Key Takeaways
- Logs are spread across various systems by default, and it is necessary to unify them to understand the complete operational and security picture.
- Log aggregation means collecting logs and then normalizing, correlating, and organizing logs to enable meaningful analysis.
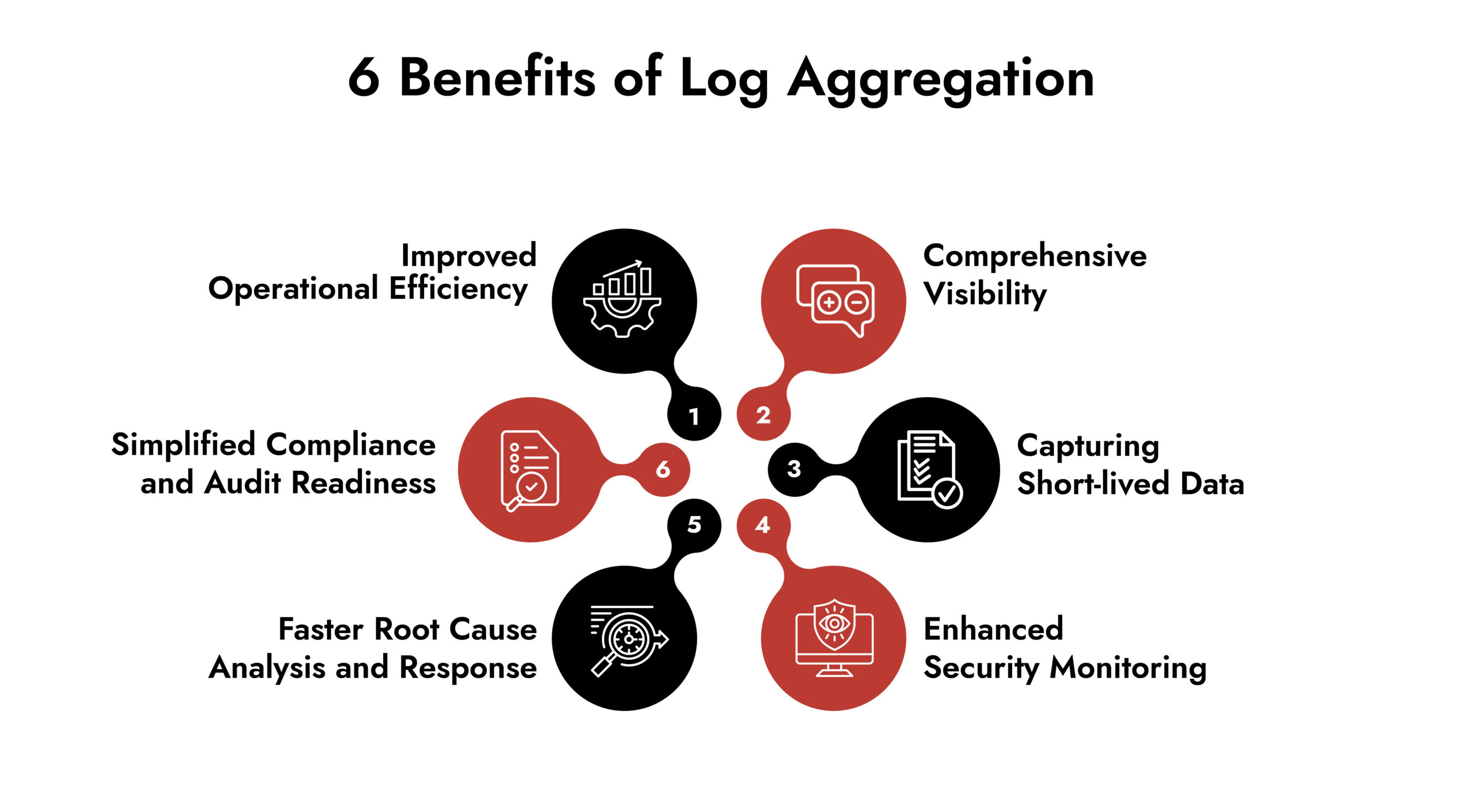
- Log aggregation helps in comprehensive visibility, capturing ephemeral logs, enhances security monitoring, accelerates analysis, simplifies compliance, and improves operational efficiency.
- Log aggregation is the first layer of defense; SIEM takes it further by supporting incident reporting and alerting.
Every system in your organization speaks their mind through logs. Your web servers record every request. Your firewalls monitor every connection attempt. Your applications document every transaction or error. But these logs remain scattered throughout the network. These fragmented logs do not show the whole picture.
That is where log aggregation comes in. Let’s look at what it means and what are the benefits of log aggregation in cybersecurity space.
What is meant by Log Aggregation?
Log aggregation is the process of collecting log data from multiple sources across your IT infrastructure. It consolidates the logs and stores them in a centralized location where it can be analyzed and searched effectively.
Log aggregation tools helps security teams to monitor activity across the organization in real-time, troubleshoot issues, investigate incidents, and meet compliance requirements.
What is the Difference Between Log Collection and Log Aggregation?
Log aggregation is often confused with log collection. But log aggregation goes several steps beyond log collection.
Log collection is a simple act of gathering logs from various systems and moving them somewhere else, if required.
Log aggregation on the other hand is collecting logs from various systems, parsing them into a uniform format, adding contextual information, correlating it to specific events, and finally organizing them in a fashion that facilitates easy searching and analysis.
For example: Log collection is installing security cameras on each floor in the office. Each camera records footage on its own system. So, while the footage exists, it is fragmented and to understand the entire sequence of an event, one must go through each floor and footage files separately and connect the dots.
Log aggregation is when all the recordings are put together and accessible in a central control room. The security team can view, search, and correlate all the footage from every floor from one place.
What are the Benefits of Log Aggregation?
Let us look at how log aggregation helps organizations in strengthening security and operations.
1. Comprehensive Visibility
When the data is scattered across the organization, connecting the dots for an insight seems like counting stars. Log aggregation overcomes this major obstacle by unifying the logs and giving 360-degree visibility across the IT infrastructure. Teams get access to a single source of truth in a centralized location as opposed to spending hours just collecting data.
This visibility helps the SOC teams accelerate their analysis and response. For CISOs, log file analysis gives insights into the risk posture for better strategic decisions around cybersecurity.
2. Capturing Short-lived Data
Modern cloud environments rely on containers, serverless functioning, and virtual workflows that exist for only a few seconds or minutes. Collecting and monitoring logs or data from such ephemeral resources manually is impossible. Advanced log aggregation solutions ensure that logs from such resources are collected before they disappear.
3. Enhanced Security Monitoring
Log aggregation is nothing but telemetry as far as security is concerned. The logs monitor and keep SOC analysts informed about unauthorized access attempts, suspicious behavior patterns, lateral movement indicators, and policy violations in real-time.
Log aggregation also ensures that the SOC team has consistent, complete, and recent data for analysis and detection.
4. Faster Root Cause Analysis and Response
During a security incident, every minute that is spent longer on analysis or any other procedure costs the organization. And unfortunately, the root cause does not exist in isolation; it may be due to a certain application logic or missed updates or external dependencies.
Log aggregation tools collects all the data and correlates them, largely simplifying analysis. This translates into faster root cause analysis and millions of savings.
For example, if your SOC detects unusual outbound traffic from a production server, with aggregated logs they can:
- Instantly search the related activities across the server
- Correlate with authentication logs to discover the user behind the activity
- Check application logs for unusual behavior
- Execute containment protocols
To execute all these activities manually, it would take hours, but with aggregated logs, this can be done within minutes.
5. Simplified Compliance and Audit Readiness
Regulatory guidelines demand comprehensive logging practices. GDPR requires data access audit logs, PCI DSS mandates cardholder data environment logs, SOC 2 requires monitoring and detection logs, and HIPAA demands audit controls for health information.
Log aggregation and management helps meet these requirements by applying consistent retention policies to produce audit-ready documents. It sets up the foundation for compliance by ensuring:
- Role-based access control to logs
- Audit trails of log access
- Protected log storage to ensure data integrity
- Automated compliance reporting
Simplify Log Management and Threat Detection with NetWitness® Logs
-Centralize and analyze logs from across your environment in one platform.
-Detect threats faster with real-time visibility and automated correlation.
-Reduce noise through advanced filtering and context-driven analytics.
6. Improved Operational Efficiency
When the logs are available in a centralized location, cross-functional teams such as SOCs, IT operations, DevOps, and application teams can refer to an up-to-date single source of truth. This shared visibility eliminates conflicting interpretations and rework due to referencing outdated data.
This also means smoother handoffs, improved collaboration, and overall enhanced efficiency.
How can NetWitness Help?
In the ever-changing threat landscape, log aggregation is definitely crucial to fortify cybersecurity defense. But it is just the first layer. Organizations should go an extra mile and employ solutions that collect data, analyze it to detect threats and as well as generate alerts to support incident response.
NetWitness SIEM captures logs from 350+ sources, including AWS, Azure, Salesforce, etc., using Syslog, ODBC, SFTP, FTPS, and SNMP protocols.
It goes beyond log aggregation and manages alerts as well as generates reports using templates that comply with regulatory standards such as SOX, HIPAA, PCI, and NERC.
Key features of NetWitness SIEM include:
- Centralized Log Management
- Dynamic Parsing & Metadata
- Cloud-Ready Deployment
- Customizable Reporting
- Automated Log Source Directory
Frequently Asked Questions
1. How do log aggregation services handle data retention and compliance?
The volume of logs generated in an IT infrastructure is immense. Saving all of the logs is inefficient as well as costly. Most of the log aggregation services manage data retention by allowing the organization to define their retention policies based on their regulatory, operational, or business requirements.
The logs can be retained for short periods for troubleshooting and long periods for compliance requirements.
2. What is the best tool for log aggregation?
There is no one-size-fits-all when it comes to log aggregation solutions because each organization has different requirements. The right choice depends on factors such as environment complexity, log volume, security requirements, scalability needs, and integration with existing tools.
While evaluating a log aggregation solution, the organizations should check for:
- Broad log source support (on-prem, cloud, SaaS, security tools)
- Reliable ingestion at scale without data loss
- Fast search and filtering capabilities
- Flexible retention and storage options
- Seamless integration with security and monitoring platforms
3. What is the difference between SIEM and log aggregation?
SIEM and Log Aggregation are similar tools, but SIEM goes beyond log aggregation. Let’s look at the differences between each tool:
Feature | Log Aggregation | SIEM |
Log Collection | Yes | Yes |
Data Normalization | Basic parsing and normalization | Advanced normalization and enrichment |
Search & Query | Yes | Yes |
Event Correlation | Limited | Core capability across multiple log sources |
Threat Detection | No | Yes |
Alerting | Basic (if supported) | Advanced and security-driven |
Incident Response Support | Provides data for investigation | Supports investigation, triage, and response workflows |
Compliance and Auditing | Yes | Yes |
Operational Overhead | Low | High |
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.





