What a DDoS Attack Means for Business Continuity?
A DDoS attack disrupts business continuity by overwhelming network infrastructure and making services unavailable to users. This prevents customers from accessing platforms, interrupts internal operations, causes revenue loss, and delays incident response. Organizations without proper ddos attack prevention and mitigation strategies experience longer downtime and greater operational impact.
Introduction
Business continuity is built on one assumption: your systems remain available. A DDoS Attack breaks that assumption instantly. It doesn’t steal data. It doesn’t exploit vulnerabilities in the traditional sense. Instead, it does something more disruptive. It makes your business inaccessible. Customers cannot log in. Employees cannot access applications. Transactions fail. Operations stop.
A distributed denial of service attack ddos attack is designed to exhaust your infrastructure, overwhelm your network, and block legitimate users from accessing services. For organizations that rely on digital platforms, this is not just an IT incident. It is an operational shutdown. And when availability disappears, business continuity collapses with it.
Why a DDoS Attack Is a Direct Threat to Business Continuity
Most security incidents compromise confidentiality or integrity. DDoS attack targets availability. That distinction matters. Availability is what keeps revenue flowing, employees productive, and customers engaged. When systems go down, the business impact begins immediately.
1. Revenue Stops the Moment Systems Become Unavailable
If customers cannot access your platform, they cannot complete transactions.
For example:
- An e-commerce platform loses sales every minute checkout fails
- A SaaS provider cannot serve customers using its application
- A banking portal prevents users from completing payments
Even short disruptions translate into measurable financial loss. This is why network availability attacks are often used to cause maximum operational damage, not just technical disruption.
2. Internal Operations Break Down Quickly
A distributed denial of service attack ddos attack does not only affect customer-facing services. It also affects internal infrastructure.
Employees may lose access to:
- CRM systems
- Communication platforms
- Cloud applications
- Internal dashboards
Support teams cannot assist customers. Operations teams cannot monitor systems. Incident response becomes slower because visibility itself is affected. What begins as a network issue becomes a business-wide disruption.
3. Customer Trust Erodes Faster Than Systems Recover
Customers expect services to work every time. When availability becomes unreliable, users begin to question whether they can depend on your platform. Even if services recover, the perception of instability remains.
Repeated availability failures often lead to:
- Customer churn
- Reduced platform usage
- Brand credibility loss
Business continuity is not just about uptime. It is about maintaining confidence.
How a Distributed DDoS Attack Actually Disrupts Infrastructure
To understand the business impact, it helps to understand how these attacks work. A distributed ddos attack uses thousands of compromised systems, often part of botnets. These systems send massive traffic volumes to a target simultaneously. The infrastructure becomes overwhelmed. Servers cannot respond fast enough. Network bandwidth becomes saturated. Applications stop responding.
From a business perspective, the symptoms appear as:
- Websites timing out
- Applications freezing
- Login failures
- API communication breakdown
What customers see is simple. Your service stops working. What happens underneath is resource exhaustion at scale.
Types of Denial-of-Service (DoS) Attack and Their Business Consequences
Not all DDoS attacks look the same. Different attack types affect different parts of your infrastructure.
1. Volumetric Attacks: Bandwidth Saturation
These attacks flood networks with traffic until bandwidth capacity is exhausted.
Business impact:
- Websites become unreachable
- Customer access stops completely
These are the most visible network availability attacks.
2. Protocol Attacks: Infrastructure Resource Exhaustion
These attacks target firewalls, load balancers, and network devices.
Business impact:
- Network instability
- Intermittent service outages
These attacks disrupt the foundation of connectivity.
3. Application Layer Attacks: Targeted Service Disruption
These attacks target specific applications such as login portals or payment systems.
Business impact:
- Critical services stop working
- Customers experience partial outages
These attacks are harder to detect because they resemble legitimate traffic.
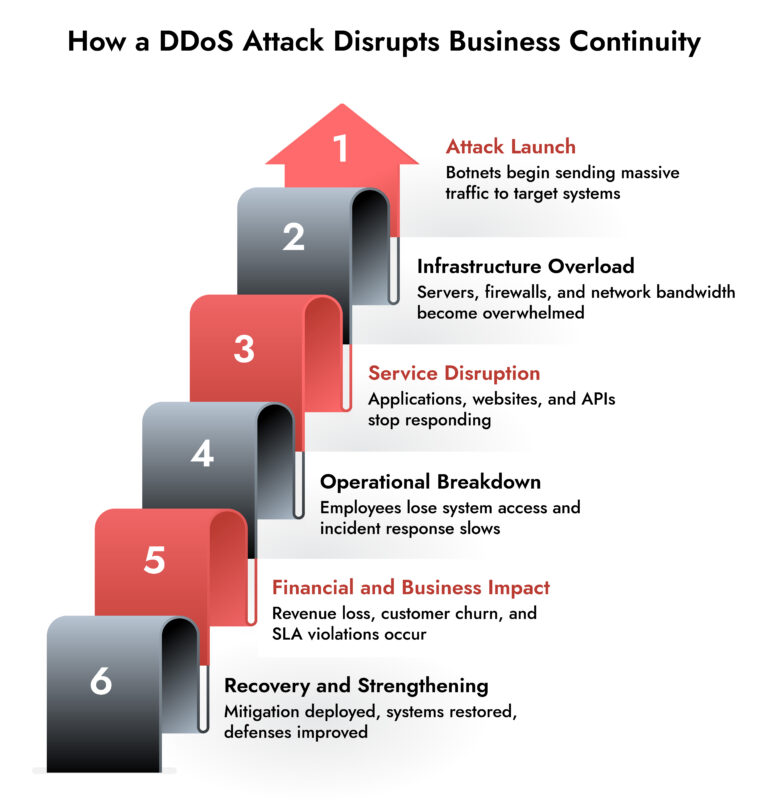
The Real Business Continuity Timeline During a DDoS Attack
The impact unfolds in phases, and each phase affects business continuity differently.
Phase 1: Performance Degradation
Systems slow down. Users experience delays.
Early signs often include:
- Slow application response
- Intermittent connection failures
This is the warning stage.
Phase 2: Service Outage
Infrastructure becomes overwhelmed.
At this stage:
- Websites stop loading
- Applications become inaccessible
- Customers cannot use services
Business continuity is now actively disrupted.
Phase 3: Operational Disruption
Internal operations begin to fail.
Teams cannot:
- Monitor systems
- Access tools
- Respond effectively
Operational visibility decreases precisely when it is needed most.
Phase 4: Recovery and Stabilization
Even after mitigation, systems require time to stabilize.
Teams must:
- Restore services
- Analyze root causes
- Strengthen defenses
Recovery often takes longer than the attack itself.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.

Why Traditional Security Tools Cannot Stop DDoS Attacks Alone
Many organizations assume network firewalls can handle these attacks. They cannot. Firewalls are designed to filter malicious connections, not absorb massive traffic floods. A distributed denial of service attack ddos attack overwhelms infrastructure capacity before traditional controls can react. This is why ddos attack prevention requires dedicated mitigation strategies and scalable infrastructure.
How DDoS Attacks Affect Critical Business Functions
The impact extends across the organization.
Customer Access Disruption – Customers cannot access services, resulting in lost engagement and revenue.
Operational Visibility Loss – Monitoring tools themselves may become inaccessible, slowing response efforts.
Incident Response Delays – Security teams cannot analyze traffic effectively without proper visibility.
Service Level Agreement Violations – Organizations may fail to meet uptime commitments, resulting in financial penalties.
DDoS Detection vs DDoS Mitigation –
| Aspect | DDoS Detection | DDoS Mitigation |
| Primary Goal | Identify abnormal or malicious traffic | Keep services available during the attack |
| Focus | Visibility and analysis | Traffic filtering and absorption |
| Key Capabilities | Traffic monitoring, anomaly detection, behavioral analysis | Scrubbing, rate limiting, rerouting, bandwidth scaling |
| Outcome | Early awareness and informed response | Reduced downtime and sustained availability |
| Limitation | Does not stop traffic overload by itself | Does not provide deep investigative insight |
Detection provides intelligence. Mitigation provides protection capacity. Business continuity depends on both working together.
How Do I Stop DDoS Attacks from Affecting Business Continuity
The goal is not just to block attacks, but to maintain availability during them. Effective ddos attack prevention focuses on resilience.
Key strategies include:
Continuous Traffic Monitoring – Real-time monitoring helps identify abnormal traffic patterns early. Early detection reduces downtime.
Infrastructure Redundancy – Distributed infrastructure ensures traffic can be absorbed across multiple systems. This prevents single points of failure.
Traffic Filtering and Mitigation – Malicious traffic must be filtered before it reaches critical infrastructure. This protects core systems.
Using Dedicated DDoS Prevention Services – DDoS prevention services absorb attack traffic and prevent infrastructure overload. These services are essential for maintaining business continuity.
How to Avoid DDoS Attack Impact Through Preparedness
Organizations cannot always avoid DDoS attack attempts, but they can avoid operational disruption.
Preparation includes:
- Scalable infrastructure
- Continuous monitoring
- Incident response planning
- Network visibility
Prepared organizations maintain availability even under attack conditions. Unprepared organizations experience downtime.
NetWitness Approach to Protecting Business Continuity Against DDoS Attacks
Maintaining business continuity during network availability attacks requires more than perimeter defenses. Organizations need visibility into traffic behavior, infrastructure stress points, and abnormal activity patterns.
NetWitness provides deep network visibility that helps security teams identify abnormal traffic surges early. This allows faster investigation and response before availability is fully impacted.
NetWitness provides deep network visibility, behavioral analytics, and investigation capabilities that help security teams detect and analyze abnormal traffic patterns during DDoS events. It delivers detailed insight and forensic investigation support, rather than traffic absorption or scrubbing capabilities. This enables faster decision-making and stronger coordination with dedicated DDoS mitigation services.
Conclusion: Availability Is the Foundation of Business Continuity
A DDoS Attack does not need to breach your systems to disrupt your business. It only needs to make them unavailable. That alone is enough to stop operations, interrupt revenue, and damage customer trust. Organizations that prioritize ddos attack prevention, invest in visibility, and implement mitigation strategies are far better positioned to maintain continuity. Because in modern business, availability is not just a technical requirement. It is the foundation of operational survival.
Frequently Asked Questions
1. What is ddos attack?
A DDoS attack is a distributed denial of service attack ddos attack where multiple systems flood a target with traffic, making services unavailable to legitimate users.
2. DDoS Attack vs DoS Attack: What Is the Difference?
A DoS attack comes from one system. A distributed ddos attack uses multiple systems, making it more powerful and harder to mitigate.
3. How long do DDoS attacks typically last?
DDoS attacks can last from a few minutes to several hours. Larger attacks may continue for days depending on mitigation capabilities.
4. how do you prevent ddos attacks?
DDoS prevention involves traffic monitoring, scalable infrastructure, traffic filtering, and using ddos prevention services to absorb attack traffic.
5. How does a DDoS attack impact business continuity?
A DDoS attack disrupts availability, prevents access to services, interrupts operations, and causes revenue and productivity loss, directly affecting business continuity.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.