What Is Unified Visibility in Cybersecurity?
A unified cybersecurity solution is an integrated security platform. It combines network detection, endpoint security, SIEM, threat intelligence, behavioral analytics, and automated response.
In 2026, organizations are shifting toward unified security. It improves visibility, reduces alert fatigue, speeds response, and closes security gaps.
This approach supports a modern unified cybersecurity platform. It helps build long-term enterprise cybersecurity resilience.
Most SOC teams are not short on alerts. They are short on answers. Dashboards are full. Alerts keep coming. Detection rules are firing exactly as designed. Yet attackers still persist inside environments longer than anyone is comfortable admitting. Investigations take too long. Context is incomplete. And threat hunting often becomes reactive instead of proactive.
This is the disconnect most security leaders eventually face. Detection tools are working. But detection alone is not enough. Because attackers do not operate in alerts. They operate across systems.
An attacker might authenticate through identity infrastructure, execute tools on endpoints, and move across the network. Each step leaves evidence in a different place. When those signals are not connected, the attack remains invisible in plain sight.
This is why unified security visibility has become essential. It transforms fragmented signals into a connected attack narrative. And that shift is what enables real cyber threat hunting.
Why Alerts Alone Cannot Support Modern Threat Hunting
Alerts are event-driven. Threat hunting is behavior-driven. This difference matters more than most teams realize.
An alert typically represents a single detection event. It might flag suspicious execution, unusual authentication, or anomalous network activity. But attackers rarely stop at one action. They move through environments in stages.
Initial access leads to privilege escalation. Privilege escalation leads to lateral movement. Lateral movement leads to persistence and data access. Each step may generate signals. But those signals are scattered across tools. Without unified visibility, investigations become slow and incomplete.
| Investigation Question | Alert-Based Visibility | Unified Visibility |
| Where did the attack start? | Requires manual investigation | Immediately visible through correlated telemetry |
| How did the attacker move? | Difficult to trace across systems | Clear attack progression across endpoints and network |
| What systems were affected? | Partial visibility | Full attack scope visible |
| Is the threat ongoing? | Uncertain | Real-time visibility into attacker activity |
Threat hunting cyber security strategies depend on answering these questions quickly and accurately. Unified visibility makes that possible.
What Unified Visibility Actually Changes for Threat Hunting
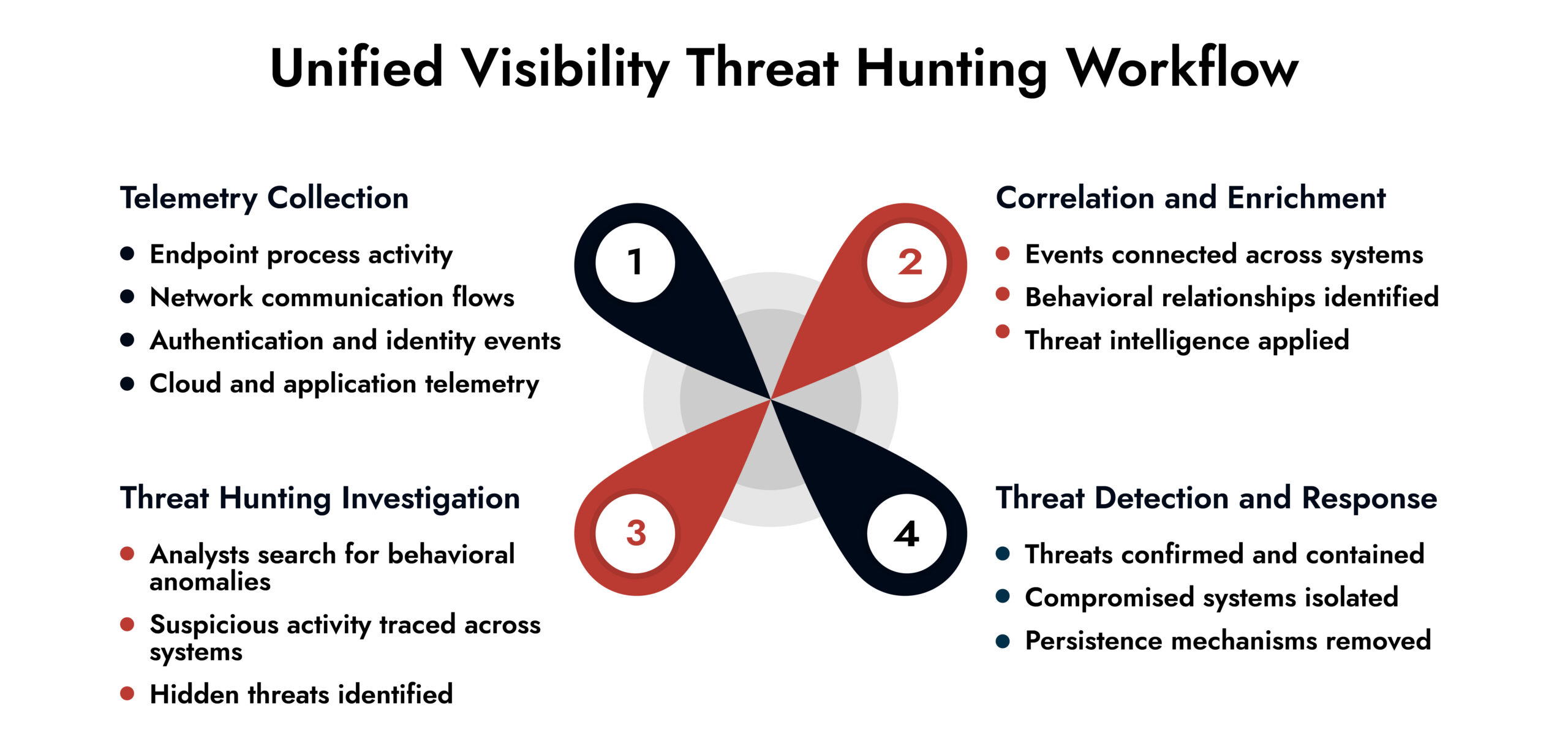
Unified visibility shifts security operations from isolated detection to continuous observation. Instead of responding only when alerts fire, threat hunters can proactively search for behavioral indicators across systems.
This includes identifying:
- Authentication anomalies indicating credential abuse
- Endpoint behavior indicating persistence or privilege escalation
- Network traffic indicating lateral movement or command-and-control communication
- Data access patterns indicating potential exfiltration
Threat hunting visibility depends entirely on access to this correlated telemetry. Without unified visibility, threat hunters see fragments. With unified visibility, they see the full picture.
How SIEM, NDR, and EDR Integration Enables Threat Hunting Visibility
Threat hunting requires multiple vantage points. This is why SIEM NDR EDR integration forms the backbone of unified visibility. Each technology answers a different investigative question.
| Technology | What It Reveals | Key Threat Hunting Value |
| SIEM | Authentication events, log activity, and historical timelines | Helps identify suspicious access patterns |
| NDR | Network communication and lateral movement | Detects attacker movement across systems |
| EDR | Endpoint execution, processes, and persistence mechanisms | Confirms compromise at the device level |
Individually, each tool provides partial insight. Together, they enable unified threat detection.
This integration allows analysts to pivot seamlessly across data sources. A suspicious login detected in SIEM can be correlated with network movement in NDR and endpoint activity in EDR. What begins as a simple alert becomes a complete attack timeline. This is what makes network threat hunting effective.
Why Threat Hunting Fails Without Unified Visibility
Threat hunting techniques rely on correlation. Without unified visibility, correlation becomes manual and unreliable. Several critical threat hunting activities become difficult or impossible.
Behavioral threat hunting requires understanding normal system activity and identifying deviations. Without unified telemetry, behavioral baselines are incomplete.
Hypothesis-driven threat hunting requires searching across multiple systems. Without unified visibility, threat hunters cannot validate hypotheses effectively.
Indicator-based hunting requires searching for indicators across endpoints, network traffic, and identities. Fragmented visibility limits search effectiveness.
Campaign tracking requires reconstructing attack timelines. Without unified visibility, attack sequences remain incomplete. These limitations reduce the effectiveness of threat hunting solutions. Unified visibility removes these barriers.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.
How Unified Visibility Improves Threat Detection and Response
Unified visibility improves detection accuracy by providing context. Instead of evaluating alerts in isolation, analysts can evaluate events as part of a larger pattern. This reduces false positives and improves confidence in detection decisions. It also accelerates investigations.
| Operational Metric | Fragmented Visibility | Unified Visibility |
| Investigation time | Hours to days | Minutes to hours |
| Detection accuracy | Limited context | Full attack correlation |
| Threat hunting effectiveness | Reactive | Proactive |
| Incident response speed | Delayed | Accelerated |
Threat detection and response becomes faster and more precise. This directly reduces risk.
The Role of Unified Visibility in Modern Threat Hunting Solutions
Modern threat hunting solutions rely on unified telemetry to operate effectively. Unified visibility enables continuous monitoring across systems. It allows security teams to detect early-stage attack activity before attackers achieve persistence or exfiltrate data. It also enables automation.
Threat hunting tools can automatically correlate telemetry, identify suspicious patterns, and assist analysts in investigation. This improves both speed and accuracy. Unified visibility also improves SOC efficiency. Analysts spend less time collecting data and more time analyzing threats.
This is critical in environments where alert volume continues to increase. Unified visibility transforms threat hunting from a manual, reactive process into a continuous, proactive capability.
Where Security Operations Are Heading
Attackers are faster than ever. Many attacks progress from initial access to lateral movement within hours. Threat hunting is no longer optional. It is essential. But threat hunting is only as effective as the visibility behind it. Organizations that rely on fragmented visibility will continue to struggle with delayed detection and incomplete investigations.
Organizations that invest in unified visibility gain the ability to detect threats earlier, investigate faster, and respond with confidence. This is not a tooling problem. It is a visibility problem. And unified visibility is the solution.
How NetWitness Supports Unified Threat Hunting Visibility
NetWitness provides unified security visibility by natively integrating SIEM, NDR, and EDR telemetry into a single operational platform. Security teams gain a complete view of attacker behavior across endpoints, networks, and identities.
This enables:
- Faster threat detection and investigation
- Improved threat hunting visibility
- Reduced blind spots across the environment
- Stronger and more effective threat detection and response
Instead of switching between tools, analysts gain one unified view. This improves both efficiency and detection effectiveness.
Frequently Asked Questions
1. Why is unified visibility essential for threat hunting?
Threat hunting requires complete visibility across systems. Unified visibility enables threat hunters to trace attacker activity, identify behavioral anomalies, and detect threats that isolated tools cannot identify.
2. Which tools contribute to unified visibility?
SIEM, NDR, EDR, identity monitoring, and cloud security platforms contribute to unified visibility by providing telemetry from different parts of the environment.
3. Can unified visibility support automated threat hunting?
Yes. Unified visibility enables automation by allowing threat hunting tools to correlate telemetry, detect anomalies, and identify threats automatically.
4. How does unified visibility improve threat hunting accuracy?
Unified visibility provides full attack context, enabling analysts to correlate events across systems and identify threats more accurately while reducing false positives.