What is ransomware?
Ransomware is a type of malicious software designed to block access to systems or encrypt files, preventing users from accessing their data. Once the attack is executed, cybercriminals demand a ransom payment in exchange for restoring access.
Modern ransomware attacks go beyond simple encryption. Attackers often gain access to systems first, move across the network, and steal sensitive data before launching the attack. They then use this data as leverage, threatening to leak it if the ransom is not paid.
Because these attacks unfold in multiple stages, early detection and response are critical to minimizing damage.
Introduction
Ransomware has become one of the most persistent cybersecurity threats facing enterprises. The scale of the problem is difficult to ignore. Recent research shows that 78% of organizations were hit by ransomware in the past year, highlighting how widespread and disruptive these attacks have become.
Yet ransomware rarely begins with encryption. In most incidents, attackers are already inside the environment long before files are locked or ransom notes appear. The intrusion often starts quietly with a compromised credential, a phishing email, or a vulnerable service exposed to the internet.
From there, attackers explore the network. They collect credentials, move laterally between systems, and identify critical infrastructure such as domain controllers, file servers, and backup systems. Only after the environment is fully mapped do they deploy ransomware across multiple systems at once.
This is why traditional malware-focused defenses often fail. By the time the ransomware payload is executed, the attacker has already completed most of the intrusion.
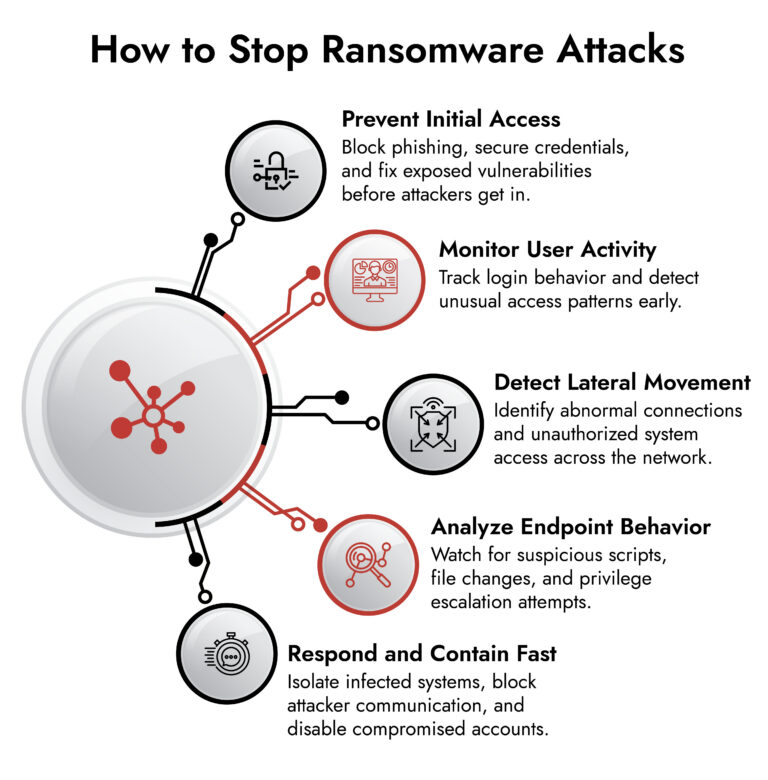
Stopping ransomware requires detecting the behaviors that appear earlier in the attack lifecycle. Security teams must identify suspicious authentication activity, unusual network communication, privilege escalation attempts, and lateral movement before encryption occurs.
NetWitness helps organizations achieve this through a unified security platform that combines network detection, endpoint visibility, log analytics, behavioral analytics, and automated response. Instead of analyzing isolated alerts, the platform correlates activity across the environment to reveal the full attack chain.
The result is a practical unified ransomware defense strategy that enables earlier ransomware detection, faster investigation, and effective containment before attackers can cause large-scale disruption.
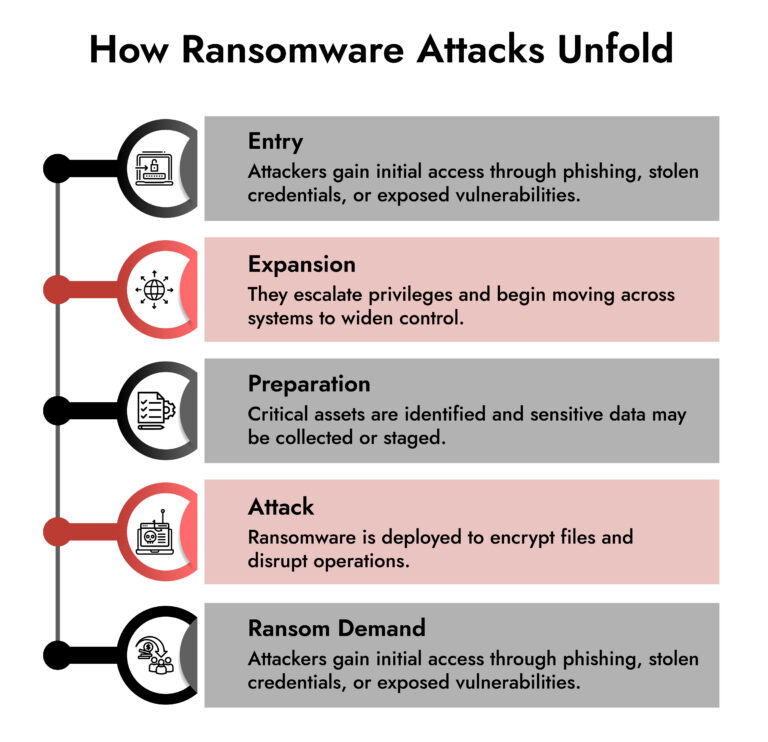
How Ransomware Works: The Modern Attack Lifecycle
To understand effective ransomware threat detection and response, it helps to look at how modern ransomware campaigns actually unfold. Most attacks follow a consistent sequence of stages, and each stage leaves behind observable signals.
Initial Access
The attack begins with a foothold inside the organization’s environment. This access may come from several different entry points. Phishing emails remain one of the most common methods. A malicious attachment or link can install a lightweight loader that gives attackers remote access to the compromised system. In other cases, attackers exploit exposed services such as Remote Desktop Protocol or unpatched vulnerabilities in internet-facing applications.
Credential compromise is another frequent entry point. Password reuse, leaked credentials, or brute-force attempts can allow attackers to log in directly to enterprise systems. At this stage the attacker’s priority is stealth. Their goal is to establish a persistent presence without triggering security alerts.
Privilege Escalation
After gaining initial access, attackers begin expanding their control. This often involves obtaining higher-level privileges that allow them to access additional systems and resources.
Credential harvesting techniques are commonly used during this phase. Attackers may dump credentials from memory, capture cached passwords, or exploit system vulnerabilities to obtain administrative privileges. Once attackers gain access to privileged accounts or domain-level credentials, they can move more freely across the environment.
Lateral Movement
Lateral movement allows attackers to explore the network and identify valuable systems. Using legitimate administrative tools, they connect to additional endpoints and servers, often blending into normal administrative activity.
During this phase, attackers may access file servers, database systems, or backup infrastructure. They may also scan the network to understand system relationships and identify security controls.
Lateral movement typically generates subtle indicators such as unusual authentication patterns, unexpected remote connections between systems, and administrative actions occurring outside normal operating hours.
Data Exfiltration
Many modern ransomware groups now steal sensitive data before launching encryption. This tactic, often referred to as double extortion, gives attackers additional leverage. If the victim refuses to pay, the attackers threaten to publish the stolen data. Large outbound data transfers or unusual file access patterns often occur during this phase.
Ransomware Deployment
The final stage is the coordinated execution of ransomware across multiple systems. Before encryption begins, attackers frequently attempt to disable security tools, delete backups, and ensure they maintain control of key infrastructure.
Once ransomware is deployed, encryption spreads rapidly across endpoints and servers. At this point the organization may experience immediate operational disruption. Detecting the attack before this stage is critical for effective ransomware mitigation.
Why Ransomware Detection Is Difficult for Many Organizations
Despite significant investment in security tools, many organizations still struggle with early ransomware detection. Several factors contribute to this challenge.
Attackers Use Legitimate Administrative Tools
Ransomware operators frequently rely on tools that are already present in enterprise environments. Utilities such as PowerShell, Windows Management Instrumentation, and Remote Desktop Protocol are commonly used by administrators. When attackers use these tools, their activity may appear legitimate unless it is analyzed in the broader context of network and user behavior.
Security Data Is Often Fragmented
Indicators of ransomware activity are rarely visible within a single tool. Network monitoring systems may detect suspicious traffic, while endpoint tools record abnormal process behavior and authentication logs reveal unusual login activity. If these signals remain isolated, security teams may fail to recognize the attack chain.
Attacks Move Faster Than Manual Investigations
Once attackers obtain elevated privileges, ransomware can spread quickly across an environment. Security teams relying on manual investigations may struggle to keep up with the pace of the attack.
These challenges highlight the importance of a unified ransomware defense approach that correlates signals across multiple security layers.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security
How NetWitness Enables Unified Ransomware Defense
NetWitness addresses ransomware threats by combining multiple detection and investigation capabilities within a single platform. Instead of treating network, endpoint, and log data as separate sources, the platform correlates them to reveal attacker behavior.
The platform integrates several key capabilities that support ransomware threat detection and response.
Network Detection and Response provides visibility into network communications and attacker infrastructure.
Endpoint Detection and Response monitors system behavior on individual devices.
SIEM analytics collect and correlate security logs from across the environment.
User and Entity Behavior Analytics identify abnormal activity associated with compromised accounts.
These capabilities work together to detect ransomware activity early and support effective response.
Detecting Early Indicators with Network Detection and Response
Network traffic often reveals attacker activity before ransomware is deployed. NetWitness Network Detection and Response continuously analyzes network communications to identify suspicious patterns.
The platform can detect command-and-control traffic associated with malware infections. It can also identify unusual DNS requests, unexpected outbound connections, or abnormal encrypted communications that may indicate hidden malware activity.
Because NetWitness captures full network packets and metadata, analysts can reconstruct communication sessions and examine exactly how attackers interacted with systems.
This network-level visibility helps organizations identify compromised systems and improve ransomware detection during the early stages of an attack.
Identifying Malicious Behavior on Endpoints
While network monitoring reveals attacker communication, endpoint telemetry shows what attackers are actually doing inside systems.
NetWitness Endpoint Detection and Response continuously monitors processes, system activity, and file changes on endpoints. This visibility helps security teams detect behaviors that often appear during ransomware preparation.
Examples include unauthorized script execution, suspicious PowerShell commands, credential dumping attempts, and abnormal file modification activity.
Endpoint monitoring can also reveal persistence mechanisms that attackers create to maintain long-term access. These signals are critical for identifying ransomware campaigns before encryption begins.
Correlating Activity with SIEM Analytics
Ransomware attacks generate evidence across multiple systems, including authentication services, servers, and network devices. NetWitness SIEM capabilities collect and correlate these logs to identify suspicious patterns.
For example, analysts may detect a sequence of failed login attempts followed by successful authentication from an unusual location. They may also observe privileged account activity occurring outside normal operating hours or access to sensitive systems that a user does not typically interact with.
By correlating these signals, NetWitness helps analysts identify attack patterns that might otherwise remain hidden.
Detecting Compromised Accounts with Behavioral Analytics
Compromised credentials play a major role in many ransomware incidents. NetWitness uses behavioral analytics to detect activity that deviates from normal user patterns.
User and Entity Behavior Analytics establish baselines for typical user activity. When behavior deviates from those patterns, the platform generates alerts.
Examples include login attempts from unusual geographic locations, sudden spikes in data access, or administrative actions that a user has never performed before. These insights support AI and ransomware prevention by identifying abnormal activity even when attackers use legitimate credentials.
Investigating Ransomware Attacks with Full Context
Once suspicious activity is detected, analysts must quickly understand how the attack unfolded. NetWitness allows investigators to reconstruct the full attack timeline using correlated data from network traffic, endpoint activity, and security logs.
This allows analysts to identify the original entry point, determine which accounts were compromised, trace lateral movement across systems, and understand how attackers communicated with external infrastructure.
Having this unified view significantly improves ransomware incident response because analysts no longer need to piece together evidence from multiple tools.
Containing Ransomware Threats
Once an attack is confirmed, immediate containment is essential. NetWitness supports rapid ransomware response by enabling security teams to take decisive action directly from the platform.
Compromised endpoints can be isolated from the network to prevent further spread. Malicious IP addresses and domains can be blocked to disrupt attacker communication. Compromised user accounts can be disabled to stop unauthorized access.
These containment actions help prevent ransomware from spreading across the environment and limit the operational impact of the attack.
Strengthening Long-Term Ransomware Mitigation
Even after an incident is contained, organizations must continue monitoring for signs of persistent access. NetWitness supports proactive threat hunting by allowing analysts to search historical telemetry for suspicious activity that may indicate hidden attacker presence.
Security teams can investigate unusual authentication events, abnormal file access patterns, and unexpected network connections to ensure the environment has been fully secured. Continuous monitoring and threat hunting play an important role in long-term ransomware mitigation.
The Growing Threat of Modern Ransomware Campaigns
Recent ransomware latest attack campaigns demonstrate how organized and sophisticated these operations have become. Many ransomware groups now operate as structured cybercriminal enterprises. Some groups specialize in initial access, while others focus on developing malware or negotiating ransom payments with victims.
The rise of ransomware-as-a-service platforms has also made it easier for less experienced attackers to launch advanced ransomware attacks. As these operations continue to evolve, organizations must strengthen their defenses with unified detection and response capabilities.
Conclusion
Ransomware attacks are no longer simple malware infections. They are complex, multi-stage intrusions that unfold across networks, endpoints, and user accounts. Stopping these attacks requires visibility into the behaviors that appear long before encryption begins.
NetWitness provides that visibility through a platform that combines network detection and response, endpoint monitoring, SIEM analytics, behavioral analytics, and automated response capabilities.
By correlating security data across the environment, NetWitness enables earlier ransomware detection, faster investigation, and coordinated containment actions. This approach allows organizations to build a resilient unified ransomware defense capable of identifying threats early and preventing ransomware from disrupting operations.
Frequently Asked Questions
1. How does NetWitness detect ransomware threats?
NetWitness detects ransomware threats by analyzing network traffic, endpoint activity, and security logs to identify suspicious behaviors such as command and control communication, lateral movement, abnormal authentication patterns, and unauthorized file activity.
2. What makes ransomware detection challenging for enterprises?
Ransomware detection is challenging because attackers often use legitimate administrative tools and move across multiple systems. Without unified visibility across network, endpoint, and log data, these activities may appear normal and remain undetected.
3. How does unified visibility improve ransomware defense?
Unified visibility allows security teams to correlate activity across endpoints, networks, and logs. This makes it easier to identify attack patterns, investigate incidents quickly, and coordinate response actions.
4. What are the threats of ransomware?
Ransomware threats include operational downtime, financial losses, data theft, regulatory penalties, and reputational damage. Many modern attacks also involve data exfiltration before encryption.
5. How is ransomware detected?
Ransomware is detected by monitoring indicators such as unusual authentication behavior, suspicious network communication, abnormal process activity, and unauthorized file encryption patterns. Advanced security platforms analyze these signals across multiple data sources to identify attacks early.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.






