What You Need to Know Before Building a SOC Team?
Merely implementing more technologies into an already existing SOC will not create an effective SOC. What makes an SOC effective is clearly laying out precisely defined roles/duties for the SOC. Every single SOC role (Tier 1 analysts to Incident Responders) must be aligned with the speed at which alerts can be detected; the depth at which an investigation will be conducted; and the outcome of the response. Teams who clearly define the roles/responsibilities of its members will decrease response times; increase visibility of potential threats and prevent overall operational chaos. If your SOC is having difficulty managing a large volume of alerts due to fatigue or an inability to quickly respond, the problem is most likely the structural design of the SOC rather than the technical design of the SOC.
Introduction
Most organizations do not focus on security as a top priority. As a result, they often lack the tools needed for effective cybersecurity measures. However, many organizations have failed at their security operations center roles and responsibilities because there is a lack of alignment and clarity around them.
The same can be said of hackers when they attempt to take advantage of flaws from within the SOC; they will do this as quickly as possible by exploiting vulnerabilities, tracking potential vulnerabilities, and taking advantage of any delay in the SOC responding to the alert in question.
To develop an efficient SOC team, first, we need to establish clear lines of ownership, enhance the skills of each team member, and align our SOC roles and responsibilities with our organizational goals, so there is a distinction between having “noise” from an event or alerts from true actionable intelligence extracted from those same events.
Why Security Operations Center Roles and Responsibilities Define SOC Success
Clear security operations center roles and responsibilities ensure that every alert, anomaly, and incident moves through a defined lifecycle without friction. Without structure, teams face:
- Alert fatigue with no prioritization
- Delayed incident response
- Miscommunication during escalations
- Gaps in accountability
According to recent guidance from NIST (2024 updates to incident handling frameworks), organizations with defined incident ownership reduce response times by up to 40%. That’s not a tooling issue. That’s a people and process issue.
What this really means is simple: your SOC maturity depends less on how many tools you deploy and more on how clearly responsibilities are assigned and executed.
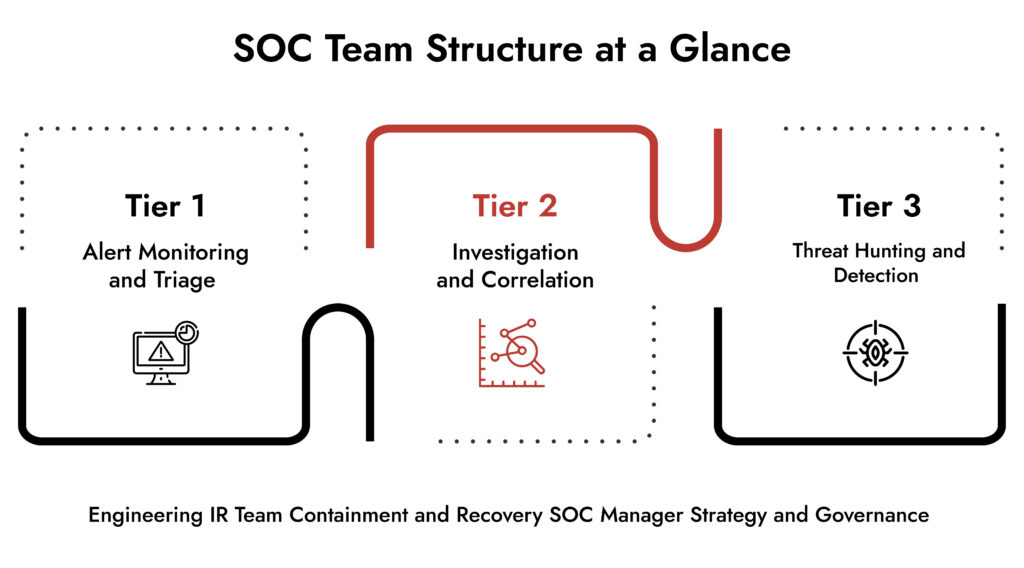
Security Operations Center Roles and Responsibilities Across the SOC Team
A high-functioning SOC relies on layered roles. Each role supports detection, investigation, and response.
Tier 1 Analysts: First Line of Defense
They monitor alerts and validate threats. They separate noise from signals. SOC responsibilities include:
- Continuous security monitoring
- Alert triage using SIEM dashboards
- Initial incident classification
- Escalation based on severity
They don’t solve everything. They ensure the right issues reach the right experts quickly.
Tier 2 Analysts: Investigation and Correlation
They dig deeper. They connect events across systems. SOC team roles and responsibilities include:
- Threat validation and enrichment
- Log correlation across endpoints and networks
- Root cause analysis
- Supporting containment actions
This layer transforms alerts into actionable intelligence.
Tier 3 Analysts: Threat Hunters and Experts
They don’t wait for alerts. They proactively hunt threats. Key responsibilities:
- Advanced threat hunting
- Malware analysis
- Adversary behavior mapping
- Detection rule development
They strengthen soc network security by identifying threats that evade automated detection.
Incident Response Team Roles
When an incident escalates, the incident response team roles take over.
Core responsibilities include:
- Containment and eradication
- Forensic investigation
- Communication with stakeholders
- Recovery planning
This team defines how quickly the organization recovers from an attack.
SOC Manager: Strategic Oversight
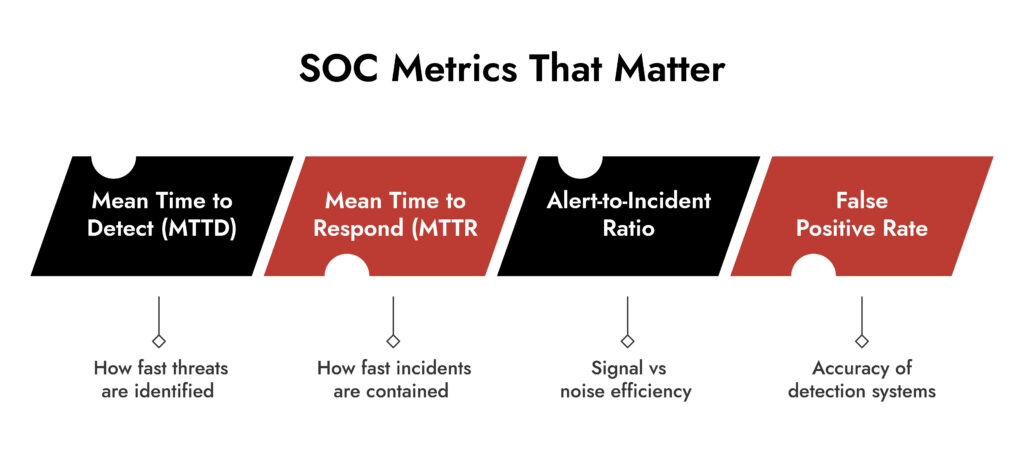
The SOC manager aligns operations with business risk. Security operations center roles and responsibilities at this level include:
- Defining KPIs (MTTD, MTTR)
- Managing team performance
- Overseeing incident response workflows
- Ensuring compliance alignment
They ensure the SOC doesn’t just operate, but evolves.
Skills That Define a High-Performance SOC Team
Technology alone doesn’t create outcomes. Skills do. An effective SOC team requires a blend of technical depth and operational awareness.
Core Technical Skills
- Log analysis and event correlation
- Network traffic analysis for SOC network security
- Threat intelligence interpretation
- Endpoint and malware analysis
Operational Skills
- Incident prioritization
- Communication during crises
- Documentation and reporting
- Decision-making under pressure
Advanced Capabilities
- Threat hunting methodologies
- Automation and scripting
- Detection engineering
- Use of security operations center tools for orchestration
A 2025 industry report from global cybersecurity agencies highlights that SOC teams with automation and threat hunting capabilities reduce breach impact by over 30%. .
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.
Security Operations Center Tools That Enable SOC Responsibilities
Tools don’t replace analysts. They amplify them. Modern SOCs rely on integrated platforms to execute security operations center roles and responsibilities efficiently. Core Tool Categories
1. SIEM Tools
- Aggregate logs and generate alerts
- Enable real-time security monitoring
2. SOAR Platforms
- Automate repetitive tasks
- Standardize incident response workflows
3. Network Detection and Response (NDR)
- Provide deep visibility into network behavior
- Strengthen soc network security
4. Endpoint Detection and Response (EDR)
- Monitor endpoint activity
- Enable rapid containment
5. Threat Intelligence Platforms
- Enrich alerts with contextual data
- Improve detection accuracy
The key is integration. Disconnected tools create blind spots. Integrated systems create clarity.
Security Operations Team Structure: Centralized vs Distributed Models
There’s no one-size structure. But the model must align with operational goals.
Centralized SOC
- Single location
- Standardized processes
- Easier governance
Distributed SOC
- Regional teams
- 24/7 coverage
- Faster localized response
Hybrid SOC
- Combines both
- Central oversight with distributed execution
Most enterprise organizations now adopt hybrid models to balance control and responsiveness.
Building an Effective Incident Response Capability
An SOC without strong incident response is incomplete.
Effective response depends on:
- Predefined playbooks
- Clear escalation paths
- Regular simulation exercises
- Integration with SIEM tools and detection systems
NIST’s latest incident response guidelines emphasize continuous testing. Organizations that simulate attacks regularly respond faster and recover more efficiently.
Where NetWitness Fits into Modern SOC Operations
A SOC needs visibility across networks, endpoints, and logs. That’s where platforms like NetWitness play a critical role.
NetWitness enables:
- Deep packet inspection for advanced threat detection
- Unified visibility across environments
- Real-time analytics for faster incident response
- Integration with security operations center tools for streamlined workflows
It supports the execution of security operations center roles and responsibilities by reducing blind spots and improving investigative depth. This isn’t about adding another tool. It’s about enabling analysts to see what others miss.
Conclusion
Building an effective SOC team requires clarity, discipline, and continuous improvement. When security operations center roles and responsibilities are clearly defined, teams move faster, respond better, and reduce risk more effectively.
Technology supports the mission. People execute it. Structure makes it scalable. If your SOC still feels reactive, the answer isn’t more alerts. It’s better alignment. Start by redefining roles. Everything else follows.
Frequently Asked Questions
1. What are the top SOC team management platforms?
Leading platforms include SIEM tools, SOAR systems and integrated detection systems that support security monitoring, automation and incident management. The best platforms provide a unified view of all three areas of network, endpoint and log data.
2. Which companies offer SOC team outsourcing services?
There are global cyber security vendors that offer managed services for SOC as well as cybersecurity (MSSP) providing Managed Service Portfolio (MSP) vendor also offer Managed Service Providers (MSPs) for a globally available MSP SOC team. This typically occurs with a 24 hours per day, seven days per week (24/7) SOC monitoring provided. The MSSPs also typically provide 24/7 incident response services and access to their global threat intelligence network (GTI) which is used to help supplement/enhance the existing operational functions/workload of internal SOC team members’ functions.
3. How to build an effective SOC team for cybersecurity monitoring?
Begin by identifying the securitized operations centre roles within the cybersecurity program to define the teams’ attributes to perform detection and response business processes. Train the team and acquire the SOC tools to perform their business objectives effectively, and continuously evaluate the team’s performance using detailed metrics for monitoring all aspects of SOC.
4. How to build an effective incident response plan for a SOC?
Define the Incident Response Team Roles Clearly and develop Playbooks for the incidents to respond in common scenarios as defined in SOPs. The Response Process/Workflow should also be integrated into the Security Information and Event Management (SIEM) Tools that provide the necessary functionality for the Response Process and have clearly established communication protocols for each of the workflows and processes within the SOC environment.
5. What skills are essential for a SOC analyst role?
SOC analysts need skills in log analysis and threat detection. They also need knowledge of soc network security. They must handle incident response situations under pressure. Advanced roles require threat hunting and scripting capabilities.
6. How much does it cost to hire a managed SOC team service?
The costs associated with using Managed SOC services can vary depending on your organization’s size as well as what type of service you need from them and how long per week would you prefer them to work. Pricing for managed SOC service usually starts around high five figure amount annually for basic monitoring (as previously mentioned) and go considerably higher than that for larger-scale full SOC support which includes incident response support and proactive threat hunting capabilities.
What to Look for in a Unified Security Platform
- Cut through tool sprawl with a practical evaluation framework.
- Compare platforms based on visibility, detection accuracy, and automation.
- Validate real-world performance across hybrid and cloud environments.
- Make confident, risk-aligned security decisions.