How to Know if Your Security Log Management Software is Failing Your SOC?
- Your security log management software misses threats due to weak correlation and limited log analysis tools
- Slow searches and inefficient log monitoring delay incident response and increase risk exposure
- Rising costs from poor network log management make scaling unsustainable
- Compliance becomes harder without automated reporting and audit-ready security log management tools
- Lack of integrations prevents your stack from functioning as one of the best security log management solutions for SOC operations
Introduction
Most security teams don’t realize their log management security setup is the problem until it’s too late. Threats slip through. Alerts pile up. Investigations drag on. At some point, it stops being a tool and becomes a bottleneck.
That’s where software for managing security logs becomes relevant or should be. It is intended to serve as the basis for identifying threats, conducting investigations, and fulfilling compliance requirements. However, not every security log management tool is designed to handle the scale, speed, and intricacies of the current threat environment.
If your team is already feeling the pressure, the last thing required is log management software that increases workload instead of alleviating it. 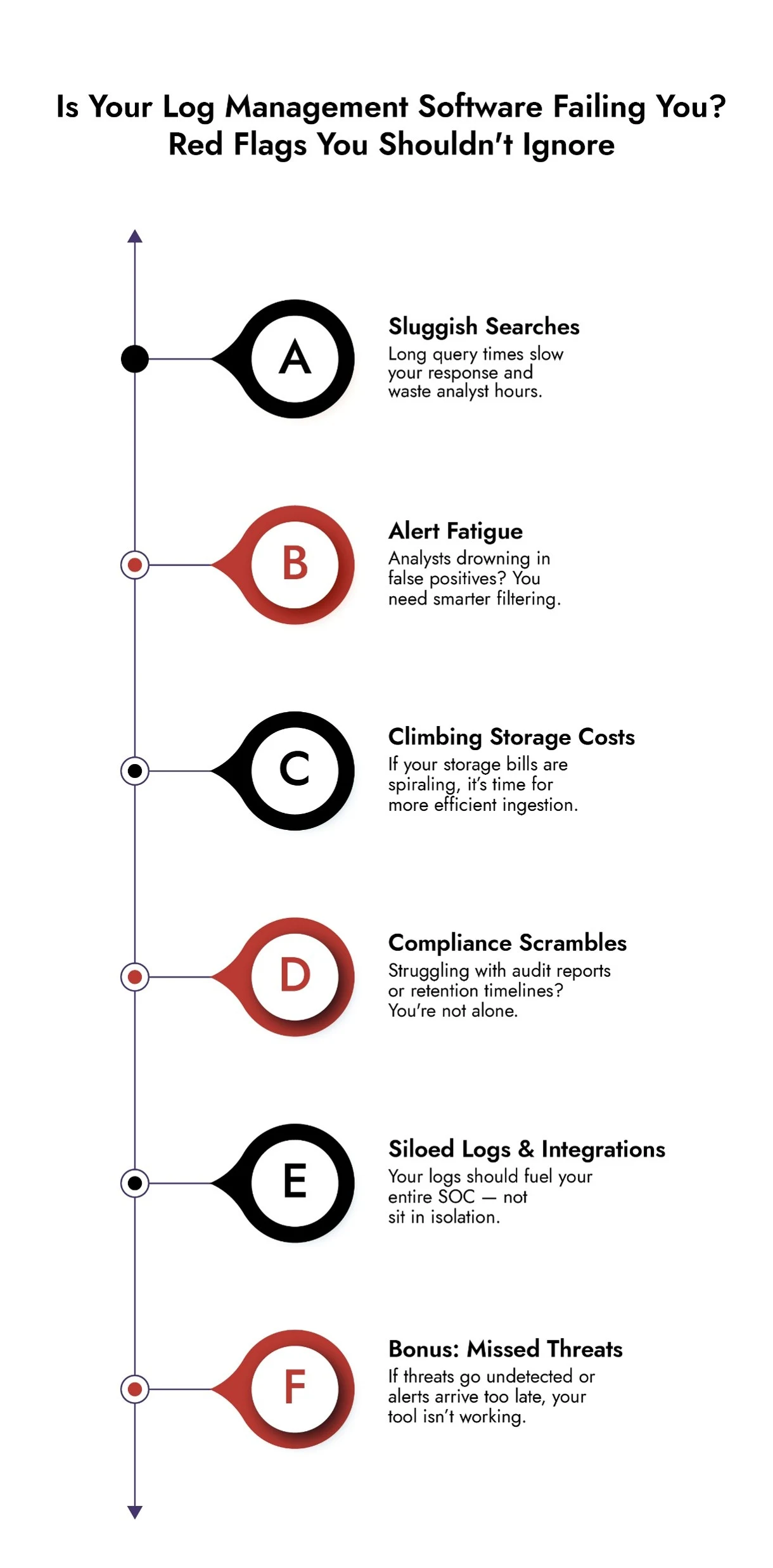
What is Security Log Management Software? Why it Matters for SOC Operations
Security log management tools gather and consolidate information from various areas of your IT infrastructure. It’s crucial for identifying risks, carrying out inquiries, and ensuring adherence.
Nonetheless, not all solutions can manage the size or intricacy of contemporary hybrid networks. The appropriate security log management tools ought to provide more than just log storage; they must facilitate log monitoring, offer profound insights with log analysis tools, and enhance network log management throughout distributed settings.
Here are five obvious indicators that your security log management system needs to be retired.
1. If You’re Missing Threats, Your Log Monitoring is Broken
Log tools are only useful if they surface the right signals. But outdated security log management software often lacks the ability to correlate logs across systems, detect anomalies, or highlight suspicious behavior in real time.
It’s not enough to collect logs anymore, you need context. You need to know about alerts that matter. And sometimes the problem isn’t just the tool, it’s whether you’re fully deployed and collecting all the data you need. Gaps in coverage mean gaps in visibility.
Modern platforms combine log monitoring with advanced log analysis tools to cut through noise and zero in on actual threats before they escalate.
If your current log management software only shows you what happened after the fact, you’re already behind.
2. Slow Log Searches and Delayed Response Times are Holding You Back
Time is everything in incident response. If your team has to wait minutes or worse, hours, for search results, it’s not just frustrating. It’s dangerous.
Slow platforms, limited query capabilities, and missing context all delay response. That’s when attackers get time to move laterally or dig deeper into your systems.
Up-to-date SIEM log software offers fast search, enriched data, and guided investigations that make response workflows faster and sharper.
If your analysts must export logs just to make sense of what happened, the tool is not working for them.
3. Rising Costs from Inefficient Network Log Management
More logs. More storage. More bills. It’s a common trap. As your organization grows, so does your data volume and suddenly, your security log management software can’t keep up without blowing the budget.
With cloud SIEMs, it’s not just storage – compute costs spike during major incidents when analysts run heavy queries, leading to unpredictable expenses.
Legacy tools often force you to retain everything or worse, guess what to keep. And as cloud workloads expand, so do ingestion fees. Newer platforms optimize log management using smart filtering, compression, and scalable architectures designed for modern SOC needs.
If you’re deleting logs to save space or holding off on ingesting new sources to cut costs, you’re sacrificing visibility. That’s a risk you can’t afford.
4. Compliance Failures Due to Weak Log Monitoring and Reporting
If every audit feels like a fire drill, you’re not alone. Meeting today’s compliance standards takes more than just storing logs. You need retention rules, access controls, audit trails and fast reporting, none of which should require hours of manual work.
Older log management security tools often lack the flexibility or automation to make this easy. That leads to late reports, missed requirements, and avoidable risk.
Modern security log management platforms automate compliance workflows, create audit-ready reports in seconds, and make it easy to prove you’re doing what the regulators expect. If you’re barely scraping through audits, or dreading the next one, you need something better.
5. Integration Issues? Your Security Log Management Software Is Working in a Silo
SIEMs don’t work in isolation. They need to integrate with the rest of your security stack: EDR, NDR, firewalls, identity tools, threat intel feeds, and orchestration platforms.
If your security log management software needs constant custom scripts or manual workarounds to connect with other tools, it’s not a system, it’s a silo.
That lack of interoperability slows down everything from investigations to reporting. It also prevents you from building automated, efficient workflows across your stack.
Modern SIEM log software uses open APIs, modular architecture, and prebuilt integrations to fit into any environment. If connecting your tools feels like duct taping a puzzle together, your current setup is due for retirement.
Simplify Log Management and Threat Detection with NetWitness® Logs
-Centralize and analyze logs from across your environment in one platform.
-Detect threats faster with real-time visibility and automated correlation.
-Reduce noise through advanced filtering and context-driven analytics.
When Your SOC Team Struggles with Log Monitoring, it’s Time to Upgrade
Ask your SOC team what they think of the current system. If the words “clunky,” “slow,” “incomplete,” or “useless” come up, it’s not just annoying, it’s hurting your defense.
Good security log management software should support your team, not frustrate them. It should reduce alert fatigue, surface meaningful insights, and simplify the day-to-day work of security analysts.
When the tool becomes something your team avoids or works around, it’s already failed.
How NetWitness Delivers Advanced Security Log Management for Modern SOCs
If a number of these sound familiar, perhaps it’s time to think about a stronger foundation.
NetWitness offers a new approach to log monitoring, network log management, and log analysis tools. It helps you detect threats faster, investigate smarter, and stay ahead of compliance requirements. Our security log management software gives you complete visibility across your entire infrastructure, correlates data in real-time, and integrates with the rest of your security tools.
From enhanced threat intelligence to automation, NetWitness helps you eliminate the blind spots and bottlenecks your current solution can’t solve.
Want to see the power of NetWitness for yourself? Schedule a demo of NetWitness in action, or learn more about the benefits of Evolved SIEM in our datasheet.
Frequently Asked Questions
1. What is security log management software?
Security log management software collects, stores, and analyzes log data from across your IT environment. It enables effective log monitoring, supports investigations, and helps organizations meet compliance requirements.
2. Which security log management tools meet standards?
The best security log management tools meet standards like GDPR, NIS2, ISO 27001, and PCI-DSS by offering secure storage, audit trails, role-based access, and automated compliance reporting.
3. Which log management cyber security solutions detect threats fastest?
The best security log management solutions for SOC operations combine real-time log monitoring, behavioral analytics, and advanced log analysis tools to detect and respond to threats quickly.
4. Why can’t my legacy SIEM keep up with cloud log volumes?
Legacy systems struggle with scalability, ingestion limits, and high processing costs. Modern network log management solutions are built for cloud-scale environments with elastic storage and distributed processing.
5. Why is scalability important in log management software?
Scalability ensures your security log management software can handle increasing data volumes without slowing down performance, increasing costs, or creating visibility gaps in your SOC.
Choose the Right SIEM with Confidence
Evaluate vendors using a comprehensive, expert-built checklist.
Identify must-have SIEM features for complete visibility and faster detection.
Compare capabilities to ensure scalability, automation, and integration.
Make informed decisions with NetWitness’ proven SIEM guidance.