What tools are best for analyzing encrypted network traffic?
The best instruments for performing encrypted traffic analysis include behavioral analysis, metadata analysis, and artificial intelligence techniques. Among these are NDR instruments, AI-based encrypted traffic analytics, and network monitoring solutions with built-in encrypted traffic visibility, which allow monitoring encrypted network traffic without decryption. Solutions applying JA3/SA3 fingerprints, anomaly detection technologies, and encrypted traffic analysis techniques can be used for detecting encrypted threats by means of analyzing encrypted packets. Solutions for enterprises like NetWitness, as well as products inspired by the technologies developed by companies such as GreyCortex, Cato Networks, and Corelight, will help address important issues, for example, how to check if network traffic is encrypted.
Staying Ahead of Hidden Threats in Encrypted Data
Encrypted network traffic has been on the rise for years due to a combination of factors, including the growing focus on data privacy and security, adoption of cloud-based services, and changes in how people work and communicate.
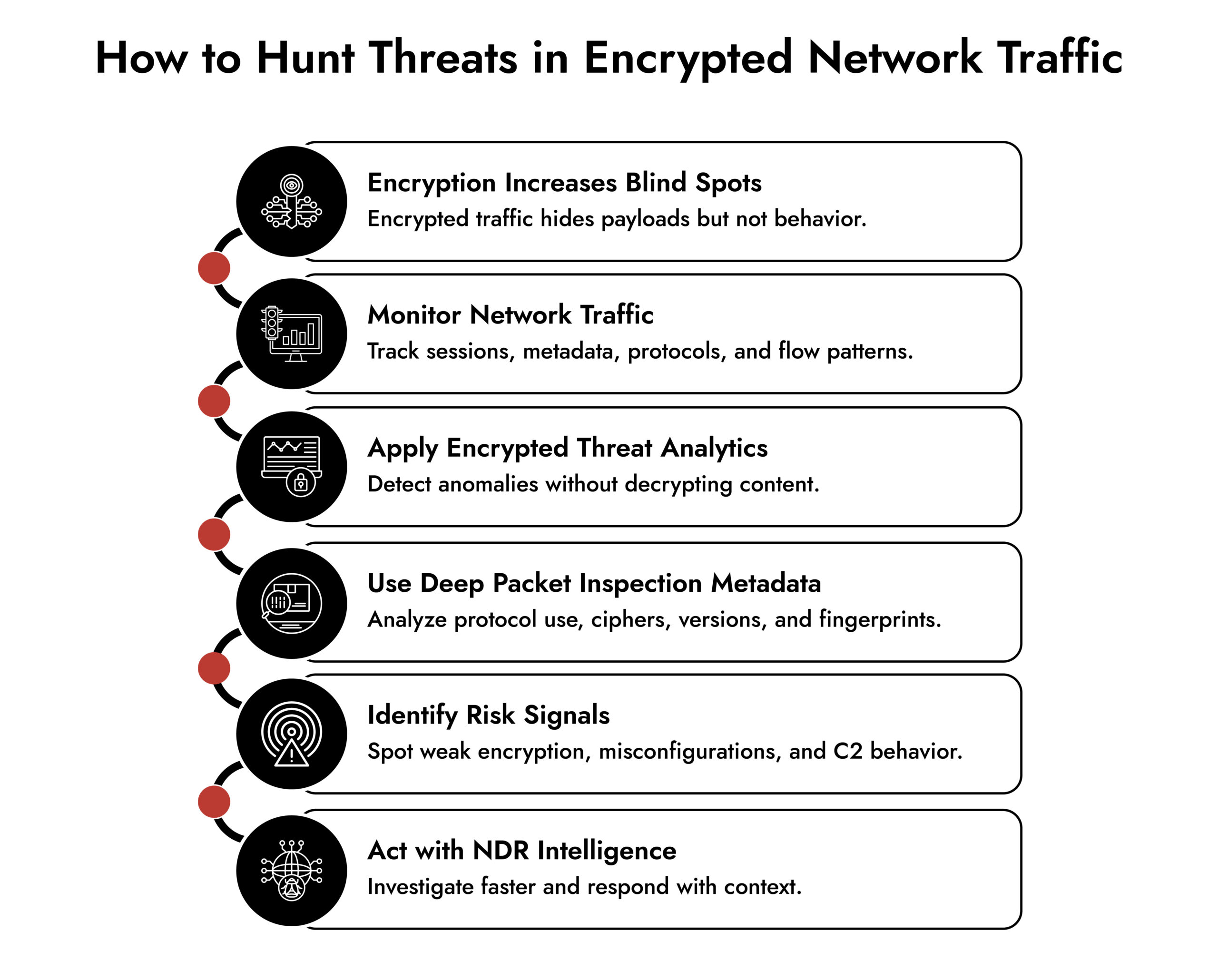
But encrypted network traffic also presents unique challenges for threat hunters. By obscuring visibility, encryption makes it more difficult to detect potential threats and calls for advanced encrypted traffic analysis techniques.
In many ways, encrypted network traffic is like Schrödinger’s cat of information security, we think the data is encrypted, and we hope it’s encrypted. Still, we don’t know for sure unless we examine the underlying network traffic. Security analysts must validate that encryption is functioning correctly to ensure data moves safely and securely and confirm how to check if network traffic is encrypted in real environments.
In this context, proactive threat hunting is about identifying risk as much as detecting attackers. While many associate it with “finding the bad guys,” it’s often about discovering misconfigurations which are far more common than active intrusions.
By understanding the challenges of encrypted network traffic and implementing proactive hunting strategies, organizations can better protect themselves against misconfigurations and cyberattacks that exploit weaknesses in network traffic and introduce encrypted threats.
What is Encryption in Network Traffic?
Encryption converts readable data (plaintext) into unreadable code (ciphertext) during transmission across an encrypted network.
The process works like this:
- Data is encrypted before it moves across the network.
- The receiver decrypts it using a key.
- Anyone in between only sees encrypted packets.
With plaintext traffic, issues are obvious. With encrypted network traffic, visibility drops significantly.
That’s why security teams rely on behavior-based analysis, not payload inspection. Instead of reading content, they analyze patterns, protocols, metadata, and anomalies using encrypted traffic analytics and encrypted threat analytic approaches.
Key Benefits of Network Traffic Analysis in Encrypted Environments
Network traffic analysis gives security teams visibility where traditional tools fall short, especially across encrypted network traffic.
Key benefits include:
- Improved visibility into encrypted traffic – Even when payloads are hidden, analyzing metadata, protocols, and behavior helps teams build encrypted traffic visibility and understand what’s happening on the network.
- Early detection of hidden threats – Abnormal traffic patterns, unusual connections, and suspicious beaconing often surface before alerts trigger elsewhere, key for identifying encrypted threats early.
- Faster threat investigation – Network traffic analysis provides context around who communicated with whom, when, and how, reducing investigation time across encrypted network environments.
- Reduced blind spots across the network – Continuous monitoring helps uncover unmanaged assets, shadow IT, and misconfigured services moving through encrypted network traffic.
- Stronger incident response – By analyzing network traffic in real time using encrypted traffic analysis methods, teams can contain threats faster and limit lateral movement.
- Better compliance and audit support – Network traffic data helps validate encryption strength, protocol usage, and policy enforcement across encrypted network traffic.
This is why organizations rely on network traffic analysis and encrypted traffic analytics to move from reactive alerting to proactive security.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
Checking Facts and Identifying Risks in Encrypted Traffic
Checking facts and identifying risks is all about challenging assumptions, analyzing encrypted network traffic to ensure it aligns with what’s expected.
If an organization has policies stating “X, Y, and Z are not allowed,” it might be tempting to assume compliance. However, network traffic monitoring often reveals violations or deviations hidden within encrypted traffic.
By proactively identifying risks, security teams can confirm whether policies are being followed and reduce exposure to misconfigurations or encrypted threats.
Practical Tips to Analyze Encrypted Network Traffic
- Start with current policies: Evaluate the current policies and establish the datasets needed to authenticate them, such as systems that provide encrypted traffic visibility.
- Begin with a theory: Any proactive threat hunt starts with one. Narrow down on what you are searching, and then apply encrypted traffic analysis methods to test your hypothesis and locate anomalies.
- Identify mismatching protocols: Use protocol mismatches to scan encrypted network traffic. A mismatch may indicate malformed traffic or potential malicious intent.
- Look at client metakeys: The client metakey shows what application initiated the traffic. Even with encryption, this provides insight into encrypted packets behavior.
- Consider the key of the cipher: Weak or outdated algorithms introduce risk in an encrypted network and must be continuously validated.
- Think about version key: Older protocol versions (like outdated TLS) can expose vulnerabilities within encrypted network traffic.
Supporting Compliance and Audits with Encrypted Traffic Visibility
As compliance regulations and cyber insurance audits grow more rigorous, organizations must demonstrate how data in encrypted network traffic is protected.
This involves assessing encryption strength, protocol versions, and algorithms used in transmission while ensuring strong encrypted traffic visibility.
Many organizations ask, “How do we translate this network traffic data into business terms?”
Tips for Supporting Audits
- Choose a tool with reporting capabilities: Select a platform that converts encrypted traffic analytics into business-ready reports.
- Translate network traffic data for actionable results: Break down insights from encrypted network traffic to demonstrate compliance and guide decision-making.
By connecting technical monitoring with business needs, organizations ensure both compliance and informed governance.
Detecting C2 Activity in Encrypted Network Traffic
Command and control (C2) traffic occurs when attackers communicate with compromised systems using network traffic as the medium.
Once a malicious payload executes, it begins beaconing back to the command server. Traditionally, such patterns were easy to identify in plaintext traffic.
But with encrypted network traffic, attackers now use jitter and randomness to evade detection, making traditional detection ineffective.
Modern detection relies on baselines and behavioral analysis using encrypted traffic analytics. Over time, even jittered beaconing reveals patterns.
Detecting behavior in encrypted network traffic is often the first step in uncovering encrypted threats and initiating deeper investigation.
Using JA3 and JA3S for Encrypted Traffic Analysis
JA3 and JA3S are widely used encrypted traffic analysis methods for fingerprinting TLS traffic.
- JA3 fingerprints the client hello message
- JA3S fingerprints the server response
Together, they create unique identifiers for sessions, helping analysts track anomalies across encrypted network traffic without decrypting encrypted packets.
How NetWitness Enables Encrypted Traffic Analysis
A network detection and response platform like NetWitness provides deep encrypted traffic visibility for proactive threat hunting.
With NetWitness, organizations can:
- Analyze encrypted traffic to uncover hidden threats.
- Apply machine learning-driven encrypted traffic analytics.
- Detect anomalies across encrypted network traffic in real time.
- Translate findings into compliance-ready reports.
- Automate workflows and response actions.
This enables a shift from reactive detection to proactive defense using advanced encrypted threat analytic capabilities.
Conclusion: Turning Encrypted Traffic from Blind Spot to Advantage
Privacy depends on encryption but encryption also creates blind spots. Without proper encrypted traffic analysis, threats can move undetected.
Organizations that invest in proactive threat hunting, continuous monitoring, and strong encrypted traffic visibility can validate encryption, detect anomalies, and reduce risk across encrypted network traffic.
Ultimately, the goal is simple: ensure that encrypted network traffic protects your data without protecting your attackers.
See Every Threat, Stop Every Attack
Gain complete visibility across cloud, on-prem, and virtual networks with NetWitness® Network Detection and Response. Detect and investigate threats faster with real-time analytics and forensic-grade session reconstruction.






