What is the evolution of cybersecurity threats?
Cybersecurity threats were loud and opportunistic attacks when they originated in the 1980s. Today, they are multi-stage campaigns orchestrated by organized groups. They are not only technically complex but also operate like businesses and long-term operators.
There was a time when cybersecurity threats meant getting an irritating virus on a computer. It often ended with strange wallpaper on your system, a slowed-down machine, or a few corrupted files. But today, that is not the world we live in now.
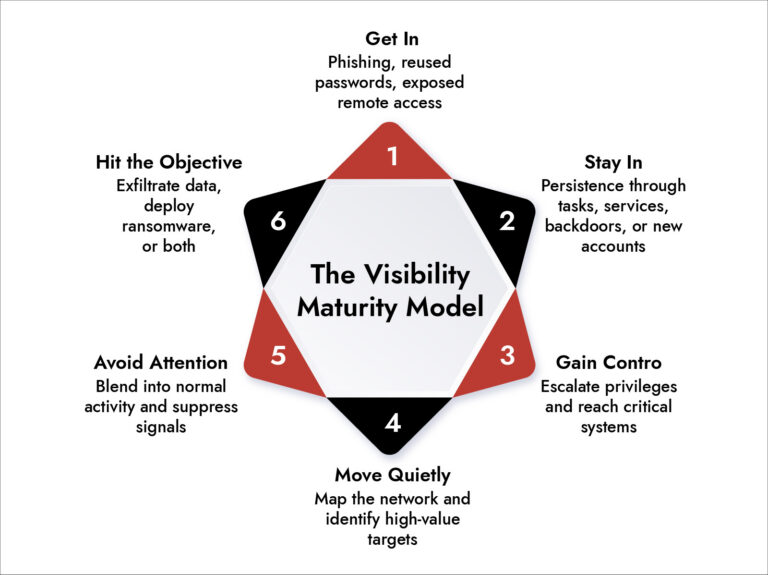
A modern threat can sit inside an organization for days or weeks without setting off anything dramatic. During that time, the attacker is moving with clear intentions. They are programmed to map the environment, steal credentials, and move stealthily towards valuable systems.
That is the real story behind the evolution of cyber threats. They got advanced and disciplined. Let’s look at how it all started and where the threats stand today. More importantly, what can help us withstand these multi-stage cybersecurity threats?
Evolution of Cybersecurity Threats
From the late 1980s through the early 2000s, most attacks were not malicious.
The likes of Morris Worm, ILOVEYOU, Melissa, Code Red, and Nimda just spread fast, caused disruption, and made headlines. Most of them were obvious the moment they landed. All that these attacks wanted to achieve was usually disruption, notoriety, experimentation, or just seeing whether something could spread.
Security teams employed signature-based antivirus software that did a decent job when the threat was loud and recognizable. Perimeter firewalls made sense when the line between “inside” and “outside” was still reasonably clear. Security was reactive, but for that phase of the internet, it often worked well enough.
By the mid-2000s, attackers started treating cybercrime less like a hobby and more like a business. That shift changed the design of attacks almost overnight. Banking trojans such as Zeus and SpyEye were built to stay quiet, watch users log in, collect credentials, and send that data back without drawing attention. The malware was designed to be invisible.
Once money became the motive, everything else followed. Command-and-control infrastructure improved. Obfuscation improved. Evasion improved. Persistence became essential because an attacker who gets detected too early loses the one thing that matters most: access.
Cybercrime had found its business model, and the threat landscape became more serious almost immediately.
Around 2010, APTs changed the tempo of cyber threats. Advanced Persistent Threats pushed the industry into a different era because they introduced a much longer game. These were not attackers trying to get in, grab something, and disappear before sunrise. They were trying to get in and stay put for months and longer. Stuxnet is still an example that showed the world that cyber operations could move beyond theft and disrupt physical operations, too.
That is also when defenders started needing a better language for describing attacks. It was no longer enough to say “malware had been found on a host.” Teams needed to talk about behavior-based frameworks such as MITRE ATT&CK, credential access, privilege escalation, lateral movement, collection, and exfiltration.
What is the Status of Cybersecurity Threats in 2026?
Today’s threat landscape is not defined by one clever exploit or one nasty malware family. It is defined by coordination.
Attackers regularly combine multiple techniques in a single intrusion. Some use fileless methods that live in memory. Some rely on built-in tools like PowerShell, WMI, and scheduled tasks so their activity blends into normal administration. Some skip malware almost entirely and go straight after identities, session tokens, and cloud access. Once the adversaries gain valid credentials, the intrusion often looks less like a “hack” and more like an ordinary login.
For instance, the Ransomware-as-a-Service model splits the work into specialties: one group builds the tooling, another group handles initial access, affiliates run the intrusion, and everyone takes a cut.
Why Do Traditional Cybersecurity Strategies Fail?
A lot of security programs are still built around the concept of catching bad artifacts. That made sense when the threat was a malicious executable with a known signature, a suspicious email attachment, or a hostile IP address that clearly did not belong.
But when the attacker uses legitimate tools, valid credentials, and cloud services that the organization already depends on, traditional tools start to fall short.
Lack of visibility and siloed data is also another reason why modern multi-stage cybersecurity threats succeed. Most tools see just small parts of the attack and never the full picture. The EDR sees one behavior. The SIEM sees another. The firewall sees something else. Identity systems log a third or fourth signal.
But modern attackers do not operate as isolated alerts. They operate as sequences. They measure progress over time. Meanwhile, many SOCs, still work as per individual alerts and not by campaigns.
Make Smarter Security Investments—Faster
- Standardize vendor evaluation with a comprehensive RFI checklist.
- Compare platforms based on real-world detection, visibility, and response capabilities.
- Reduce risk by identifying gaps before deployment.
- Empower security leaders with actionable insights from NetWitness.
How should Cybersecurity Teams Handle Multi-stage Cyberthreats?
The shift from isolated EDR to unified TDR (Threat Detection and Response) approaches like NetWitness Platform works because it forces correlation across endpoints, identities, cloud services, and network activity.
Behavior-based detection matters because it focuses on what an attacker is doing, not just what a malicious file looks like.
Threat hunting matters because waiting for the perfect alert is not a strategy.
Threat intelligence has become more useful, too, but only when it is tied to actual operations. A threat report sitting unread in a folder is not intelligence. Intelligence becomes valuable when it changes what gets monitored, what gets prioritized, and what analysts actively go looking for. Automation is helpful when it is applied well.
IBM’s Cost of a Data Breach Report 2025 found that organizations using AI and automation extensively in security operations reduced breach lifecycle by 80 days and saved an average of $1.9 million per incident.
A unified platform with ML-based behavioral detection enables faster allowing analysts to spend more time on the signals that actually matter.
What Security Leaders Should Be Thinking About
The biggest mindset shift is simple: prevention still matters, but prevention alone is not a strategy anymore.
The stronger programs assume that, sooner or later, something will get in. That assumption changes the questions leadership asks. Not “Are the controls in place?” but “If an attacker got in this morning, how fast would the team know? How would they trace movement? What would containment look like in the first hour?”
A tool generating a huge alert volume is not necessarily performing well. A team that can find, understand, and contain an intrusion quickly is. Mean time to detect and mean time to respond say more about defensive maturity than raw alert counts ever will.
Vulnerability management needs to focus on attack paths, not just isolated CVEs. Identity protection needs to sit much closer to the endpoint and cloud monitoring than it did a few years ago. And detection engineering needs to be treated as a real discipline, not an afterthought squeezed in between escalations.
Conclusion
A virus twenty years ago was usually an event. Loud, visible, annoying, and often short-lived. A serious attack today is a process. It unfolds in stages. It blends in. It waits. It adapts. By the time the real damage shows up, the threat has already been underway for a while.
That is why older security habits keep underperforming. They were built to catch events. Modern cyber defense has to watch behavior, connect signals, and interrupt the attack before the final stage lands. That’s the kind of evolution needed in combating cyber threats.
Frequently Asked Questions
1. How have cyber threats become more advanced?
Modern adversaries design complex cyberattacks campaigns using AI to abuse legitimate tools, leverage identity compromise, and structure intrusions through stages in such a way that each step looks relatively harmless to avoid detection. They have become modular and behavior-driven.
2. What is the cyberattack lifecycle?
Cyberattacks usually go through the following phases in their lifecycle:
- Initial access
- Privilege escalation,
- Lateral movement
- Defense evasion,
- Exfiltration, encryption, or both.
3. What role does threat intelligence play in cybersecurity?
Threat intelligence helps teams understand who is likely to target the enterprises, what those actors tend to do, and where detection effort should go. Its value shows up when it is built into detection rules, hunting workflows, and response playbooks.
4. What industries are hit hardest by advanced threats?
Manufacturing, healthcare, financial services, government, transportation, and energy are consistently high-value targets because disruption in those sectors creates immediate pressure.
What to Look for in a Unified Security Platform
- Cut through tool sprawl with a practical evaluation framework.
- Compare platforms based on visibility, detection accuracy, and automation.
- Validate real-world performance across hybrid and cloud environments.
- Make confident, risk-aligned security decisions.