What are the largest network security challenges in 2026?
- The most pressing network security challenges in the current era are a result of a lack of east-west visibility, blind spots in encrypted traffic, and slow lateral movement detection.
- Hybrid and multi-cloud environments are increasing network security risks, and therefore, a need for telemetry is required to address enterprise network security.
- Credential abuse and insider threats are still the most prominent causes of network security threats.
- Organizations that integrate deep packet visibility with behavioral analytics significantly reduce dwell time and investigation delays.
- Strong network security and management practices now require continuous monitoring, correlation, and automated response workflows.
Introduction
Network defenders face a simple truth: most network security issues don’t shout. They whisper – small deviations, encrypted beacons, an unusual east-west connection. Attackers exploit that quiet.
Hybrid clouds, SaaS sprawl, and encryption mean the network stops being a simple pipe and becomes an evidence archive you can’t always read. Fixing network security issues means reading that archive fast and accurately.
Key Network Visibility Challenges Causing Network Security Issues
1. Visibility Fragmentation
Many teams lack unified visibility across on-prem, cloud, and OT zones. That gap creates the single biggest vector for modern network security issues. Security tooling often aggregates logs, not sessions. When you lose packet-level or session context, investigation slows and false positives multiply. NIST’s zero trust guidance underscores continuous inspection and verification across all traffic paths, yet organizations still struggle to roll this out consistently.
Tactical moves:
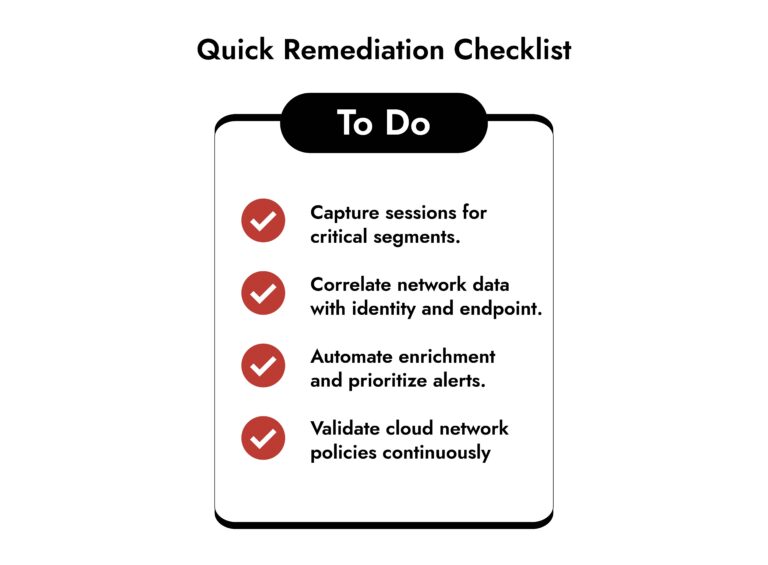
- Prioritize session capture for critical segments.
- Map east-west flows and instrument cloud VPCs.
- Link network telemetry to identity and endpoint signals.
2. Lateral Movement Detection
Detecting lateral movement quickly remains one of the toughest network security issues. Attackers move using legitimate tools and credentials; signatures won’t catch that.
What happens in practice: An adversary escalates privileges, uses SMB, RDP, or cloud API calls, and blends with normal traffic. Verizon’s DBIR highlights how lateral activity features heavily in confirmed intrusions.
What works:
- Behavioral baselining that focuses on flows and session intent.
- Full packet capture for reconstruction.
- Correlation with identity and endpoint telemetry so network anomalies map to user context.
3. Encryption
Widespread TLS adoption means many network security issues hide in encrypted channels. You must detect anomalies without violating privacy or performance SLAs. Evidence: TLS 1.3 adoption and broad encryption of web traffic have increased the need for selective inspection and metadata analysis. Simple signature checks aren’t enough.
Practical options:
- Use selective decryption in high-risk zones.
- Apply encrypted traffic analysis via flow, timing, and metadata anomalies.
- Keep legal/privacy teams in the loop for policy design.
4. Signal Overload
Too many alerts, too little context; that’s a core operational network security issue. Analysts drown in noise and miss the real signals. Why it breaks things: High log volume and siloed tools generate alerts that lack forensic evidence. Investigations become manual stitching exercises. IBM and other industry reports link delayed detection and slow containment to higher breach costs.
Fixes that scale:
- Prioritize alerts with automated enrichment (assets, identity, risk score).
- Invest in playbooks that act on high-confidence detections.
- Tune detection rules based on real adversary behaviors, not vendor defaults.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
5. Insider Threats and Credential Abuse
Not all network security issues come from outside. Insiders, compromised credentials, and shadow IT create high-risk activity that looks legitimate. Insider incidents continue to rise and often involve data access over legitimate encrypted channels. Detecting that behavior requires tying identity timelines to network flows.
Stopgaps:
- Monitor anomalous access patterns and atypical data flows.
- Combine DLP, behavioral analytics, and least-privilege enforcement.
- Use session reconstruction to prove intent during investigations.
6. Cloud and Multi-Cloud Misconfigurations
Misconfigurations create exploitable gaps that quickly become severe network security issues in multi-cloud environments. Security group rules, permissive IAM roles, or missing VPC flow logs leave attackers paths to move and exfiltrate. Continuous validation of network and cloud policies is essential.
Action items:
- Automate cloud network rule checks.
- Aggregate cloud network telemetry into the same investigative plane as on-prem capture.
- Treat cloud east-west traffic like on-prem east-west traffic – instrument it.
Strengthening Enterprise Network Security with Deep Network Detection and Response
Addressing these challenges requires more than incremental tuning. Modern enterprise network security strategies increasingly rely on advanced Network Detection and Response (NDR) capabilities that provide:
- Full packet capture and session reconstruction
- Behavioral analytics for anomaly detection
- Correlation across network, endpoint, and cloud telemetry
- Automated investigation workflows
Platforms such as NetWitness Network Detection and Response combine deep packet inspection with advanced analytics to improve lateral movement detection, uncover insider threats in networks, and enhance overall network threat monitoring.
The advantage lies in forensic depth. When analysts can replay traffic and reconstruct attacker actions, investigation shifts from guesswork to evidence-driven response. This approach directly addresses critical network security issues tied to visibility, encryption, and hybrid complexity.
Conclusion
Most network security issues collapse when you treat the network as the authoritative source for detection and investigation. Detection matters. But so does evidence. When teams combine session fidelity, behavioral analytics, and automated enrichment, they shorten dwell time and make containment decisive.
Pick a high-value segment, capture sessions, add identity context, and prove that you can investigate faster. That practice turns vague alerts into actionable cases. If you want to dig into the mechanics of modern NDR and session reconstruction, NetWitness offers practical resources on integrating deep network telemetry into response workflows.
Frequently Asked Questions
1. What are the most common network security issues today?
Encrypted blind spots, lateral movement detection failures, visibility fragmentation across hybrid estates, alert overload, insider threats in networks, and cloud misconfigurations top the list.
2. How do I troubleshoot network security issues?
Start with evidence. Validate session capture, link network telemetry to identity, reconstruct suspicious flows, and prioritize alerts that correlate to high-value assets.
3. Why are network threats becoming harder to detect?
Threats use legitimate channels, credentials, and encryption. Signature-only defenses miss these behaviors, so detection must pivot to behavioral and session analysis.
4. How can organizations improve their network security posture?
Integrate packet/session capture, contextualize alerts with identity and asset information, automate investigative actions, and continuously verify cloud and network configurations.
5. What role does network visibility play in reducing risk?
Visibility enables you to identify anomalies early, backtrack attack chains, and demonstrate containment. Visibility translates suspicion into action.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.