What's the main difference between IT and OT?
IT manages data. OT controls physical processes. In IT, the big concerns are confidentiality and integrity. In OT, availability comes first because when OT goes down, production stops and things can break or worse. They also run on entirely different protocols, with OT equipment typically lasting far longer and being far harder to update.
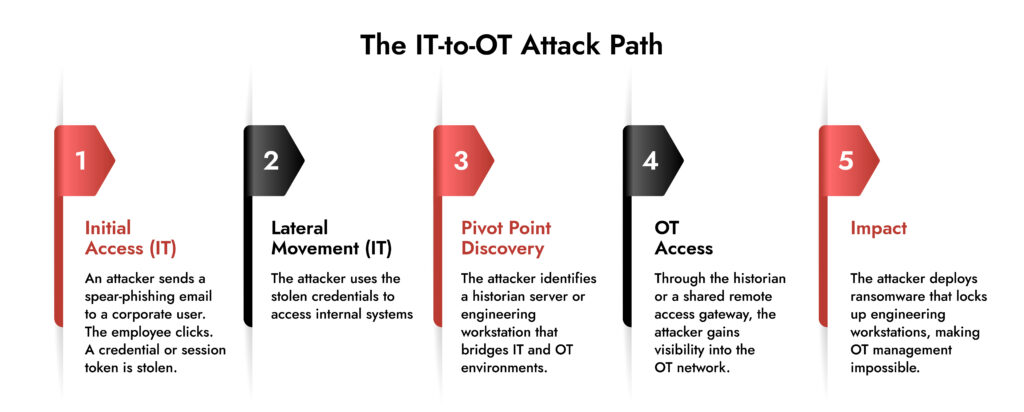
When IT Gets Breached, OT Pays the Price
A cybercriminal collective named Scattered Lapsus Hunters, comprising of Scattered Spider, Lapsus$, and ShinyHunters, gained access to Jaguar Land Rover’s systems using stolen credentials. Within days, the attackers had crossed into the systems that physically run JLR’s factories. Assembly lines at Solihull, Halewood, and Wolverhampton shut down. They stayed shut down for five weeks.
JLR itself absorbed around £196 million. The knock-on damage to the broader U.K. economy came close to £1.9 billion with suppliers scrambling, workers facing layoffs, and September car production falling to levels the country hadn’t seen since 1952. The government had to step in with a £1.5 billion loan guarantee just to keep the supply chain from collapsing further.
The attackers hit IT and moved through it to the factory floor. We are discussing this lethal trend that is impacting industries around the world.
Why IT/ OT Convergence Cybersecurity Matters?
For decades, OT and IT existed in entirely separate worlds. No real connection between them, which meant an attack on one couldn’t easily touch the other.
Remote monitoring, cloud connectivity, predictive maintenance, and digital transformation have broken the wall between corporate networks and industrial systems. Equipment designed to run for 20 or 30 years is now connected to infrastructure that talks to the internet. Which means attackers get two attack surfaces instead of one.
Ransomware attacks on industrial targets jumped 87% year-over-year in 2024. Manufacturing has been the top ransomware target for four years running. Unplanned downtime costs industrial manufacturers around $50 billion a year, and for Fortune Global 500 companies, the figure swells to roughly $1.4 trillion annually, about 11% of total revenues, per Siemens’ 2024 True Cost of Downtime report.
What is Operational Technology?
Operational technology is the technology that makes physical things happen. The systems that run the plant, manage the grid, and control the pipeline.
There are a few popular operational technologies used, out of which SCADA sits at the top of the stack. It lets an operator in a control room monitor and manage dozens of remote substations without ever physically visiting them. PLCs are down on the factory floor, running tight control loops thousands of times per shift. DCS handles continuous process environments such as chemicals, refining, and pharma, where the whole plant is essentially one giant interconnected process rather than discrete steps. HMIs are the screens operators actually look at, though those screens are just a front end for whatever SCADA or DCS is running underneath. And RTUs are out in the field like substations, pipelines, and remote sites that send readings back to the control center.
Anything going wrong in OT can lead to a wrong valve opening, breaker tripping, or a safety interlock going offline. The damage manifests in equipment, production, and sometimes people.
What is Information Technology?
IT is the world of servers, databases, email, business applications, cloud platforms, and the laptops everyone carries around.
Everything in IT is fundamentally about data. Moving it, storing it, securing it, making sense of it. When IT goes down, people can’t access files, transactions stall, and emails bounce. It is disruptive but does not directly affect physical operations.
What is the Difference between IT and OT?
| Dimension | IT | OT |
| Primary purpose | Processing and managing data | Monitoring and controlling physical processes |
| Top priority | Confidentiality → Integrity → Availability | Availability → Integrity → Confidentiality |
| Downtime impact | Business disruption, lost access | Production halt, equipment damage, safety risk |
| Patch cycle | Regular, often automated | Infrequent; needs vendor sign-off and planned shutdowns |
| System lifespan | 3–7 years | 15–30+ years |
| Communication protocols | TCP/IP, HTTP/S, DNS, SMTP | Modbus, DNP3, PROFINET, OPC-UA, HART |
| Security tooling | Mature — EDR, SIEM, DLP, IAM | Immature — most enterprise security tools don’t work here |
| Vendor flexibility | High — broad ecosystem | Low — proprietary systems, certified configurations |
| Testing/validation | Can sandbox or run in parallel | Testing on live systems is rarely an option |
| Safety stakes | Data loss, regulatory risk | Physical harm, equipment damage, environmental incident |
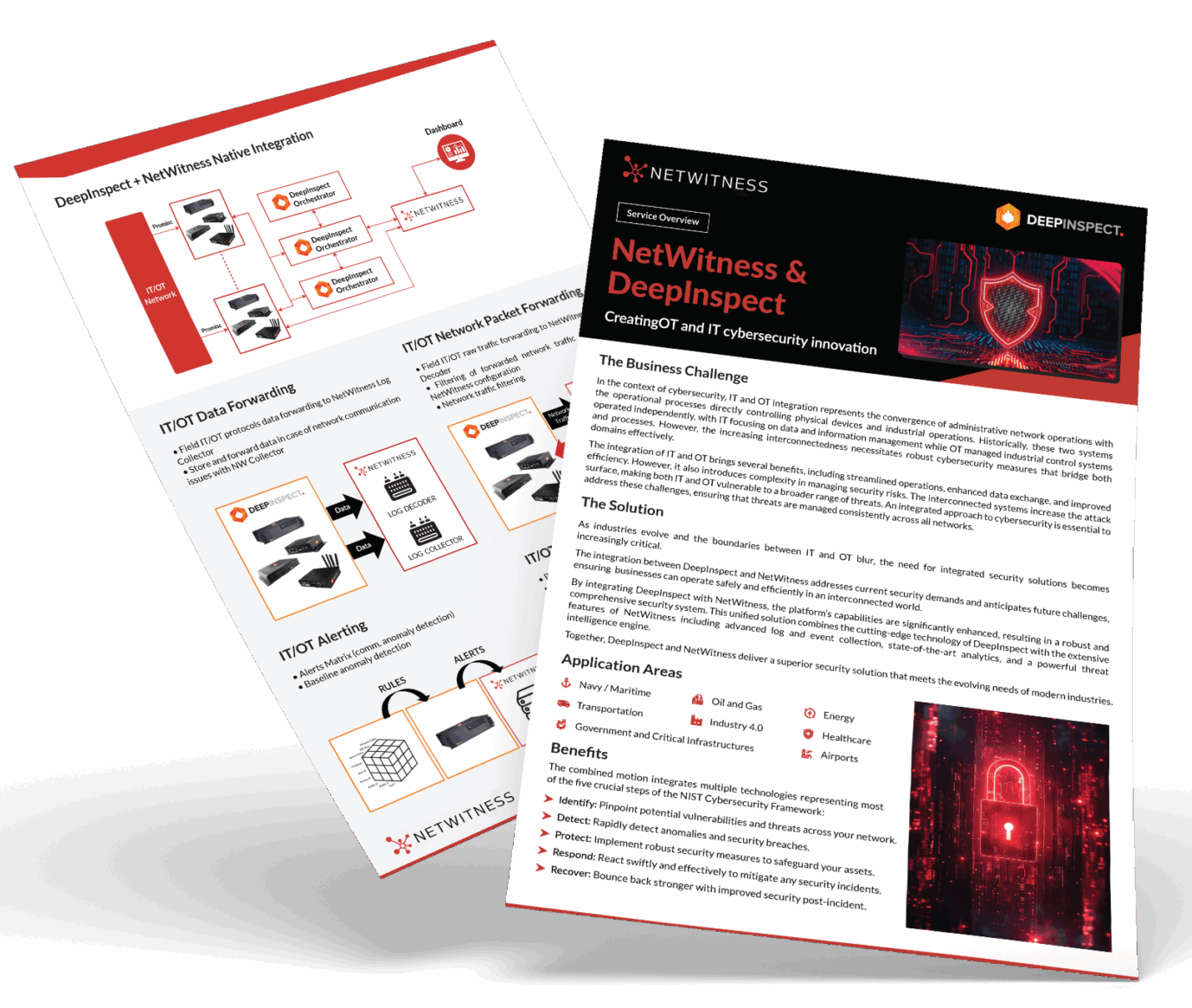
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
Why is OT Security Difficult?
It’s not that OT security has been neglected out of carelessness. The difficulty is baked into technology.
For example, the patching process in OT is way more complicated than in IT. A PLC installed in a refinery in 2003 might still be running the firmware it shipped with, because it works, is certified, and patching it means a planned shutdown and a capital project in the six figures. These systems weren’t designed to receive security updates over the internet.
Then there’s the downtime problem. In IT, taking something offline to contain an incident is completely standard. In OT environments, an unplanned shutdown can cost millions of dollars per hour. In automotive manufacturing, that number is $2.3 million per hour. Nobody on the security team can make that call casually.
IT security tools do not fit in OT environments. The protocols are different. The device behaviors are different. And there’s a real risk that a security tool designed for IT will cause a disruption just by running on an OT network. OT network security needs passive monitoring approaches and tools built specifically for industrial protocols.
And then there’s visibility or the lack of it. Most OT environments have no complete asset inventory. Devices were installed by vendors, commissioned by contractors, and never formally documented in a way a security team can actually use. You can’t protect what you can’t see.
How NetWitness OT Solution Helps
NetWitness OT Solution, powered by DeepInspect, was built for this environment specifically. It correlates activity across both IT and OT security at the same time, giving security teams a single view of what’s happening across the whole environment rather than two partial pictures. It identifies threats within OT protocols and industrial systems, and it’s designed to get organizations to faster detection and clearer visibility — without disrupting the operations that keep the business running.
Frequently Asked Questions
1. Why does OT security matter so much?
OT systems are connected to the physical world. Attacks can halt production, damage equipment, cause safety incidents, or put people at risk.
2. What are the biggest challenges in OT environments?
The biggest challenges in OT environments are:
- Legacy systems that can’t be safely patched.
- Limited visibility into what’s actually on the network.
- Incompatibility with standard IT security tools.
- Insufficient segmentation between IT and OT.
- Lack of people who understand OT security.
3. Why does visibility matter so much in OT?
Without knowing what devices are on the network, security teams can’t spot vulnerable systems, detect unusual behavior, or understand the scope of an incident. Many OT environments have assets that were deployed years ago with no formal documentation. Passive monitoring tools are the right approach; they build that visibility without putting operational systems at risk.
4. How do organizations secure OT environments?
To secure Operational Technology environments, organizations use a combination of:
- OT monitoring tools to continuously discover assets and detect anomalies
- Network segmentation between IT and OT for controlled data flow
- Strict access control and multi-factor authentication for remote access
- Regular OT-focused risk assessments
- Incident response plans based on OT scenarios
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.