Why is SIEM cloud integration important for cloud security?
SIEM cloud integration is important for cloud security because it enables centralized visibility across cloud security services, users, networks, and workloads. By correlating identity events, cloud logs, and SIEM networking data, SIEM technologies support continuous cloud security monitoring and stronger cloud threat detection. This integration helps security teams uncover credential misuse, misconfigurations, and lateral movement that often go unnoticed in isolated tools, strengthening overall SIEM cybersecurity and the effectiveness of SIEM security solutions across hybrid environments.
Introduction
Cloud didn’t break security. It broke old assumptions about visibility.
Logs are no longer coming from a handful of data centers. They’re streaming from SaaS apps, cloud workloads, identity providers, containers, APIs, and serverless functions. If SIEM stayed on-prem and static, it would be blind.
At the same time, the cost of getting security wrong keeps climbing. The average data breach now costs $5.2 million globally and $10.1 million for U.S. firms, while a persistent cybersecurity skills gap leaves millions of roles unfilled. Security teams are expected to defend larger, more dynamic cloud environments with fewer people and less time.
This is where SIEM technologies become essential. Through SIEM cloud integration, organizations can centralize cloud security monitoring, automate analysis, and correlate identity, network, and workload activity at scale. Instead of chasing isolated alerts, SIEM security solutions connect signals across cloud security services to enable faster, more accurate cloud threat detection.
Let’s break down how SIEM cloud integration actually works, where the value shows up, and what security teams need to get right.
Why SIEM and Cloud Security Had to Converge
Traditional SIEM was designed around predictable infrastructure. Fixed networks. Known endpoints. Stable log formats.
Cloud security is the opposite.
You’re dealing with:
- Ephemeral workloads that spin up and disappear
- Identity-driven access replacing network perimeters
- Shared responsibility models where visibility is fragmented
- Massive log volumes generated every second
Without deep cloud security monitoring, SIEM loses context. Without SIEM, cloud security tools operate in silos.
Integration is what connects behavior across users, workloads, networks, and applications into a single story.
The cloud has fundamentally transformed the approach to IT systems: its dynamic nature — with ephemeral workloads and resources that are created and destroyed rapidly — risks leaving analysts “blind.” If information is not properly collected and made persistent, critical events and logs can be lost, creating blind spots that are difficult to monitor and potentially exploitable.
A cloud-native SIEM integration ensures that these data are persistently retained, enabling continuous event collection and correlation, and making monitoring more effective and reliable.
— Alessandro Zatti, Sales Engineer, NetWitness
How SIEM Technologies Integrate with Cloud Security Services
Cloud security tools generate enormous volumes of signals, but on their own, those signals lack context. SIEM technologies bridge that gap by bringing cloud activity, identity events, and network data into a single analytical layer. The goal of SIEM cloud integration is not just to collect logs, but to connect behavior across cloud security services so threats can be detected, investigated, and contained faster.
Below are the key ways SIEM technologies integrate with cloud security services.
1. Native Log Ingestion from Cloud Platforms
Modern SIEM solutions integrate directly with cloud providers using native APIs and services.
This includes:
- Audit logs from cloud control planes
- Network flow logs from virtual networks
- Identity and access events
- Storage access logs
- Application and workload telemetry
Instead of agents everywhere, SIEM platforms pull structured data directly from cloud logging services. This is the foundation of cloud threat detection.
The result is near real-time visibility into what changed, who did it, and where it happened.
2. Integration with Cloud Security Tools
SIEM doesn’t replace cloud security tools. It connects them.
Common integrations include:
- Cloud workload protection platforms
- Cloud security posture management tools
- Identity protection services
- Endpoint detection and response platforms
Events from these tools flow into the SIEM, where they’re normalized, enriched, and correlated.
For example, a risky identity login combined with unusual network activity and a new workload deployment tells a much stronger story than any alert alone.
This is where SIEM cybersecurity moves from alerting to investigation.
3. Correlation Across Hybrid and Multi-Cloud Environments
Most enterprises aren’t cloud-only. They’re hybrid.
Modern SIEM networking capabilities allow teams to correlate:
- On-prem firewall logs
- Cloud network flow data
- VPN activity
- SaaS access events
A single user session can now be traced from an endpoint, through identity, across networks, and into cloud resources.
That end-to-end visibility is what makes SIEM security solutions relevant in real-world environments.
4. Cloud-Aware Detection Logic
Cloud changes how attacks look.
SIEM technologies integrate cloud-specific detection logic, such as:
- Excessive API calls
- Privilege escalation through identity misconfigurations
- Suspicious automation activity
- Abnormal access to object storage
- Lateral movement between cloud workloads
These detections rely on understanding cloud context, not just raw logs.
That’s why SIEM cloud integration is not just about data ingestion. It’s about cloud-native analytics.
5. Automation and Response Through Cloud Services
Integration doesn’t stop at detection.
Modern SIEM platforms integrate with:
- Cloud automation services
- Serverless workflows
- Ticketing and orchestration tools
- Cloud-native response actions
This allows security teams to:
- Disable compromised identities
- Quarantine workloads
- Block network paths
- Trigger forensic snapshots
All without manual intervention.
This is where SIEM solution value becomes operational, not theoretical.
Architecture Models for SIEM and Cloud Integration
Cloud-Native SIEM
Cloud-native SIEMs are deployed entirely in the cloud and integrate directly with cloud services by design.
They scale automatically, handle high log volumes, and support continuous updates. For organizations that are cloud-first, this model simplifies operations and accelerates detection.
Hybrid SIEM
Hybrid deployments combine cloud-based analytics with on-prem data sources.
This is common in regulated industries or large enterprises transitioning to the cloud. It allows teams to maintain control while still gaining cloud visibility.
SaaS-Based SIEM Platforms
SaaS SIEMs remove infrastructure management entirely.
They integrate easily with cloud security services, SaaS platforms, and remote endpoints. This model is especially effective for distributed teams and fast-growing environments.
Benefits of Integrating SIEM With Cloud Security Services
When done right, integration delivers more than compliance.
Key benefits include:
- Unified visibility across cloud and on-prem environments
- Faster detection of cloud-specific threats
- Reduced alert noise through correlation
- Improved investigation context
- Automated response at cloud speed
This is why SIEM security solutions remain central to modern security operations, even as tooling evolves.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.

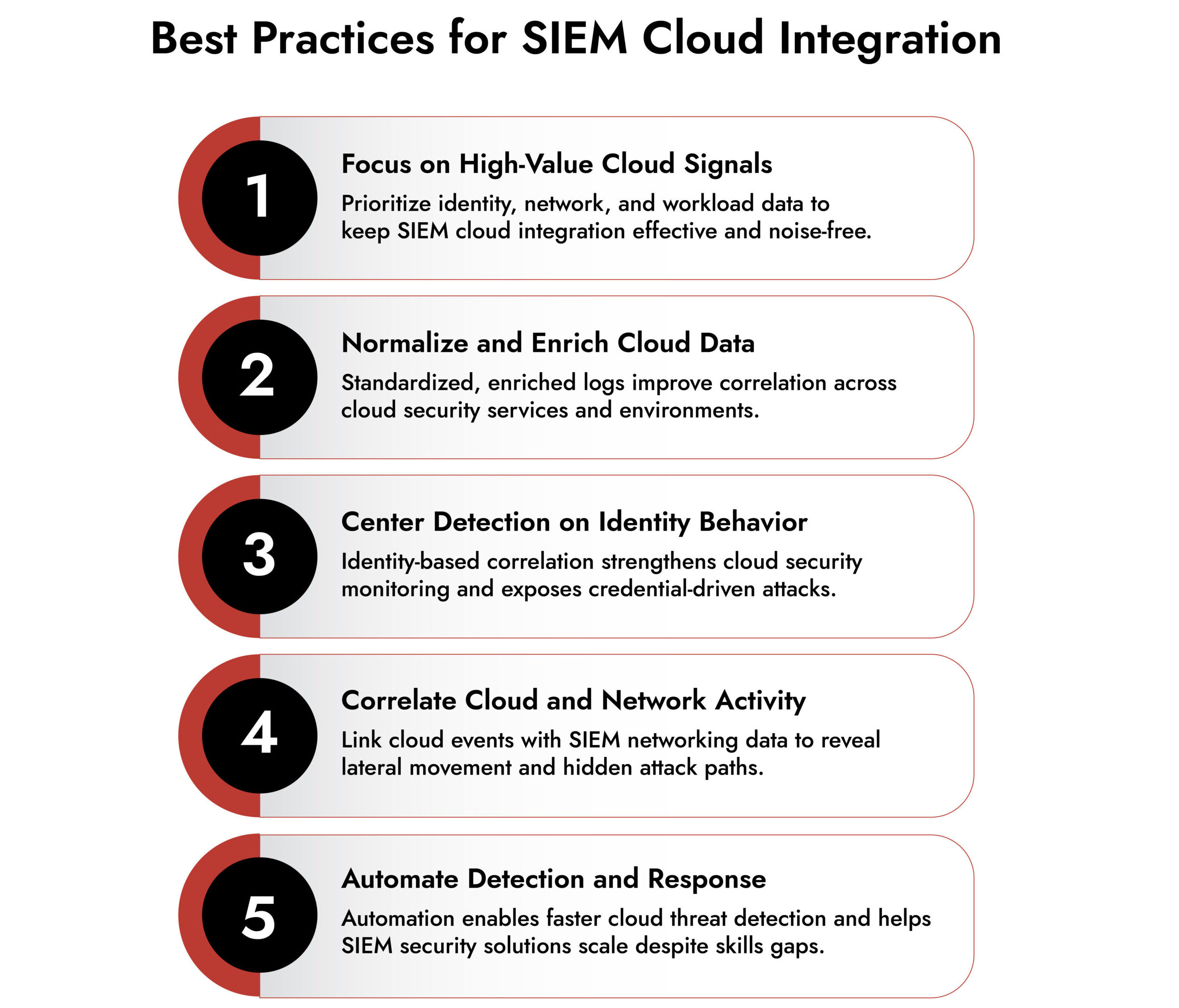
Common Integration Challenges to Watch For
Integration is powerful, but not effortless.
Security teams often struggle with:
- Data overload from cloud logs
- Poor normalization across sources
- Gaps in identity visibility
- Limited support for multi-cloud environments
- High costs tied to log ingestion
Choosing SIEM technologies that are cloud-aware by design is critical. Retrofitting cloud support onto legacy platforms rarely scales.
NetWitness SIEM Services for Cloud-Integrated Threat Detection
NetWitness SIEM services are built to support deep SIEM cloud integration by unifying cloud security services, on-prem infrastructure, and network telemetry into a single investigative view. Instead of treating cloud data as isolated logs, NetWitness correlates identity activity, workload behavior, and cloud security monitoring signals with SIEM networking and endpoint context to expose real attack paths. This approach strengthens cloud threat detection by focusing on behavior rather than static rules, helping security teams spot credential abuse, lateral movement, and suspicious automation that blend into normal cloud operations. As a result, NetWitness delivers SIEM cybersecurity and SIEM security solutions that scale with dynamic cloud environments while preserving the visibility and context required for faster, more confident response.
What This Really Means for Security Teams
Cloud security tools generate signals. SIEM turns them into understanding.
Without integration, teams chase alerts. With integration, they investigate behavior.
That shift is why SIEM technologies remain foundational, even as cloud security services multiply. The future isn’t fewer tools. It’s a better connection between them.
Frequently Asked Questions
1. What are the deployment options for modern SIEM technologies?
Modern SIEM technologies support cloud-native, hybrid, and SaaS-based deployments. Organizations choose based on compliance needs, infrastructure strategy, and scalability requirements.
2. Which SIEM solutions have the strongest integration with endpoint detection tools?
SIEM platforms that offer native integrations with leading EDR tools or support open APIs typically provide the strongest endpoint correlation. Cloud-native SIEMs often excel here due to real-time data ingestion.
3. What companies offer SIEM consulting and implementation services?
Many security vendors and managed service providers offer SIEM consulting, including platform deployment, integration, tuning, and ongoing optimization services for cloud and hybrid environments.
4. Which SIEM providers support hybrid cloud environments?
Several enterprise SIEM providers support hybrid cloud environments by correlating on-prem, cloud, and SaaS data sources within a single analytics layer.
5. What are the leading SIEM technologies used by enterprises?
Enterprises commonly use platforms such as Microsoft Sentinel, Splunk, IBM QRadar, and NetWitness, depending on their cloud strategy, scale, and security operations model.