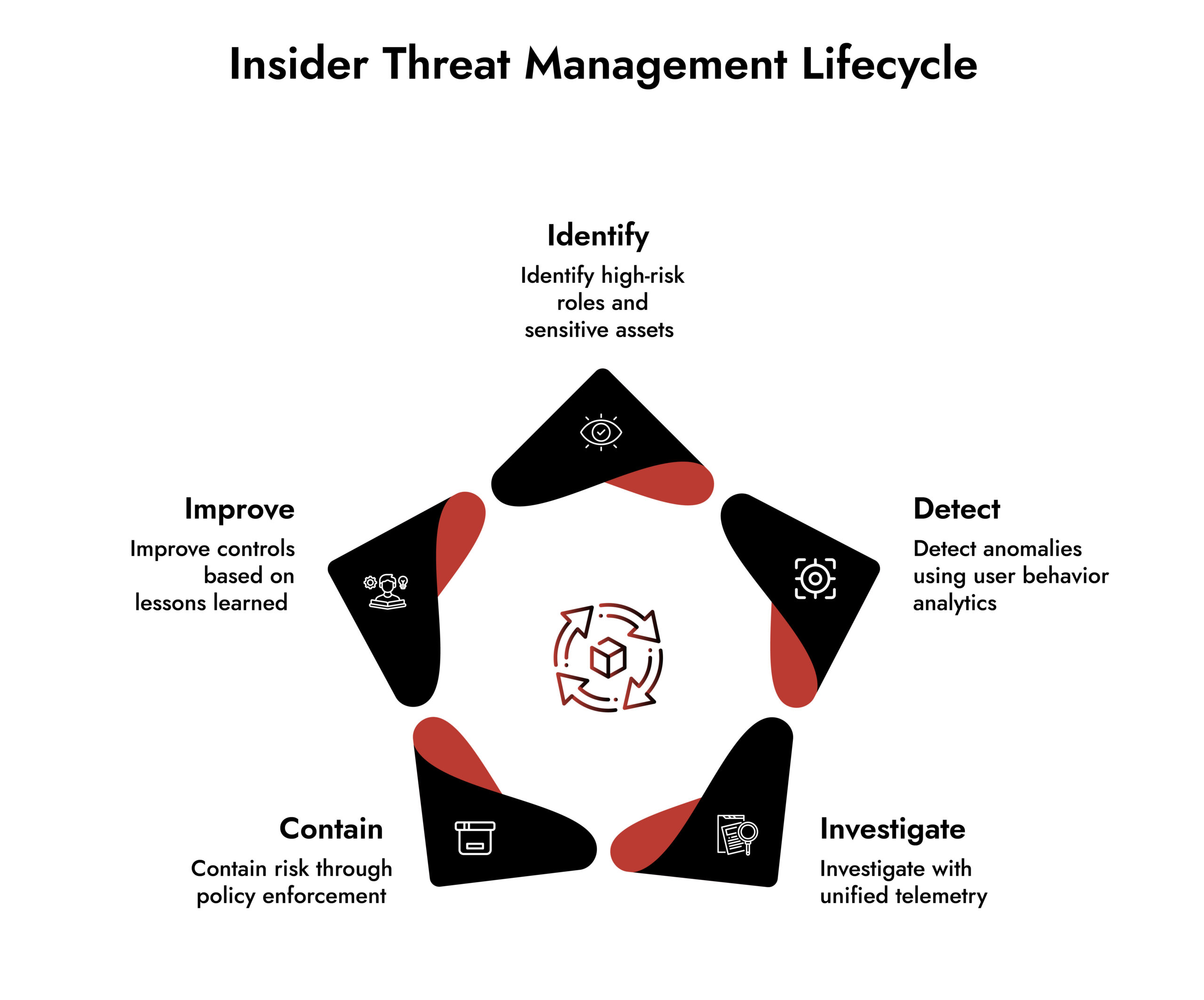
At its core, insider threat management is a process. It helps identify, detect, investigate, and reduce risks from trusted access.
It is not employee surveillance. It is risk governance backed by telemetry and analytics.
A mature insider threat management framework includes:
- Continuous insider threat monitoring
- Behavioral baselining through user behavior analytics
- Contextual insider threat detection
- Clearly defined escalation workflows
- Legal and HR alignment
- Measurable performance metrics
NIST doesn’t treat insider risk as theoretical. In SP 800-53 and related guidance, the message is clear:
- Log meaningful activity across systems and identities
- Establish a baseline for what normal behavior actually looks like
- Monitor access according to roles, privileges, and risk exposure
- Detect anomalies early before impact escalates
In other words, visibility and context come first. Without them, insider threat management remains reactive.
Programs that rely on scattered alerts without that context struggle. A single outlier seldom provides the complete picture. Teams lacking behavioral baselines and role awareness tend to pursue distractions rather than recognizing genuine insider risk.
Why Insider Threats are so Hard to Detect
Insider threats don’t breach the perimeter, they operate inside it. That difference defines the risk.
Traditional controls excel at blocking perimeter attacks. Insider threat cyber security requires identifying misuse of legitimate access. That means detecting behavior that is technically allowed but operationally risky.
Detection becomes difficult because:
- Access is authorized.
- Privileges may be broad.
- Behavioral changes unfold gradually.
- Data exfiltration can mimic normal business activity.
Consider a senior engineer accessing repositories outside their project scope. The access may not violate policy immediately. But combined with unusual working hours and bulk file compression, the risk profile shifts.
This is where insider threat detection must move beyond static rules and into a behavioral context.
How Insider Threat Management Defends the Enterprise
A good insider threat management program does three important things.
First, it creates context. Second, it prioritizes risk, directly leading to a faster response.
Let’s break it down.
1. It Establishes Behavioral Baselines
Every effective insider threat management initiative begins with understanding normal activity.
User behavior analytics track patterns such as:
- Login frequency and location
- File access patterns
- Peer group comparisons
- Data transfer volumes
- Privilege changes
Over time, the system learns what typical behavior looks like for each role.
When deviations occur, analysts gain context, not just alerts.
Example: A financial analyst begins accessing engineering documentation and compressing large data sets at unusual hours. No rule may explicitly block this action. But behaviorally, it diverges from baseline patterns. The program surfaces it for review before data leaves the environment.
That’s insider threat prevention – powered by intelligence, not assumption.
2. It Correlates Signals Across the Environment
Single data sources rarely tell the full story.
Strong insider threat management correlates:
- Endpoint activity
- Identity and authentication logs
- Cloud application events
- Email metadata
Correlation transforms noise into narrative. For instance:
- Endpoint logs show mass file staging.
- Network telemetry shows encrypted outbound traffic.
- Identity logs reveal recent privilege elevation.
Individually, these signals may appear routine. Together, they indicate elevated insider risk.
This layered visibility strengthens insider threat protection significantly.
3. It Applies Risk Scoring
Not every anomaly signals malicious intent. Mature insider threat solutions prioritize risk using dynamic scoring models.
Risk scoring considers:
- Sensitivity of accessed assets
- Degree of behavioral deviation
- Historical activity patterns
- Threat intelligence context
- Role criticality
This prevents alert fatigue and ensures that insider threat monitoring focuses on meaningful risk.
4. It Enables Structured Investigation
Detection without investigation capability stalls response.
Effective insider threat software supports:
- Timeline reconstruction
- Full-session visibility
- File movement tracing
- Lateral movement tracking
- Historical packet analysis
Techniques for threat hunting enhance this model even more. Analysts actively look for trends such as inactive credential exploitation or slow data extraction that could evade threshold-based notifications.
Insider threat management becomes strategic when hunting supplements detection.
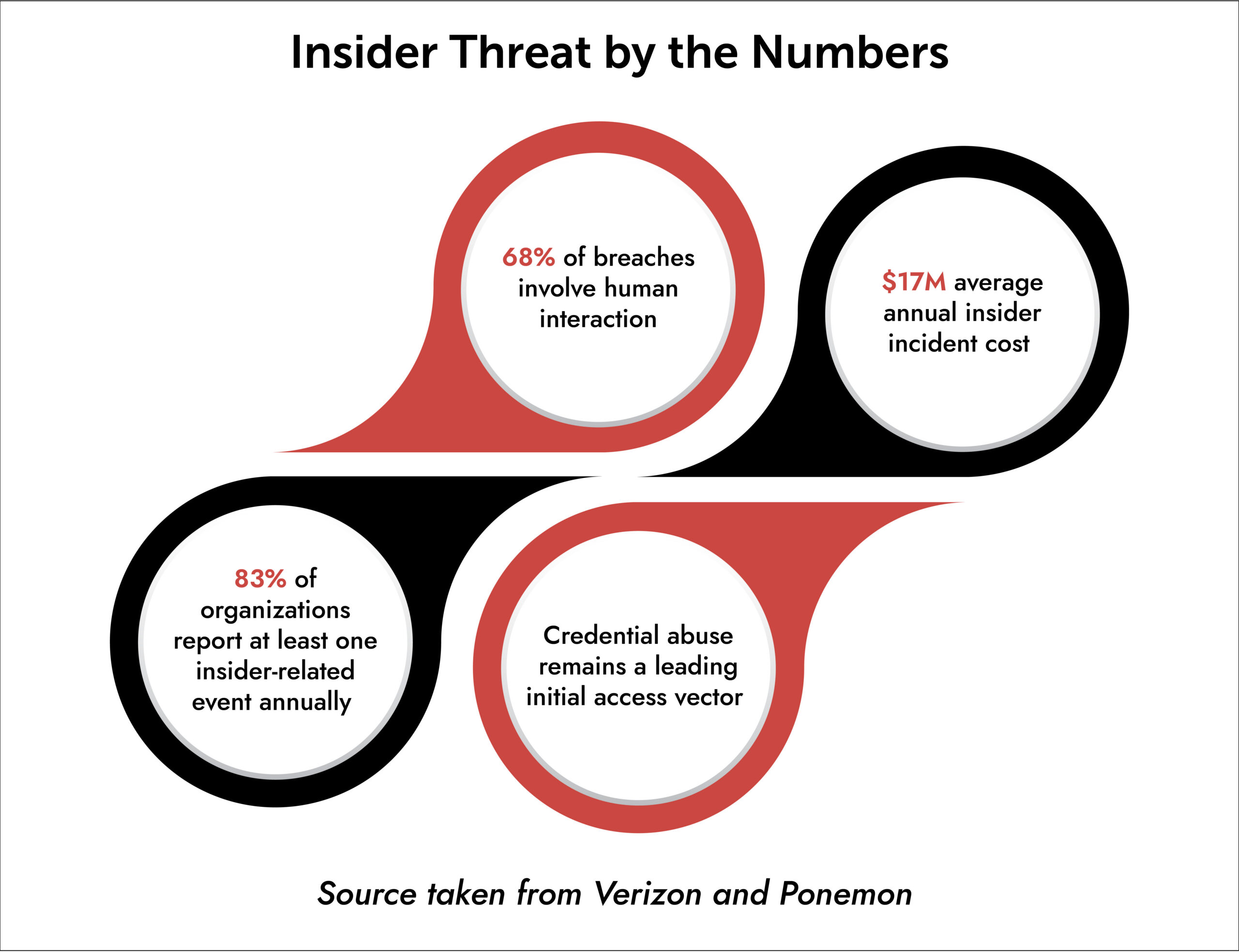
Source taken from Verizon and Ponemon
Aligning Insider Threat Management with Zero Trust
Zero Trust operates on continuous validation. Insider threat management operationalizes that principle.
When behavioral risk increases, Zero Trust controls can respond:
- Trigger step-up authentication
- Restrict session access
- Temporarily reduce privileges
- Isolate endpoints
Instead of taking trust as a given based solely on identity, organizations consistently verify behavior. Insider threat cybersecurity improves when access choices integrate behavioral risk indicators immediately.
Accelerate Threat Detection with Predictive Intelligence
Traditional security detection often catches threats after an attack has begun—when domains are already registered and command-and-control infrastructure is active. The NetWitness + BforeAI integration changes that by bringing predictive intelligence directly into threat detection and response workflows.

Common Implementation Challenges
Even technically mature enterprises face obstacles when deploying insider threat programs.
Challenges often include:
- Privacy and legal concerns
- Cross-functional coordination gaps
- Fragmented telemetry sources
- Excessive false positives
- Absence of a formal insider threat plan
A well-defined insider threat plan should outline:
- Scope and objectives
- Monitoring boundaries
- Escalation pathways
- Governance oversight
- Metrics and reporting cadence
Without governance, insider threat tools lose effectiveness quickly.
The Role of Technology
Technology does not replace governance. It enables scale.
Strong insider threat software integrates:
- Advanced analytics
- Long-term data retention
- Cross-domain correlation
- Case management workflows
- Automated response triggers
When evaluating insider threat tools, focus on:
- Depth of telemetry
- Investigation speed
- Transparency of scoring models
Insider threat protection improves when tools reduce friction between detection and response.
How NetWitness Supports Insider Threat Management
Insider investigations demand depth. You need to see what happened, not just that something happened.
NetWitness supports enterprise insider threat management by unifying:
- Full packet capture for forensic reconstruction
- Endpoint visibility for file and process tracking
- Log analytics for identity and privilege monitoring
- Centralized investigation workflows
This method helps in reconstructing user sessions and detecting data exfiltration attempts, as well as validating behavioral anomalies in different layers.
Threat hunting techniques can also benefit from the historical visibility provided. Insider activities are often carried out slowly, and the ability to perform retrospective analysis is available over a long extent of time.
Organizations that are committed to insider threat solutions can gain unified visibility to minimize blind spots between multiple tools.
A Quick Reality Check
Which scenario worries you most?
- A privileged administrator with broad access
- A third-party contractor with limited oversight
- A remote employee using unmanaged devices
- A compromised service account
The correct answer is not one. It’s all of them.
That’s why insider threat management must operate across identity, device, and network layers simultaneously.
Conclusion
Insider risk is not a theoretical concern. It is measurable, recurring, and expensive.
Robust insider threat management initiatives protect the organization by establishing behavioral context, linking telemetry, intelligently prioritizing risk, and facilitating organized investigations.
They reinforce zero trust. They reduce uncertainty. They transform internal visibility into decisive action.
The next serious breach may not involve sophisticated malware. It may involve trust misused.
The question is simple: will your organization detect it early enough?
Frequently Asked Questions
1. What is an insider threat in cyber security?
A threat insider in cyber security is a user, contractor, or account. They misuse their access in ways that create security risks.
2. What is an insider threat management program?
An insider threat management program is a group of policies and procedures in an organization. It includes governance, analytics, monitoring insider threats, and response plans.
3. Why are insider threats so difficult to detect?
They use valid credentials and often mimic normal behavior. Effective insider threat detection requires behavioral analytics and contextual correlation across systems.
4. How do insider threat programs defend the enterprise?
They support baselining behavior and have built-in risk scoring as well as correlation, which aids in strengthening insider threat prevention efforts.
5. How does insider threat management align with Zero Trust?
Zero Trust enforces continuous verification. Insider threat management feeds behavioral risk insights into access decisions, enabling adaptive controls.
6. What challenges do enterprises face when implementing insider threat programs?
Common challenges include privacy considerations, data fragmentation, alert fatigue, and unclear governance. A formal insider threat plan supported by scalable insider threat software helps address these barriers.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.





