Key Takeaways
- Network Monitoring has shifted from an optional visibility tool to a foundational SOC capability.
- Cloud complexity has outpaced perimeter-based security models.
- SOC cloud monitoring depends on continuous, context-rich network telemetry.
- Network monitoring reduces blind spots, shortens MTTD and MTTR, and improves investigation quality.
- Network visibility in hybrid and SaaS-heavy environments is now directly tied to SOC accountability.
- Effective cloud security operations require integrated network detection and response.
Cloud adoption around the world and in businesses has been on the rise for all the right reasons. But it offers its own set of complex security challenges. That complexity has quietly shifted accountability to SOC. Therefore, network monitoring has become a core requirement for modern cloud security operations.
When incidents happen, leaders ask whether the SOC has visibility. Without sustained network visibility across the cloud security network, detection quality drops. Lateral movement hides within encrypted traffic. Ephemeral workloads disappear before logs are reviewed.
Network Monitoring now defines whether cloud cybersecurity programs are reactive or operationally resilient.
What Is Cloud Network Monitoring?
Cloud network monitoring is a subset of network monitoring. It involves continuous monitoring of traffic flows, connections, and communication patterns across the cloud. Cloud network monitoring is accountable for dynamic workloads, API-driven services, ephemeral containers, and encrypted east-west traffic.
Network monitoring enables visibility into how data moves within and between environments. It helps security teams understand:
- Who is communicating with whom
- Which services are exposed externally
- Where anomalous traffic patterns emerge
- How workloads interact inside the cloud security network
In modern cloud network and security models, the network is not a static pathway. SOC cloud monitoring leverages its dynamic telemetry to correlate behavior across endpoints, users, and infrastructure.
Without cloud network monitoring, threat detection becomes challenging. Logs show events, endpoints show symptoms, but only unified network visibility reveals attacker movement.
Why Has Cloud Network Monitoring Become A SOC Requirement?
Cloud network monitoring has become a SOC requirement because the operational reality of cloud cybersecurity has changed. The following factors make Network Monitoring foundational to SOC cloud monitoring:
1. Hybrid Networks Are the New Normal
Enterprises operate across on-premises data centers, public cloud providers, and SaaS platforms, and not just cloud or on-prem systems. Traditional monitoring is unable to cover such hybrid environments. Cloud network monitoring bridges the gaps by providing unified network visibility.
Without it, SOC teams investigate in silos. With it, they correlate activity across environments.
Result: Faster investigations and fewer blind spots.
2. Encrypted Traffic Hides Lateral Movement
Most cloud traffic is encrypted. Network monitoring collects metadata, flow records, and behavioral analytics to detect suspicious communication patterns even when payloads are encrypted.
Result: Cloud threat detection improves without breaking encryption models.
3. Ephemeral Workloads Demand Real-Time Telemetry
Containers and serverless functions may exist for minutes. Network monitoring captures traffic patterns as they occur, whereas other tools often lag. This ensures SOC cloud monitoring keeps pace with cloud-native architectures.
Result: Reduced Mean Time to Detect (MTTD).
4. SaaS Sprawl Creates Unmanaged Exposure
SaaS applications connect directly to the core enterprise environment. Network monitoring helps gain visibility into outbound and third-party communications that otherwise bypass traditional controls.
Result: Better control over shadow IT and data exfiltration pathways.
5. Alert Fatigue
SOC analysts are often overwhelmed by the large volume of alerts from fragmented tools. They lose crucial time investigating and correlating false positives and end up missing out on the actual threats. Cloud network monitoring solutions enrich alerts with context, communication patterns, peer relationships, and anomaly baselines that help them accelerate detection and response.
Result: Lower Mean Time to Respond (MTTR) and more confident triage decisions.
6. Perimeter-based Security Models Are Obsolete
In cloud cybersecurity, identity and workload relationships matter more than IP boundaries. Network Monitoring supports telemetry-driven security models where behavior, not location, defines trust.
Result: Stronger network security in cloud environments.
7. Cloud Security Operations Require Correlation
Effective cloud security operations rely on integrating endpoint, identity, and network detection and response. Network Monitoring strengthens this integration by serving as a central telemetry layer.
Result: Improved cross-domain investigations.
“In a hybrid world, visibility is often fragmented across disparate tools, leaving SOC analysts to piece together a puzzle with missing parts. True operational resilience isn’t just about collecting logs; it’s about mastering continuous, context-rich telemetry that follows a workload across containers, SaaS, or on-premises data centers. By centralizing this network telemetry with endpoint and log data, NetWitness ensures that lateral movement is no longer a blind spot, but a visible trail for decisive response.”
— Clemens Muller, Sales Engineer, NetWitness
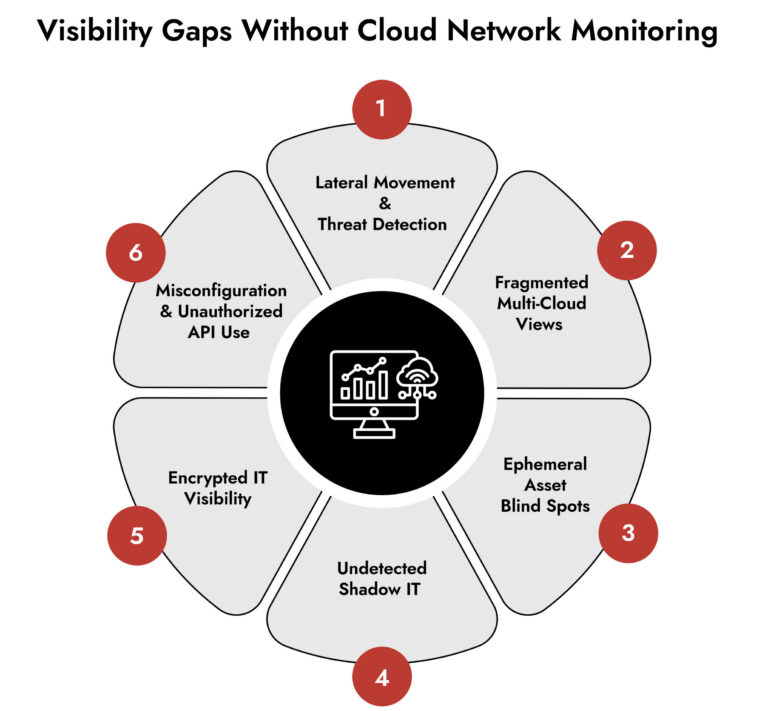
Impact of the Visibility Gaps That Exist Without Cloud Network Monitoring
Without cloud network monitoring, SOC teams operate with partial awareness.
- Lateral movement between workloads goes undetected because no single log source captures relationship changes comprehensively.
- Misconfigurations in cloud network and security policies come to light after exploitation. Network monitoring helps highlight unusual communication flows at an early stage.
- Lack of network visibility directly impacts incident investigations.
- Shadow pathways introduced by SaaS and third-party integrations go unnoticed.
The cumulative effect is operational strain. MTTD increases, MTTR expands, and analysts lose confidence in coverage. Cloud cybersecurity programs become reactive.
How NetWitness Helps?
NetWitness enables unified network detection and response across hybrid and cloud environments. It strengthens SOC cloud monitoring and enhances cloud threat detections by providing full network visibility and centralizing it.
It connects network telemetry with endpoint and log data, resulting in improved correlation, clearer incident narratives, and stronger network security in cloud environments.
NetWitness analyzes traffic metadata, behavioral anomalies, and communication patterns across the cloud security network to accelerate investigations.
Frequently Asked Questions
1. How Does Cloud Network Work?
Cloud network connects virtual machines, containers, serverless functions, and SaaS services through software-defined infrastructure. Instead of physical switches and routers, connectivity is managed via virtual networks, subnets, security groups, and routing policies.
Workloads communicate internally (east-west traffic) and externally (north-south traffic) through cloud-managed gateways and APIs. Identity and access controls influence network paths as much as IP configurations.
For security professionals, this means the cloud security network is programmable and dynamic. Resources scale up and down automatically. IP addresses change. Services integrate through APIs.
Network monitoring becomes essential because it tracks these dynamic connections continuously. It ensures SOC cloud monitoring reflects real-time infrastructure states rather than static configurations.
2. How Does Cloud Network Monitoring Support Threat Detection?
Cloud network monitoring supports threat detection by providing behavioral telemetry across the cloud cybersecurity environment.
Instead of relying solely on signatures, network monitoring observes communication patterns. It detects unusual peer relationships, abnormal data transfers, unexpected outbound connections, and deviations from established baselines.
In SOC cloud monitoring workflows, this telemetry enhances correlation. Network detection and response platforms combine flow data with endpoint and identity signals to build a complete incident picture.
This approach improves cloud threat detection in encrypted environments where payload inspection is limited. It also accelerates response because analysts understand movement paths immediately.
3. What challenges do SOC teams face without cloud network monitoring?
Without cloud network monitoring, SOC teams end up investigating without context. They miss out on the lateral movement and workload communications. These blind spots become critical and allow cyberthreats to exploit them.
4. How does cloud monitoring differ from traditional network monitoring?
Traditional network monitoring works within fixed boundaries and around fixed environment. Cloud environments are inherently flexible and dynamic. Hence, cloud monitoring focuses on behavioral analytics more than physical checkpoints. It requires continuous visibility into traffic flows, workload relationships, and communication patterns.
5. What features should SOC teams look for in a cloud network monitoring solution?
The main features of an effective cloud network monitoring solution are:
- Unified visibility
- Behavioral analytics
- Integration with broach SOC workflows
- Real-time telemetry
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.