How Visibility is the Key to Making or Breaking Cybersecurity Solutions?
The great majority of cyber security solutions run perfectly well and never fail to operate but without any context whatsoever. Without having enough information, threats will not be detected, no investigation can take place, and any response to cyber incidents would be only reactionary. Having a strong cyber security visibility solution unifies network traffic, endpoint activities, and user identity into one package. That is how threat detection and cyber risk assessment, along with an efficient SOC can occur.
Introduction
Here’s the uncomfortable truth: most cybersecurity solutions don’t fail due to lack of investment. They fail because teams operate with blind spots.
Security stacks have grown deeper, not smarter. Alerts flood dashboards, logs pile up, and teams still struggle to answer basic questions: What happened? Where did it start? What’s impacted? Without cybersecurity visibility, even the most advanced tools turn into noise generators.
What this really means is simple. If you can’t see your environment clearly, you can’t defend it effectively.
Visibility is not another capability layered into cybersecurity solutions. It’s the foundation that determines whether everything else works.
Why Cybersecurity Solutions Depend on Visibility First
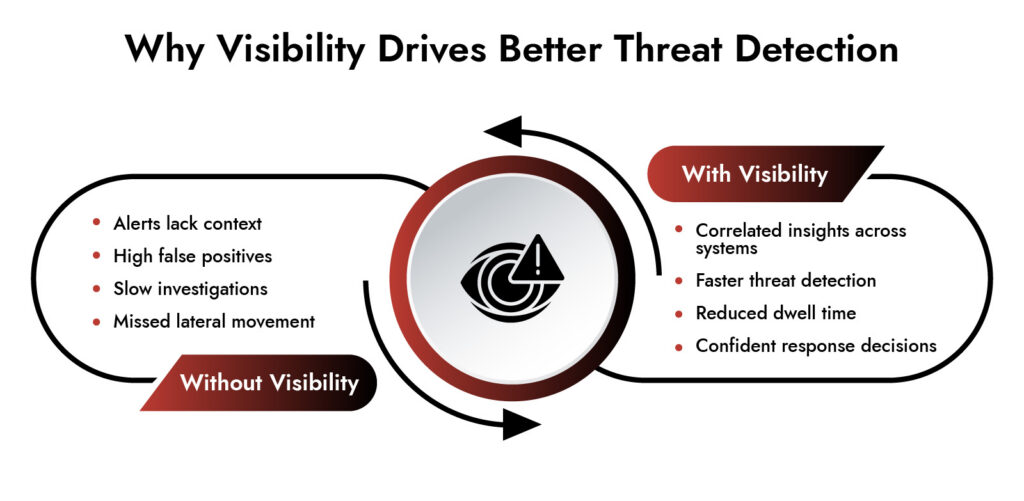
Effective cybersecurity solutions rely on accurate, real-time data across systems. Without visibility, detection, investigation, and response all degrade.
Security teams don’t struggle with lack of data. They struggle with fragmented data.
Modern enterprise environments span:
- On-prem infrastructure
- Multi-cloud environments
- Remote endpoints
- OT and IoT systems
Each generates signals. But signals without correlation don’t create insight. According to IBM Security, the average cost of a data breach reached $4.45 million in 2024. A major contributor? Delayed detection caused by poor visibility.
Cybersecurity solutions need visibility to:
- Correlate events across environments
- Detect lateral movement early
- Reduce false positives
- Enable faster incident response
Without this, teams operate reactively. And attackers move faster than response cycles.
Cybersecurity Visibility: What it Really Means in Practice
Cybersecurity visibility is the ability to observe, analyze, and understand all activity across your digital environment in real time. It’s not just about collecting logs. It’s about context.
True visibility answers:
- Who accessed what system?
- What changed?
- Where did traffic originate?
- How did an attacker move?
This is where most cybersecurity solutions fall short. They capture fragments, not the full story.
A mature visibility strategy includes:
- Network traffic visibility for deep packet inspection.
- Endpoint telemetry for behavioral insights.
- Identity tracking across access points.
- Cloud workload monitoring.
When combined, these create a unified view. That’s when detection becomes proactive, not reactive.
Network Visibility Cybersecurity: The Missing Link in Threat Detection
Network visibility cybersecurity focuses on monitoring and analyzing traffic across networks to identify suspicious behavior. It remains one of the most underutilized strengths in modern cybersecurity solutions.
Why? Because encrypted traffic and distributed architectures make inspection harder. But here’s the reality: attackers still leave traces in network behavior.
According to Cybersecurity and Infrastructure Security Agency advisories (2024), lateral movement and command-and-control communications remain key indicators of compromise.
Network traffic visibility enables:
- Detection of unusual communication patterns,
- Identification of data exfiltration attempts.
- Tracking attacker movement across systems.
Example: An attacker compromises a user endpoint. Endpoint tools flag nothing unusual. But network telemetry shows abnormal outbound traffic to a suspicious domain. That’s your early warning. Without network visibility cybersecurity, that signal disappears.
Why Modern Attacks Target What You Can’t See
Recent 0-day attacks aren’t targeting endpoints. They’re hitting systems where visibility is weakest.
Think:
- VPNs, firewalls, and edge devices
- OT/IoT systems
- Assets where EDR can’t be deployed
- Environments where logs are limited or can be disabled
This breaks traditional assumptions behind many cybersecurity solutions. No agent. No reliable logs. No endpoint telemetry.
According to 2024–2025 advisories from NIST and CISA, attackers are increasingly exploiting these blind zones because they sit outside standard detection coverage.
Why Network Traffic Visibility Becomes Critical – When everything else fails, the network still tells the story.
Network traffic visibility enables:
- Detection of anomalous outbound connections
- Identification of command-and-control activity
- Tracing lateral movement from unmanaged devices
Example: A firewall is compromised via a 0-day. No logs flag it. No agent detects it.
But network traffic reveals unusual external communication. That’s your signal.
Without strong Network visibility cybersecurity, this activity goes unnoticed.
What This Means for Cybersecurity Solutions – Modern cybersecurity solutions must account for what cannot be instrumented.
That means:
- Prioritizing agentless visibility
- Relying on network-level detection
- Correlating signals beyond endpoints and logs
Because the next breach is more likely to start where you have the least visibility—not the most controls.
Achieve NIS2 Compliance with Confidence
- Meet NIS2 requirements across IT and OT environments
- Detect and respond to threats in real time
- Streamline compliance reporting and audit readiness
- Reduce risk with continuous monitoring and analytics

Cyber Risk Assessment Starts with What You Can See
You cannot assess what you cannot observe. Every cyber risk assessment depends on accurate visibility into assets, vulnerabilities, and activity.
Most organizations still rely on:
- Periodic scans
- Static asset inventories
- Compliance checklists
These approaches don’t reflect real-time risk.
Modern cybersecurity solutions use visibility-driven risk assessment:
- Continuous monitoring of asset behavior.
- Identification of shadow IT.
- Real-time vulnerability exposure tracking.
According to National Institute of Standards and Technology, continuous monitoring is essential for effective risk management.
Without visibility:
- Critical assets remain untracked
- Misconfigurations go unnoticed
- Risk prioritization becomes flawed
Visibility turns risk assessment into an ongoing process, not a quarterly exercise.
Security Operations Center Performance Hinges on Visibility
A security operations center is only as effective as the visibility it operates on. SOC teams don’t need more alerts. They need clarity.
Poor visibility leads to:
- Alert fatigue
- Slow triage
- Incomplete investigations
Strong visibility enables:
- Faster root cause analysis
- Better incident prioritization
- Reduced mean time to respond (MTTR)
Organizations with integrated visibility reduce incident response time by up to 40%. That’s not a tooling advantage. That’s a visibility advantage.
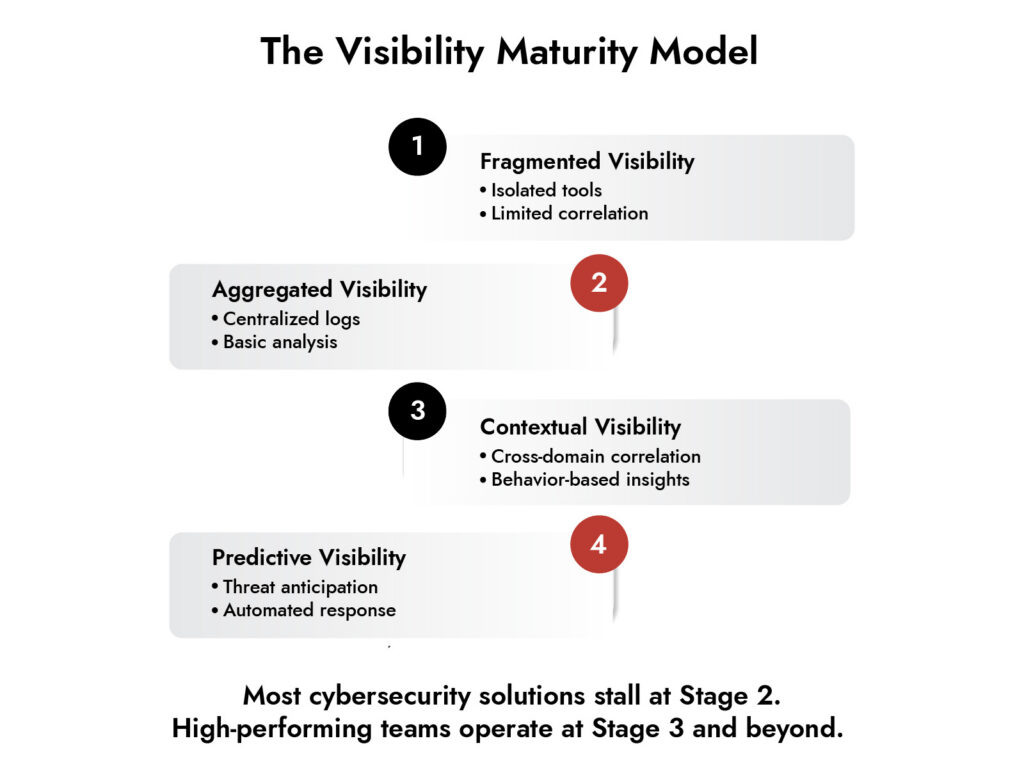
How Modern Cybersecurity Solutions Build Visibility
Strong cybersecurity solutions don’t treat visibility as a feature. They design around it.
This requires integration across:
- Network data
- Endpoint telemetry
- Logs and events
- Threat intelligence
Key capabilities include:
- Deep packet inspection for network traffic visibility.
- Real-time analytics for threat detection.
- Behavioral modeling across users and systems.
- Automated correlation across environments.
Example: A phishing attack leads to credential theft. Endpoint signals look normal. Identity logs show unusual login behavior. Network traffic shows data movement. Individually, these signals seem harmless. Together, they expose a breach. That’s visibility in action.
Where NetWitness Fits into Visibility-Driven Cybersecurity Solutions
NetWitness approaches cybersecurity solutions with visibility at the core.
Instead of relying on isolated signals, it provides:
- Deep network visibility cybersecurity through packet capture and analysis.
- Endpoint and log visibility for full context.
- Unified threat detection across environments.
Its strength lies in reconstructing attacker activity:
- Full session visibility
- Timeline reconstruction
- Forensic-level investigation
For organizations managing hybrid IT and OT environments, this matters. In operational technology environments, visibility becomes even more critical. You cannot patch systems easily. You cannot afford downtime. Detection must happen early.
NetWitness enables:
- Monitoring of industrial protocols.
- Detection of anomalies in OT networks.
- Integration into the broader security operations center.
This aligns visibility with operational continuity, not just security posture.
The Cost of Ignoring Visibility in Cybersecurity Solutions
Ignoring visibility doesn’t just slow detection. It increases impact.
According to reports:
- 74% of breaches involve human elements.
- Many go undetected for weeks or months.
Why? Lack of visibility across systems.
Common consequences:
- Delayed incident response
- Incomplete investigations
- Regulatory exposure
- Business disruption
Strong cybersecurity solutions mitigate these risks by ensuring every action leaves a trace and every trace is analyzed.
Conclusion
Visibility is not optional. It’s the baseline. Every investment in cybersecurity solutions either strengthens visibility or adds noise. The difference shows up in detection speed, response quality, and business resilience.
Organizations that prioritize visibility don’t just respond faster. They understand their environment better. And that changes everything. If your current approach feels reactive, the issue isn’t effort. It’s visibility.
Frequently Asked Questions
1. What is cybersecurity visibility?
In the world of cybersecurity, visibility means being able to watch and analyze what happens on various endpoints, networks, and systems in real-time. Good cybersecurity solutions depend on visibility to function efficiently.
2. What types of visibility are important in cybersecurity?
The types of visibility that are most important in justification of security are network, endpoint, identity tracking; and the cloud. Together these types of visibility provide a more complete view of how to detect and respond to threats.
3. How do organizations achieve full cybersecurity visibility?
Complete visibility requires the use of cybersecurity solutions that utilize logs, network traffic visibility, and behavior analytics. Continuous monitoring and centralized analysis are necessary components of this strategy.
4. How does visibility support IT/OT environments?
Visibility allows identifying abnormal behavior in both IT and OT infrastructures without interfering with any processes. It facilitates threat detection in those environments where patches or downtimes are unacceptable.
5. What cybersecurity solutions help protect against ransomware attacks?
Good cybersecurity solutions involve visibility-based detection technologies such as network traffic visibility, endpoint monitoring, and behavioral analysis. This way, ransomware can be detected early and isolated.
6. Why is network visibility critical for threat detection?
The use of cybersecurity solutions with network visibility allows discovering communication patterns leveraged by cybercriminals. Such tools can discover lateral movements, C&C communications, and data exfiltration.
Uncover the Top Threats Shaping Industrial Network Security
- Emerging threats targeting industrial control systems (ICS)
- Ransomware and supply chain risks in OT environments
- Hidden attack paths across converged IT/OT networks
- Real-world trends impacting critical infrastructure security