How to Build and Enforce a Network Security Policy?
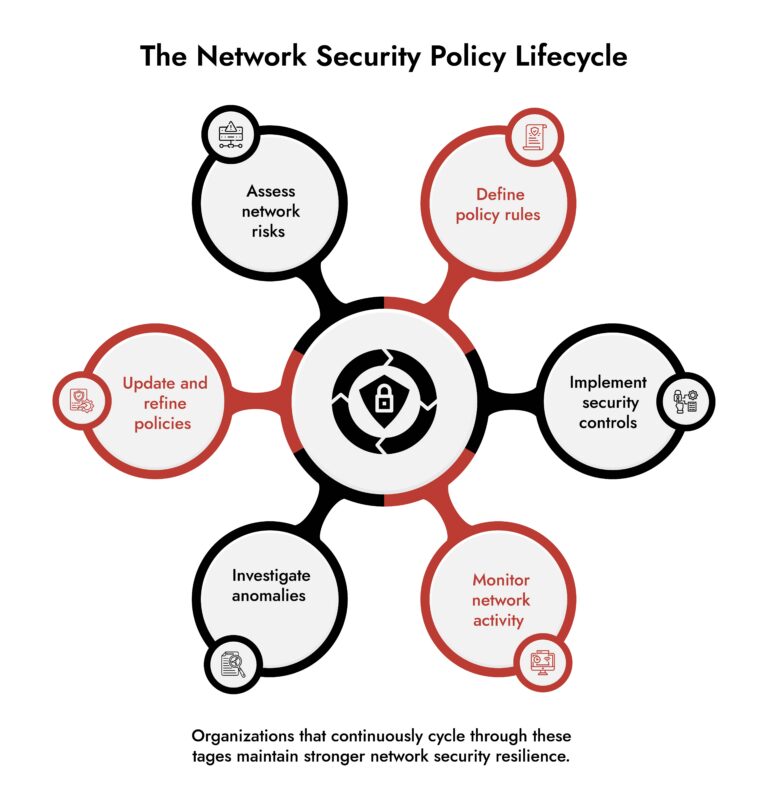
The network security policy of an organization is a document that outlines how to secure the data and assets of the organization. The goals of the document will be diverse depending on the nature of the organization and the data that is being protected. The process of developing a network security policy uses effective planning, implementation, and assessment. It includes each step of the process. These steps are risk assessment, control definition and implementation, governance alignment, and policy implementation and enforcement.
In practice, effective management of enterprise network security is reliant on visibility, defined accountability, and consistent monitoring. Organizations that consider policy enforcement to be a continuously evolving operational activity (instead of just a “document”) typically identify potential threats sooner and experience fewer losses from security breaches.
Introduction
Security leaders have long been aware of the unpleasant reality: attackers seldom access systems through spectacular means. Attackers typically gain entry utilizing overlooked situational use configurations, inconstant control methodologies, as well as policies not existing other than “on paper”.
Additionally, these reasons explain why a network security policy is essential. A network security policy defines how different types of devices communicate, who can access which devices, and how different mechanisms will operate across the entire network and connect through the entire network within an organization. Additionally, a well-designed and implemented Network Security Policy will help provide continuity across various security products and have a uniform response towards the multitude of threats facing the systems.
There’s ample evidence indicating that we must pay more attention to this issue. The 2024 IBM Cost of a Data Breach Report showed that the average global cost of a data breach has never been higher – $4.88 million. Furthermore, future CISA advisories for 2024 point to weak enterprise network segmentation. Poor security monitoring remains the main root cause of intrusions into enterprise networks.
A properly designed Network Security Policy can close gaps in product security (through improving enterprise intrusions response time) by providing a replicable framework for cybersecurity network security, providing for consistency in monitoring in responding with timely responses to anomalies that arise.
This guide will provide the specific steps that each organization may take to build and to enforce a policy that is effective in real world computing environments.
Why Every Enterprise Needs a Strong Network Security Policy
A network security policy sets the rules that govern network behavior. It defines acceptable traffic, security controls, access restrictions, monitoring practices, and response procedures. Without this foundation, even advanced network security solutions struggle to deliver results.
Organizations face three persistent challenges:
- Expanding hybrid infrastructure
- Increasing attack automation
- Fragmented visibility across tools
A policy-driven approach solves these issues by establishing consistent security rules across environments. According to NIST Special Publication 800-41, network policies remain one of the most effective controls for reducing attack surfaces in enterprise networks.
Key benefits include:
- Stronger enterprise network security management
- Consistent security enforcement across locations
- Faster detection through structured network security monitoring
- Reduced configuration drift and policy conflicts
In short, a Network Security Policy converts strategy into operational discipline.
How to Build and Enforce a Network Security Policy in Practice
Step 1: Assess the Enterprise Network Security Environment
Before defining controls, organizations must understand what they are protecting. A Network Security Policy begins with a clear view of infrastructure, assets, and traffic patterns. Security teams must map every component that interacts within the enterprise network.
This includes:
- Data centers
- Cloud workloads
- Remote endpoints
- Industrial or OT networks
- Third-party integrations
The NIST cybersecurity framework recommends that ongoing asset identification be the initial step in achieving robust enterprise network security.
The major activities in this phase include:
- Asset Inventory – Identification of critical systems and applications.
- Traffic Analysis – Understanding the baseline for traffic patterns.
- Threat Mapping – Determining what gets the most threat activity.
- Risk Prioritization – Understanding where controls must be the most stringent.
It is surprising for organizations to learn that shadow systems or old applications/integrations pose the greatest threat. It is impossible to have an effective network security policy without understanding these realities.
Step 2: Define a Network Security Policy Framework
A framework for network security policies converts security principles into practical standards. The policy must clearly define how the network functions in both normal and abnormal circumstances.
Essential elements usually consist of:
- Access Control Policies – Specify which users, systems, and services are permitted to access network resources.
- Network Segmentation Guidelines – Isolate essential systems from standard traffic.
- Traffic Filtering Guidelines – Define allowed and prohibited communication protocols.
- Monitoring Requirements – Specify which logs, telemetry, and traffic information need to be collected.
- Incident Escalation Protocols – Detail response processes when policy breaches take place.
As per Gartner’s security guidance (2024), companies that implement segmentation policies can minimize the risk of lateral movement. They can reduce this risk during assaults by as much as 80%. A well-structured Network Security Policy also clarifies ownership.
Every control must have:
- A responsible team
- A monitoring mechanism
- A documented enforcement process
Without these elements, policies remain theoretical.
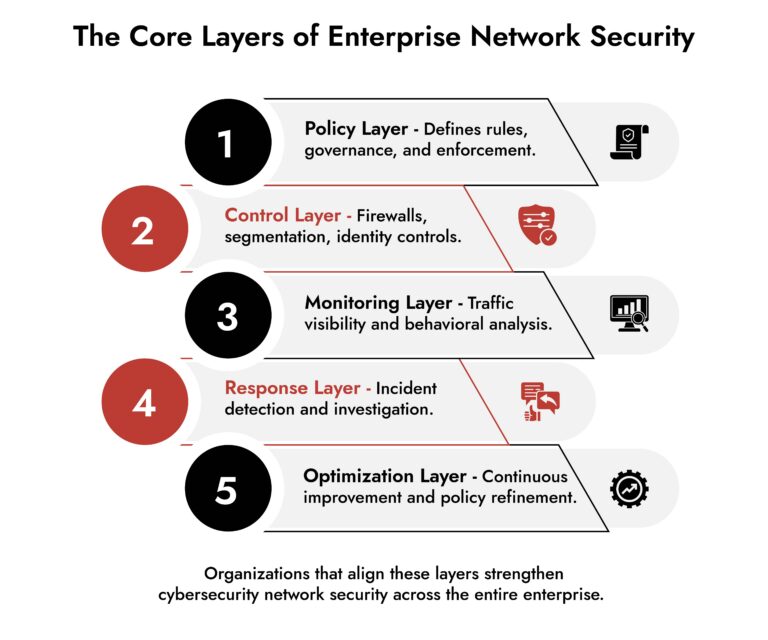
Step 3: Align Security Controls with Network Security Policy Rules
Policy without enforcement equals exposure. Once the Network Security Policy framework is defined, organizations must align their network security solutions with those rules. This step converts policy statements into real security controls.
Typical implementations include:
- Firewall rule enforcement
- Identity-based access control
- Network segmentation
- Intrusion detection systems
- Behavioral analytics platforms
Many enterprises rely on layered architectures where multiple network security companies supply components such as firewalls, endpoint protection, and monitoring tools. The challenge lies in coordination. Security teams must ensure that these technologies enforce a unified policy rather than conflicting configurations.
For example, if a policy restricts database access to internal systems only, the following controls must align:
- Firewall access rules
- Identity permissions
- VPN policies
- Traffic monitoring alerts
A cohesive enterprise network security management strategy ensures these layers operate together.
Step 4: Establish Continuous Network Security Monitoring
Once policies and controls exist, monitoring becomes the enforcement mechanism. A Network Security Policy only succeeds when violations trigger immediate investigation. Modern network security monitoring relies on high-fidelity telemetry from across the network.
Key monitoring capabilities include:
- Deep packet inspection
- Network traffic analytics
- Behavioral anomaly detection
- Centralized security logging
Based on Gartner’s 2025 SOC modernization report, firms with strong network telemetry cut threat dwell time by over 50%. This is compared to firms that rely only on endpoint alerts.
Effective monitoring answers three questions quickly:
- What changed in the network?
- Which systems were involved?
- How far did the activity spread?
Without this visibility, policy violations remain hidden until damage occurs.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
Step 5: Train Teams and Operationalize the Network Security Policy
However, it has to be adopted into operation to be effective, regardless of how good it is. Security professionals, network administrators, and IT management must understand how policy rules impact their daily operations.
The training should cover:
- Acceptable network usage standards
- Incident escalation procedures
- Monitoring responsibilities
- Change management procedures
The SANS Institute points out that policy training can help minimize misconfigurations in enterprise networks.
Step 6: Continuously Audit and Improve the Network Security Policy
Threat actors evolve quickly. Policies must evolve faster.
A Network Security Policy should undergo periodic reviews to address:
- New infrastructure deployments
- Emerging attack techniques
- Regulatory changes
- Lessons learned from incidents
Security teams should evaluate policies at least annually, though high-risk industries often review them quarterly.
Effective improvement strategies include:
- Conducting policy compliance audits
- Simulating attack scenarios
- Analyzing historical incident investigations
- Updating monitoring rules
Continuous refinement ensures the policy remains relevant to real threats.
How NetWitness Helps Enforce a Network Security Policy
Defining a Network Security Policy is the easy part. Enforcing it across a real, messy network is where things usually fall apart. This is where visibility makes the difference.
NetWitness helps teams see what’s actually happening on the network, not just what should be happening. It captures network traffic, flags unusual behavior, and lets analysts investigate incidents down to the packet level.
That matters because most policy failures don’t show up as obvious alerts. They show up as subtle deviations – unexpected connections, lateral movement, or data moving where it shouldn’t.
With NetWitness, teams can:
- Validate whether the Network Security Policy is being followed
- Detect violations early through stronger network security monitoring
- Investigate incidents with enough detail to take confident action
It also helps bring together signals from different network security solutions, so enforcement stays consistent across the environment. In simple terms, it turns a network security policy from a document into something you can actually see, test, and enforce.
Conclusion
Organizations need to adopt a systematic approach to risk assessments, policy development, control implementations, monitoring and continuous improvements in order to defend from today’s cyber threats.
A systematic methodology to managing risk is key to comprehensive enterprise network security. Organizations that successfully implement systematic methodologies to manage all aspects of enterprise information security achieve a competitive advantage by being able to identify and respond to security incidents sooner, thus protecting their most critical assets.
Organizations that want to improve enterprise network security management would benefit from better security policy enforcement. In fact, better enforcement is one of the most effective ways to enhance enterprise network security management.
Frequently Asked Questions
1. What is a network security policy?
Network Security Policy is defined as a set of rules that regulate communication between various systems connected together in a network. It is also defined as a set of rules that determine access, monitoring, and security requirements of a network.
2. Why is a network security policy important for enterprises?
A Network Security Policy helps in the effective implementation of security measures across the organization’s systems and environments. It plays a vital role in the maintenance of robust enterprise network security, early threat detection through monitoring, as well as the minimization of unauthorized access and data breaches.
3. What are the key components of a network security policy?
A typical Network Security Policy includes:
- Access control standards
- Network segmentation rules
- Traffic filtering guidelines
- Monitoring and logging requirements
- Incident response procedures
Together, these elements form a comprehensive network security policy framework.
4. What are the steps to build a network security policy?
The process generally includes:
- Assess network assets and risks
- Define a network security policy framework
- Implement aligned network security solutions
- Enable continuous network security monitoring
- Train teams and enforce compliance
- Audit and update policies regularly
5. What are common challenges in enforcing network security policies?
Organizations often struggle with:
- Limited network visibility
- Policy conflicts across tools
- Inconsistent enforcement across cloud and on-prem environments
- Lack of continuous enterprise network security management
Strong monitoring and centralized investigation capabilities help address these issues.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.